3.1 Adding a Profile Using the Wizard
is designed to set up Novell AppArmor profiles using the AppArmor profiling tools, aa-genprof (generate profile) and aa-logprof (update profiles from learning mode log file). For more information about these tools, refer to Section 4.6.3, Summary of Profiling Tools.
-
Stop the application before profiling it to ensure that application start-up is included in the profile. To do this, make sure that the application or daemon is not running.
For example, enter rcPROGRAM stop (or /etc/init.d/PROGRAM stop) in a terminal window while logged in as root, replacing PROGRAM with the name of the program to profile.
-
Start YaST and select .
-
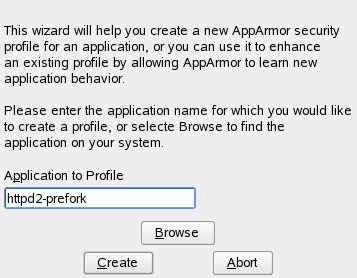
Enter the name of the application or browse to the location of the program.
-
Click . This runs an AppArmor tool named aa-autodep, which performs a static analysis of the program to profile and loads an approximate profile into the AppArmor module. For more information about aa-autodep, refer to aa-autodep—Creating Approximate Profiles.
Depending on whether the profile you are about to create already exists either in the local profile repository (see Section 2.4, Using the Local AppArmor Profile Repository) or in the external profile repository (see Section 2.5, Using the External AppArmor Profile Repository) or whether it does not exist yet, proceed with one of the following options:
-
Determine whether you want to use or fine-tune an already existing profile from your local profile repository, as outlined in Step 5.
-
Determine whether you want to use of fine-tune an already existing profile from the external profile repository, as outlined in Step 6.
-
Create the profile from scratch and proceed with Step 7 and beyond.
-
-
If the profile already exists in the local profile repository under /etc/apparmor/profiles/extra, YaST informs you that there is an inactive profile which you can either use as a base for your own efforts or which you can just accept as is.
Alternatively, you can choose not to use the local version at all and start creating the profile from scratch. In any case, proceed with Step 7.
-
If the profile already exists in the external profile repository and this is the first time you tried to create a profile that already exists in the repository, configure your access to the server and determine how to use it:
-
Determine whether you want to enable access to the external repository or postpone this decision. In case you have selected , determine the access mode (download/upload) in a next step. In case you want to postpone the decision, select and proceed directly to Step 7.
-
Provide username and password for your account on the profile repository server and register at the server.
-
Select the profile to use and proceed to Step 7.
-
-
Run the application to profile.
-
Perform as many of the application functions as possible so learning mode can log the files and directories to which the program requires access to function properly. Be sure to include restarting and stopping the program in the exercised functions. AppArmor needs to handle these events as well as any other program function.
-
Click to parse the learning mode log files. This generates a series of questions that you must answer to guide the wizard in generating the security profile.
If requests to add hats appear, proceed to Section 5.0, Profiling Your Web Applications Using ChangeHat.
The questions fall into two categories:
-
A resource is requested by a profiled program that is not in the profile (see Figure 3-2). Allow or deny access to a specific resource.
-
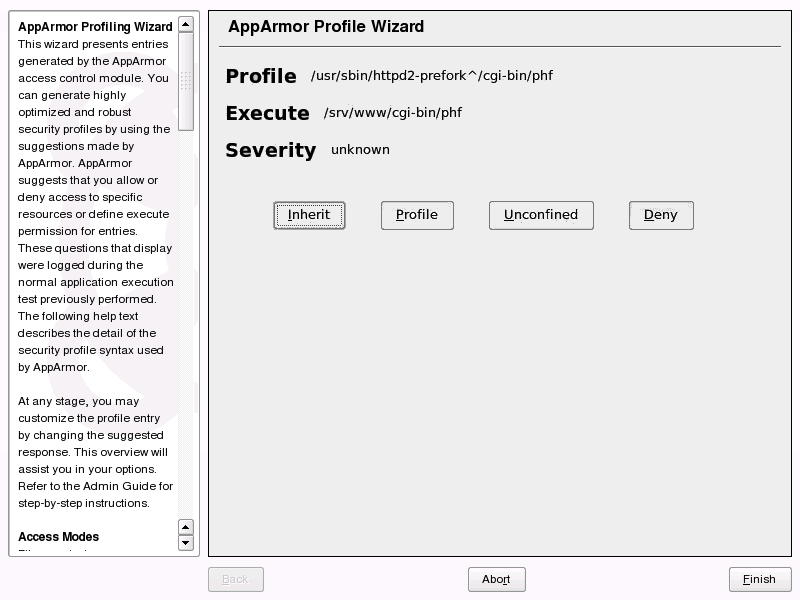
A program is executed by the profiled program and the security domain transition has not been defined (see Figure 3-3). Define execute permissions for an entry.
Each of these cases results in a series of questions that you must answer to add the resource to the profile or to add the program to the profile. For an example of each case, see Figure 3-2 and Figure 3-3. Subsequent steps describe your options in answering these questions.
NOTE: Varying Processing Options
Depending on the type of entry processed, the available options vary.
Figure 3-2 Learning Mode Exception: Controlling Access to Specific Resources
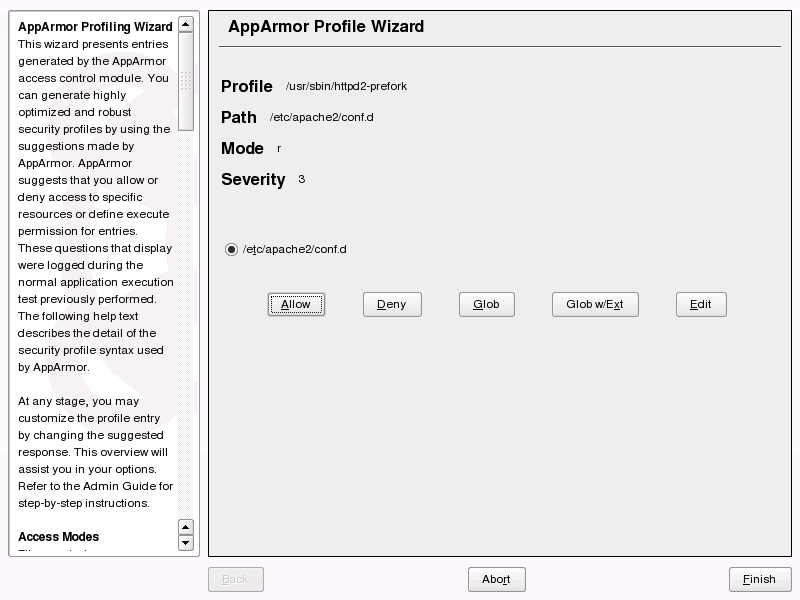
Figure 3-3 Learning Mode Exception: Defining Execute Permissions for an Entry
-
-
The begins suggesting directory path entries that have been accessed by the application profiled (as seen in Figure 3-2) or requires you to define execute permissions for entries (as seen in Figure 3-3).
-
For Learning Mode Exception: Controlling Access to Specific Resources: Select the option that satisfies the request for access, which could be a suggested include, a particular globbed version of the path, or the actual pathname. Depending on the situation, these options are available:
- #include
-
The section of a Novell AppArmor profile that refers to an include file. Include files give access permissions for programs. By using an include, you can give the program access to directory paths or files that are also required by other programs. Using includes can reduce the size of a profile. It is good practice to select includes when suggested.
- Globbed Version
-
Accessed by clicking . For information about globbing syntax, refer to Section 2.1.2, Paths and Globbing.
- Actual Pathname
-
Literal path that the program needs to access to run properly.
After selecting a directory path, process it as an entry to the Novell AppArmor profile by clicking or . If you are not satisfied with the directory path entry as it is displayed, you can also or it.
The following options are available to process the learning mode entries and build the profile:
- Allow
-
Grant the program access to the specified directory path entries. The suggests file permission access. For more information about this, refer to Section 2.1.3, File Permission Access Modes.
- Deny
-
Click to prevent the program from accessing the specified paths.
- Glob
-
Clicking this modifies the directory path (using wild cards) to include all files in the suggested directory. Double-clicking it grants access to all files and subdirectories beneath the one shown. For more information about globbing syntax, refer to Section 2.1.2, Paths and Globbing.
- Glob w/Ext
-
Modify the original directory path while retaining the filename extension. A single click causes /etc/apache2/file.ext to become /etc/apache2/*.ext, adding the wild card (asterisk) in place of the filename. This allows the program to access all files in the suggested directories that end with the .ext extension. When you double-click it, access is granted to all files with the particular extension and subdirectories beneath the one shown.
- Edit
-
Edit the highlighted line. The new edited line appears at the bottom of the list.
- Abort
-
Abort aa-logprof, losing all rule changes entered so far and leaving all profiles unmodified.
- Finish
-
Close aa-logprof, saving all rule changes entered so far and modifying all profiles.
Click or for each learning mode entry. These help build the Novell AppArmor profile.
NOTE: The number of learning mode entries corresponds to the complexity of the application.
-
For Learning Mode Exception: Defining Execute Permissions for an Entry: From the following options, select the one that satisfies the request for access. For detailed information about the options available, refer to Section 2.1.3, File Permission Access Modes.
- Inherit
-
Stay in the same security profile (parent's profile).
- Profile
-
Require a separate profile to exist for the executed program. When selecting this option, also select whether AppArmor should sanitize the environment when switching profiles by removing certain environment variables that can modify the execution behavior of the child process. Unless these variables are absolutely required to properly execute the child process, always choose the more secure, sanitized option.
- Unconfined
-
Execute the program without a security profile. When prompted, have AppArmor sanitize the environment to avoid adding security risks by inheriting certain environment variables from the parent process.
WARNING: Risks of Running Unconfined
Unless absolutely necessary, do not run unconfined. Choosing the option executes the new program without any protection from AppArmor.
- Deny
-
Click to prevent the program from accessing the specified paths.
- Abort
-
Abort aa-logprof, losing all rule changes entered so far and leaving all profiles unmodified.
- Finish
-
Close aa-logprof, saving all rule changes entered so far and modifying all profiles.
-
-
Repeat the previous steps if you need to execute more functionality of the application.
When you are done, click . Choose to apply your changes to the local profile set. If you have previously chosen to upload your profile to the external profile repository, provide a brief change log entry describing your work and upload the profile. If you had postponed the decision on whether to upload the profile or not, YaST asks you again and you can create an account the upload the profile now or not upload it at all.
As soon as you exit the , the profile is saved both locally and on the repository server, if you have chosen to upload it. The profile is then loaded into the AppArmor module.