19.4 Additional Configuration for Enterprise Mode
The Enterprise mode of SSL VPN requires some additional configurations to be done through the command line.
19.4.1 Configuring Routes
In Enterprise mode, SSL VPN assigns IP addresses to each client from subnet specified in the configuration. For more information on configuring IP address, see Section 19.2, Configuring the IP Address, Port, and NAT. The values specified in the and fields determine the IP addresses that are assigned to the clients. Make sure that the assigned IP address and the IP address of the client do not match.
The packets from these clients reach the application server with the IP address of the client as the source address. The response packets need to be routed back to the SSL VPN server, which sends them on to the clients. You can solve this routing problem in one of the following ways:
Configuring the OpenVPN Subnet in Routing Tables
If you have a gateway for your network between the application server and the SSL VPN server, you can configure the gateway to send the dynamically assigned IP addresses from the OpenVPN address pool to the SSL VPN server. This is the best routing approach because most applications, including ActiveFTP and TFTP, can work in this type of environment. To establish this type of routing, you need to add a static route to your network’s routing infrastructure so that traffic to the OpenVPN subnet pool of addresses is sent via the SSL VPN gateway.
Configuring Source NAT
You can configure Source NAT to change the dynamically assigned client addresses to the address of the SSL VPN server before sending them to the application server. The application server can then use the source address in the packets to send them back to the SSL VPN server, which can then reassign the client address and send the packets on to the client. This is the best approach if you are using SSL VPN for TCP and UDP applications. Other applications, such as ActiveFTP and TFTP, cannot work in this type of environment. To establish this type of routing, you need to create an entry in the iptables file on the SSL VPN server. If the option is set to 10.8.0.0/16 and the IP address of the SSL VPN server is 10.16.12.247, the entry should be similar to the following:
iptables -t nat -A POSTROUTING -s 10.8.0.0/16 -j SNAT --to 10.16.12.247
Restart the SSL VPN services after the iptables file has been modified.
IMPORTANT:This simple solution only works if you are not using iptables to translate ports of other applications or Access Manager components. For a solution that works with multiple components, see Configuring SUSE Firewall for the SSL VPN Component in Access Manager.
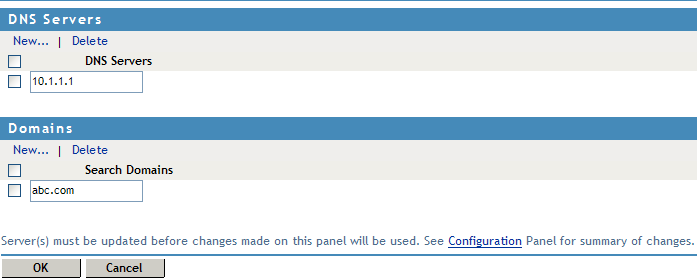
19.4.2 Configuring DNS Servers for the Enterprise Mode
-
In the Administration Console, click > .
The Server configuration page is displayed.
-
Select from the section.
The DNS server list page is displayed.
-
To configure a DNS server, click in the section, specify the IP address of the server, then click .
-
To configure a Domain, click in the section, specify the domain name, then click .
-
To delete a DNS server or a domain, select the check box next to the field and click in the section.
-
To save your modifications, click then click on the Configuration page.