29.4 Configuring a Custom Header Policy
To inject values into a custom header, you need to know the name of the tag and its expected value type. The names are specific to the application. The names might be case sensitive. They might require an X- prefix. Because the requirements vary, you need to enter them in the format as specified by the application. For example, an application might require the following to be in the custom header:
If you create a custom header policy with these name/value pairs, the policy injects these names with their values into a custom header, before sending the request to the Web server.
To create such a policy:
-
In the Administration Console, click > > .
-
Specify a name for the policy, select for the type, then click .
-
(Optional) Specify a description for the injection policy. This is useful if you plan to create multiple custom header policies to be used for multiple resources.
-
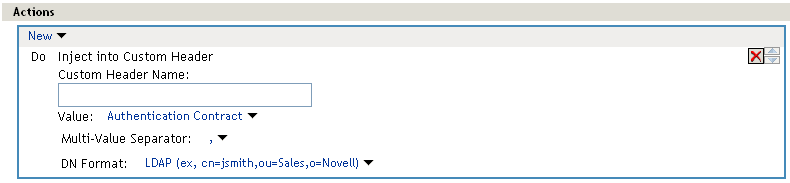
In the section, click , then select .
-
Fill in the following fields:
Custom Header Name: Specify the name to be inserted into the custom header. These are the names required by your application. If your application requires the X- prefix, make sure you include the prefix in this field.
Value: Select the value required by the name. Select one of the following:
-
Authentication Contract: Injects the URI of a local authentication contract that the user used for authentication.
-
Client IP: Injects the IP address associated with the user.
-
Credential Profile: Injects the credentials that the user specified at login. You can select , , or . For more information, see Section 29.3, Configuring an Authentication Header Policy.
-
LDAP Attribute: Injects the value of the selected attribute.
-
Liberty User Profile: Injects the value of the selected attribute. If no profile attributes are available, you have not enabled their use in the Identity Server configuration. See Section 12.2, Enabling Web Services and Profiles.
-
Proxy Session Cookie: Injects the session cookie associated with the user.
-
Roles for Current User: Injects the roles that have been assigned to the user.
-
Shared Secret: Injects a value that has been stored in the selected shared secret store. Select the shared secret store and the name of the value you want injected.
You can create your own value. Click , specify a display name for the store, and the Access Manager creates the store. Select the store, click , specify a name for the attribute, then click . The name you select for the attribute should match the Custom Header name. The store can contain one name/value pair or a collection of name/value pairs. For more information, see Section 30.4, Creating and Managing Shared Secrets.
-
String Constant: Injects a static value that you specify in the text box. This value is used by all users who access the resources assigned to this policy.
-
Java Data Injection Module: Specifies the name of a custom Java plug-in, which injects custom values into the header. Usually, you can use either the or option to supply custom values, because both are extensible. For more information, see Novell Access Manager Developer Tools and Examples.
-
-
Specify the format for the value:
Multi-Value Separator: Select a value separator, if the value type you have select is multi-valued. For example, can contain multiple values.
DN Format: If the value is a DN, select the format for the DN:
-
LDAP: Specifies LDAP typed, comma notation: For example:
cn=jsmith,ou=Sales,o=novell
-
NDAP Partial Dot Notation: Specifies eDirectory typeless, dot notation: For example:
jsmith.sales.novell
-
NDAP Leading Partial Dot Notation: Specifies eDirectory typeless, leading dot notation.
.jsmith.sales.novell
-
NDAP Fully Qualified Partial Dot Notation: Indicates eDirectory typed, dot notation. For example:
cn=jsmith.ou=Sales.o=novell
-
-
To save the policy, click twice, then click .