48.2 Distribution Options Tab
The Distribution Options tab includes the following pages to help you configure how the Application object is distributed to users:
48.2.1 Icons/Shortcuts Page
The Icons/Shortcuts property page is available only on Application objects created for simple applications and AOT/AXT applications. It is not available on Application objects created for MSI applications, Web applications, and terminal server applications.
The Icons/Shortcuts property page, shown below, determines the icons and shortcuts that Application Launcher creates when distributing the application to the workstation. You can add the application’s icon as an item in a program group or as a shortcut on the workstation’s desktop or in a folder. You can also delete existing icons, shortcuts, and program groups.
Figure 48-7 Application Object > Distribution Options Tab > Icons/shortcuts Page
The icons and shortcuts you add with this page are in addition to the Application object’s icon. Although the Application object’s icon might cause various actions to occur, including installing the application or running it, the icons and shortcuts defined on this page link directly to the application’s executable file and simply launch the application.
You can use icons and shortcuts in combination with other options to create the user environment you want. For example, you could define the icons and shortcuts you want to be created and configure the Application object to run one time ( > ). When a user selects the Application object, Application Launcher runs the application one time, creates the icons and shortcuts, performs any other tasks specified by the Application object's properties, and then removes the Application object's icon from the workstation. Thereafter, the user needs to select the icon or shortcut to launch the application.
IMPORTANT:If Application Launcher cannot create a shortcut, the application is not distributed. In this case, all application files and settings are removed. However, if other shortcuts were created before the shortcut that failed, those shortcuts are not removed.
Icons and Shortcuts
This list displays the icons and shortcuts that are created when the application is distributed to a workstation.
Files
Click > to search for icon and shortcut definitions that include certain information.
Click > Import to import icons and shortcuts from another Application object. The Open dialog box defaults to *.axt for its file type display. If you are importing from an .aot file, you must change the file type display to *.aot or in order to select the .aot file.
Add
Click to add a new program group, program group item, or shortcut. Program groups and program group items are supported on Windows 98 workstations but not on Windows 2000/XP workstations. Shortcuts are supported on all Windows versions.
IMPORTANT:When defining the target path for a shortcut, if the application will be distributed to a Windows 2000/XP workstation you must use a UNC path rather than a mapped drive path. Long mapped drive paths are truncated on Windows 2000/XP, resulting in an invalid shortcut that does not work.
Modify
Select an icon or shortcut from the Icons and Shortcuts list, then click to change the information associated with it.
Delete
Select an icon or shortcut from the Icons and Shortcuts list, then click to delete it from the list.
Track Distribution Per User
If you have implemented roaming user profiles, use this option to ensure that particular icons and shortcuts are distributed to each workstation a user logs in to.
In the Icons and Shortcuts list, select the desired icon or shortcut, then select .
Distribute Always
By default, Application Launcher creates the icons and shortcuts defined in the Icons and Shortcuts list only at the following times:
-
The first time the application is launched on a workstation.
-
The first time the application is launched after the application’s version number ( tab > page) has been changed.
To force Application Launcher to create an icon or shortcut each time the application is launched, select the icon or shortcut in the Icons and Shortcuts list, then select .
If the user has a NAL cache directory on his or her local machine, Application Launcher uses the information stored in the NAL cache directory to create the icon or shortcut. If the user does not have a NAL cache directory (for example, the user is running Application Launcher through a terminal server client session) or if writing to the cache has been disabled for the user (User object > tab > page > option), Application Launcher uses the information stored in eDirectory.
48.2.2 Registry Page
The Registry property page is available only on Application objects created for simple applications, AOT/AXT applications, and MSI applications. It is not available on Application objects created for Web applications and terminal server applications.
The Registry property page, shown below, determines the registry modifications that Application Launcher makes when distributing the application to a workstation.
Figure 48-8 Application Object > Distribution Options Tab > Registry Page
Registry Settings
The Registry Settings tree displays all settings that are modified when the application is distributed to a workstation. If you used an .aot, .axt, or .msi file when creating the Application object, the tree automatically includes all registry settings that are defined in those templates.
If there are additional registry settings you want created or deleted during distribution, you need to add the settings to the tree and then specify the appropriate action (create or delete) in the field.
NOTE:For Application objects created for AOT/AXT applications, the Novell Application Launcher (NAL) handles the distribution of the registry settings and the distribution of the application. If you modify registry settings for an AOT/AXT application and the registry settings fail to distribute, the application itself fails and NAL rolls back the application's installation.
For Application objects created for MSI applications, NAL handles the distribution of registry settings and the Microsoft Windows Installer (MSI) handles distribution of the application. If you modify the Application object's registry settings for a MSI application and the registry settings fail to distribute, the application is installed by Windows Installer, but the registry settings do not roll back. As a result, the application might not function properly, depending on how the registry settings affect the application.
File
This option lets you search for keys or values in the tree, import settings into the tree, and export settings from the tree.
Click , then choose one of the following options:
-
Find: Searches for specific keys, value names, or value data in the registry.
-
Find next: Finds the next occurrence of the key, value name, or value data previously searched for.
-
Import: Imports registry settings from another Application object’s .aot or .axt file, or from a registry file (.reg). The Open dialog box defaults to *.axt for its file type display. If you are importing from an .aot file or .reg file, you must change the file type display to *.aot, *.reg, or in order to select the appropriate file.
-
Export: Exports the registry settings to a registry file (.reg). To export the settings to an .aot or .axt file format, you must export the entire Application object using the Export Application Object option located on the > > menu.
Add
This option lets you add registry settings to the tree. Only settings displayed in the Registry Settings tree are created or deleted when the application is distributed.
To add a registry key or value, select the registry folder where you want to add the key, or select the key where you want to add a value, click the Add button, then choose one of the following options:
-
Key: Adds a key to the selected registry folder.
-
Binary: Adds a binary value to the selected key.
-
Expand string: Adds an expand string value to the selected key. The expand string setting does not exist in the Windows 98 registry; if you use this setting, it is changed to a string setting during distribution to Windows 98 workstations.
-
Default: Adds a default string value to the selected key.
-
DWORD: Adds a DWORD value to the selected key.
-
Multi-string value: Adds a multi-value string to the selected key. The multi-value string setting does not exist in the Windows 98 registry; if you use this setting, it is changed to a binary setting during distribution to Windows 98 workstations.
-
String: Adds a string value to the selected key.
