A.1 User Application Configuration: Basic Parameters
Figure A-1 User Application Configuration Basic Options
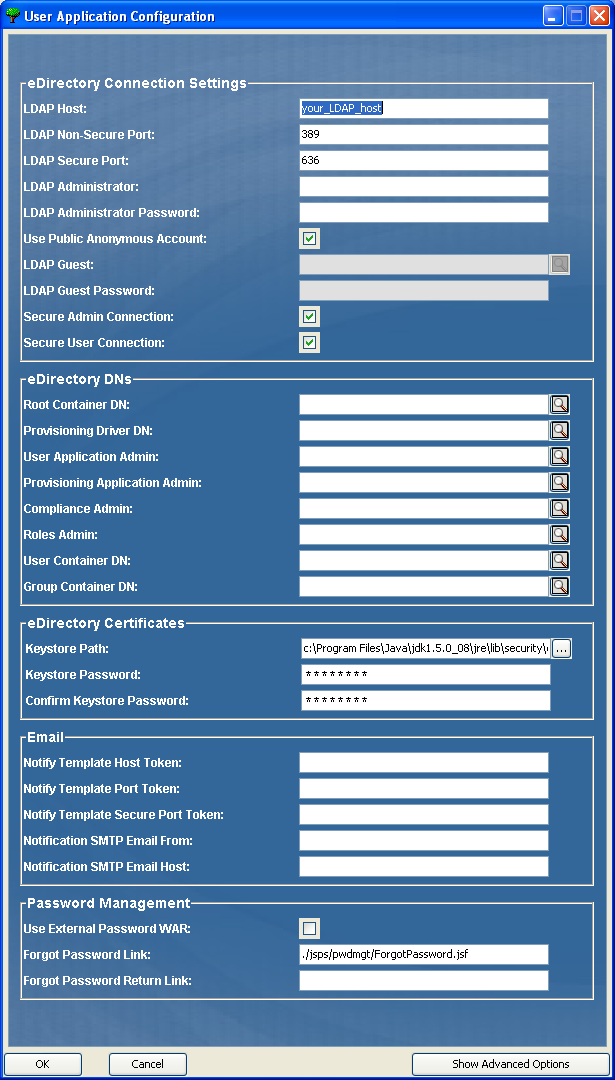
Table A-1 User Application Configuration: Basic Options
|
Type of Setting |
Option |
Description |
|---|---|---|
|
eDirectory® Connection Settings |
|
Required. Specify the hostname or IP address for your LDAP server and its secure port. For example: myLDAPhost |
|
|
Specify the non-secure port for your LDAP server. For example: 389. |
|
|
|
Specify the secure port for your LDAP server. For example: 636. |
|
|
|
Required. Specify the credentials for the LDAP Administrator. This user must already exist. The User Application uses this account to make an administrative connection to the Identity Vault. This value is encrypted, based on the master key. You can use configupdate utility to modify this setting as long as you have not modified it using the User Application’s Administration tab. |
|
|
|
Required. Specify the LDAP Administrator password. This password is encrypted, based on the master key. You can use configupdate utility to modify this setting as long as you have not modified it using the User Application’s Administration tab. |
|
|
|
Allows users who are not logged in to access the LDAP Public Anonymous Account. |
|
|
|
Allows users who are not logged in to access permitted portlets. This user account must already exist in the Identity Vault. To enable the LDAP Guest, you must deselect . To disable the Guest User, select . |
|
|
|
Specify the LDAP Guest password. |
|
|
|
Select this option to require that all communication using the admin account be done using a secure socket. (This option can have adverse performance implications). This setting allows other operations that don't require SSL to operate without SSL. |
|
|
|
Select this option to require that all communication using the logged-in user’s account be done using a secure socket. (This option can have adverse performance implications). This setting allows other operations that don't require SSL to operate without SSL. |
|
|
eDirectory DNs |
|
Required. Specify the LDAP distinguished name of the root container. This is used as the default entity definition search root when no search root is specified in the directory abstraction layer. |
|
|
Required. Specify the distinguished name of the User Application driver (described in Section 3.1, Creating the User Application Driver in iManager). For example, if your driver is UserApplicationDriver and your driver set is called myDriverSet, and the driver set is in a context of o=myCompany, you would type a value of: cn=UserApplicationDriver,cn=myDriverSet,o=myCompany |
|
|
|
Required. An existing user in the Identity Vault who has the rights to perform administrative tasks for the User Application user container specified. This user can use the tab of the User Application to administer the portal. If the User Application Administrator participates in workflow administration tasks exposed in iManager, Novell Designer for Identity Manager, or the User Application ( tab), you must grant this administrator appropriate trustee rights to object instances contained in the User Application driver. Refer to the User Application: Administration Guide for details. To change this assignment after you deploy the User Application, you must use the pages in the User Application. You cannot change this setting via configupdate if you have started the application server hosting the User Application. |
|
|
|
The Provisioning Application Administrator uses the tab (under the tab) to manage the Provisioning Workflow functions. These functions are available to users through the tab of the User Application. This user must exist in the Identity Vault prior to being designated the Provisioning Application Administrator. To change this assignment after you deploy the User Application, you must use the pages in the User Application. |
|
|
|
