25.0 Override-Password Key Generator
Productivity interruptions that a user might experience due to restrictions to connectivity, disabled software execution, or access to removable storage devices are probably caused by the security policy the Security Client is enforcing. Changing locations or firewall settings usually lifts these restrictions and restores the interrupted functionality. However, in some cases the restriction might affect all locations and firewall settings, or the user might be unable to make a location or firewall setting change.
When this occurs, the restrictions in the current policy can be lifted via a password override to allow productivity until the policy can be modified. This feature allows an administrator to set up a password-protected override for specified users and functionality, which temporarily permits the necessary activities.
Password overrides disable the current security policy and restores the default All Open policy for a predefined period of time. After the time-limit expires, or if the endpoint reboots, the current policy is restored. The password for a policy is set in the security policy's Global settings.
Password override does the following:
-
Overrides application blocking
-
Allows users to change locations
-
Allows users to change firewall settings
-
Overrides hardware control (thumb drivers, CD ROM, etc.)
The password in a policy should never be issued to an end user. You should use the Override-Password Key Generator to generate a key for short-term use.
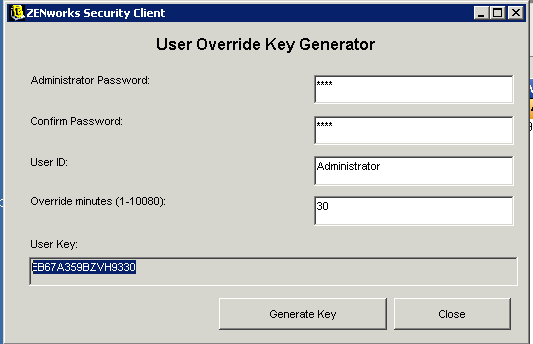
To generate an override key:
-
On the Management Console machine, click .
-
Specify the global policy password in the box, and confirm it in the next box.
-
Specify the local user logged in on the target machine.
The username is case sensitive.
-
Specify the amount of time the policy should be disabled.
-
Click the button to generate an override key.
-
Copy the key and give it to the end user.
To use the key, the user must open the About dialog box in the ZENworks Security Client, click the button, then enter the key. For detailed instructions, see Password Override
in the ZENworks Endpoint Security Client for Windows 2000/XP User Guide or Password Override
in the ZENworks Endpoint Security Client for Windows Vista/7 User Guide.
This key is valid for that user's policy only and only for the specified amount of time or until the computer reboots. Once the key has been used or the computer reboots, the key cannot be used again.
If you publish a new policy to fix the problems with the user’s current policy, you should instruct the user to check for a policy update. For instructions, see Policy Updates
in the ZENworks Endpoint Security Client for Windows 2000/XP User Guide or Policy Updates
in the ZENworks Endpoint Security Client for Windows Vista/7 User Guide.