3.3 Building Novell AppArmor Profiles with the YaST GUI
Open the YaST GUI displays from the SUSE menu with . Novell AppArmor opens in the YaST interface as shown below:
NOTE: You can also access the YaST GUI by opening a terminal window, logging in as root, and entering yast2.
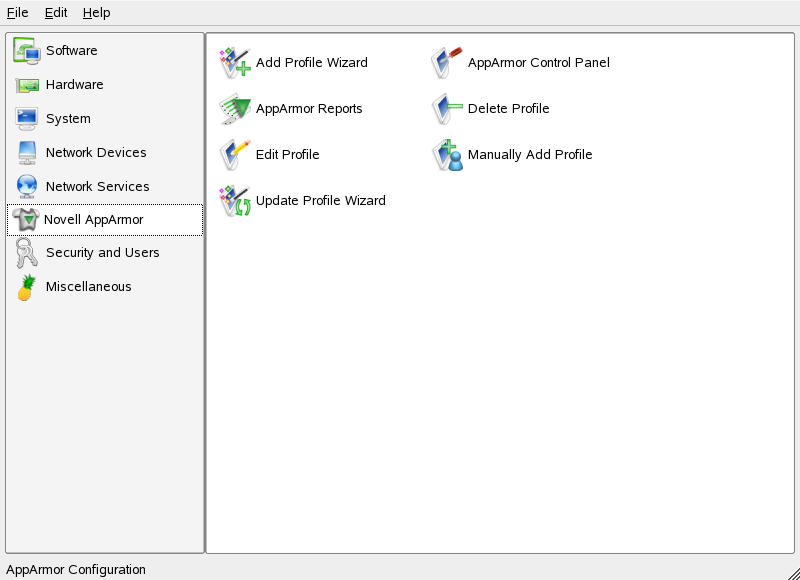
In the right frame, you see several Novell AppArmor option icons. If Novell AppArmor does not display in the left frame of the YaST window or if the Novell AppArmor icons do not display, you might want to reinstall Novell AppArmor. Refer to the Novell AppArmor Powered by Immunix 1.2 Installation and QuickStart Guide if you need further installation instructions. The following actions are available from Novell AppArmor.
Click one of the following Novell AppArmor icons and proceed to the section referenced below:
- Add Profile Wizard
-
For detailed steps, refer to Section 3.3.1, Adding a Profile Using the Wizard.
- Manually Add Profile
-
Add a Novell AppArmor profile for an application on your system without the help of the wizard. For detailed steps, refer to Section 3.3.2, Manually Adding a Profile.
- Edit Profile
-
Edits an existing Novell AppArmor profile on your system. For detailed steps, refer to Section 3.3.3, Editing a Profile.
- Delete Profile
-
Deletes an existing Novell AppArmor profile from your system. For detailed steps, refer to Section 3.3.4, Deleting a Profile.
- Update Profile Wizard
-
For detailed steps, refer to Section 3.3.5, Updating Profiles from Syslog Entries.
- AppArmor Reports
-
For detailed steps, refer to Section 4.3, Reports.
- AppArmor Control Panel
-
For detailed steps, refer to Section 3.3.6, Managing Novell AppArmor and Security Event Status.
3.3.1 Adding a Profile Using the Wizard
The is designed to set up Novell AppArmor profiles using the Novell AppArmor profiling tools, genprof (Generate Profile) and logprof (Update Profiles From Learning Mode Log File). For more information about these tools, refer to Section 3.5.3, Summary of Profiling Tools.
-
Stop the application before profiling it to ensure that the application start-up is included in the profile. To do this, make sure that the application or daemon is not running prior to profiling it.
For example, enter /etc/init.d/PROGRAM stop in a terminal window while logged in as root, replacing PROGRAM is the name of the program to profile.
-
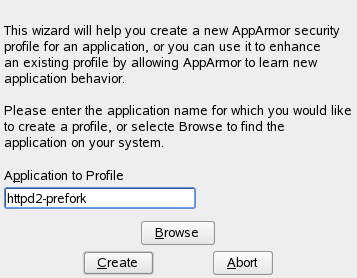
If you have not done so already, in the YaST GUI, click .
-
Enter the name of the application or browse to the location of the program.
-
Click . This runs a Novell AppArmor tool named autodep, which performs a static analysis of the program to profile and loads an approximate profile into Novell AppArmor module. For more information about autodep, refer to autodep.
The window opens.
In the background, Novell AppArmor also sets the profile to learning mode. For more information about learning mode, refer to Complain or Learning Mode.