After the key or value is added to the Registry Settings tree, you can use the Distribution Options list to determine whether or not the key or value is created in the workstation’s registry or deleted from the registry.
You can use a macro for a key name, value name, or value data. For information about macros, see Section 49.0, Reference: Macros.
Modify
Select the key or value you want to modify, then click .
Delete
Select the key or value you want to delete, then click . When you delete a key, everything subordinate to the key is also deleted.
Distribution Options
The distribution options let you determine how individual registry settings (included in the Registry Settings tree) are handled during distribution of the application.
Item Will
In the Registry Settings tree, select the setting, then select the action that you want to occur for the setting when the application is distributed:
-
Create always: The setting is always created in the registry, even if it already exists. If it exists, the setting's current values are overwritten. For example, if PATH=C:\ already exists, PATH=C:\TEMP replaces it.
-
Create if does not exist: The setting is created only if it does not already exist.
-
Create if exists: The setting is created only if it already exists. The setting's current values are overwritten. For example, if PATH=C:\ already exists, PATH=C:\TEMP replaces it.
-
Delete: The setting is deleted. If the registry setting has subordinate settings, Application Launcher deletes the subordinate settings also.
-
Append if exists otherwise create: This option applies only to string values (, > , , and ). The string value's data is added to the existing string as the last entry. If the string value (or its key) does not exist, it is created.
When specifying the string value, you must include a semicolon (;) delimiter before the value if the string has existing values. For example, assume that the registry already includes a string1=value1 setting. You want to append a second value (value2). When specifying the string value, you must specify ;value2 so that the resulting string is string1=value1;value2.
-
Prepend if exists otherwise create: This option applies only to string values (, , , and ). The string value’s data is added to the existing string as the first entry. If the string value (or its key) does not exist, it is created.
When specifying the string value, you must include a semicolon (;) delimiter after the value if the string has existing values. For example, assume that the registry already includes a string1=value1 setting. You want to prepend a second value (value2). When specifying the string value, you must specify value2; so that the resulting string is string1=value2;value1.
Track Distribution Per User
If you have implemented roaming user profiles, use this option to ensure that particular registry settings are distributed to each workstation a user logs in to. You should enable this option for all registry settings that are not saved as part of roaming user profiles.
In the Registry Settings list, select the desired registry modification, then select the Track Distribution Per User check box.
Distribute Always
By default, Application Launcher distributes the registry modifications defined in the Registry Settings list only at the following times:
-
The first time the application is launched on a workstation.
-
The first time the application is launched after the application’s version number ( tab > page) has been changed.
To force Application Launcher to distribute a registry modification each time the application is launched, select the registry setting in the list, the select the check box.
If the user has a NAL cache directory on his or her local machine, Application Launcher uses the setting information stored in the NAL cache directory to modify the registry. If the user does not have a NAL cache directory (for example, the user is running Application Launcher through a terminal server client session) or if writing to the cache has been disabled for the user (User object > tab > page > option), Application Launcher uses the setting information stored in eDirectory.
48.2.3 Application Files Page
The Application Files property page is available only on Application objects created for simple applications and AOT/AXT applications. It is not available on Application objects created for MSI applications, Web applications, and terminal server applications.
The Application Files property page, shown below, specifies the application files that Application Launcher installs or removes when distributing the application to a workstation.
Figure 48-9 Application Object > Distribution Options Tab > Application Files Page
Application Files
The Application Files list displays all files and directories that are installed, removed or copied during distribution. The name, target directory (the location on the workstation where the file is installed), and source (the file or directory that is being used to install the file) are listed for each application file or directory.
If you used an .aot or .axt file when creating the Application object, the list automatically includes all files and directories that are defined in those templates.
File
This option lets you search for items in the Application Files list and import files and directories into the list.
Click > choose one of the following options:
-
Find: Searches for specific items in the list. You can search for text in the , > , or fields. For example, you could search for all files and directories that are being installed under the Program Files directory.
-
Find next: Finds the next occurrence of the item specified by the initial search.
-
Import: Imports application files and directories from another Application object’s .aot or .axt file. The Open dialog box defaults to *.axt for its file type display. If you are importing from an .aot file, you must change the file type display to *.aot or in order to select the .aot file.
Add
This option lets you add files or directories to the list. Only files and directories displayed in the list are installed to, removed from, or copied to the workstation during distribution.
-
File: To add a file to the list, click , then click to display the Edit Files dialog box.
In the field, specify the file to be used as the source of the installation. You can use a mapped drive, UNC path, or macro, or you can browse and select the file (for example, \\server1\vol1\bookmarks\bookmark.htm or %SOURCE_PATH%\bookmark.htm). The source file can be a single file that is copied, multiple files (for example, %SOURCE_PATH%\*.*), or a snAppShot™ application source (.fil) file.
If you are deleting a file from the workstation, leave this field blank.
In the field, specify the file on the workstation where the source file is to be copied (for example, c:\program files\novell\browser\bookmark.htm). You can also substitute a macro for the target path (for example, %TARGET_PATH%\bookmark.htm). If you are copying multiple files using a wildcard (*.*), specify the destination directory only (for example, c:\program files\novell\browser\).
If you are deleting the file from a workstation, enter the full path for the file from the perspective of the workstation, then select the check box.
-
Directory: To add a directory to the list, click , then click to display the Edit Directory dialog box.
In the field, specify the directory to be used as the source, if you are copying the directory. You can use a mapped drive, UNC path, or macro, or you can browse and select the directory (for example, c:\program files\novell). You can also substitute a macro for the directory path (for example, %DIRECTORY_TARGET_PATH%\novell).
If you are creating or deleting a directory, the field is disabled.
In the field, specify the directory to create or delete, or you can specify the directory on the workstation where the source directory is to be copied (for example, c:\program files\novell). You can also substitute a macro for the directory path (for example, %DIRECTORY_TARGET_PATH%\novell).
Select to create the directory on the workstation.
Select to delete the directory from the workstation.
Select to copy the directory to the workstation. When you select , the option becomes available. Click the check box if you want to copy the subdirectories of the directory listed in the field.
Modify
Select the file or folder you want to modify, then click .
Delete
Select the file or folder you want to delete, then click to remove it from the list.
NOTE:If there are files and subfolders in the folder to be deleted, those files and subfolders must be deleted before the parent folder can be deleted.
Selected Item(s) Options
Use these options to set individual distribution options for files and directories included in the list.
