1.1 Understanding an Access Manager Configuration
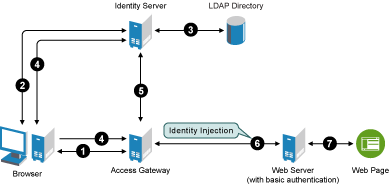
The following figure illustrates the components and process flow that make up a basic configuration.
Figure 1-1 Basic Process Flow
-
The user requests the Access Gateway for access to a protected resource.
-
The Access Gateway redirects the user to the Identity Server, which prompts the user for a username and password.
-
The Identity Server verifies the username and password against an LDAP directory user store (eDirectory™, Active Directory*, or Sun ONE*).
-
The Identity Server returns an authentication artifact to the Access Gateway.
-
The Access Gateway retrieves the user’s credentials from the Identity Server.
-
The Access Gateway injects the basic authentication information into the HTTP header.
-
The Web server validates the authentication information and returns the requested Web page.
You configure the Access Manager so that a user can access a resource on a Web server whose name and address are hidden from the user. This basic configuration sets up communication between the following four servers.
Figure 1-2 Basic Access Manager Configuration
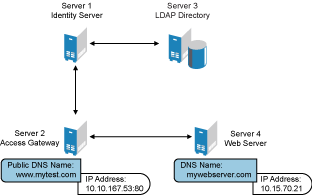
Although other configurations are possible, this section explains the configuration tasks for this basic Access Manager configuration. This section explains how to set up communication using HTTP. For HTTPS over SSL, see Section 3.0, Enabling SSL Communication.