13.6 Creating Entitlement Policies
The Entitlements Service driver implements entitlements through the use of entitlement policies. An entitlement policy contains the following:
-
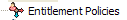
General: The name and description of the entitlement policy.
-
Membership: The list of users assigned to the policy. A user can be dynamically assigned to the policy when he or she meets the criteria for the policy, or the user can be statically (manually) assigned to the policy.
-
Entitlements: The list of entitlements associated with the policy. Users assigned to the policy receive all of the entitlements associated with the policy. If the user is removed from the policy, he or she loses all entitlements associated with the policy.
To create an entitlement policy:
-
In Designer, right-click the .
-
When you double-click the
 , it displays the editor to configure policies.
, it displays the editor to configure policies.
-
On the left side, click on the ‘+’ icon to add the entitlement policy. The editor displays three tabs- General, Membership, and Entitlements.
This list displays all entitlement policies that have been created for the driver set. If you are using Role-Based Entitlements for the first time, no policies are listed. The order of the policies in the list assumes importance during the conflict resolution of the entitlement, especially if the conflict-resolution is ‘priority’.
General page contains the following fields:
Entitlement Policy Name: Provide a name that indicates the purpose of the entitlement. The name must be unique within the driver set and cannot include more than 64 characters.
Description: Provide any additional information you want to identity the policy.
-
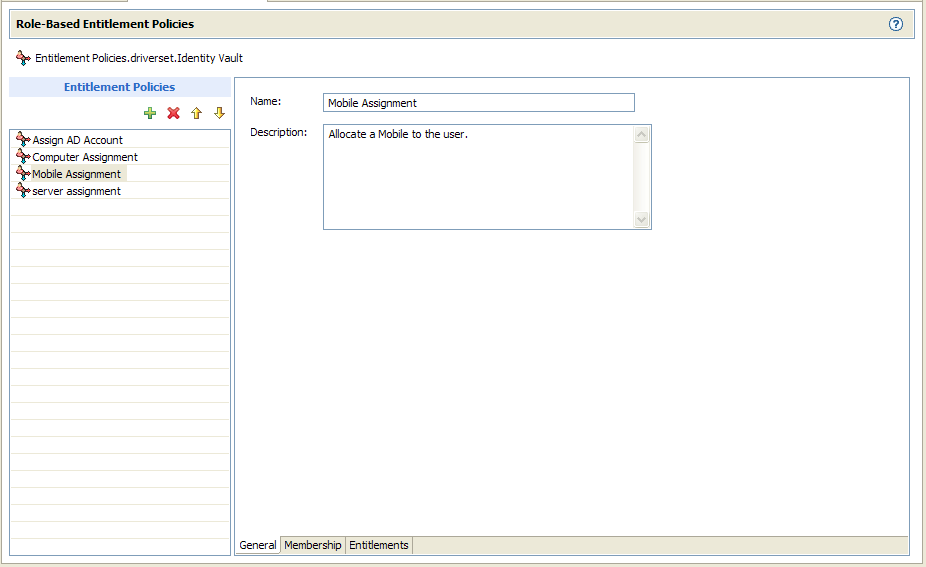
Membership page allows you to configure static and dynamic membership.
-
Static membership lets you include users who don’t meet the dynamic membership criteria or exclude users who meet the criteria but should not be members of the policy.
Under the , fill in the fields:
Include Members: Type the DN of a user you want to include, or click
 to browse for and select the user, then press Enter to add the user to the inclusion list. To remove a user from the inclusion list, select the user and and click
to browse for and select the user, then press Enter to add the user to the inclusion list. To remove a user from the inclusion list, select the user and and click  icon. To edit a user name, double-click the user.
icon. To edit a user name, double-click the user.
Exclude Members: Type the DN of a user you want to exclude, or click
 to browse for and select the user, then press Enter to add the user to the exclusion list. To remove a user from the exclusion list, select the user and click
to browse for and select the user, then press Enter to add the user to the exclusion list. To remove a user from the exclusion list, select the user and click  icon. To edit a user name, double-click the user.
icon. To edit a user name, double-click the user.
-
Dynamic membership lets you define which users should be members of the entitlement policy by specifying criteria and specifying where in the tree to search for users that meet the criteria. If a user meets the criteria you specify, the policy’s entitlements are automatically applied to the user. If the user’s information changes and no longer meets the criteria, the entitlements are revoked without any manual intervention.
Under , fill in the fields:
Search Identity: Specify an object that has the rights that you want to be used when querying for Dynamic Membership. Specify the object with the appropriate rights.
For example, there might be parts of the tree that you have rights to that you don't want included in the query for the dynamic list of members.
You could use this field to specify the Driver Set object, making sure that the Driver Set has the appropriate rights. Or, you could create a User object specifically for use with Entitlement Policies, and assign it the rights you want the query to use.
Begin Search at (Base DN): Specify the base container where you want the user search to begin.
Scope of Search: Specify whether you want to search the base container and all of its subcontainers () or only the base container ().
For the entitlement policy to evaluate users in the containers you specify, the users must be in a read/write or master replica on the Metadirectory server that is running the Entitlements Service driver.
Criteria: Specify the criteria that determine which users are members of the policy. The criteria are organized into criteria groups. Each group can contain one or more criterion. You click the
 icon to add criterion to a group. You can also click to create additional groups.
icon to add criterion to a group. You can also click to create additional groups.
