8.0 Viewing Effective Policies
Each policy type (Firewall, Application Control, USB Connectivity, and so forth) has one effective policy that is enforced on the device per location. The effective policy is created by merging all of the user, device, and zone assigned policies of that type according to established ordering and merging rules (see Effective Policies
in the ZENworks 11 SP2 Endpoint Security Policies Reference). The Endpoint Security Agent lets you view the effective policies for the device.
NOTE:You can also use ZENworks Control Center to generate a report that shows the effective policies for a device. The report shows the effective policies according to the last time they were collected from the device. For more information, see Policy Reports
in the ZENworks 11 SP2 Endpoint Security Policies Reference.
To view the effective policies in the Endpoint Security Agent:
-
Make sure you have enabled the device to accept an override password. For information, see Section A.0, Override Password.
-
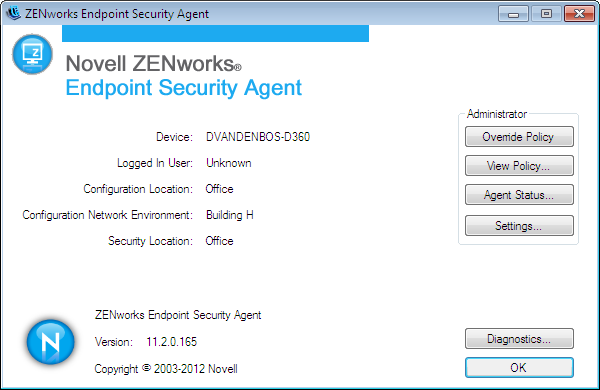
On the device, double-click the
 icon in the notification area, then click .
icon in the notification area, then click .
-
In the section, click to display the About dialog box.
-
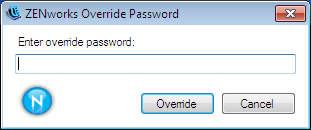
Click .
-
Specify the override password or the override password key, then click .
The View Policy dialog box includes a tab for each policy type.
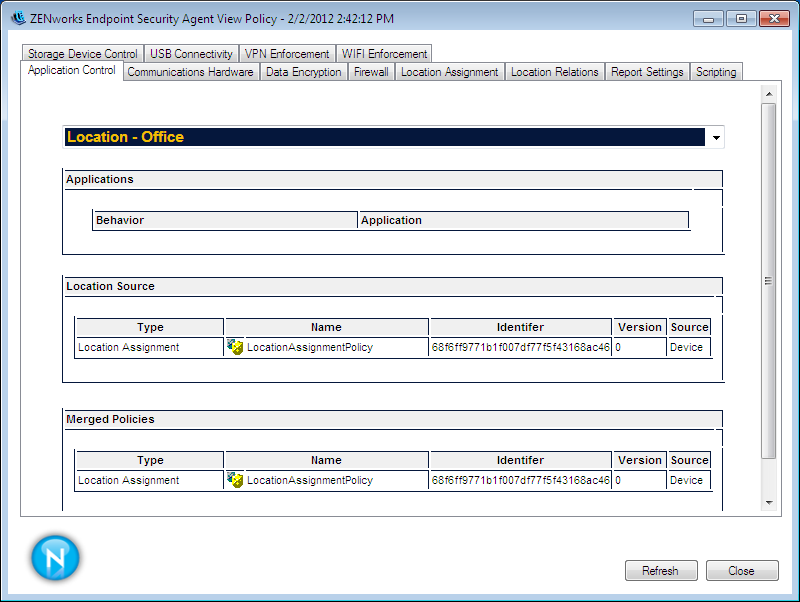
Each policy type includes the following:
Location list: All policies might not be available in all locations. Therefore, the effective policy can be different from one location to another. This list lets you select the location whose effective policy you want to view. The Data Encyption, Security Settings, VPN Enforcement, and Location Assignment policies are global-only policies; they do not have a location list because the effective policy is the same regardless of the location.
Policy settings: The location’s effective policy settings are displayed in one or more sections after the location list. These settings are a result of the ordering and merging rules used to determine the effective policy.
Location Source: This section lists both the Location Assignment policies that are the source of the currently selected location and the policies that are the source of the effective policy settings. The
 icon identifies a global policy. The
icon identifies a global policy. The  icon identifies a location-based policy. This section is not displayed for policy types that support only global policies (Data Encyption, Security Settings, VPN Enforcement, and Location Assignment).
icon identifies a location-based policy. This section is not displayed for policy types that support only global policies (Data Encyption, Security Settings, VPN Enforcement, and Location Assignment).
Merged Policies: This section lists all of the policies available for the available locations, regardless of the currently selected location (or no location for global-only policies). For example, if there are four available locations included in the Locations list, the policies that apply to any of the four locations are shown in the list. This list does not change when you change the location to view the effective policy for that location.
In addition to the tabs for each policy type, the tab displays the report settings that are currently effective on the device. The tab shows all available security locations for the device and the related network environments.
-
After you finish viewing the policy assignments, click to exit the dialog box.