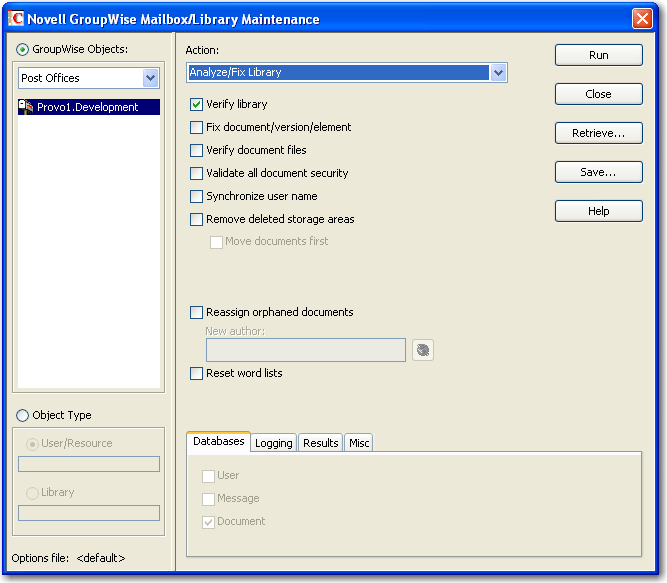
28.2 Analyzing and Fixing Library and Document Information
The option of Mailbox/Library Maintenance performs more library-specific functions than . For all options except , all documents in each of the selected library databases are checked. This can be a time-consuming process. Therefore, if you intend to select more than one of the options, you can save time by selecting each of them before clicking . This causes all selected options to be run against each document, which is faster than running each option individually against all documents.
To validate library databases:
-
In ConsoleOne, browse to and select one or more Post Office objects where you want to validate libraries.
-
Click .
-
From the drop-down menu, select .
-
Select from the following options:
Verify Library: This is a post office-level check. It verifies that all libraries are on the libraries list. It also checks the schema and guarantees its integrity. If there is a problem with the schema, it resets to a default schema to reclaim any missing items. For example, if you deleted the Document Type property, you could recover it using this option.
Fix Document/Version/Element: This performs an integrity check to verify the following:
-
Each document has one or more versions linked to it.
-
Each version has one or more elements linked to it.
-
All versions are linked to a document.
-
All elements are linked to a version.
If there are any missing links, the missing documents or versions are created from the information contained in the existing version or element for which the link is missing. For example, if a version is found that shows no link to a document, a document is created from the information contained in the version and the link is reestablished. Of course, any information in the lost document that might have been newer than the information contained in the old version is lost.
Verify Document Files: This determines if the BLOB exists for a document and the document is accessible. If not, an error is logged for that document. The log message does not indicate why a file is missing or inaccessible. You can recover a file by restoring it from backup.
Possible errors that would be logged include:
-
If the file system on the network becomes corrupted, this tells you which documents cannot be opened or which BLOB files are missing.
-
If a file was marked by someone as Read Only or Hidden, this option logs an error indicating that the file is inaccessible.
Validate All Document Security: This option validates document security for the Author, Creator and Security (document sharing) fields. The validation replaces the results of selecting the option, and is more thorough. Therefore, you only need to select one option or the other.
Synchronize User Name: The and fields display users’ full names, not unique IDs. If a user’s name is changed, such as for marriage, this option verifies that the user’s name on document and version records is the same as the user’s current display name. In other words, the and fields in documents and versions are updated to the user’s newer name.
Remove Deleted Storage Areas: When you delete a document storage area in the Storage Areas page of a library’s details dialog box, the document storage area and the documents stored there remain on the system. Deleting the storage area from the library only means that new documents are not stored there. The documents there continue to be available to users.
If you want to also remove the document storage area from the system, you have two options: delete the storage area and its documents, or first move the documents and then delete the storage area. The first option is not advisable, but exists so that if you have moved all of the documents that can be moved, but some corrupted documents are left behind, you can force the document storage area to be deleted.
You should normally select so that users continue to have access to those documents from a different document storage area. With this option, all BLOBs in the library are checked to see which documents are in the area being deleted.
Reassign Orphaned Documents: Documents can occasionally become orphaned (unattached to a user). For example, this can happen when a user leaves your organization and the user object is removed. All documents belonging to that user are no longer available in GroupWise searches and cannot be accessed by anyone (document security is controlled by the user listed in the and fields). This option lets you reassign these documents to another user. You must select a new author from the browser menu after checking this option. The new author you designate has access to all orphaned documents in this library.
Reset Word Lists: Documents stored in a library are indexed and inserted into a generated word list. This allows users to search for a document by keywords as well as any word contained within a document. The document library word list might become outdated and if this occurs, the word list must be regenerated. This option allows the program to regenerate the document library word list the next time an index operation is performed.
-
-
Using the tabs at the bottom of the Mailbox/Library Maintenance dialog box, set the following options:
Selected options can be saved for repeated use. See Saving Mailbox/Library Maintenance Options.
-
Click to perform the Analyze/Fix Library operation.
Analyze/Fix Library can also be run using the stand-alone GroupWise Check program. See Section 34.1, GroupWise Check. It can also be scheduled to run on a regular basis by properly configuring the POA. See Section 36.4.1, Scheduling Database Maintenance.