18.0 Identity Integration
Sentinel Rapid Deployment provides an integration framework for identity management systems. This integration provides functionality on several levels:
-
Identity Browser provides the ability to look up the following information about a user:
-
Contact information
-
Accounts associated with that user
-
Most recent authentication events
-
Most recent access events
-
Most recent permissions changes
-
-
Identity Browser lookup from events
-
Reports and correlation rules provide an integrated view of a user's true identity, even across multiple systems on which that user has separate accounts. For example, accounts like NOVELL\testuser; > cn=testuser,ou=engineering,o=novell, and TUser@novell.com can be mapped to the actual person who owns the accounts.
By displaying information about the people initiating a given action or people affected by an action, incident response times are improved and behavior-based analysis is enabled.
Novell provides an optional integration with Novell Identity Manager. The screenshots and descriptions in this section are based on Novell Identity Manager.
Sentinel Rapid Deployment synchronizes identity information with major identity management systems and stores local copies of key information about each Identity. The following table summarizes the commonly used information provided:
Table 18-1 Identity Information
The Identities stored by Sentinel are then linked with accounts created on endpoint systems by the identity management system. This helps Sentinel associate the correct identity information with the native events from those endpoint system. Some identity information is injected directly into the inbound event by using the mapping service. The remaining identity information, such as photograph and contact information, is accessible through the Identity Browser.
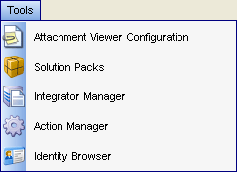
Figure 18-1 Accessing the Identity Browser
The identity information injected into the event can be used for correlation and for performing actions on the identities that are associated with detected activity. For example, Sentinel is able to see multiple failed logins from a given person and not just an account. A detected violation could trigger disabling activities for all accounts associated with an identity.
Figure 18-2 Identity Details
