27.3 Creating Access Manager Roles from an Existing Role-Based Policy System
If you have already implement a role-based administration policy for granting access to print, file, and LDAP resources, you can leverage your role definitions and use Access Manager policies to control access to Web resources. If your role definitions use the following types of LDAP features, you can create Access Manager Role policies that use them:
-
The values found in LDAP attributes
-
The location of the user objects in the directory tree
-
Membership in groups or roles
The Access Manager Role policies that you create using these features can then be used to control access to protected Web resources.
27.3.1 Creating a Role Using an LDAP Attribute
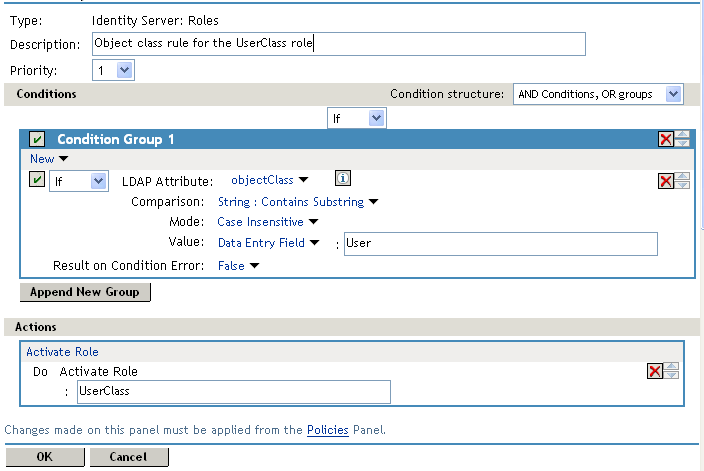
You can assign a user to a role by using a value found in any LDAP attribute in your directory. The following example uses the objectClass attribute because every object in an LDAP directory has an objectClass attribute that contains the object classes to which the object belongs. This attribute contains the name of the object class that was used to create the object as well as the names of the superior object classes of this class. All you need to know is the name of the object class you used to create your users in the LDAP directory. For example, the following instructions create a Role policy for users who were created with the User object class.
-
In the Administration Console, click > .
-
Click , specify a name for the Role policy, select for the type, then click .
-
In , click , then select .
-
In , select the conditions the user must meet:
LDAP Attribute: Select the objectClass attribute. If you have not added this attribute, it won’t appear in the list. Scroll to the bottom of the list, click , specify objectClass for the name, then click .
If you are using eDirectory™ for your LDAP directory, you need to specify standard LDAP names for the attributes. Access Manager does not support spaces or colons in attribute names.
Comparison: Select how you want the attribute values to be compared. For the objectClass attribute, select > .
The objectClass attribute is a multi-valued attribute and, for most objects, contains multiple values. For example in eDirectory, users created with the User object class have User, organizationalPerson, person, ndsLoginProperties, and top as values in the objectClass attribute.
Mode: Select .
Value: Select and specify User as the value.
Result on Condition Error: This sets up the results that are returned if an error occurs while evaluating the condition (for example, the LDAP server goes down). This rule is set up to grant the user the role of UserClass if the condition evaluates to . If an error occurs, you do not want random users assigned the role of UserClass. Therefore, for this rule, you need to select .
-
In the section, click .
-
In the box, type UserClass, then click
The name you enter in the box is the role you want assigned to the users who match the condition.
Your rule should look similar to the following:
-
Click twice, then click .
-
To enable the role so that it can be used in Authorization and Identity Injection policies, click > > .
-
Select the check box by the name of the role, then click .
-
Click .
-
To update the Identity Server, click > .
You can now use this role when creating Authorization and Identity Injection policies, which control access to protected Web resources. For more information, see the following:
27.3.2 Creating a Role Using the Location of the User Objects
If you have created your users in specific containers in your LDAP tree, you can use these container objects to assign users to roles. For example, suppose your LDAP tree looks similar to the following tree.
