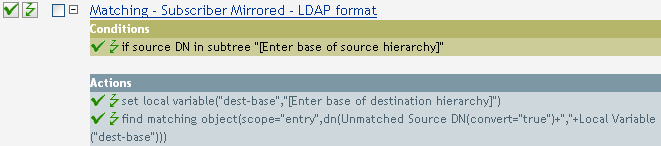
6.12 Matching - Subscriber Mirrored - LDAP Format
This rule finds matches in a connected system that uses LDAP format DNs for objects in the Identity Vault based on their names and locations. Implement the rule on the Subscriber Matching policy in the driver.
There are two steps involved in using the predefined rules: creating a policy in the Matching policy set, and importing the predefined rule. If you already have a Matching policy that you want to add this rule to, skip to Importing the Predefined Rule.
6.12.1 Creating a Policy
-
Open the for the driver you want to manage.
-
Click the Matching Policy object on the Subscriber channel.
-
Click .
-
Name the policy, make sure to implement the policy with the Policy Builder, then click .
The Rule Builder is launched.
-
Continue with Section 6.12.2, Importing the Predefined Rule.
6.12.2 Importing the Predefined Rule
-
In the Rule Builder, click .
-
Select .
-
To edit the rule, click in the Rule Builder.
-
Delete from the .
-
Browse to the container in the source hierarchy where you want the matching to start, then click .
-
Click .
-
Delete from the field.
-
Click on the icon to launch the Argument Builder.
-
Select in the Noun list, then click .
-
In the Editor, click the browse button, then browse to and select the container in the destination hierarchy where you want the source structure to be matched, then click .
-
Click .
6.12.3 How the Rule Works
When an Add event occurs on an object in the Identity Vault that is located within the specified source subtree, the rule constructs a DN that represents the same object name and location within the connected system relative to the specified destination subtree. If the destination objects exists and is of the desired object class, then it is considered a match. You must supply the DNs of the source (Identity Vault) and destination (connected system) subtrees. The connected system must use an LDAP-formatted DN.