Item Will
Select a file in the list > select one of the following options from the list:
-
Copy always: Copies the file regardless of whether the file currently exists on the workstation.
-
Copy if exists: Copies the file only if the file currently exists on the workstation.
-
Copy if does not exist: Copies the file only if the file does not currently exist on the workstation.
-
Copy if newer: Copies the file only if its date and time are newer than the existing file’s date and time, or if the file does not currently exist on the workstation.
-
Copy if newer and exists: Copies the file only if it already exists on the workstation and has an older date or time.
-
Copy if newer version: Copies the file only if its internal version is newer than the existing file’s version (if version information is present). This is useful if you want to update the version of an .exe or .dll file based on the compiled version information.
-
Request confirmation: Prompts the user to verify that the file should be copied.
-
Copy if different: Copies the file if its date, time, or size is different than the existing file’s date, time, or size.
-
Delete: Deletes the file from the workstation.
Select a folder in the list, then select one of the following options from the list:
-
Create: Creates the directory on the workstation.
-
Delete: Deletes the directory from the workstation.
Track Distribution Per User
If you have implemented roaming user profiles, use this option to ensure that application files are distributed to each workstation a user logs in to. You should enable this option for all application files that are not saved as part of roaming user profiles.
In the list, select the desired application files, then select .
Distribute Always
By default, Application Launcher distributes the file and folder modifications defined in the list only at the following times:
-
The first time the application is launched on a workstation.
-
The first time the application is launched after the application’s version number ( tab > page) has been changed.
To force Application Launcher to distribute a file or folder modification each time the application is launched, select the file or folder in the list, then select .
If the user has a NAL cache directory on his or her local machine, Application Launcher uses the information stored in the NAL cache directory to install or remove the file or folder. If the user does not have a NAL cache directory (for example, the user is running Application Launcher through a terminal server client session) or if writing to the cache has been disabled for the user (User object > tab > page > option), Application Launcher uses the information stored in eDirectory.
Shared File
Use this option to mark a file as a shared file (that is, one that is used by more than one application). Shared files are usually Windows DLL files. SnAppShot detects shared files when it discovers application installation changes on a workstation.
48.2.4 INI Settings Page
The INI Settings property page is available only on Application objects created for simple applications, AOT/AXT applications, and MSI applications. It is not available on Application objects created for Web applications and terminal server applications.
The INI Settings property page, shown below, determines the INI settings that Application Launcher creates or deletes when distributing the application to a workstation.
Figure 48-10 INI Settings Page
INI Settings
The INI Settings tree displays the INI settings that are modified when the application is distributed to the workstation. If you used an .aot, .axt, or .msi file when creating the Application object, the tree automatically includes all INI settings defined in those templates.
If there are additional INI settings you want created or deleted during distribution, you need to add the settings to the tree and then specify the appropriate action (create or delete) in the field.
The INI Settings tree can include multiple INI files and each file can include multiple sections. When you add a setting to the INI Settings tree, you must add it to a file and section. This means that you might need to add new files and new sections to the tree before you can add new settings.
For example, assume that you want to add a CLASSPATH= setting to the ENVIRONMENT section of the sample.ini file. You would 1) add a file entry to the tree for the sample.ini file, 2) add an ENVIRONMENT section under the sample.ini file, 3) add the CLASSPATH= setting under the ENVIRONMENT section, and 4) select the CLASSPATH= setting and choose the appropriate action in the field.
If, instead of adding the CLASSPATH=setting, you wanted to delete it, you would follow the same process but then choose the appropriate action in the field.
NOTE:For Application objects created for AOT/AXT applications, the Novell Application Launcher (NAL) handles the distribution of the INI settings and the distribution of the application. If you modify INI settings for an AOT/AXT application and the INI settings fail to distribute, the application itself fails and NAL rolls back the application's installation.
For Application objects created for MSI applications, NAL handles the distribution of INI settings and the Microsoft Windows Installer (MSI) handles distribution of the application. If you modify the Application object's INI settings for a MSI application and the INI settings fail to distribute, the application is installed by Windows Installer, but the INI settings do not roll back. As a result, the application might not function properly, depending on how the INI settings affect the application.
File
This option lets you search for files, sections, or values in the INI Settings tree, import settings into the tree, export settings from the tree, or view a file’s INI settings.
Click > choose one of the following options:
-
Find: Searches for specific files, sections, or values.
-
Find next: Finds the next occurrence of the item specified by the initial search.
-
Import: Imports INI settings from another Application object’s .aot or .axt file, or from a .ini file. The Open dialog box defaults to *.axt for its file type display. If you are importing from an .aot file or .ini file, you must change the file type display to *.aot, *.ini, or in order to select the appropriate file.
-
Export: Exports the settings to an .ini file. To export the settings to an .aot or .axt file, you must export the entire Application object using the option located on the > > menu.
-
View file: Displays the INI settings for a specific file that are modified when the application is distributed. You must select the file from the INI Settings tree before you click > .
Add
This option lets you add INI settings to the INI Settings tree. Only settings displayed in the INI Settings tree are created or deleted when the application is distributed. You can add a file to the tree, a section to a file, or a value to a section.
To do so, select the appropriate item in the tree, click the button, then choose one of the following options:
-
File: Adds a file to the INI Settings tree. In addition to providing a file name, you can specify the target location for the file. By default, the %*WINDIR% macro is used, which represents the workstation’s Windows directory (typically c:\windows or c:\winnt). After you name the file, you can begin adding sections to it.
-
Section: Adds a section to the selected file. After you name the section, you can begin adding values to it.
-
Value: Adds a value to the selected section. You must specify the value name and value data.
After you’ve added a value to the INI Settings tree, you can use the list to determine whether or not it is created or deleted from the workstation. If the value needs to be created but the file or section does not exist, Application Launcher creates the file or section before adding the value.
You can use a macro for a section name, value name, or value data. For more information about macros, see Section 49.0, Reference: Macros.
Modify
You can modify a file's name, a section's name, or a value's name and data. Select the file, section, or value you want to modify, then click .
Delete
Select the file, section, or value you want to delete from the tree, then click . When deleting a file or section, everything subordinate to it is also deleted.
Distribution Options for the Selected Item
The distribution options let you determine how individual INI settings (included in the INI Settings tree) are handled during distribution of the application.
Item Will
Use this option to determine whether a setting is created or deleted when the application is distributed. Select a value in the tree, then select one of the following options from the list:
-
Create always (default): Creates the value regardless of whether the value currently exists in the section.