-
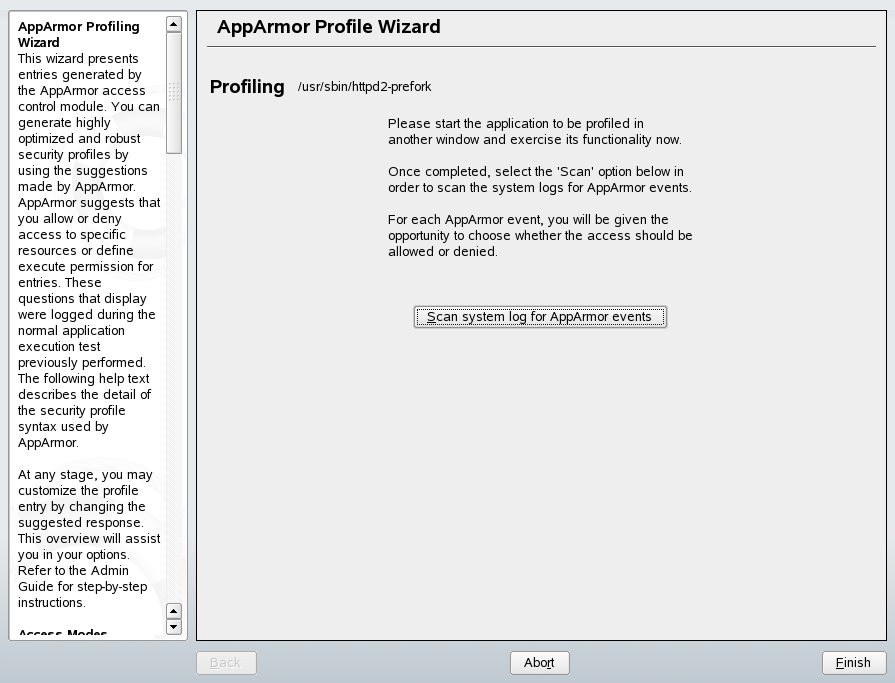
Run the application that is being profiled.
-
Perform as many of the application functions as possible so learning mode can log the files and directories to which the program requires access to function properly.
-
Click to parse the learning mode log files. This generates a series of questions that you must answer to guide the wizard in generating the security profile.
NOTE: If requests to add hats appear, proceed to Section 5.0, Profiling Your Web Applications Using ChangeHat Apache.
The questions fall into two categories:
-
A resource is requested by a profiled program that is not in the profile (see Figure 3-1). The learning mode exception requires you to allow or deny access to a specific resource.
-
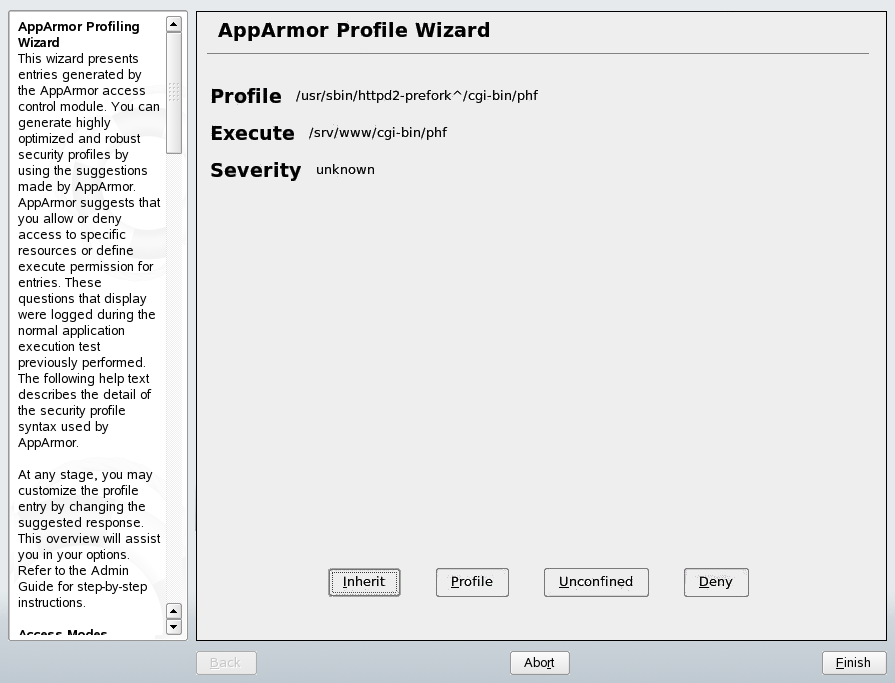
A program is executed by the profiled program and the security domain transition has not been defined (see Figure 3-2). The learning mode exception requires you to define execute permissions for an entry.
Each of these cases results in a series of questions that you must answer to add the resource to the profile or to add the program into the profile. The following two figures show an example of each case. Subsequent steps describe your options in answering these questions.
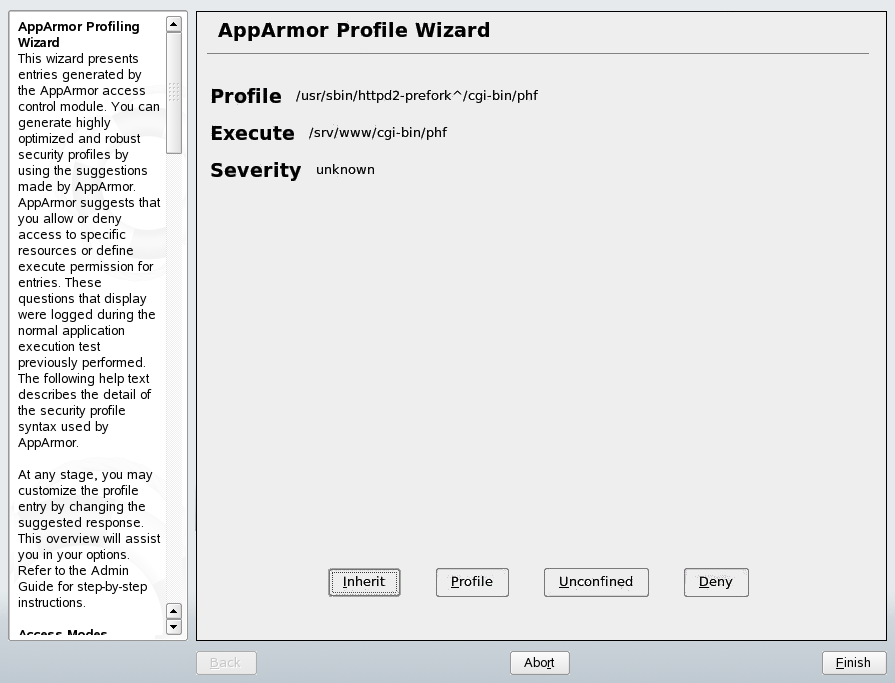
The window opens.
Figure number="3-1" Learning Mode Exception: Controlling Access to Specific Resources
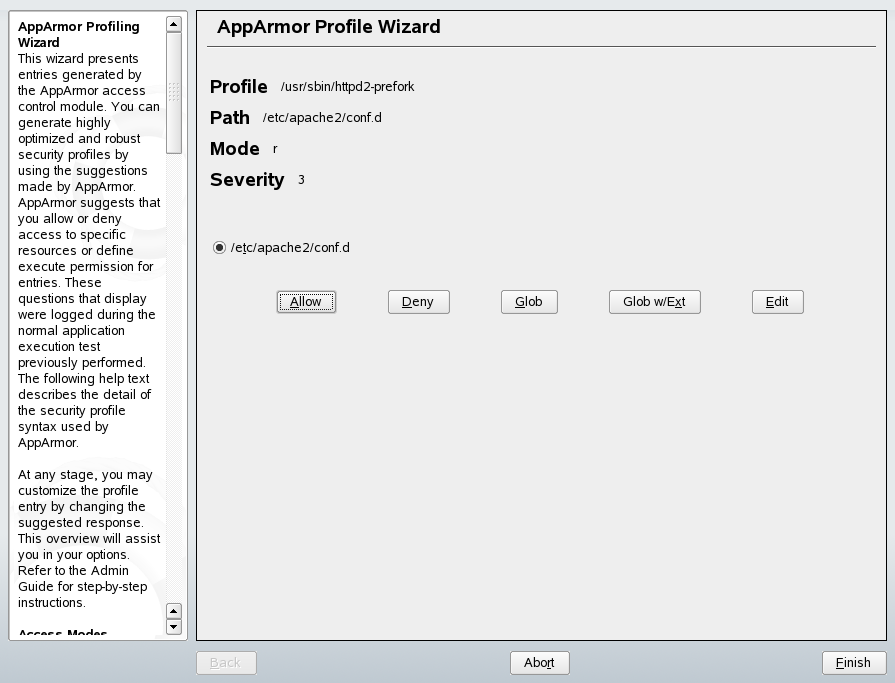
Figure number="3-2" Learning Mode Exception: Defining Execute Permissions for an Entry
-
-
The begins suggesting directory path entries that have been accessed by the application you are profiling (as seen in Figure 3-1) or requiring you to define execute permissions for entries (as seen in Figure 3-2).
-
For Learning Mode Exception: Controlling Access to Specific Resources: From the following options, select the one that satisfies the request for access, which could be a suggested include, a particular globbed version of the path, or the actual pathname. Note that all of these options are not always available.
- #include
-
The section of a Novell AppArmor profile that refers to an include file. Include files procure access permissions for programs. By using an include, you can give the program access to directory paths or files that are also required by other programs. Using includes can reduce the size of a profile. It is good practice to select includes when suggested.
- Globbed Version
-
Accessed by clicking as described in the next step. For information about globbing syntax, refer to Section 3.6, Pathnames and Globbing.
- Actual Pathname
-
Literal path that the program needs access to so that it can run properly.
-
For Learning Mode Exception: Defining Execute Permissions for an Entry: From the following options, select the one that satisfies the request for access.
- Inherit
-
Stay in the same security profile (parent's profile).
- Profile
-
Requires that a separate profile exists for the executed program.
- Unconfined
-
Executes the program without a security profile.
WARNING:Unless absolutely necessary, do not run unconfined. Choosing the option executes the new program without any protection from AppArmor.
-
-
After you select a directory path, you need to process it as an entry into the Novell AppArmor profile by clicking or . If you are not satisfied with the directory path entry as it is displayed, you can also or it.
The following options are available to process the learning mode entries and to build the profile:
- Allow
-
Grants the program access to the specified directory path entries. The suggests file permission access. For more information about this, refer to Section 3.7, File Permission Access Modes.
- Deny
-
Click to prevent the program from accessing the specified directory path entries.
- Glob
-
Clicking this modifies the directory path (by using wild cards) to include all files in the suggested entry directory. Double-clicking it grants access to all files and subdirectories beneath the one shown.
For more information about globbing syntax, refer to Section 3.6, Pathnames and Globbing.
