7.2 Configuring Adaptive Agent Security
To secure the ZENworks Adaptive Agent on devices, you can configure both uninstall and self-defense settings for the agent.
-
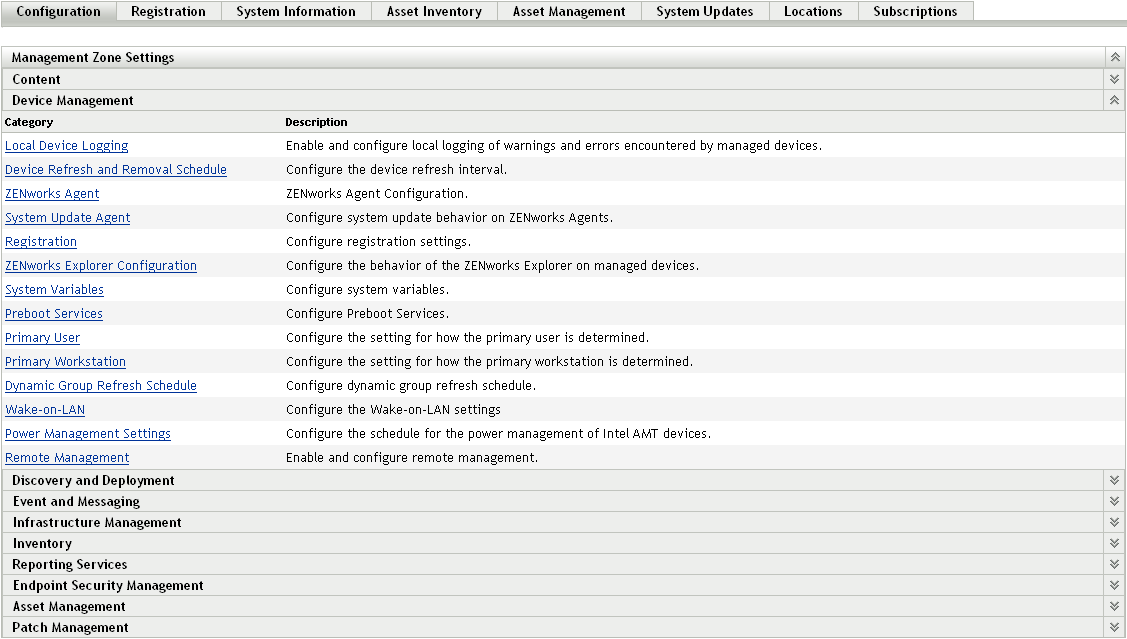
In ZENworks Control Center, click the tab.
-
In the Management Zone Settings panel, click , then click .
-
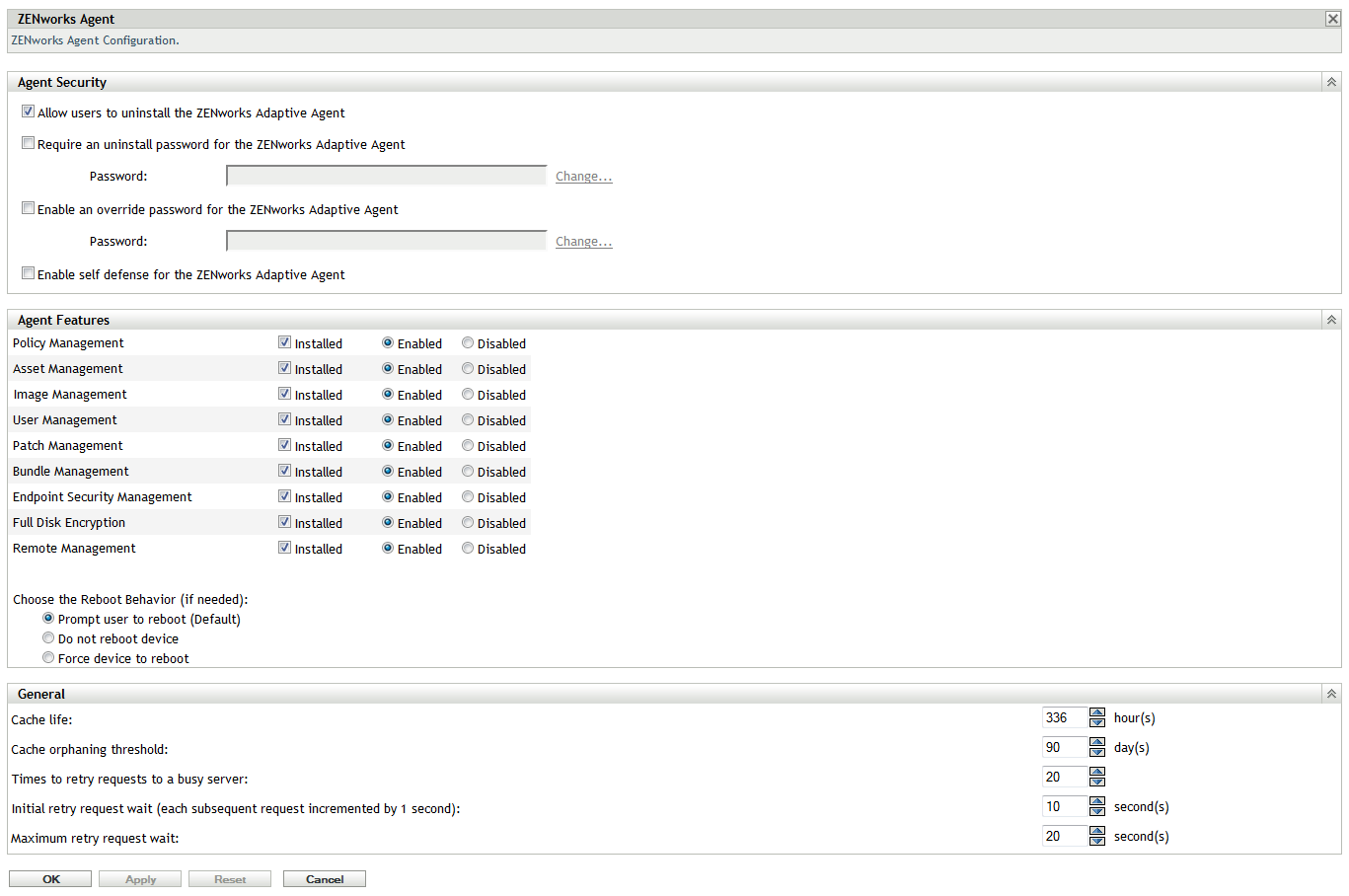
In the Agent Security panel, configure the following settings:
Allow Users to Uninstall the ZENworks Adaptive Agent: Enable this option to allow users to uninstall the ZENworks Adaptive Agent.
Require an Uninstall Password for the ZENworks Adaptive Agent: Enable this option to require users to enter a password in order to uninstall the ZENworks Adaptive Agent. Click to set the password.
To avoid distributing the uninstall password to users, we recommend that you use the Password Key Generator utility to generate a password key. The key, which is based on the uninstall password, functions the same as the uninstall password but can be tied to a single device or user so that its use is limited.
The Password Key Generator utility is accessible under the Configuration Tasks list in the left navigation pane.
Enable an Override Password for the ZENworks Adaptive Agent: An override password can be used in the ZENworks Adaptive Agent to:
-
Access information about the device’s current location and how the location was assigned.
-
Access the Administrative options in the Endpoint Security Agent. These options let you disable the currently applied security policies (with the exception of the Data Encryption policy), view detailed policy information, and view agent status information.
-
Access the Administrative options in the Full Disk Encryption Agent. These options let you view detailed policy information, view agent status information, and perform functions such as enabling user capturing and decrypting volumes.
-
Uninstall the ZENworks Adaptive Agent.
Enable Self Defense for the ZENworks Adaptive Agent: Currently, self-defense functionality protects only the ZENworks Endpoint Security Agent. It does not protect the other ZENworks Adaptive Agent modules.
Self defense protects the Endpoint Security Agent from being shut down, disabled, or tampered with in any way. If a user performs any of the following activities, the device is automatically rebooted to restore the correct system configuration:
-
Using Windows Task Manager to terminate any Endpoint Security Agent processes.
-
Stopping or pausing any Endpoint Security Agent services.
-
Removing critical files and registry entries. If a change is made to any registry keys or values associated with the Endpoint Security Agent, the registry keys or values are immediately reset.
-
Disabling NDIS filter driver binding to adapters.
Select the check box to enable self defense.
-
-
To save the changes, click .