A.5 Application Operations
The following figure illustrates Modeler operations that are available when you right-click an application.
Figure A-5 Application Operations
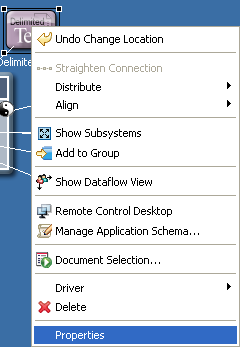
Table A-5 Application Operations
|
Operation |
Description |
|---|---|
|
|
Returns an item to its previous status. |
|
|
(Viewable when you select an eDir-to-eDir application) Separates the eDir-to-eDir application into two eDirectory drivers. |
|
|
Straightens a driver connection line. If a line is not within a few degrees of being horizontal or vertical, this option is dimmed. |
|
|
Evenly distributes applications vertically or horizontally. Press Ctrl, select the items that you want to distribute, then select a pattern. |
|
|
Aligns the selected objects horizontally and vertically. For more information, see Table A-6. |
|
|
(Viewable when you select an eDirectory application.) Runs the Driver Configuration Wizard to install an eDir-to-eDir driver. Places a tree icon in the Identity Vault. |
|
|
(Viewable when you select an eDirectory application.) Runs the Driver Configuration Wizard to install an eDir-to-eDir driver. Places a vault con in the Identity Vault. |
|
|
Lets you model an application’s or operating system’s subsystems. For example, if you have a Linux system, you can open it and drop MySQL* inside as a subapplication that runs on Linux. This is for diagramming purposes only, but can be convenient for accurately capturing the structure of the enterprise systems around which you are building the identity solution. |
|
|
Creates a Domain Group, and adds the selected items to it. The selected items are removed from any group that they were previously associated with. |
|
|
Displays the flow of information between the application and the driver in the Developer view. Launches the Dataflow view and lists Dataflow on the menu. For more information, see Section 7.0, Managing the Flow of Data. |
|
|
Launches a remote control session for the selected application. The host server must have an existing VNC server running. |
|
|
Enables you to manage a copy of the connected system’s schema. You can make changes to a copy of the application schema so that you can test the Identity Manager drivers in Designer. See Section 6.7, Managing a Copy of an Application Schema. |
|
|
Launches the Document Generation Wizard, which documents the application. |
|
|
Runs the Simulate Policy Transformation program against the selected driver. |
|
|
Launches the Policy Set and Policy Flow views. For more information, see Policy Set View in the Understanding Designer for Identity Manager. |
|
|
Guides you through creating a driver. After you fill out the wizard’s forms, Designer automatically generates policies that configure the driver to function as described in the forms. |
|
hronization |
Configures and displays the flow of password synchronization. For more information, see Section 7.6, Integrating Passwords. |
|
|
Launches the Document Generation Wizard, which documents the driver. |
|
|
Exports the driver to a .xml file. iManager can consume this format, and Designer can re-import it. For more information, see Section 15.10, Exporting To a File. |
|
|
Allows you to browse to and import a driver configuration file |
|
|
Enables you to connect to a server, browse to and select a driver, and import the objects into the driver. |
|
|
Prepares a deployment summary and then deploys selected objects and attributes. |
|
|
Allows you to compare the information structure in Designer on an object, to the object that is deployed or running on an eDirectory server. |
|
|
Imports attributes from an existing driver. |
|
|
Deploys the modified or imported attributes. |
|
|
Allows you to compare the attributes of a policy to the attributes that are already deployed. |
|
|
Reports whether the drivers are stopped or running. |
|
|
Starts the driver. |
|
|
Stops the driver. |
|
|
Allows you to specify how much information you want to see in a trace level log from the driver. Settings go from 0-5. |
|
|
Restarts the drivers. |
|
|
Launches the Driver Security Equals/Exclusions dialog box. Enables you to configure the selected driver’s security equivalences and to exclude selected users from administrative roles. If you select multiple drivers, this dialog box lets you add, modify, and remove common security equivalences and exclusions of the selected drivers. |
|
|
Launches the driver’s property pages. Enables you to configure the driver. |
|
|
Deletes the application and driver. |
|
|
Enables you to configure Identity Vaults, driver sets, drivers, and applications. |