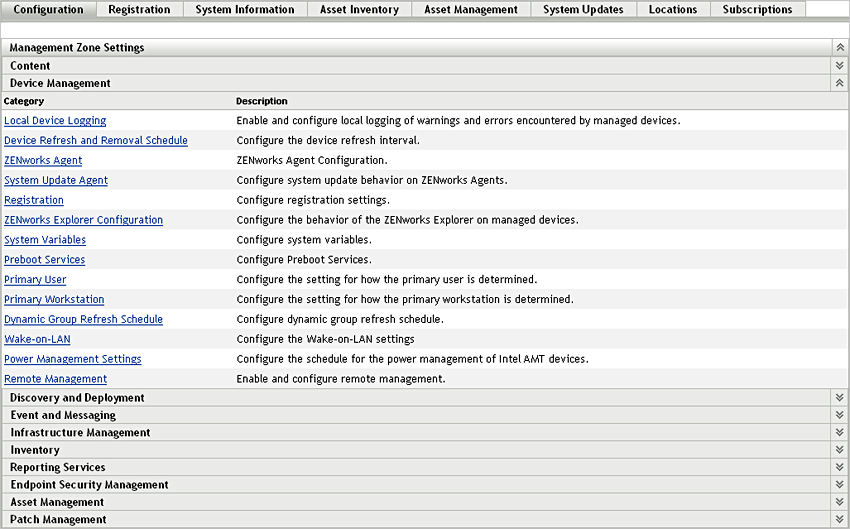
2.1 Configuring Discovery Settings
IP discoveries use the following configuration settings that can be modified, if necessary:
-
Number of discoveries that can be processed concurrently (default is 5)
-
IP subnets or address ranges that are to be excluded from the discovery
-
Discovery technologies that are used (the default is LDAP, MAC Address, WinAPI, ZENworks, and SSH)
-
In ZENworks Control Center, click the tab.
-
In the Management Zone Settings panel, click , then click the option.
-
In the Discovery Process Settings panel, modify the following settings as necessary:
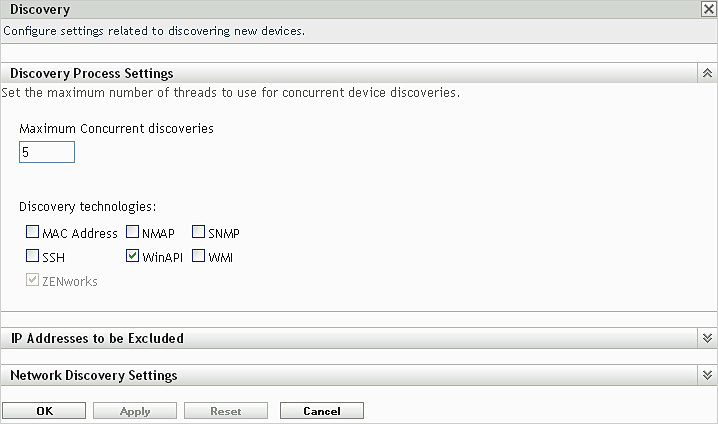
Maximum Concurrent Discoveries: A discovery task consists of one or more discovery requests. For IP-based discovery tasks, a request is created for each discovery technology and each IP address in the specified range. Therefore, if you use six technologies to discover 10 IP addresses, 60 requests are created. For LDAP-based discovery tasks, a request is created for each context or group to be searched.
You use this field to specify the maximum number of discovery requests that the ZENworks Server can process at one time. A smaller number eases the traffic load on the network but requires more time to complete the discovery task; you should use a smaller number if you schedule discovery tasks during peak network load times. A larger number has the opposite effect; heavier traffic load with less time to complete the task.
For more information on the IP discovery process, see Section 1.3, IP Discovery Technologies.
Discovery Technologies: The discovery process can utilize a variety of different technologies. When more than one technology is used, the discovery process initiates a discovery request for each technology, with all technology requests running simultaneously. This is done for each target IP address. For example, if you use MAC Address, SNMP, and WMI, the discovery process creates three requests for each target IP address. The requests are queued and run according to the setting.
If more than one technology request returns information for a discovered device, the information is merged together. In the case of conflicting information, the discovery process chooses the “best” information.
Using fewer discovery technologies reduces the time required to complete the discovery task but might also reduce the amount of information received.
For detailed information about each technology, see Section 1.3, IP Discovery Technologies.
-
In the IP Addresses to be Excluded panel, specify the IP subnets or address ranges to be excluded from the discovery.
NOTE:All the discovery tasks inherit the IP address ranges specified at the Management Zone level. If the IP address range is specified at a task level, the combined ranges of the Management Zone and discovery task are excluded from the discovery.