The Compliance Module Administrator is a system role that allows members to perform all functions on the tab. This user must exist in the Identity Vault prior to being designated as the Compliance Module Administrator. During a configupdate, changes to this value only take effect if you do not have a valid Compliance Module Administrator assigned. If a valid Compliance Module Administrator exists, then your changes are not saved. To change this assignment after you deploy the UserApplication, use the page in the User Application. |
|
eDirectory DNs (continued) |
|
This role is available in the Novell Identity Manager Roles Based Provisioning Module. This role allows members to create, remove, or modify all roles, and grant or revoke any role assignment to any user, group, or container. It also allows its role members to run any report for any user. By default, the User Application Admin is assigned this role. To change this assignment after you deploy the User Application, use the page in the User Application. During a configupdate, changes to this value only take effect if you do not have a valid Roles Administrator assigned. If a valid Roles Administrator exists, then your changes are not saved. |
|
|
Required. Specify the LDAP distinguished name (DN) or fully qualified LDAP name of the user container. This defines the search scope for users and groups. Users in this container (and below) are allowed to log in to the User Application. IMPORTANT:Be sure the User Application Administrator specified during User Application driver set up exists in this container if you want that user to be able to execute workflows. You cannot change this setting via configupdate if you have started the application server hosting the User Application. |
|
|
|
Required. Specify the LDAP distinguished name (DN) or fully qualified LDAP name of the group container. Used by entity definitions within the directory abstraction layer. You cannot change this setting via configupdate if you have started the application server hosting the User Application. |
|
|
eDirectory Certificates |
|
Required. Specify the full path to your keystore (cacerts) file of the JDK that the application server application server is using to run, or click the small browser button and navigate to the cacerts file. On Linux or Solaris, the user must have permission to write to this file. |
|
|
Required. Specify the cacerts password. The default is changeit. |
|
|
|
|
Specify the application server hosting the Identity Manager User Application. For example: myapplication serverServer This value replaces the $HOST$ token in e-mail templates. The URL that is constructed is the link to provisioning request tasks and approval notifications. |
|
|
Used to replace the $PORT$ token in e-mail templates used in provisioning request tasks and approval notifications. |
|
|
|
Used to replace the $SECURE_PORT$ token in e-mail templates used in provisioning request tasks and approval notifications. |
|
|
|
Specify e-mail to come from a user in provisioning e-mail. |
|
|
|
Specify the SMTP e-mail host that provisioning e-mail is using. This can be an IP address or a DNS name. |
|
|
Password Management |
|
This feature enables you to specify a Forgot Password page residing in an external Forgot Password WAR and a URL that the external Forgot Password WAR uses to call back the User Application through a Web service. If you select , you must supply values for and . If you do not select IDM uses the default internal Password Management functionality, ./jsps/pwdmgt/ForgotPassword.jsf (without the http(s) protocol at the beginning). This redirects the user to the Forgot Password functionality built into the User Application, rather than to an external WAR. |
|
|
This URL points to the Forgot Password functionality page. Specify a ForgotPassword.jsf file in an external or internal password management WAR. For details, see Configuring External Password Management. |
|
|
|
If you are using an external password management WAR, supply the path that the external Password Management WAR uses to call back the User Application through Web Services, for example https://idmhost:sslport/idm. |
NOTE:You can edit most of the settings in this file after installation. To do so, run the configupdate.sh script or the Windows configupdate.bat file located in your installation subdirectory. Remember that in a cluster, the settings in this file must be identical for all members of the cluster.