Figure 27-10 Using an eDirectory Tree for access control
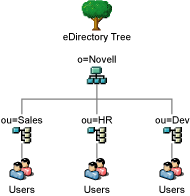
Such a tree organization can be used to control access to resources. The following instructions explain how to create a Role policy for the users created under the Sales container.
-
In the Administration Console, click > .
-
Click , specify a name for the Role policy, select for the type, then click .
-
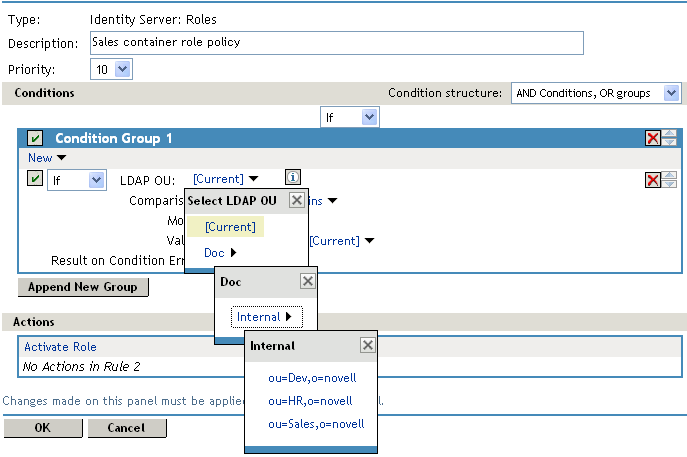
In , click , and select > > > .
The following example illustrates how to make these selections:
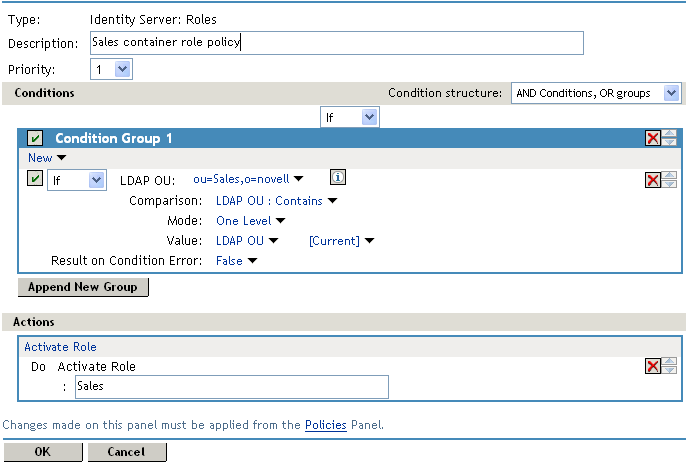
Comparison: Select how you want the attribute values to be compared. For LDAP OU, select .
Mode: Select if all your users are created in ou=Sales. Select if your users are created in various containers under the ou=Sales container.
Value: Select , then select .
The DN of the authenticated user is compared with the value specified in LDAP OU. If the DN of the user contains the LDAP OU value, the user matches the condition. For example, if the DN of the user is cn=bsmith,ou=sales,o=novell and the LDAP OU value is ou=sales,o=novell, the user matches the condition. If you selected Subtree for the Mode, a user with the following DN also matches the condition: cn=djones,ou=provo,ou=sales,o=novell.
Result on Condition Error: This sets up the results that are returned if an error occurs while evaluating the condition (for example, the LDAP server goes down). This rule is set up to grant the user the role of Sales if the condition evaluates to . If an error occurs, you do not want random users assigned the role of Sales. Therefore, for this rule, you need to select .
-
In the section, click .
-
In the box, type Sales, then click
The name you enter in the box is the role you want assigned to the users who match the condition.
Your rule should look similar to the following:
-
Click twice, then click .
-
To enable the role so that it can be used in Authorization and Identity Injection policies, click > > .
-
Select the check box by the name of the role, then click .
-
Click .
