9.0 Creating Security Policies
The following instructions explain how to create a new security policy by using the Create New Policy Wizard. In addition to using the wizard, you can create policies by:
-
Copying an existing security policy. All original system requirements, details, and settings are copied to the new policy. You can then make any desired modifications to the new policy. See Section 16.2, Copying a Policy.
-
Creating a Sandbox version of an existing security policy and then publishing it as a new policy. For information, see Section 15.2, Publishing a Sandbox Version.
-
Importing a policy from another Management Zone. All original system requirements, details, and settings (if applicable) are imported to the new policy. For information, see Section 19.0, Importing and Exporting Policies.
|
|
To create a security policy by using the Create New Policy Wizard:
-
In ZENworks Control Center, click to display the Policies page.
-
In the Policies panel, click > to launch the Create New Policy Wizard.
-
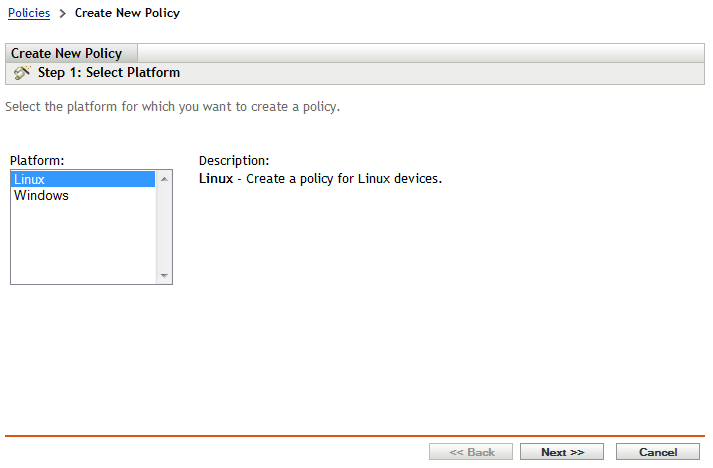
On the Select Platform page, select , then click .
-
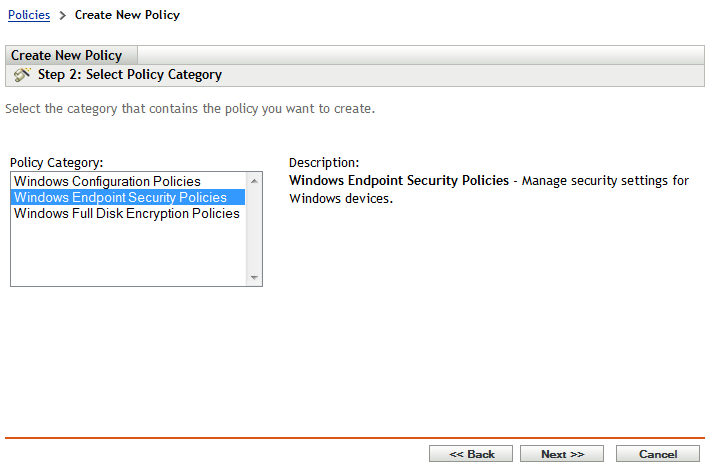
On the Select Policy Category page, select , then click .
-
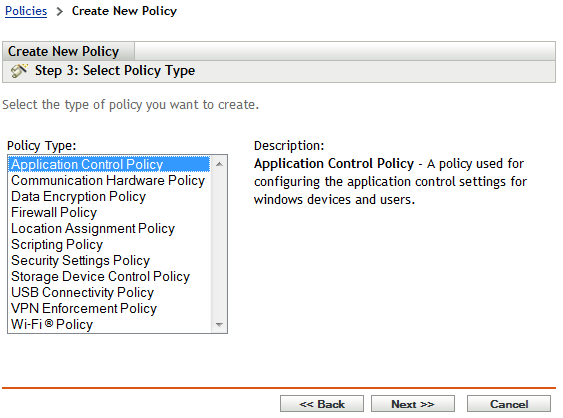
On the Select Policy Type page, select the type of policy you want to create, then click .
Application Control Policy: Blocks execution of applications or denies Internet access to applications. You specify the applications that are blocked or denied Internet access.
Communication Hardware Policy Disables wireless adapters, blocks wireless connections, controls connections to wireless access points, and so forth.
Data Encryption Policy: Enables data encryption of files on fixed disks and removable storage devices. With fixed disks, you specify the folders (referred to as Safe Harbor folders) that provide encryption; all other fixed disk folders are unaffected.
Firewall Policy: Controls network connectivity by disabling ports, protocols, and network addresses (IP and MAC).
Location Assignment Policy: Provides a list of predefined locations for the Endpoint Security Agent. ZENworks Endpoint Security Management lets you associate different security policies with different locations. For example, you might have an Office location and a Remote Office location; you also have a default Unknown location. The Endpoint Security Agent evaluates its current network environment to see if it matches any of the locations included in the Location Assignment policy. If so, the security policies associated with the matched location are applied. If not, the security policies associated with the Unknown location are applied.
Security Settings Policy: Protects the Endpoint Security Agent from being tampered with and uninstalled.
This policy is not used with ZENworks 11 SP2 Endpoint Security Agents. The ZENworks 11 SP2 Endpoint Security Agent’s security settings are not applied as a policy; instead, they are applied as ZENworks Agent settings (ZENworks Control Center > Configuration > Management Zone Settings > Device Management > ZENworks Agent).
This policy is retained in ZENworks 11 SP2 to provide support for devices that are still running the ZENworks 11 or ZENworks 11 SP1 Endpoint Security Agent. Those versions of the agent continue to use the Security Settings policy.
Storage Device Control Policy: Controls access to CD/DVD drives, floppy drives, and removable storage drives. Each storage device type is configured individually, which means that you can disable some and enable others.
USB Connectivity Policy: Controls access to USB devices such as removable storage devices, printers, input devices (keyboards, mice, etc). You can specify individual devices or groups of devices. For example, you can disable access to a specific printer and enable access to all SanDisk USB devices.
VPN Enforcement Policy: Enforces a VPN connection based on the device’s location. For example, if the device’s location is unknown, you can force a VPN connection through which all Internet traffic is routed.
Wi-Fi Policy: Lets you disable wireless adapters, block wireless connections, control connections to wireless access points, and so forth.
-
On the Define Details page, specify a name for the policy, select the folder in which to place the policy, then click .
The name must be unique among all other policies located in the selected folder. For additional requirements, see Section C.0, Naming Conventions in ZENworks Control Center.
-
(Conditional) If the Configure Inheritance and Location Assignments page is displayed, configure the following settings, then click .
Inheritance: Leave the setting selected if you want to enable this policy to inherit settings from same-type policies that are assigned higher in the policy hierarchy. For example, if you assign this policy to a device and another policy (of the same type) to the device’s folder, enabling this option allows this policy to inherit settings from the policy assigned to the device’s folder. Deselect the setting if you don’t want to allow this policy to inherit policy settings.
Location Assignments: Policies can be global or location-based. A global policy is applied regardless of location. A location-based policy is applied only when the device detects that it is within the locations assigned to the policy.
Select whether this is a global or location-based policy. If you select location-based, click , select the locations to which you want to assign the policy, then click to add them to the list.
-
Configure the policy-specific settings, then click until you reach the Summary page.
For information about a policy’s settings, you can click > in ZENworks Control Center, or you can see Section A.0, Security Policy Settings.
-
On the Summary page, review the information to make sure it is correct. If it is incorrect, click the button to revisit the appropriate wizard page and make changes. If it is correct, select either of the following options (if desired), then click .
-
Create as Sandbox: Select this option to create the policy as a Sandbox version. The Sandbox version is isolated from users and devices until you publish it. For example, you can assign it to users and devices, but it is applied only after you publish it. You can also use the Sandbox version to test the policy on devices you’ve designated as test devices. For information, see Section 10.0, Testing Security Policies.
-
Define Additional Properties: Select this option to display the policy’s property pages. These pages let you define system requirements that must be met before the policy can be assigned to a device, assign the policy to users and devices, and add the policy to policy groups.
-
-
To test the policy before assigning it to users and devices, see Section 10.0, Testing Security Policies
-
To assign the policy to users and devices, see Section 11.0, Assigning Security Policies.