By default, the criteria includes all User class objects (and objects of classes derived from the User class) within the search scope.
If you create a new object class derived from User, an existing entitlement policy does not recognize that class until you make a modification to the entitlement policy. This prevents users of a new class from being granted entitlements unintentionally. When any modification is made to the entitlement policy, the list of user-derived classes for that policy is updated.
-
-
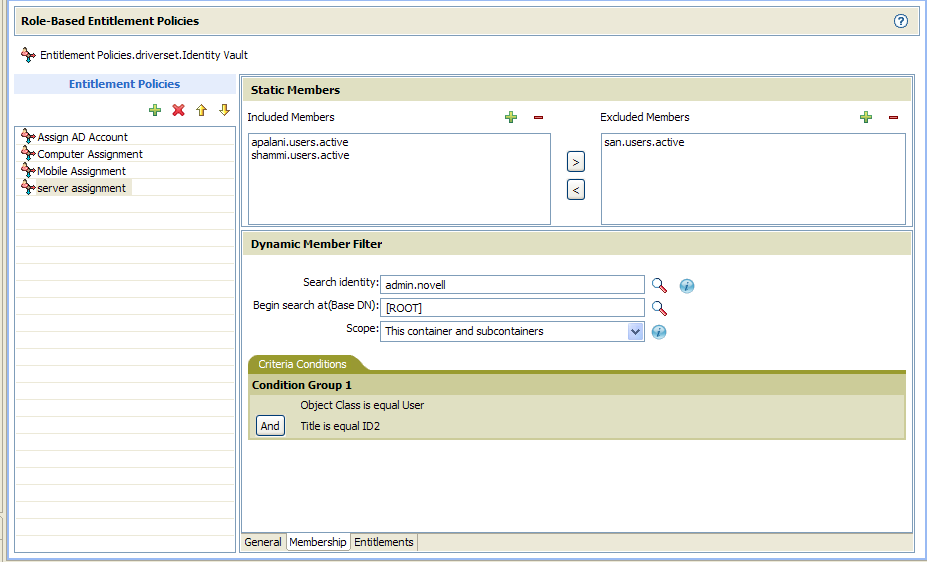
In the Entitlements page, add the entitlements you want associated with the policy.
Associating Entitlements
-
In the section, click
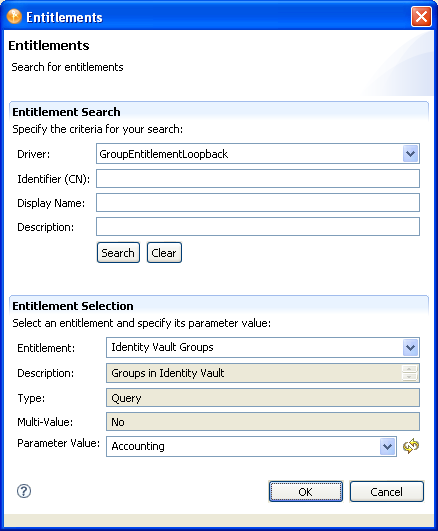
 icon to add an entitlement for this role. The Entitlement Search dialog box displays:
icon to add an entitlement for this role. The Entitlement Search dialog box displays:
-
To complete the Entitlement search:
-
Choose the driver that contains the entitlement you want.
-
Specify the , , and on which you want to search.
You can enter a wildcard (such as S*, *S) or a regular expression (such as [A-Z][a-z]*), then click .
You can enter a value for all of the fields or none of the fields. If you do not supply a value in a particular field, the search returns all of the possible values for that field. If you enter values in one or more of the fields, the values are ANDed together to create the search filter. The search occurs locally. Entitlements contained by the selected driver that match the search criteria are displayed in the Entitlements Selection section.
-
The search is complete when the field displays .
-
-
To complete the Entitlement selection:
-
Choose the entitlement from the Entitlement drop-down list.
The , , and fields are read-only. These values are obtained from the Entitlement definition.
-
Choose the parameter value.
-
Click to save the definition. Designer displays the definition in the Entitlements table. Query parameter values are translated to the query’s full CN when displayed in the table.
-
-
Configuring Entitlements
-
To update/modify the value of the entitlement, click the value cell of the associated entitlement and click
 icon.
icon.
-
Click the
 icon to add a new value.
icon to add a new value.
-
-
-
You can assign rights to the objects through iManager. Refer to iManager 2.7 documentation.
Each member of the policy becomes a trustee of the objects you add. There are several reasons why you might want to make the policy a trustee of an object:
-
One of the policy’s entitlements requires the policy’s members to have rights to an object.
-
You want to use the policy to assign users as trustees of an object even though rights to the object are not required for an entitlement. In this case, you are using the entitlement policy to grant and revoke trustee rights for members of the policy.
-
NOTE:You must verify entitlements that users have on the connected systems, and decide whether to grant, change, or revoke their entitlements. You must re-evaluate the entitlements before creating or editing an Entitlement Policy, when a related membership attribute is changed for a user, or when a user is moved or renamed. iManager supports re-evaluation process. Refer to the Identity Manager 3.6 Driver for Role-Based Entitlements: Implementation Guide for more information.
 :
:  :
: