ZENworks Patch Updates
After a version of ZENworks is released, if any enhancements or bug fixes are made based on customers’ request, they are provided as patch updates. This document lists the released patches and provides instructions about the sequence in which patches have to be applied on the devices:
1.0 What is a Patch?
A patch is an update that is installed into an existing product and a fix between the releases. A patch can fix bugs, install drivers, address security vulnerabilities, or address stability issues. The patches can also be referred to as FTF (Field Test File), which requires no testing and can be directly deployed in the production environment.
1.1 What is a Server Patch?
The server patches are released to improve the security, fix bugs or improve the performance of the product running on the server. The release version is considered the base server patch. If any server patch is baselined, then that becomes the base for future server patches. Server patches are cumulative.
1.2 What is Baseline Patch?
A baseline patch is a pre-requisite patch that is required for all future patches.
When the patch will be Baselined?
-
When a patch should be applied mandatorily such as a patch that addresses security vulnerability (example 20.2.0.998 FTF).
-
To limit the size of the patch.
Once a patch is baselined, subsequent patches will be cumulative.
1.3 What is Agent Patch?
Similar to server patches, agent patches are released to improve the efficiency of the agents. Unlike server patches, agent patches are not cumulative.
1.4 Dependencies Between Agent and Server Patches
Depending on customer needs or due to binary dependencies as per implementation, agent patches might be dependent on the server patch, which implies that the server patch should be installed before installing the agent patch. If a server patch is required to be applied, then the readme provided with the server and agent patches will have cross-references to each other.
2.0 Downloading and Installing Patches
All the released patches or FTFs (Field Test Files) can be downloaded either from Software Licenses and Downloads (SLD) or KM Viewer.
Each patch that is released will include a Readme. The readme section will include instructions to install a patch.
3.0 Understanding the Patching Sequence
In this document, the release version is considered as the base patch. If any server patch is baselined, then that patch becomes the base patch for future server patches.
As a best practice, it is always recommended to install the related server patch and then install the agent patch. Some patches, though they will be applied on servers, will be delivered as agent patches. For example, ZeUS.
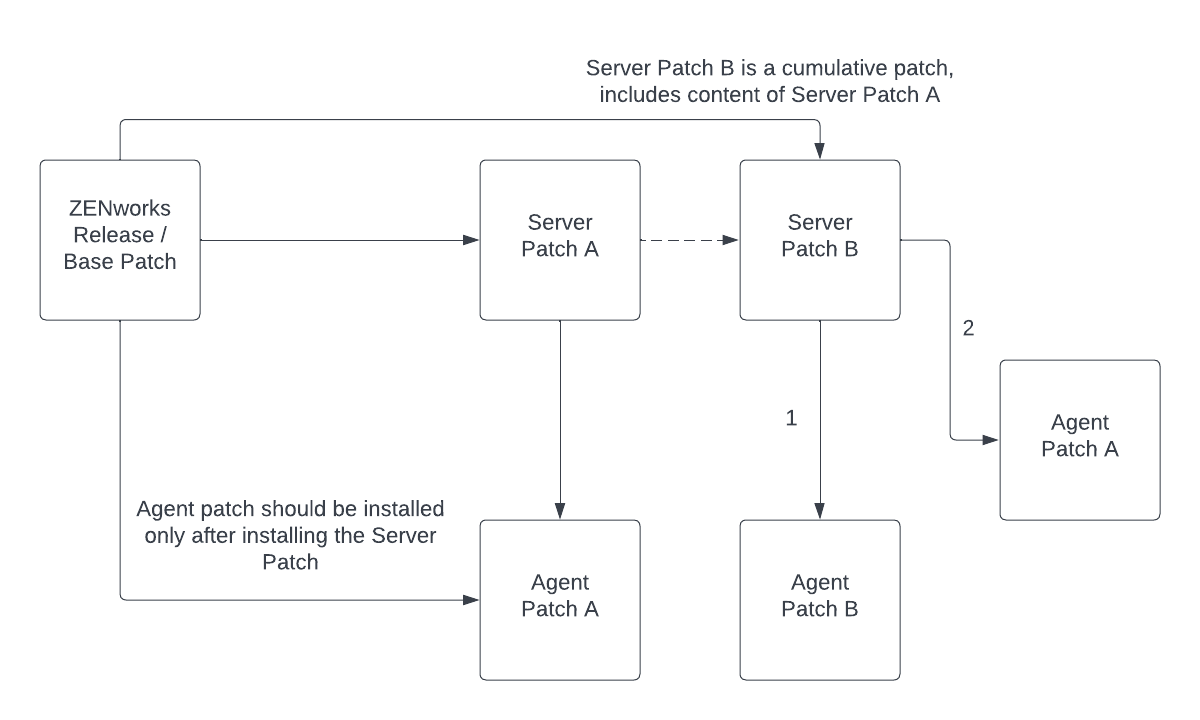
The above chart represents the sequence in which patches have to be applied. After the ZENworks release, it will be considered as a base patch (Server Base Patch). After a next few days, Server Patch A is released. Again, after some more days, Server Patch B is released. Now, Server Patch B is a cumulative patch of Server Patch A, which implies that Server Patch B includes all the content from Server Patch A. Hence, Server Patch B can be installed without having to install Server Patch A prior to it.
