8.4 Configuring Authentication Contracts
Authentication contracts define how authentication occurs. An Identity Server configuration might have several authentication contracts available, such as name/password or X.509, which is used for mutual SSL authentication between the Identity Server and the Access Gateway. Resources at an Access Gateway or agent are protected by authentication contracts.
NOTE:You cannot delete a contract if it is in use by an Access Gateway or J2EE agent.
Contracts are executed by the identity provider when authenticating a user. A URI uniquely identifies each contract, and you can assign authentication methods to each contract. A single contract can be specified for local logins.
-
In the Administration Console, click > > > > >
-
Click .
-
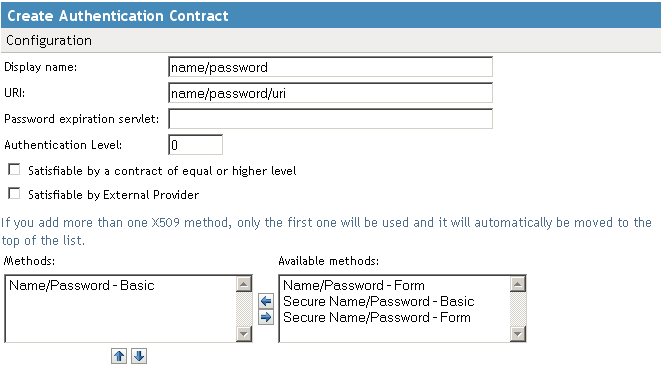
Fill in the following fields:
Display name: Specifies the name of the authentication contract.
URI: Specifies a value that uniquely identifies the contract from all other contracts. For example, as an identity provider, you might want to publish the details of a contract. In this case, you can use a URL so that the link resolves to a page. No spaces can exist in the URI field.
Password expiration servlet: Specifies a URL to a page where the user can change his or her password. This applies only to eDirectory servers when the password is expired or within the grace login period. You must use eDirectory to change the number of grace logins.
IMPORTANT:Failure to specify a value for the number of grace logins causes the contract to redirect to the password management servlet only when the grace login count has reached 0 and the password has expired.
The Identity Server needs to read the value of the grace login attribute in order to properly redirect to the password management servlet. If restricting grace logins is not important to your security model, enable grace logins and set the maximum to 9999 (the equivalent of infinite in most environments). For more information, see TID 3465171.
Access Manager works with any password management servlet, but for an implementation example, see Configuring Access Manager for UserApp and SAML.
Authentication Level: A number you can assign to this authentication contract to specify its security level or rank. You use this setting to preserve authentication contracts of a higher security level. When you enable the option on this page, the system uses this value as a reference.
For example, you might create a name/password authentication contract and assign it to level one. You might also create an X.509 authentication contract and assign it to level two. If a user supplies the credentials for the X.509 level-two contract, the system does not require the credentials to satisfy the name/password level-one authentication contract.
Satisfiable by a contract of equal or higher level: Allows the system to satisfy this authentication contract if a user has logged in using another contract of an equal or higher authentication level, as specified in the field of an authentication contract.
Satisfiable by External Provider: Enables your server to be authenticated by an external Identity Server. If your server and an external server are capable of performing an authentication, they must have the same URI.
Methods and Available Methods: Specifies the authentication method to use for the contract. You can specify the order in which the methods are executed for login; however, this is not a graded list, so all the methods you specify are required. are the authentication methods you have set up.
If you add more than one X.509 method, only the first one is used and it is automatically moved to the top of the list.
When choosing a secure method, such as Secure Name/Password, ensure that you have enabled security for the Identity Server configuration by setting the protocol to HTTPS. See
Configuring Secure Communication on the Identity Server
in the Novell Access Manager 3.0 SP4 Setup Guide. -
Click , then .
-
Update the Identity Server and any devices that use the Identity Server configuration.