-
Create if does not exist: Creates the value only if the value does not currently exist in the section.
-
Create if exists: Creates the value only if the value currently exists in the section.
-
Create or add to existing section: Creates the value if the value does not currently exist in the section. If the value exists, it adds this value to the section in addition to the one that already exists. This is useful, for example, if you need multiple values of the same type, such as two "DEVICE=" values.
-
Create or append to existing value: Creates the value if the value does not currently exist in the section. If the value exists, it appends the data for the new value to the existing value. The first character in the value data needs to be the separator character, such as a space.
-
Delete: Deletes the value from the section.
-
Delete or remove from existing value: Deletes the value from the section, or, if the value has multiple data entries, removes this value’s data entry from the value. For example, suppose the following setting is in the win.ini file: Run = sol.exe calc.exe. Using this option, you can remove just calc.exe, leaving the following: Run = sol.exe. The first character in the value data needs to be a separator character, such as a space.
Move Up / Move Down
Use these options to position sections and values in the order in which you want them to be created, modified, or deleted.
In the tree, select the section or value to move, then click or .
Distribute Always
By default, Application Launcher distributes the modifications defined in the INI Settings list only at the following times:
-
The first time the application is launched on a workstation.
-
The first time the application is launched after the application’s version number ( tab > page) has been changed.
If the user has a NAL cache directory on his or her local machine, Application Launcher uses the information stored in the NAL cache directory to make the INI modification. If the user does not have a NAL cache directory (for example, the user is running Application Launcher through a terminal server client session) or if writing to the cache has been disabled for the user (User object > tab > page > option), Application Launcher uses the information stored in eDirectory.
To force Application Launcher to distribute an INI modification each time the application is launched, select the INI setting in the list, then select .
NOTE:After you save the Application object and open it again, settings that you mark as are grouped after settings that are not marked , regardless of their creation order or their forced order (by using the and arrows).
For example, if you have a section with two values (DAValue1 and DAValue2) and two non-Distribute Always value (Value3 and Value 4), the values are listed in the following order: Value3, Value4, DAValue1, DAValue2.
You can use the and arrows to change the order within the two groupings, but the group is always listed second. For example, using the previous ordering (Value3, Value4, DAValue1, DAValue 2), you could change the order of the first two values and the order of the second two values to get the following order: Value4, Value3, DAValue2, DAValue1. However, if you change the order to list the Distribute Always values first (DAValue2, DAValue1, Value4, Value3), when you save the Application object the order reverts to Value4, Value3, DAValue2, DAValue1.
Track Distribution Per User
If you have implemented roaming user profiles, use this option to ensure that particular .ini file settings are distributed to each workstation a user logs in to. You should enable this option for all .ini file settings that are not saved as part of roaming user profiles.
In the tree, select the setting you want to track, then select .
48.2.5 Text Files Page
The Text Files property page is available only on Application objects created for simple applications and AOT/AXT applications. It is not available on Application objects created for MSI applications, Web applications, and terminal server applications.
The Text Files property page, shown below, determines the modifications that Application Launcher makes to text files (such as config.sys and autoexec.bat) when distributing the application to a workstation.
Figure 48-11 Application Object > Distribution Options Tab > Text Files Page
Text Files
The Text Files tree shows the text files that Application Launcher modifies. Each modification to a file is displayed subordinate to the file.
File
This option lets you search for files or text in the tree and import files into the tree.
Click , then choose one of the following options:
-
Find: Searches for specific files or information in the tree.
-
Find next: Finds the next occurrence of the item specified by the initial search.
-
Import: Imports text files from another Application object’s .aot or .axt file. The Open dialog box defaults to *.axt for its file type display. If you are importing from an .aot file, you must change the file type display to *.aot or in order to select the .aot file.
Add
This option lets you add text file modifications to the tree. Only the modifications displayed in the tree are made when the application is distributed.
-
File: To add a text file to the tree, click > to create the file entry. You can type the filename or the path and filename (for example, autoexec.bat or c:\autoexec.bat). Only local workstation drives, UNC server paths, and macros are valid.
You should specify a path if possible. If you enter only the filename, Application Launcher searches all directories specified in the workstation’s PATH environment variable. If it does not find a matching filename, it assumes the file doesn’t exist and creates it in the first directory specified in the PATH variable.
-
Change: To add a change to a file that is in the Text Files list, select the file, click > to display the Edit Text File dialog box. Make the desired changes. Click in the Edit Text File dialog box for information about each of the dialog box fields.
You can add multiple modifications to a text file. For example, you might want to make one modification that replaces text in the file and another modification that adds text to the end of the file. Each modification you add is displayed beneath the text file in the list.
IMPORTANT:If you make changes to a text file (adding text, for example), you can add only one line at a time. If you press Enter to create a line break, your change saves.
Modify
To change the name of a text file, select the file in the tree, click , then specify the new name.
To edit one of the text file’s modifications, select the modification in the tree, click to display the Edit Text File dialog box, then make the desired changes. Click in the Edit Text File dialog box for information about each of the dialog box fields.
Delete
In the tree, select the text file or text file modification you want to delete > click .
Distribution Options for the Selected Item
Use these options to set individual distribution options for text files and text file modifications. The options change depending on whether you have selected a text file or a text file modification in the Text Files tree.
No Reboot Needed If Modified
This option appears only when you have selected a text file. Select this option if you don’t want users to reboot after you make changes to the selected text file. The and options on the Options > page override this setting.
Move Up / Move Down
These options appear only when you have selected a text file modification. Click or to position the modification according to the order in which you want it applied.
Distribute Always
By default, Application Launcher distributes the text file modifications defined in the list only at the following times:
-
The first time the application is launched on a workstation.
-
The first time the application is launched after the application’s version number ( tab > page) has been changed.
If the user has a NAL cache directory on his or her local machine, Application Launcher uses the information stored in the NAL cache directory to make the modification. If the user does not have a NAL cache directory (for example, the user is running Application Launcher through a terminal server client session) or if writing to the cache has been disabled for the user (User object > tab > page > option), Application Launcher uses the information stored in eDirectory.
To force Application Launcher to distribute a text file modification each time the application is launched, select the modification in the list, then select .
NOTE:After you save the Application object and open it again, modifications that you mark as are grouped after modifications that are not marked , regardless of their creation order or their forced order (by using the and arrows).