- Glob w/Ext
-
Modifies the original directory path while retaining the filename extension. A single click causes /etc/apache2/file.ext to become /etc/apache2/*.ext, adding the wild card (asterisk) in place of the file name. This allows the program to access all files in the suggested directories that end with the .ext extension. When you double-click it, access is granted to all files (with the particular extension) and subdirectories beneath the one shown.
- Edit
-
Enables editing of the highlighted line. The new (edited) line appears at the bottom of the list.
- Abort
-
Aborts logprof, dumping all rule changes entered so far and leaving all profiles unmodified.
- Finish
-
Closes logprof, saving all rule changes entered so far and modifying all profiles.
Click or for each learning mode entry. These help build the Novell AppArmor profile.
NOTE: The number of learning mode entries corresponds to the complexity of the application.
Repeat the previous steps if you need to execute more functionality of your application.
When you are done, click . In the following pop-up, click to exit the . The profile is saved and loaded into the Novell AppArmor module.
3.3.2 Manually Adding a Profile
Novell AppArmor enables you to create a Novell AppArmor profile by manually adding entries into the profile. You simply need to select the application for which to create a profile, then add entries.
-
To add a profile, open . The Novell AppArmor interface opens.
-
In , click (see Figure 3-3).
Figure number="3-3" Manually Adding a Profile: Select Application
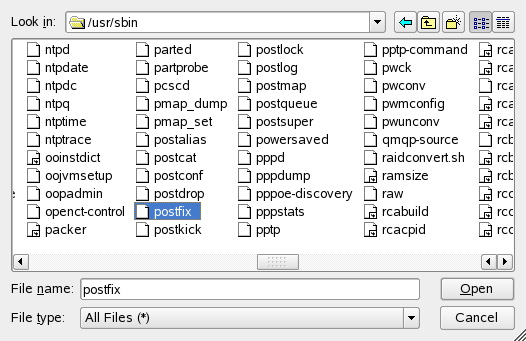
-
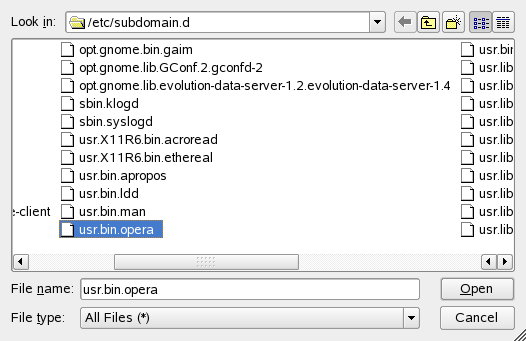
Browse your system to find the application for which to create a profile.
-
When you find the profile, select it and click . A basic, empty profile appears in the window.
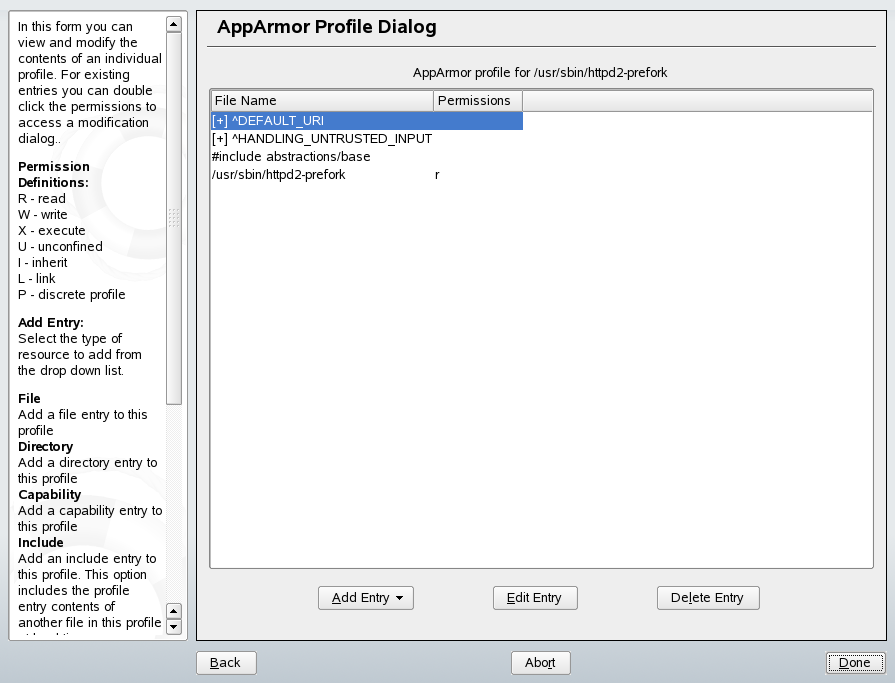
-
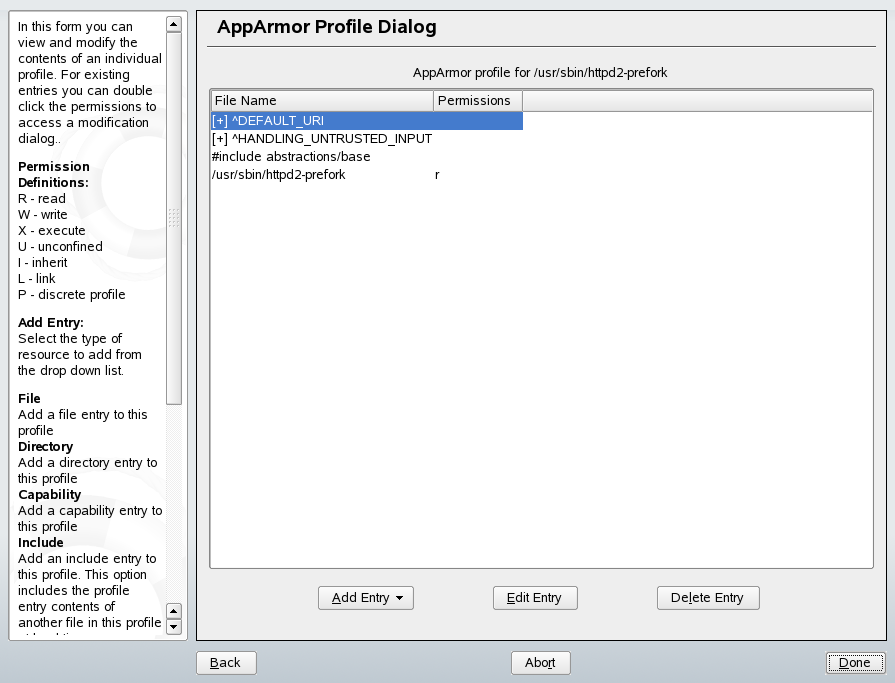
In the window, you can add, edit, or delete Novell AppArmor profile entries by clicking the corresponding buttons and referring to the following sections: Adding an Entry, Editing an Entry, or Editing an Entry.