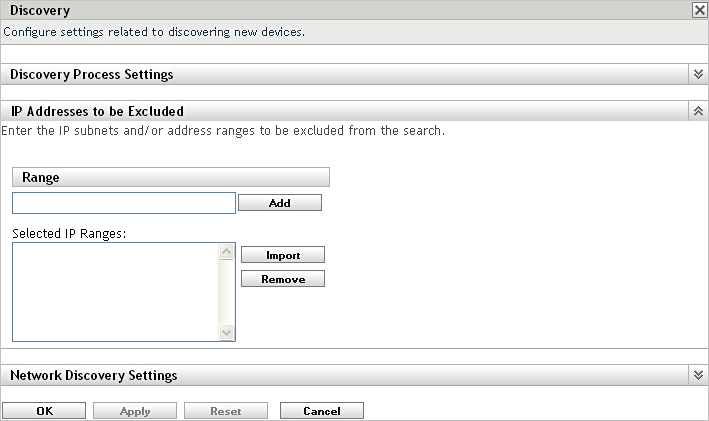
You can manually add the IP addresses to be excluded or import the IP addresses to be excluded from a CSV file.
-
To manually add the IP address to be excluded:
-
In the field, enter the IP address range in one of the following formats:
xxx.xxx.xxx.xxx: Standard dotted-decimal notation for a single address. For example, 123.45.167.100.
xxx.xxx.xxx.xxx - xxx.xxx.xxx.xxx: Standard dotted-decimal notation for a range of addresses. For example, 123.45.167.100 - 123.45.167.125.
xxx.xxx.xxx.xxx/n: Standard CIDR (Classless Inter-Domain Routing) notation. With CIDR, the dotted decimal portion of the IP address is interpreted as a 32-bit binary number that has been broken into four 8-bit bytes. The number following the slash (/n) is the prefix length, which is the number of shared initial bits, counting from the left side of the address. The /n number can range from 0 to 32, with 8, 16, 24, and 32 being commonly used numbers. For example, 123.45.167.100/24 matches all IP addresses that start with 123.45.167. When you add the IP address range to the list (see the next step), it is automatically expanded to show the range of addresses in dotted-decimal notation.
-
To add the IP address range to the list, click .
-
-
To use a CSV list to import an IP address to be excluded:
-
In the list, click .
The Import CSV File dialog box is displayed.
-
Click to browse for and select a file that contains a comma-separated or columnar list of IP addresses.
-
Click .
-
-
-
In the Network Discovery Settings panel, modify the following settings as necessary:
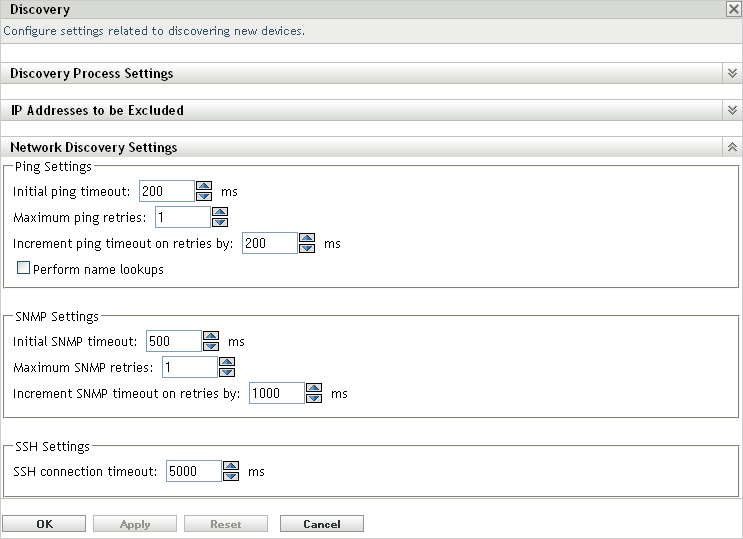
IP Settings: These settings apply when using the WMI and SNMP discovery technologies.
-
Initial ping timeout: Specifies how long the discovery technology waits for a response to an ICMP query (ping).
-
Maximum ping retries: Specifies the number of times a ping is repeated before giving up.
-
Increment ping timeout on retries by: Adds the specified amount of time to each retry. For example, if the initial ping timeout is 200 milliseconds, the maximum ping retries is 3, and the increment is 200 milliseconds, the first retry timeout is 400, the second retry timeout is 600, and the third retry timeout is 800.
-
Perform name lookups: Uses a reverse lookup to associate the target IP address with a DNS name. Deselect this option if you do not want the DNS name discovered.
SNMP Settings: These settings apply when using the SNMP discovery technology.
-
Initial SNMP timeout: Specifies how long the discovery technology waits for a response to an SNMP query before assuming that the packet is lost.
-
Maximum SNMP retries: Specifies the number of times an SNMP query is repeated before giving up.
-
Increment SNMP timeout on retries by: Adds the specified amount of time to each retry. For example, if the initial SNMP timeout is 500 milliseconds, the maximum SNMP retries is 3, and the increment is 1000 milliseconds, the first retry timeout is 1500, the second retry timeout is 2500, and the third retry timeout is 3500.
SSH Settings: These settings apply when using the SSH discovery technology.
-
SSH connection timeout: Specifies how long the discovery technology waits to establish a SSH connection with the Linux device.
-
-
Click to save the changes.