For example, if you have a file with two modifications (DAMod1 and DAMod2) and two non-Distribute Always modifications (Mod3 and Mod4), the modifications are listed in the following order: Mod3, Mod4, DAMod1, DAMod2.
You can use the and arrows to change the order within the two groupings, but the group is always listed second. For example, using the previous ordering (Mod3, Mod4, DAMod1, DAMod 2), you could change the order of the first two modifications and the order of the second two modifications to get the following order: Mod4, Mod3, DAMod2, DAMod1. However, if you change the order to list the modifications first (DAMod2, DAMod1, Mod4, Mod3), when you save the Application object the order reverts to Mod4, Mod3, DAMod2, DAMod1.
Track Distribution Per User
If you have implemented roaming user profiles, use this option to ensure that particular text file modifications are distributed to each workstation a user logs in to. You should enable this option for all modifications that are not saved as part of roaming user profiles.
In the list, select the desired modification, then select .
48.2.6 Distribution Scripts Page
The Distribution Scripts property page is available on Application objects created for simple applications, AOT/AXT applications, and MSI applications only. It is not available on Application objects created for Web applications and terminal server applications.
As part of the process of distributing an application, Application Launcher can launch a script engine to execute a “before distribution” script and an “after distribution” script (for details about the order of script execution, see Script Execution Order). The Distribution Scripts property page, shown below, defines the script engine that you want Application Launcher to use and the scripts you want executed.
Figure 48-12 Application Object > Distribution Options Tab > Distribution Scripts Page
On Windows 2000/XP, distribution scripts are run in the secure system space, which means that users do not see any of the script commands or command results. Therefore, you should not include any commands that require or initiate user interaction. If you do so, the script halts at that point. For example, you would not want to include a command to run a program that requires user interaction because the program, which runs in secure system space, is never displayed to the user. On Windows 98, distribution scripts are run in the user space (because there is no system space).
This section includes information about the following items available on the Distribution Scripts page:
Run Before Distribution
Use this text window to enter any script commands you want executed before the application is distributed. Do not use extended characters in the script; extended characters are not supported. For script example, see Script Example.
Run After Distribution
Use this text window to enter any script commands you want executed after the application is distributed. Do not use extended characters in the script; extended characters are not supported. For script example, see Script Example.
NOTE:If you configure an application to launch a script using the Run After Distribution method, and if that application is associated to a workstation, the distribution script runs every time a new user initially logs in. Distribution items (such as files and registry keys) are not run for the new user if the distribution has already been delivered to the workstation.
For more information, see TID 3591452 (Run After Distribution Application Script Is Not Working as Expected) in the Novell Support Knowledgebase.
Script Engine Location
The script engine determines the script commands and scripting language you need to use. If you do not define a script engine in the field, Application Launcher uses the Novell Client™ as the script engine (if the workstation has the Novell Client installed), which means that you can use most Novell Client login script commands (see Supported Novell Client Login Script Commands).
If you want to use a script engine other than the Novell Client, specify the alternate script engine. The script engine must reside in a location that is always available to users, such as their local drives. The script engine can reside on a network server only if users can map a drive to the server (for example, through the Novell Client or the Client for Microsoft Networks). If Application Launcher cannot find the script engine, it displays an error to the user and fails to distribute the application.
If you use the Windows command interpreter as the script engine, you must include the /C switch, as shown in the following examples:
-
Windows 2000/XP: %*winsysdir%\cmd.exe /c
-
Windows 98: %*windir%\command.com /c
The %*winsysdir% and %*windir% variables specify the Windows system directory (for example, c:\winnt\system32), and the /c switch instructs the command interpreter to execute the script and then stop. If the /c switch is not used, the script does not complete.
For a script example, see Script Example.
Script File Extension
This applies only if you specified a script engine in the Script Engine Location field.
When the application is distributed, Application Launcher creates temporary script files for the scripts and scripts. These files are passed to the script engine, which then executes the script. You need to specify the file extension that the script engine requires for its script files.
For a script example, see Script Example.
Script Example
The following script uses the Windows 2000/XP command interpreter as the script engine. Before the distribution occurs, a listing of the c:\ directory is saved to a text file and the autoexec.bat file is backed up.
Run Before Distribution Field
dir c:\ >c:\1.txt copy autoexec.bat autoexec.bak /y
Script Engine Location Field
cmd.exe /c
Enter or Select the Extension of the Script File Field
.bat
Script Execution Order
Application Launcher can execute up to four different scripts when distributing and launching an application:
-
Distribution scripts: Run Before Distribution and Run After Distribution ( tab > page)
-
Launch scripts: and ( tab > page)
Application Launcher executes the scripts in the following order:
-
Run Before Launching script executed
-
Run Before Distribution script executed
-
Application distributed (files copied, settings modified, etc.)
-
Run After Distribution script executed
-
Application launched
-
Application closed (by user)
-
Run After Termination script executed
NOTE:Selecting for individual items on certain pages of the Distribution Options Tab causes those items to be processed after the post distribution objects, so the order above becomes invalid. The pages where you will see this behavior include:
-
Icons/Shortcuts page
-
Registry page
-
Application Files page
-
INI Settings page
-
Text Files page
Supported Novell Client Login Script Commands
When using the Novell Client as the script engine, you can use all but the following script commands:
Table 48-1 Supported Novell Client Login Script Commands
|
CLS |
INCLUDE |
PCOMPATIBLE |
|
DISPLAY |
LASTLOGINTIME |
SCRIPT_SERVER |
|
EXIT |
NO_DEFAULT |
SET_TIME |
|
FDISPLAY |
NOSWAP |
SWAP |
|
IF MEMBER OF |
PAUSE |
WRITE |
Application Launcher does not output anything to the screen or display script errors.
For script commands, syntax, and examples, see the Novell Client documentation on the Novell Documentation Web site.
48.2.7 Pre-Install Schedule Page
The Pre-Install Schedule property page is available only on Application objects created for simple applications, AOT/AXT applications, and MSI applications. It is not available on Application objects created for Web applications and terminal server applications.
The Pre-Install Schedule property page, shown below, enables you to distribute portions of the application to a workstation before the user launches the application the first time. Because you can schedule the distribution, you can perform an off-line, or lights-out, distribution of the application and save the user some of the wait typically associated with a distribution. For example, you could pre-install the application after work hours so the application is ready to use the next day.
