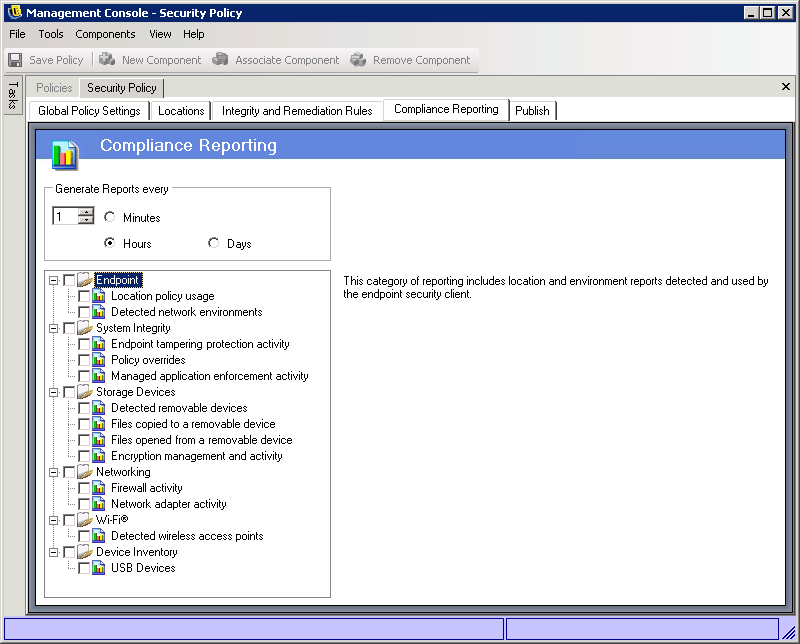
13.0 Configuring a Policy’s Compliance Reporting
Because of the level and access of the Security Client's drivers, virtually every transaction the endpoint performs can be reported. In addition, the Security Client can create system inventory reports that you can use for troubleshooting problems and creating security policies.
Reporting is not available when running the Stand-Alone Management Console
To determine which reports are generated and how often they are generated:
-
In the Management Console, open the policy by double-clicking the policy in the list.
-
Click the tab.
-
In the field, specify how often you want the Security Client to generate reports and upload them to the Policy Distribution Service.
-
Select the reports you want generated. The reports are described below:
Endpoint
-
Location policy usage: The Security Client reports all location policies enforced and the duration of that enforcement.
-
Detected network environments: The Security Client reports all detected network environment settings.
System Integrity
-
Endpoint tampering protection activity: The Security Client reports any attempts to tamper with it.
-
Policy overrides: The Security Client reports all attempts to initiate the administrative override on it.
-
Managed application enforcement activity: The Security Client reports all enforcement activities for managed applications.
Storage Devices
-
Detected removable devices: The Security Client reports all removable storage devices detected by the security client.
-
Files copied to a removable device: The Security Client reports files that are copied to a removable storage device.
-
Files opened from a removable device: The Security Client reports files that are opened from a removable storage device.
-
Encryption management and activity: The Security Client reports its encryption/decryption activity.
Networking
-
Firewall activity: The Security Client reports all traffic blocked by the firewall configured for the applied location policy. Enabling this report may result in large volumes of data being gathered
IMPORTANT:This data can overwhelm a database very quickly. A test of one Security Client reported 1,115 data uploads of blocked packets over a 20-hour period. You should run a monitoring and tuning period with a test Security Client in the deployment environment prior to wide-scale use of this report.
-
Network adapter activity: The Security Client reports all traffic activity for a managed network device.
Wi-Fi
-
Detected wireless access points: The Security Client reports all detected access points.
Device Inventory
-
USB Devices The Security Client reports all USB devices.