5.1 Overview
Access to corporate information assets using mobile computing devices creates a variety of security challenges. GroupWise Mobile Server provides a solution that securely manages the flow of information among corporate servers and mobile and remote devices including laptops, handheld devices, and smart phones.
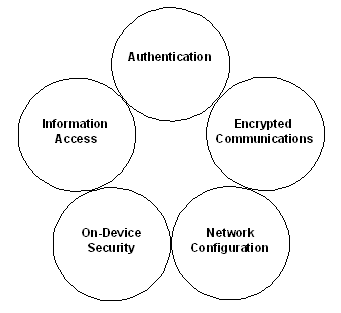
GroupWise Mobile Server’s security strategy addresses the following areas:
-
Authentication: Guaranteeing users are authorized to connect.
-
Information Access: Managing access and authorization to control the information delivered to users.
-
Encrypted Communications: Securing information in transit to and from the mobile user.
-
On-Device Security: Protecting information on the device from unauthorized users.
-
Network Configuration: Locating the Intellisync Mobile Suite server relative to existing firewalls and allowing it to communicate with other servers.
Figure 5-1 Key Elements of GroupWise Mobile Server’s Security Strategy
Highlights of GroupWise Mobile Server security include the following:
5.1.1 New Session Keys
For key exchange, GroupWise Mobile Server uses Diffie-Hellman with elliptical curve strengths of up to 1024-bit RSA. Each new sync session negotiates encryption and randomly generates new session-based keys for added security.
5.1.2 Encrypting All Data
GroupWise Mobile Server encrypts all packets of information, from the first to the last. No “clear text” user data is ever sent between client and server, unless you disable the encryption capabilities.
5.1.3 Encrypting User Credentials
GroupWise Mobile Server always encrypts user credentials as they are passed from client to server for authentication, unless you disable the encryption capabilities.
5.1.4 Storing User Credentials on the Device
GroupWise Mobile Server does not store user passwords on the device. The password is only an element of an encrypted credentials token, and the key is never transmitted or stored on the device. Therefore, you cannot encrypt or decrypt the password on the device. Depending on your configuration, the device can store user credentials and send this information to the server for each sync session.
Maintaining or Expiring User Credentials on the Device
You can keep user credentials on the device indefinitely or have credentials expire after a certain period of time. If user credentials expire, the user must enter the password to continue. Using this option provides better security in case the device is lost or stolen. If credentials never expire, the user must enter the password only when connecting for the first time.