-
When you are finished, click .
Adding an Entry
This section explains the option that can be found in Section 3.3.2, Manually Adding a Profile or Section 3.3.3, Editing a Profile. When you select , a drop-down list displays the types of entries you can add to the Novell AppArmor profile.
-
From the list, select one of the following:
- File
-
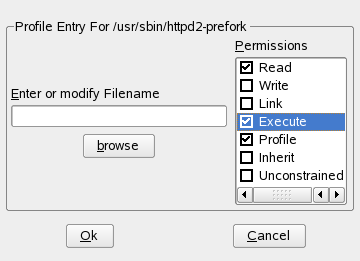
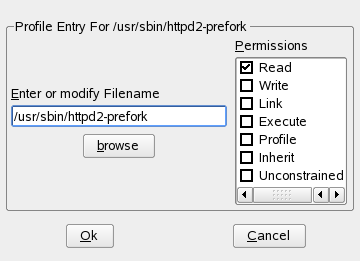
In the pop-up window, specify the absolute path of a file, including the type of access permitted. When finished, click .
You can use globbing if necessary. For globbing information, refer to Section 3.6, Pathnames and Globbing. For file access permission information, refer to Section 3.7, File Permission Access Modes.
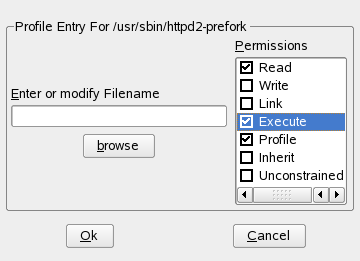
- Directory
-
In the pop-up window, specify the absolute path of a directory, including the type of access permitted. You can use globbing if necessary. When finished, click .
For globbing information, refer to Section 3.6, Pathnames and Globbing. For file access permission information, refer to Section 3.7, File Permission Access Modes.
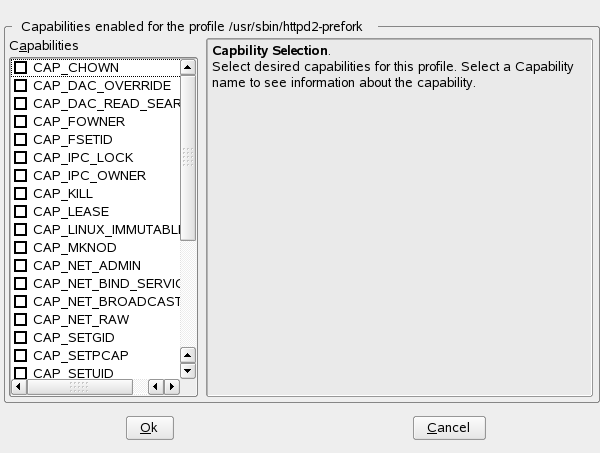
- Capability
-
In the pop-up window, select the appropriate capabilities. These are statements that enable each of the 32 POSIX.1e capabilities. Refer to Section 3.1.1, Breaking a Novell AppArmor Profile into Its Parts for more information about capabilities. When finished making your selections, click .
- Include
-
In the pop-up window, browse to the files to use as includes. Includes are directives that pull in components of other Novell AppArmor profiles to simplify profiles. For more information, refer to Section 3.1.2, #include.
Editing an Entry
This section explains the option that can be found in Section 3.3.2, Manually Adding a Profile or Section 3.3.3, Editing a Profile. When you select , the file browser pop-up window opens. From here, you can edit the selected entry.
In the pop-up window, specify the absolute path of a file, including the type of access permitted. You can use globbing if necessary. When finished, click .
For globbing information, refer to Section 3.6, Pathnames and Globbing. For file access permission information, refer to Section 3.7, File Permission Access Modes.
Deleting an Entry
This section explains the option that can be found in the Section 3.3.2, Manually Adding a Profile or Section 3.3.3, Editing a Profile. When you select an entry then select , Novell AppArmor removes the profile entry that you have selected.
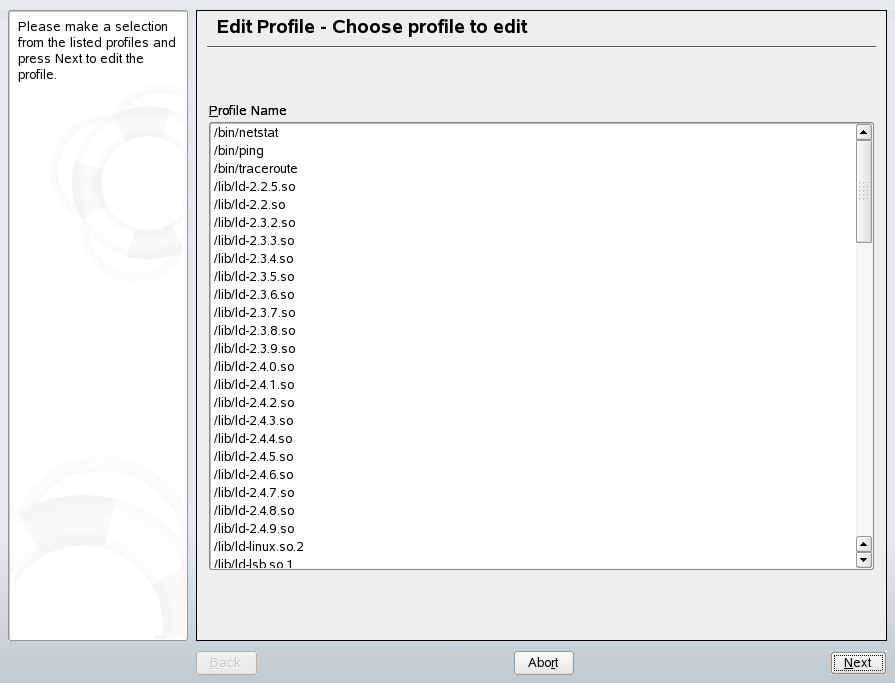
3.3.3 Editing a Profile
Novell AppArmor enables you to manually edit Novell AppArmor profiles by adding, editing, or deleting entries. You simply need to select the profile then add, edit, or delete entries. To edit a profile, follow these steps:
-
Open .
-
In , click . The window opens.
-
From the list of profiled programs, select the profile to edit.
-
Click . The window displays the profile.
-
In the window, you can add, edit, or delete Novell AppArmor profile entries by clicking the corresponding buttons and referring to the following sections: Adding an Entry, Editing an Entry, or Deleting an Entry.
-
When you are finished, click .
-
In the pop-up that appears, click to confirm your changes to the profile.
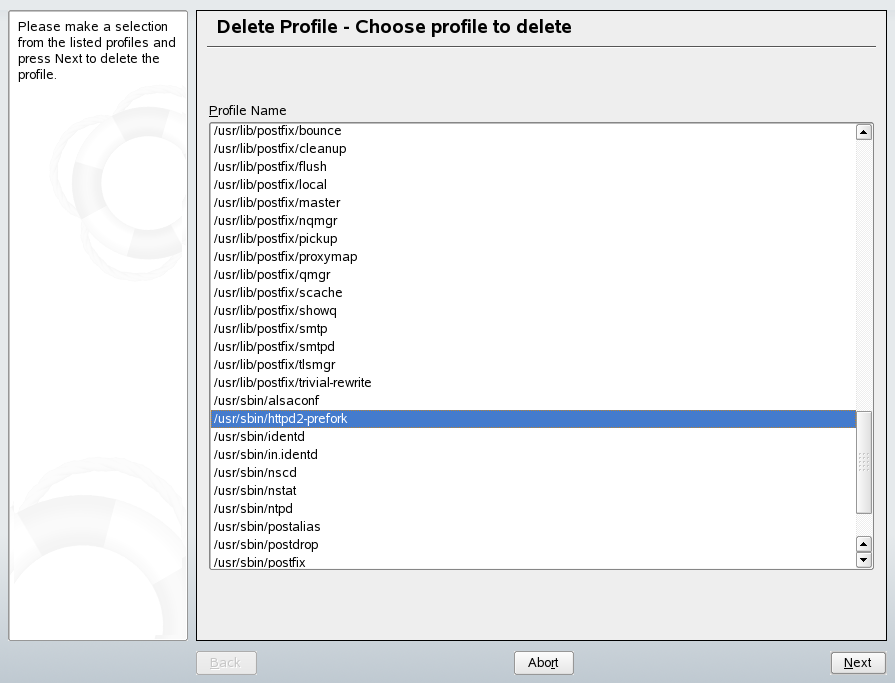
3.3.4 Deleting a Profile
Novell AppArmor enables you to delete a Novell AppArmor profile manually. You simply need to select the application for which to delete a profile then delete it as follows:
-
Open the . The Novell AppArmor interface displays.
-
In , click icon. The window opens.
-
Select the profile to delete.
-
Click .
