1.1 Security Enforcement for Mobile Computers
Security is enforced both globally and by network location. Each location listed in a security policy determines the user's permissions in that network environment and determines which firewall settings are activated. The firewall settings determine which networking ports, network addresses, and applications are granted network access and how that access is permitted.
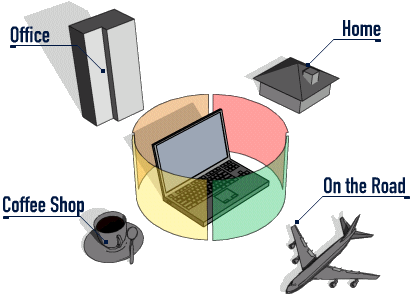
Figure 1-1 ESM Adjusts Security Settings Based on the Detected Network Environment
Normal operations of the Endpoint Security Client 3.5 are transparent to the user, after the network environments have been defined. Occasionally, Endpoint Security Client 3.5 protective measures can interrupt normal operation; when this occurs, messages and hyperlinks display to notify the user about the security policy, what protective steps have been taken, and refer them to additional information to help correct the issue.