16.2 Provisioning Users and Groups
For users to access Filr, they must be provisioned on the Filr system. They can then be assigned access rights.
16.2.1 User Provisioning Overview
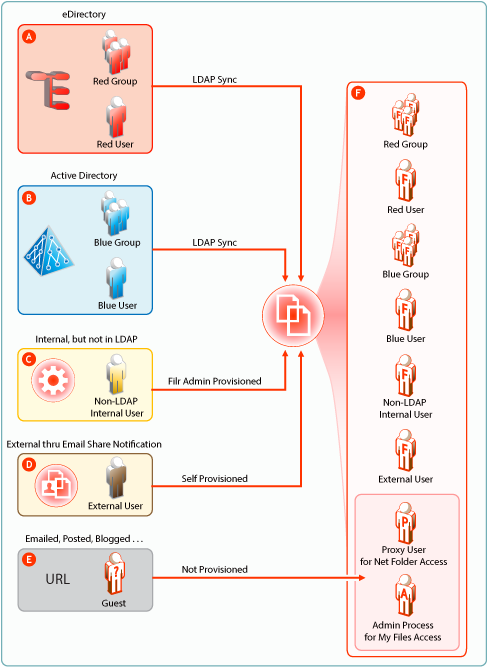
Figure 16-1 provides a high-level overview of the provisioning process that allows users and groups to access an organization’s internal data through Filr.
Figure 16-1 Provisioning Users and Groups
|
Letter |
Details |
|---|---|

|
eDirectory users are provisioned on Filr through LDAP/LDAPS synchronization. Synchronization is one-way. Password and other changes on the eDirectory side are handled in Filr without additional configuration. Password and other changes can be made to a user’s Filr configuration. However, they are not synchronized back to eDirectory. Instead, they are overwritten by the configuration in eDirectory with each synchronization. |

|
Active Directory (AD) users are provisioned on Filr through LDAP/LDAPS synchronization. Synchronization is one-way. Password and other changes on the AD side are handled in Filr without additional configuration. Password and other changes can be made to a user’s Filr configuration. However, they are not synchronized back to AD. Instead, they are overwritten by the configuration in AD with each synchronization. |

|
Filr administrators can also provision users on the Filr appliance. These are referred to as Local users in the documentation and Filr interfaces. |

|
External User accounts are created when share invitations are issued through email from Filr. The users provision themselves with a password, and so on when they log in to Filr. |

|
Public users (Guests) aren’t provisioned with accounts on Filr. Public users are anonymous to Filr and are allowed access to shared files in Net Folders through the Proxy User assigned to the Net Folder they are accessing. For shared files and folders in My Files, Public users gain access through the Filr admin process. |
16.2.2 LDAP Proxy User Role and Rights
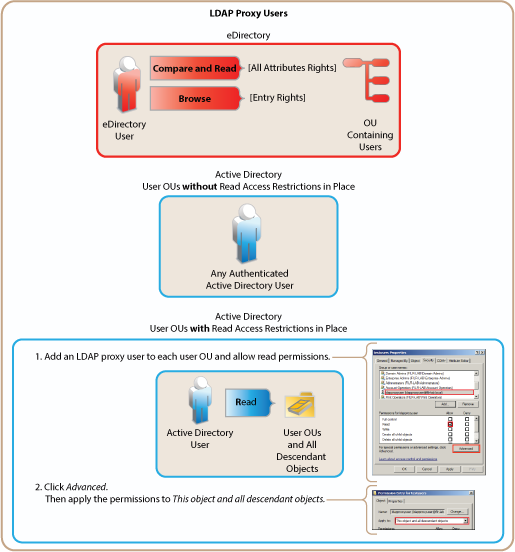
Filr synchronizes LDAP users by leveraging proxy users in the targeted LDAP directories that have sufficient rights to read the user and group information required by Filr.
Currently, eDirectory and Active Directory are supported as LDAP identity stores.
The rights required for LDAP synchronization are platform-specific, and for Active Directory they vary depending on whether read access restrictions are in place, as illustrated in Figure 16-2.
Figure 16-2 Rights Required for LDAP Proxy Users
16.2.3 Types of Filr Users
-
LDAP Synchronized Users and Groups: Can be synchronized from an internal LDAP identity store.
After users and groups are provisioned through an initial synchronization, they have accounts in Filr that correspond to their original identities, but these are only secondary. By leveraging the rights of one or more LDAP proxy users in the directory, Filr synchronizes regularly to keep authentication credentials current, update changes in home directory and file system rights assignments, and so on.
-
Filr Admin Created Users and Groups: Can be created by Filr administrators.
Admin-created groups are managed as part of the Filr system. They can be assigned personal storage, but access to Net Folders and other users’ home directories happens only through Filr-based sharing.
-
External, Self-Provisioned Users: Can be invited to participate through share invitations.
When they respond to the invitations, they are given the opportunity to self-provision an account on the Filr server.
-
Guest Users: When Filr administrators allow it, Filr users can share the URLs to files in Net Folders and My Files, making them available to the general public. Those who access files in this way are referred to as
Guest
users. Guest users are not provisioned and are anonymous from a Filr perspective.For example, a city government might give Filr user accounts to only key city knowledge workers and allow other city workers and regular citizens to access the site to see a listing of upcoming events, read city news, report complaints, and so forth.
When Guest users log in they can:
-
See the Shared with Me tab with all files and folders that are shared with the public.
-
Search within publicly shared files and folders.
-
Comment on items unless the Guest access is read only option is selected in Web Application configuration settings.
-
16.2.4 The Role of Groups in Filr
Users can be assigned rights on Filr as members of groups, including as members of All Internal Users group, which includes those whose accounts were created as a result of an email share invitation.