Figure 48-13 Application Object > Distribution Options Tab > Pre-install Schedule Page
With a pre-install, all workstation-related distribution processes (file copying, modifying text files, .ini files, and workstation registry settings) are performed prior to launching of the application. When the user launches the application, the user-specific distribution processes (modifying user registry keys and so forth) are completed.
You can pre-install an application that is associated with either workstations or users:
-
For user-associated applications, the user must be logged in and Application Launcher must be running. Application Launcher uses the logged-in user’s credentials (authentication and file system access) to distribute the application.
-
For workstation-associated applications, the workstation must be running but Application Launcher does not need to be running. If the application is a non-MSI application (for example, an AOT application), NAL Workstation Helper uses the workstation's credentials to distribute the application. If the application is an MSI application, NAL Workstation Helper uses the logged-in user's credentials. If you want it to use the workstation's credentials rather than require a user to be logged in (for example, to perform a lights-out distribution of the MSI application), you must enable the option ( tab > page).
When pre-installing a workstation-associated application, you should also be aware of the following:
-
Any shortcuts, registry settings, application files, INI settings, and text file modifications that are marked as must also be marked as . Otherwise, they are not distributed. To do so, use the and options on the Icons/Shortcuts page, Registry page, Application Files page, INI Settings page, and Text Files page.
-
On Windows 2000/XP workstations, if a user is not logged in, any user-specific macros ( > page) point to the default user directories. This scenario affects the ability to place folders and icons on the Start menu. There are two ways to solve this issue: 1) Mark the macro entries in the Application object as or 2) change the user-specific macro to an All Users macro (such as %*PROGRAMS% to %*COMMONPROGRAMS%).
-
If an application requires a reboot during installation, you must select or in the Reboot group box and in the group box.
Pre-Install Application
Select this option to enable the application to be pre-installed. If you don't select this option, the application is not pre-installed, even if you establish a schedule.
Schedule Type
Select the type of schedule you want to use. You can choose , , or.
None
Use this option to indicate no schedule. The application is pre-installed as soon as the application is associated with a user or workstation (Associations page).
Specified Days
Use this option to select specific dates when you want to pre-install the application. You cannot select more than 350 specific dates.
-
Date range: The Date Range list displays all dates when the application can be pre-installed. To add a date, click , select the date you want, then click to display it in the list.
-
Time for selected dates: Select the availability start time and end time. The times apply to all dates in the list.
NOTE:The time increments in 5 minute intervals, with the earliest available start time being 00:00 (12:00 a.m.) and the latest end time being 23:55 (11:55 p.m.). This means there is always a 5-minute time period from 11:55 p.m. to 12:00 midnight when the application is unavailable. If you want the application to be available the entire day, you need to use the schedule type. For more information, see Range of Days.
-
Spread from start time (in minutes): The option spreads out user access times over the number of minutes specified so the application doesn’t become available to all users at the same time. If you anticipate all users launching the application as soon as it becomes available and the application is being distributed or run from the network, you can use this option to avoid possible network overload.
For example, if you have a moderate number of users to whom the application is to be distributed (say about 100), you might specify a one-hour (60 minute) block of time (starting at the scheduled start time) to randomly distribute the application: thus all users will gain access to the application some time during the first sixty minutes after the scheduled start time.
If you want to substantially ease the load on your servers caused by the application distribution, or if you have bandwidth concerns, you might want to make the application distribute randomly throughout the time of availability. To spread out access times across the entire time ( and ) that the application is available, use the total availability time specified for that application in terms of minutes. This will require that you make the maximum time available for each day you specify. For example, if an application is configured for a typical business day in the United States (9 hours per day: 8:00 a.m. to 5:00 p.m.), you calculate the total time of availability for that application like this:
Number of specified hours x 60 minutes per hour = Total availability time per day
Using this equation, the example above would be calculated like this:
9 x 60 (minutes per hour) = 540 minutes of availability
In this example, when you enter 540 minutes in the field, the application is distributed randomly for the entire 540 minutes that you have made it available on that scheduled day. Note that this might not be suitable for applications that must be distributed in a timely fashion, such as anti-virus updates. Note also that this is an example only: you can schedule the distribution for any specified amount of time for any day of the week.
Remember that the setting makes the last five minutes of a day unscheduleable, so you need to consider these five minutes if the application schedule ends at 11:55 p.m. for that day.
Range of Days
Use this option to select a range of days to pre-install the application. You can also use this option to pre-install the application only on certain days of the week within a given range of dates.
-
Date range: To define the range of days, select a start date and an end date > select the days (Sunday through Saturday) within the established date range. By default, all days are selected; a day is selected when the button appears to be pressed in.
-
Time for selected range: Select the availability start time and end time. This option works differently depending on whether the date range includes one day, multiple days, or all seven days. If the date range includes one to six days (but not all seven days), the application is available between the start and end times on those days. For example, if you make the application available on Monday between 8:00 and 5:00, it is available during those hours. However, if the date range includes all seven days, the times are ignored and the application is available every day, 24 hours a day.
-
Spread from start time (in minutes): The option spreads out user access times over the number of minutes specified so the application doesn’t become available to all users at the same time. If you anticipate all users launching the application as soon as it becomes available and the application is being distributed or run from the network, you can use this option to avoid possible network overload.
For example, if you have a moderate number of users to whom the application is to be distributed (say about 100), you might specify a one-hour (60 minute) block of time (starting at the scheduled start time) to randomly distribute the application: thus all users will gain access to the application some time during the first sixty minutes after the scheduled start time.
If you want to ease the load of the application distribution on your servers or if you have bandwidth concerns, you might want to make the application distribute randomly throughout the time of availability. To spread out access times across the entire time ( and ) that the application is available, use the total availability time specified for that application in terms of minutes. For example, if a workstation-associated application is configured for an entire 24-hour, three-shift day, you can calculate the total time of availability for that application like this:
Number of days in date range x Time of availability per day = Total availability time
Using this equation, and making sure to convert hours to minutes, the example above would be calculated like this:
7 (days) x 24 (hours) = 168 hours of availability
168 x 60 (minutes per hour) = 10,080 minutes of availability
When you enter 10800 minutes in the field, the application is distributed randomly for the entire10800 minutes that you have made it available. Note that this is not suitable for applications that must be distributed in a timely fashion, such as anti-virus updates.
-
Use this schedule in GMT for all clients: The schedule is based on the workstation’s time zone. If your network spans different time zones and you schedule an application to run at 1:00 p.m., it runs at 1:00 p.m. in each time zone. You can select this option to have workstations run applications at the same time regardless of their time zones (for example, 1:00 p.m. Rome time and 4:00 a.m. Los Angeles time).
48.2.8 Pre-Distribution Process Termination Page
The Pre-Distribution Process Termination property page, shown below, determines the executables and services that Application Launcher terminates before distributing the application to a workstation.
Figure 48-14 Application Object > Distribution Options > Pre-distribution Process Termination Page
Application Launcher can terminate any process running in the user space. In addition, it can terminate any service running in the system space (provided the service is displayed in the Microsoft Management Console’s Services list and you use that service name). Application Launcher cannot terminate executables running in the system space.
When terminating a process, Application Launcher terminates all processes that match the specified filename. For example, if you specify notepad.exe as the process executable to terminate, all instances of notepad.exe terminate. In other words, if both c:\notepad.exe and c:\winnt\notepad.exe are running, both terminate. You cannot target specific instances of a process (for example, only c:\notepad.exe or c:\winnt\notepad.exe).
Add
This option lets you add processes to the list. Only processes displayed in the list are terminated before the application is distributed.
Click to display the Edit Processes dialog box. In the or box, enter the executable (.exe) filename or enter the service name (as defined in the Services list in the Microsoft Management Console). Do not include the full file paths; if you do so, the termination fails.
Click if the process is a Windows service, then click to add the process to the list.
Modify
You can modify a process name and type. Select the process in the list, then click .
Delete
Select the process you want to delete from the list, then click .
Up-Arrow and Down-Arrow
Select a process from the list, then click the up-arrow to move the process up in the list or click the down-arrow to move it down in the list. Application Launcher terminates the processes in the order they are listed, from top to bottom.
48.2.9 Options Page
The Options property page is available on Application objects created for all application types (simple, AOT/AXT, MSI, Web, and terminal server).
The Options property page, shown below, determines general options to be used by Application Launcher when distributing the application to a workstation.
Figure 48-15 Application Object > Distribution Options Tab > Options Page
GUID and Version Number
Application Launcher uses the application's GUID (global unique identifier) and version number to manage the distribution of the application. When Application Launcher distributes an application to a workstation, it adds the GUID and the version number to the workstation's Windows registry. If either the GUID or version number changes, Application Launcher redistributes the application.
The GUID is randomly generated when the Application object is created. In general, you should not need to change the GUID. There are, however, situations such as the following that might necessitate changing an application’s GUID:
-
The Application object is accidentally deleted from eDirectory. You re-create the Application object, but when you do so it is given a new, unique GUID. Because the new GUID causes the application to be redistributed to all users and workstations associated with the application, you use the GUID Manager (available by clicking the button) to change the new GUID to the old GUID.
-
You have multiple Application objects for the same application (to enable fault tolerance, load balancing, site lists, and so forth). You want to make sure that all Application objects have the same GUID so that the application is distributed one time only regardless of the Application object that is used. You use the GUID Manager to synchronize the GUIDs.
-
Site 1 and Site 2 have the same applications chains. You must synchronize the GUIDs of each application in the chain at Site 1 with the GUIDs of each matching application at Site 2. Use the GUID Manager to synchronize the GUIDs.
The version number is a unique number between 0 and 65535 (0 is assigned when the Application object is first created) that you can increment as you make revisions to the Application object. If you make a change to the Application object’s information, you should increment the version number so that Application Launcher redistributes the application. Application Launcher redistributes the application only if the new version number is larger than the current version number in the workstation’s Windows registry.
Options
These options let you determine if Application Launcher should redistribute the application each time the application is run and if Application Launcher should prompt the user to accept or reject the distribution. The Options fields are not displayed on Application objects created for Web applications and Terminal Server applications because they do not apply
Distribute Always
By default, Application Launcher makes the distribution changes associated with the Application object at the following times:
-
The first time the application is launched on a workstation.
-
The first time the application is launched after the application's version number has been changed.
To force Application Launcher to redistribute the application each time it is launched, select .
This option is useful to ensure that all application settings and files are updated every time the application runs. If the user has a NAL cache directory on his or her local machine, the files and settings are distributed from the NAL cache directory. If the user does not have a NAL cache directory (for example, the user is running Application Launcher through a terminal server client session) or if writing to the cache has been disabled for the user (User object > tab > page > option), the application files and settings are updated from eDirectory. To force a distribution from eDirectory even if the user has a NAL cache directory on his or her local machine, you need to change the application's version number or have individual users right-click the Application object and click .
If you need only specific files or settings to be distributed each time, you can update these on a case-by-case basis. For example, if you want to always distribute a particular registry key and value, you can set the option on the Registry Settings page tab) for that particular key and value.
Because this setting causes all application files and settings to be distributed each time, it overrides the option on the Registry, INI Settings, Application Files, Icons/Shortcuts, and Text Files pages (Distribution Options tab).
Prompt Before Distribution
Select this option to prompt users to accept the distribution. Users are prompted the first time they click the application icon; all subsequent times they are not prompted. To better help users make a decision about installing the application, the prompt includes the text you’ve entered in the Description page ( tab).
Distribute in Workstation Security Space if Workstation Associated
The function of this option is conditional, based on whether you are configuring an MSI application or an AOT/Simple application.
If the application is an MSI: This check box is not selected by default. Workstation-associated MSI applications are normally distributed in the user security space, meaning that Application Launcher uses the user’s credentials and file system access.
Select this option to instruct Application Launcher to distribute the application in the workstation security space. Application Launcher turns over distribution to the NAL Workstation Helper, which runs in the system space and uses the workstation’s credentials. Using this option enables you to 1) do a lights-out distribution of the application and 2) better secure the application’s source .msi files by giving the workstation, not the user, access to the source .msi files. Consider the following examples:
-
You want to associate the application with a workstation and have it distributed before the user launches it. This is referred to as a lights-out distribution. To do so, you associate the application with the workstation on the Associations page ( tab), set the distribution schedule on the page ( tab), and then enable this option. As long as the workstation is running at the scheduled distribution time, the NAL Workstation Helper distributes the application using the workstation security space rather than the user space normally used for installation of MSI applications.
-
You want to distribute the application to a workstation but you don’t want to give the user rights to the application's source files on the network. To do so, you associate the application with the workstation on the page ( tab) and then select this option. When the user launches the application, Application Launcher calls NAL Workstation Helper. Workstation Helper distributes the application using the workstation security space.