In the above chart, Agent Patch A and Agent Patch B are agent patches. To install the agent patches, ensure that you have already installed the dependent server patch. In this scenario, Agent Patch A should be installed only after installing Server Patch A, or it can be installed after installing Server Patch B. However, if Agent Patch B is released before you install Agent Patch A, then you can install the agent patches in any order.
The agent patches are non-cumulative while server patches are cumulative.
4.0 Patch Updates
This section provides information on the patches that are released. After installing the server patch, install the related agent patch specified in the table, if applicable.
4.1 Server Patches
This section lists all the server patches that are released for ZENworks 23.3. As server patches are cumulative, you can install the latest patch that is released.
|
Release Date |
Patch Name |
Download Link and Patch File Name |
Prerequisite Patch Details |
Related Agent Patch |
|---|---|---|---|---|
|
December, 2023 |
Server FTF 335 on ZENworks 23.3 |
ZCM_23.3.0_FTF_Server_335.zip |
NA |
NA |
|
September, 2023 |
Server FTF 334 on ZENworks 23.3 |
ZCM_23.3.0_FTF_Server_334.zip (Latest) |
NA |
NA |
4.2 Agent Patches
Unlike server patches, agent patches are not cumulative. Hence, agent patches should be installed in the following release order.
NOTE:Ensure that the agent services are not running while installing the agent patches.
4.3 Standalone Patches
A standalone patch is a type of update that can be applied independently. It is designed to fix a specific issue or vulnerability and can be installed without the need to update or upgrade the entire system. Standalone patches are typically small and focused and are often released in response to a bug that needs to be addressed quickly.
4.4 Imaging Driver Updates
ZENworks Imaging driver updates are designed to enhance the functionality, compatibility, and performance of ZENworks imaging, making it easier for IT administrators to manage and deploy system images. ZENworks provides driver update packages that can be imported into ZENworks. These packages contain the latest drivers for supported hardware devices, allowing administrators to easily update driver libraries to ensure that when creating or deploying system images, the most current drivers are available.
4.5 Appliance Patches
Appliance patches are a type of update that is specifically designed for ZENworks Appliance. These patches are used to update and maintain the ZENworks Appliance, including the ZENworks server, operating system, and other components. These patches typically include bug fixes, security updates, and other improvements to the software.
For more information on applying Appliance patches, see Online Update in the ZENworks Appliance Deployment and Administration Reference.
4.6 Security Patches
Security patches are software updates that fix vulnerabilities that could be exploited by malicious attackers. These vulnerabilities might allow attackers to gain unauthorized access to the system, steal sensitive information, or carry out other actions.
Security patches are usually released when a security flaw or vulnerability is detected. These patches are typically released on a regular schedule or as soon as a critical vulnerability is detected.
Security patches are released to address security vulnerabilities, whereas other patches to improve performance, fix bugs, or add new features. Security patches are high-priority updates that should be installed immediately to ensure security.
4.7 Product Recognition Update (PRU)
A Product Recognition Update (PRU) is a type of software update that is used to identify and classify software products on managed devices. After applying, the PRU enables ZENworks to recognize and classify new software products that may not have been previously identified.
The PRU is important as it enables ZENworks to accurately identify and manage all software products on a managed device, including those that may be less common or not well known. This allows administrators to effectively monitor and manage software license compliance, security vulnerabilities, and software updates for all devices on the network.
PRUs are released regularly and are designed to be compatible with specific versions of ZENworks. It is important to ensure that the correct PRU is downloaded and applied to the appropriate ZENworks server or zone to ensure proper identification and management of software products.
For more information, see Downloading and Installing the PRU.
|
Released Date |
PRU Details |
Download Link and File Name |
|---|---|---|
|
December, 2023 |
ZCM and ZAM 23.3 Dec 2023 Product Recognition Update |
23.3.Dec2023pru.zip |
|
November, 2023 |
ZCM/ZAM 23.3 NOV 2023 PRU |
23.3.Nov2023pru.zip |
|
October, 2023 |
ZCM/ZAM 23.3 OCT 2023 PRU |
23.3.Oct2023pru.zip |
|
September, 2023 |
ZCM/ZAM 23.3 Sep 2023 PRU |
23.3.Sep2023pru.zip |
5.0 Legal Notice
For information about legal notices, trademarks, disclaimers, warranties, export and other use restrictions, U.S. Government rights, patent policy, and FIPS compliance, see https://www.microfocus.com/en-us/legal.
© Copyright 2008 - 2023 Open Text.
The only warranties for products and services of Micro Focus and its affiliates and licensors (Open Text) are set forth in the express warranty statements accompanying such products and services. Nothing herein should be construed as constituting an additional warranty. Micro Focus shall not be liable for technical or editorial errors or omissions contained herein. The information contained herein is subject to change without notice.