-
To update the Identity Server, click > .
You can now use this role when creating Authorization and Identity Injection policies, which control access to protected Web resources. For more information, see the following:
27.3.3 Creating a Role Using Role or Group Membership
If you have created an LDAP group and assigned users to the group, you can use group membership to assign a role to the user. For example, you might have created a first level managers group and made all your first level managers a member of this group. You would have other groups for your upper level managers. You can create a Role policy that assigns the user a role if the user is a member of a specific group. The Role policy can then be used in an Authorization or Identity Injection policy to protect a Web resource.
-
In the Administration Console, click > .
-
Click , specify a name for the Role policy, select for the type, then click .
-
In , click , then select .
-
In , select the conditions the user must meet:
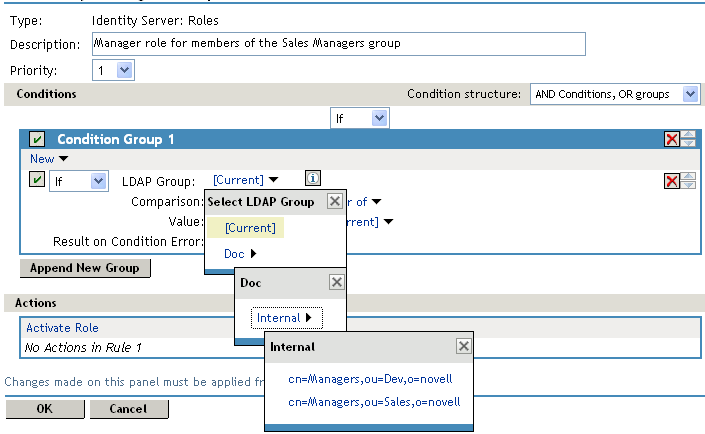
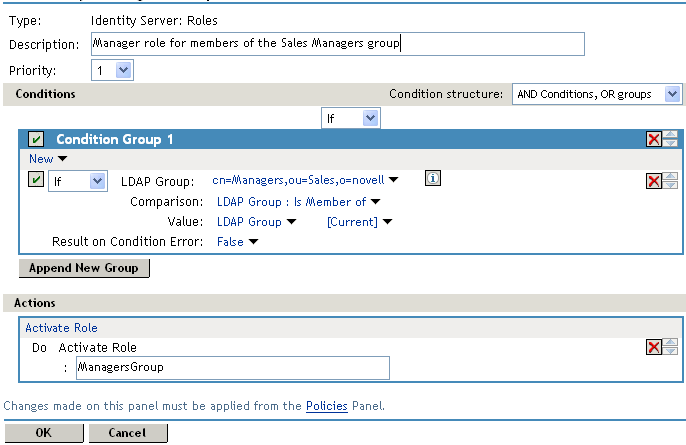
LDAP Group: Select the Identity Server Configuration, the user store, then the Group. The following figure illustrates this selection process.
Comparison: Select how you want the attribute values to be compared. For LDAP Group, select .
Value: Select , then select .
The DN of the authenticated user is compared with the members of the LDAP Group. If the DN of the user matches one of the members, the user matches the condition.
Result on Condition Error: This sets up the results that are returned if an error occurs while evaluating the condition (for example, the LDAP server goes down). This rule is set up to grant the user the role of ManagersGroup if the condition evaluates to . If an error occurs, you do not want random users assigned the role of ManagersGroup. Therefore, for this rule, you need to select .
-
In the section, click .
-
In the box, type ManagersGroup, then click .
The name you enter in the box is the role you want assigned to the users who match the condition.
Your rule should look similar to the following:
-
Click twice, then click .
-
To enable the role so that it can be used in Authorization and Identity Injection policies, click > > > .
-
Select the check box by the name of the role, then click .
-
Click .
-
To update the Identity Server, click > .
You can now use this role when creating Authorization and Identity Injection policies, which control access to protected Web resources. For more information, see: