9.0 Creating a Security Policy
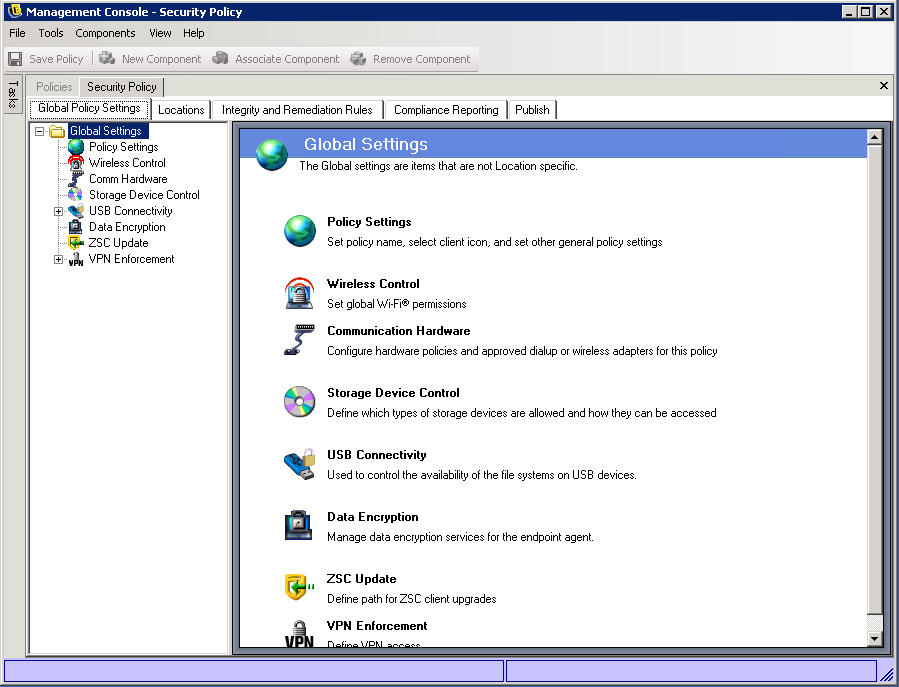
A security policy consists of global settings, location-specific settings, integrity rules, and compliance reporting settings:
-
Global settings: Global security settings are applied regardless of the endpoint device’s location. Some global settings determine general Security Client behavior, such as whether or not Client Self Defense is enabled or a password is required to uninstall the client. Other settings determine basic security policy, such as data encryption for fixed and removable drives.
-
Location-based settings: Location-based security settings are applied based upon the endpoint device’s current network environment. You can define multiple locations, such as Office, Home, and Airport, to provide the appropriate security at each locations. To define a location, you specify the network environment parameters (gateway servers, DNS servers, access points, etc.) that identify the location; when the endpoint device detects that its current location matches the defined location, the Security Client applies the security settings for that location.
You can use location-based settings to determine firewall security, wireless availability (including allowed access points, encryption security levels, and supported wireless adapters), communication hardware availability (IrDA, Bluetooth*, etc.), USB device connectivity, and storage device availability.
Many of the components, such as locations, network environments, and firewalls are saved as individual components so that you can reuse them.
-
Integrity and Remediation Rules: These rules provide the ability to verify that required software is running on the endpoint devices and then provide instant remediation procedures if the verification fails. For example, you might require that specific antivirus or spyware software be running.
-
Compliance Reporting: The Security Client gathers extensive information about the endpoint device’s activity. You can determine what information you want reported. For example, you can receive information about attempts to tamper with the Security Client, information about files copied to removable drives, and information about firewall activity. You can use this information to determine whether or not your security policies are configured correctly to enforce your organization’s paper policies.
To create a security policy:
-
Launch the Management Console and log in.
The Management Console launches with the list displayed. Policies you create are listed here so that you can open and modify them as necessary.

-
Click > .
-
Specify the name for the new policy, then click .
-
Configure and distribute the policy by referring to the information and instructions in the following sections: