16.0 Generating a Password Key
The following are passwords that users might need:
-
ZENworks Adaptive Agent uninstall password: Required when uninstalling the agent from a device. This password is configured in the ZENworks Agent Security settings (Configuration > Management Zone Settings > Device Management > ZENworks Agent).
-
ZENworks Adaptive Agent override password: Required to view how the current configuration location assignment was decided. If ZENworks Endpoint Security Management is being used, required to override the currently enforced security policies (with the exception of the Data Encryption policy) and access the Endpoint Security Agent’s Administrator options. Can also be used in place of the uninstall password and the FDE Admin password.
This password is configured in the ZENworks Agent Security settings (Configuration > Management Zone Settings > Device Management > ZENworks Agent)
-
ZENworks Full Disk Encryption Agent administration password (FDE Admin password): Required to access the Full Disk Encryption Agent’s Administrator options. This password is configured in the Disk Encryption policy.
Rather than distribute a password, you can use the Password Key Generator in ZENworks Control Center to generate a key for the password and then give the key to users who need it. The key functions the same as the password with the added benefit that you can specify who can use the key, what machine it can be used on, and when the key expires.
-
In ZENworks Control Center, click .
-
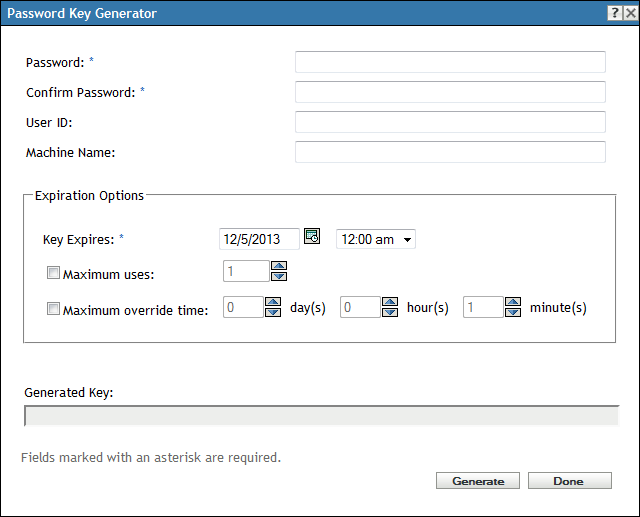
Under (in the left navigation pane), click to display the following dialog box:
-
Fill in the following fields:
Password: Specify the password for which you want to generate a key.
Confirm Password: Specify the password again.
User ID: To restrict the key to a single user, specify the user’s ZENworks login ID. The ZENworks login ID is the same as the user’s LDAP directory user ID (Novell eDirectory or Microsoft Active Directory).
Machine Name: To restrict the key to a single device, specify the device’s computer name. This is the computer name defined in Windows System Properties on the device.
-
Fill in the expiration options.
The expiration options apply only to an override password key when it is used to disable a device’s currently enforced security policies. The options are ignored if you set them when generating an uninstall password key or an FDE Admin password key.
Key Expires: Click
 to select the expiration date, then select the expiration time. After the specified date and time, the key no longer works.
to select the expiration date, then select the expiration time. After the specified date and time, the key no longer works.
Maximum Uses: Each time the key is entered counts as one use. To restrict the key so that it can only be used a certain number of times, select , then select the number of uses. After the maximum use has been reached, the key no longer works, even if the date and time have not been reached.
Maximum Override Time: Select this option to restrict the period of time that the security policies remain disabled by the override password key. For example, if you want the key to override the policies for a maximum of 36 hours, select 1 day and 12 hours. After 36 hours, the override key expires and the security policies are enforced again. If the computer reboots during the 36 hour period, the override password key must be entered again and the override time is restarted.
-
Click .
The generated key is displayed in the field. Copy the key and give it to the user.
-
After you finish generating keys, click .