It is important to remember that Application Launcher uses the workstation's credentials, not the user's credentials, to distribute the application. This means that you must assign the workstation the appropriate file system rights to access the network location where the source .msi files reside.
Not all MSI applications can be installed using this option. Some MSI applications have dependencies on a logged-in user (for example, to read and write to the HKCU hive in the Windows registry). In this situation, you must deselect this option in order to have the distribution occur in the user security space and not the workstation security space.
NOTE:If an application requires a reboot during installation, you must select or in the group box and in the group box.
If the application is an AOT or a simple application: This check box is selected by default. Workstation-associated AOT or simple applications are normally distributed in the workstation security space, meaning that Application Launcher uses the workstation’s credentials and file system access.
Deselect this option to instruct Application Launcher to distribute the application in the user security space. Application Launcher then runs in the user space and uses the user credentials to distribute the files, even if the application is associated to the workstation.
Reboot
Select how a workstation reboot should occur. The available options are:
-
If needed: Application Launcher reboots the workstation if changes need to be made that cannot occur while Windows is running (such as replacing open DLLs).
-
Always: Application Launcher always reboots the workstation after distributing the application.
-
Never: Application Launcher does not reboot the workstation. The changes take effect the next time the workstation reboots.
The NAL Service, which runs in the “system” space rather than the “user” space, distributes workstation-associated applications on Windows 2000/XP workstations. If you select the option, the NAL Service automatically reboots the workstation, even if you've set the option to (see below); in other words, the NAL Service ignores the setting. The same is true if you select the option and a reboot is needed.
Prompt Reboot
Select whether or not the user is prompted to reboot the workstation. If you select , but deselect the option ( tab > page), the user is not prompted (in other words, disabling the option overrides enabling the option).
48.2.10 BITS Settings Page
This functionality is available beginning with Support Pack 1 of Novell ZENworks 7.
The BITS Settings property page is available only on Application objects created for simple applications, AOT/AXT applications, and MSI applications. It is not available on Application objects created for Web applications and terminal server applications.
The BITS Settings page lets you configure the settings used by the Microsoft Background Intelligent Transfer Service (BITS) when transferring the application to a workstation. BITS is used only if Novell Application Launcher and the application are configured to use BITS (see Section 34.0, Advanced Distribution: Transferring Applications Using BITS).
Figure 48-16 Application Object > Distribution Options Tab > BITS Setting Page
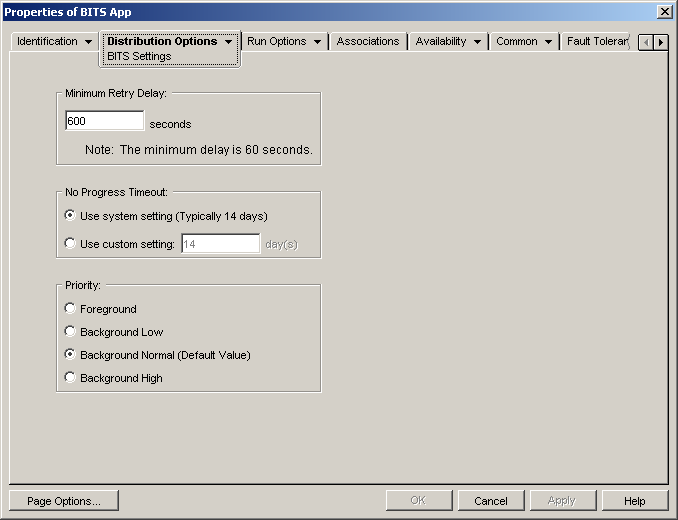
Minimum Retry Delay
If BITS encounters an error during transfer of the application, BITS classifies it as a fatal error or a transient error. BITS cannot recover from fatal errors; fatal errors require administrator intervention to fix the problem. BITS can possibly recover from transient errors.
Use this option to specify the minimum amount of time you want BITS to wait after a transient error occurs before trying to transfer the application again. The default is 600 seconds, or 10 minutes. The minimum setting is 60 seconds. The maximum setting is 2,147,483,647 seconds.
No Progress Timeout
Use this option to specify how many days you want BITS to continue to attempt to transfer the application after a transient error has occurred if no progress is being made.
-
Use System Setting (Typically 14 Days): Select this option to use the Windows system setting. The Windows system setting comes from either 1) the BITS default setting, which is 14 days, or 2) the Timeout (Days) for Inactive Jobs setting in the Windows Group Policy, which is undefined by default. If you select this option, the BITS default setting (14 days) is used unless the Windows Group Policy setting has been assigned a value. You can use the Windows Group Policy Editor (gpedit.msc) to view and change the Windows Group Policy setting.
-
Use Custom Setting: Select this option to manually enter a timeout period.
-
The minimum setting is 0 days. Enter 0 only if you do not want BITS to attempt to transfer the application again after it encounters a transient error; in this case, BITS immediately returns control of the transfer to Application Launcher.
-
The maximum setting is 24,855 days. However, BITS compares this number to the number in the Timeout (Days) for Inactive Jobs setting in the Windows Group Policy. If the Timeout (Days) for Inactive Jobs setting is less than this number, BITS uses the policy setting. For example, if you enter 45 days for this setting, but the policy is set to 30 days, BITS uses 30 days. If the Timeout (Days) for Inactive Jobs setting is undefined (the default state), the policy setting defaults to 90 days. In this case, for example, if you enter 91 days in this setting, BITS uses the policy setting (90 days).
-
If any transfer progress is made during the timeout period, the counter is reset. If BITS times out because no progress is being made, control of the transfer is returned to Application Launcher, which then transfers the application using its standard distribution process.
Priority
Use this option to assign a transfer priority level to the application. You can choose from one foreground priority and three background priorities (low, normal, high).
The foreground priority causes BITS to transfer the application in the foreground. Foreground transfers are the highest priority and are processed before any background transfers. Foreground transfers compete for network bandwidth with other applications, which can impede the user’s network experience. Unless the timing of the transfer is critical or the user is actively waiting, you should use a background priority. In addition, BITS only supports foreground priority for files less than 2 GB.
For the three background priorities, the priority level determines when the transfer is processed relative to other transfers in the queue. Higher priority transfers preempt lower priority transfers. Transfers with the same priority level share transfer time, which prevents a large transfer from blocking the transfer queue. Lower priority transfers do not receive transfer time until all higher priority transfers are completed or are in an error state.