-
In the pop-up that opens, click to delete the profile.
3.3.5 Updating Profiles from Syslog Entries
The Novell AppArmor Profile wizard uses logprof, the tool that scans log files and enables you to update profiles. logprof tracks messages from the Novell AppArmor module that represent exceptions for all profiles running on your system. These exceptions represent the behavior of the profiled application that is outside of the profile definition for the program. You can add the new behavior to the relevant profile by selecting the suggested profile entry.
-
Open . The Novell AppArmor interface displays.
-
In , click . The window displays.


Running the (logprof) parses the learning mode log files. This generates a series of questions that you must answer to guide logprof to generate the security profile.
The questions fall into two categories:
-
A resource is requested by a profiled program that is not in the profile (see Figure 3-4).
-
A program is executed by the profiled program and the security domain transition has not been defined (see Figure 3-5).
Each of these cases results in a question that you must answer that enables you to add the resource or program into the profile. The following two figures show an example of each case. Subsequent steps describe your options in answering these questions.
Figure number="3-4" Learning Mode Exception: Controlling Access to Specific Resources
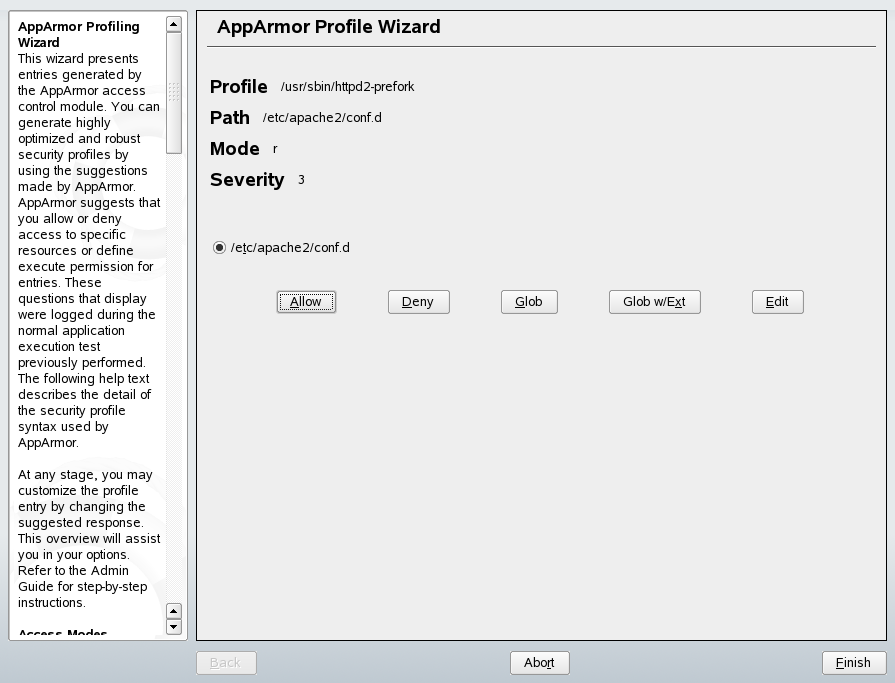
Figure number="3-5" Learning Mode Exception: Defining Execute Permissions for an Entry
-
-
logprof begins suggesting directory path entries that have been accessed by the application you are profiling (as seen in Figure 3-4) or requiring you to define execute permissions for entries (as seen in Figure 3-5).
-
For Figure 3-4: From the following options, select the one that satisfies the request for access, which could be a suggested include, a particular globbed version of the path, or the actual pathname. Note that all of these options are not always available.
- #include
-
The section of a Novell AppArmor profile that refers to an include file. Include files fetch access permissions for programs. By using an include, you can give the program access to directory paths or files that are also required by other programs. Using includes can reduce the size of a profile. It is good practice to select includes when suggested.
- Globbed Version
-
Accessed by clicking as described in the next step. For information about globbing syntax, refer to Section 3.6, Pathnames and Globbing.
- Actual Pathname
-
This is the literal path to which the program needs access so that it can run properly.
-
For Figure 3-5: Select the one that satisfies the request for access by choosing one of the following:
- Inherit
-
stay in the same security profile (parent's profile)
- Profile
-
requires that a separate profile exists for the executed program
- Unconfined
-
program executed without a security profile
WARNING:Unless absolutely necessary, do not run unconfined. Choosing the option executes the new program without any protection from AppArmor.
-
-
After you select a directory path, you need to process it as an entry into the Novell AppArmor profile by clicking or . If you are not satisfied with the directory path entry as it is displayed, you can also or it.
The following options are available to process the learning mode entries and to build the profile:
- Allow
-
Grant the program access to the specified directory path entries. The suggests file permission access. For more information about this, refer to Section 3.7, File Permission Access Modes.
- Deny
-
Click to prevent the program from accessing the specified directory path entries.
- Glob
-
Clicking this modifies the directory path (by using wild cards) to include all files in the suggested entry directory. Double-clicking it grants access to all files and subdirectories beneath the one shown.
For more information about globbing syntax, refer to Section 3.6, Pathnames and Globbing.
