10.1 Overview
To understand Net Folders, it is useful to see the similarities and differences between them and the mapped drives that you probably have on your current network. Figure 10-1 and Figure 10-2 illustrate such a comparison.
Figure 10-1 File Servers and Mapped Drives
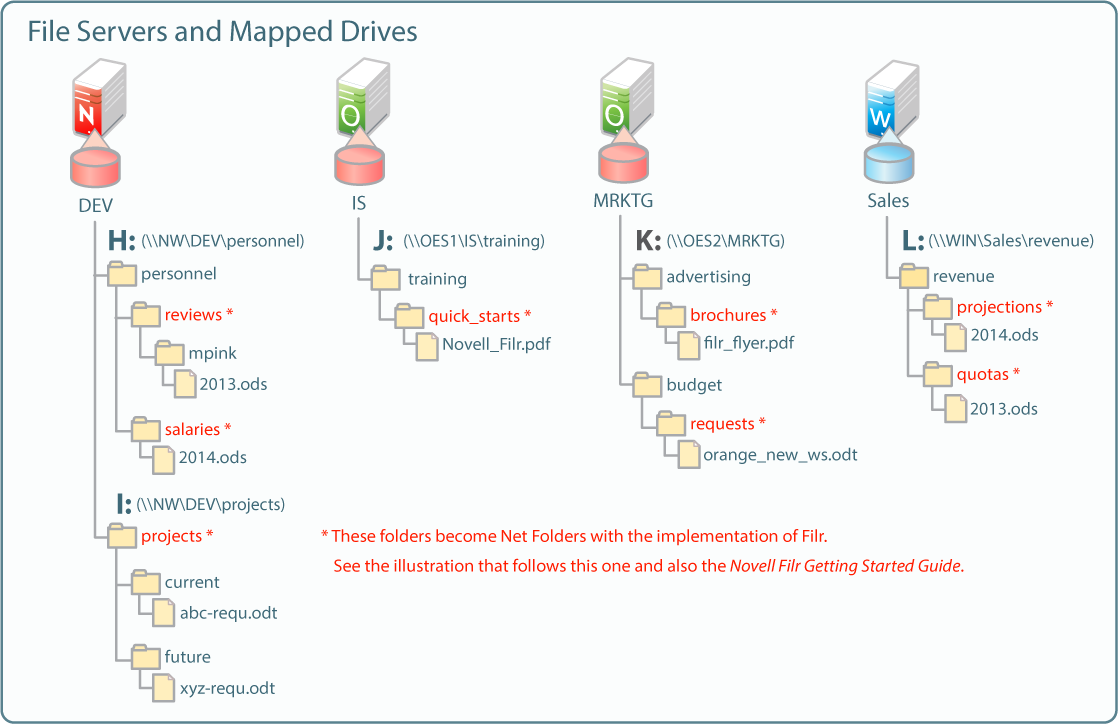
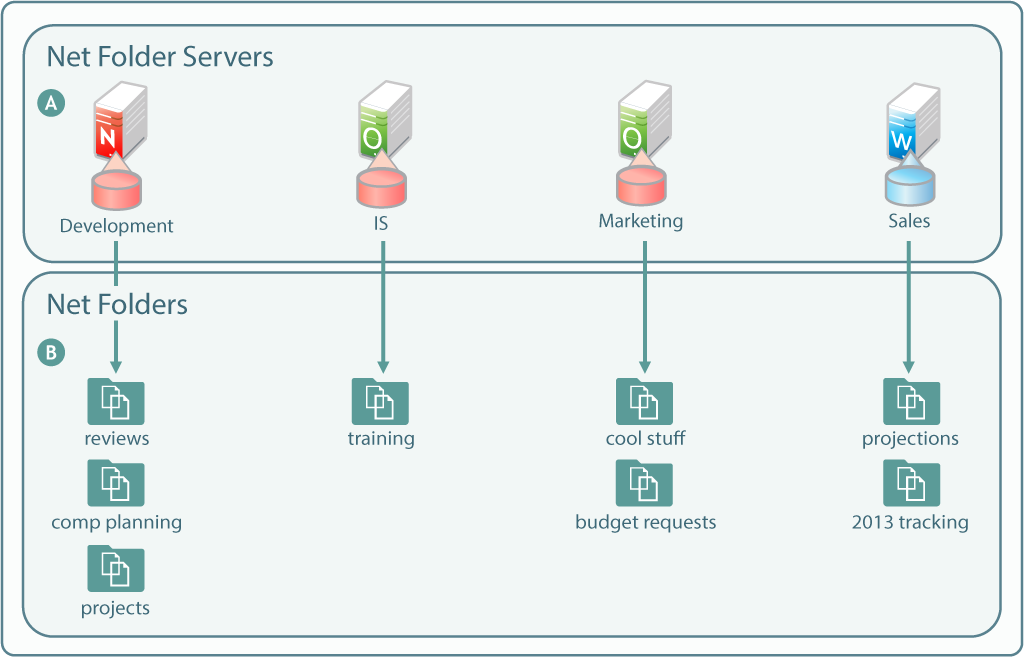
Figure 10-2 shows the same servers as in Figure 10-1, with their volumes defined as Net Folder Servers. Notice that the Net Folder Server names do not need to match the volume names, which can sometimes be rather cryptic.
The asterisk-marked folders in Figure 10-1 are shown as Net Folders here.
As with the Net Folder Server names, some of the Net Folder names in Figure 10-2 are different from the Figure 10-1 volume and folder names that they represent. This illustrates that Net Folder names are not tied to their corresponding actual folder names. Instead, you can name them whatever best communicates their purpose and content to those who access them.
Figure 10-2 Net Folder Servers and Net Folders
|
Letter |
Information |
|---|---|

|
A Net Folder Server represents a volume or share on a NetWare, OES, or Windows file server. Net Folder Servers for OES servers point to the root of an NSS volume on the server. Net Folder Servers for Windows servers point to a Windows share, which is usually defined at a folder level other than at the root of the file system. Therefore, it is common for a Net Folder Server for Windows to point to the same folder as an associated Net Folder does. There is usually one Net Folder Server per volume or share, but you can create multiple Net Folder Servers to the same volume or share if needed. |

|
A Net Folder is a pointer or reference to a specific folder within a Net Folder Server. Often there is just one Net Folder for every Net Folder Server, but you can create multiple Net Folders that point to a single Net Folder Server. You can even create multiple Net Folders that point to the same relative path. Why might you want to duplicate Net Folders? Possibilities include the following:
|