- Glob w/Ext
-
Modify the original directory path while retaining the filename extension. A single click causes /etc/apache2/file.ext to become /etc/apache2/*.ext, adding the wild card (asterisk) in place of the filename. This allows the program to access all files in the suggested directories that end with the .ext extension. When you double-click it, access is granted to all files (with the particular extension) and subdirectories beneath the one shown.
- Edit
-
Enable editing of the highlighted line. The new (edited) line appears at the bottom of the list.
- Abort
-
Abort logprof, dumping all rule changes entered so far and leaving all profiles unmodified.
- Finish
-
Close logprof, saving all rule changes entered so far and modifying all profiles.
Click or for each learning mode entry. These help build the Novell AppArmor profile.
NOTE: The number of learning mode entries corresponds to the complexity of the application.
Repeat the previous steps if you need to execute more functionality of your application.
When you are done, click . In the following pop-up, click to exit the . The profile is saved and loaded into the Novell AppArmor module.
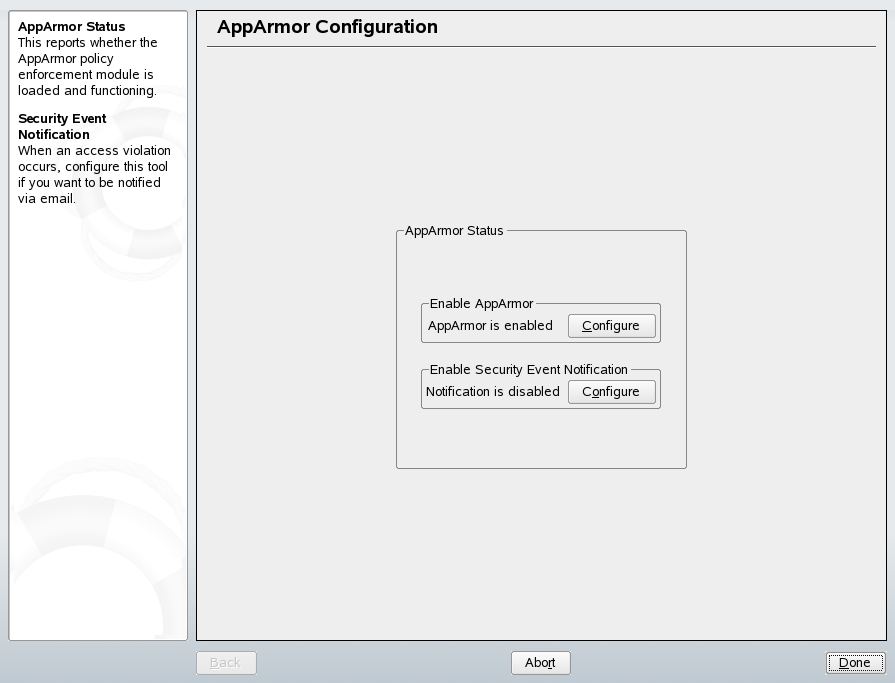
3.3.6 Managing Novell AppArmor and Security Event Status
Novell AppArmor enables you to change the status of Novell AppArmor and configure event notification.
- Changing Novell AppArmor Status
-
You can change the status of Novell AppArmor by enabling or disabling it. Enabling Novell AppArmor protects your system from potential program exploitation. Disabling Novell AppArmor, even if your profiles have been set up, removes protection from your system.
- Configuring Event Notification
-
You can determine how and when you are notified when system security events occur.
NOTE: You must set up a mail server on your SUSE Linux server that can send outgoing mail using the single mail transfer protocol (smtp). For example, postfix or exim, in order for event notification to work.
To either configure event notification or change the status of Novell AppArmor, perform the following steps:
-
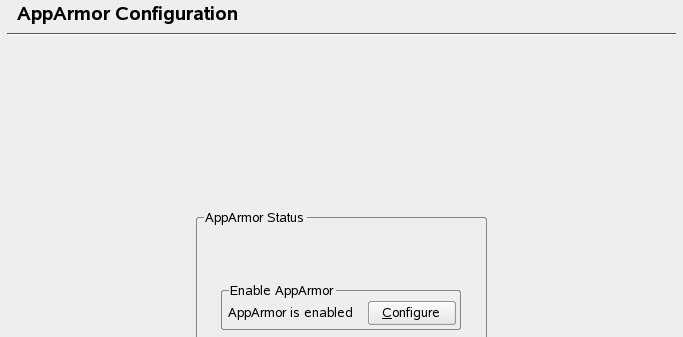
When you click , the window appears as shown below:
-
From the screen, determine whether Novell AppArmor and security event notification are running by looking for a status message that reads .
-
To change the status of Novell AppArmor, continue as described in Changing Novell AppArmor Status.
-
To configure security event notification, continue as described in Section 4.2.2, Configuring Security Event Notification.
-
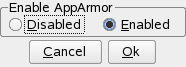
Changing Novell AppArmor Status
When you change the status of Novell AppArmor, you set it to enable or disable. When Novell AppArmor is enabled, it is installed, running and enforcing the Novell AppArmor security policies.
-
To enable Novell AppArmor, open . The Novell AppArmor main menu opens.
-
In the main menu, click . The window appears.
-
In the section of the window, click . The dialog box opens.
-
Enable Novell AppArmor by selecting or disable Novell AppArmor by selecting . Then click .
-
Click in the window.
-
Click in the YaST Control Center.