12.1 NCP on Linux Security
The NetWare and Linux security models are quite different. The basic NetWare security model assumes that users have no rights until they are granted specific rights. Those rights are inherited by the users in all child subdirectories. This means that a single trustee assignment can give a user rights to a large number of subdirectories and files. A user’s home directory is set up so that only the user and the system administrator have rights there. A user’s files are secure.
The POSIX/Linux security model takes a different approach. The POSIX permissions are specified for each file and subdirectory, and nothing is inherited. If a user is to have access to all the files in a subdirectory, the permissions (UID, GID, and mode bits) must be set for each file in a manner that gives the user the appropriate access. This can’t be done with a simple trustee assignment to the parent subdirectory. In order for a user to use the dir or ls command, the user must have the read and execute rights in that directory and all its parent directories up to the root. Because of this, users usually have read rights by default across most of the system, and then the rights for everyone are masked for areas that need to be private. This means that the default for POSIX is open and shared rather than private. In POSIX, files are private when you make them private rather than private by default.
Figure 12-1 Comparison of the Linux ACL Model and the Novell Trustee Model
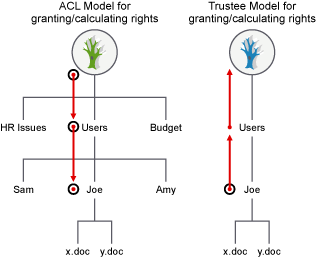
Novell Storage Services (NSS) volume on Linux and NCP volumes on Linux use the Novell trustee model to control user access to files. Users can see only those directory paths that they need to see in order to access their files. On a Linux POSIX file system using Access Control Lists, visibility of the entire directory structure is not restricted.
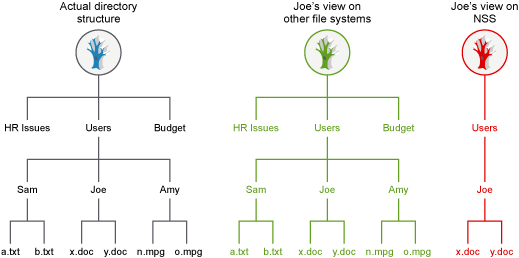
For example, Figure 12-2 shows how the user Joe has restricted visibility into the file system to view only those paths needed to access the files in his home directory on an NSS volume on Linux. On Linux POSIX file systems without NCP Server, Joe is able to view the entire directory structure.
Figure 12-2 Comparison of File Visibility for Users of Linux POSIX Volumes and NSS Volumes on Linux
If users want to share files with others, they can grant rights through trustee assignments on the individual files, or by creating a shared subdirectory and assigning trustees to it. When a user is given a trustee assignment to a file or directory, he or she can automatically see each parent directory along the path up to the root. However, the user cannot see the contents of those directories, just the path to where he or she has rights.
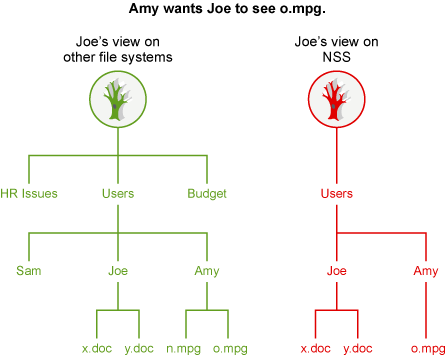
For example, if the user Amy wants user Joe to see a particular file in her home directory, she can add Joe as a trustee of the file, then grant Joe limited rights to see the file. Joe can see the path to the file, but cannot see other files in Amy’s home directory, as shown in Figure 12-3. On Linux file systems without NCP Server, Joe would be able to see all files in Amy’s home directory.
Figure 12-3 File Visibility Granted to Trustees
These differences in access control approaches can become problems when you try to share files between NCP users and Linux users that rely on the POSIX rights for their access (Local, SSH, and Samba users). In order for the Linux/POSIX users to access files, they need to be granted read and execute (r and x) rights through the group and other mode bits for subdirectories along the path up to the root of the volume. This gives them the right to see and read all files in those directories up to the root. This is unlike NCP rights on NetWare, where users see only the subdirectory path to the locations where they have been granted trustee rights. For shared volumes, NetWare users should be aware that Linux/POSIX users might have more rights to files and subdirectories than NCP users do.
Because the NetWare model is secure/private until granted specific rights, all files and subdirectories created by NCP clients have the following POSIX security permissions:
-
The UID is that of the user (or root if the user is not Linux-enabled with Linux User Management).
-
The GID is root.
-
The mode bits are:
rwx --- ---
This way, by default, the only people who can access a file or subdirectory from a LINUX environment are root and the creator of the file or subdirectory. An option is included with OES that lets a volume be configured such that the permissions (GID and mode bits) are inherited from the parent directory. This lets shared areas be more easily created and managed. This option is not enabled by default. The more secure model of the OES release is still the default. See Section 10.8, Configuring Inherit POSIX Permissions for an NCP Volume for information on how to enable or disable this option.
Because NSS is not a POSIX file system, NSS rights don’t behave like standard POSIX rights. NSS volumes keep track of trustee assignments; all trustee assignments are synchronized between NCP and NSS. For NSS volumes, access is based on trustee rights for the user (UID) rather than the permissions (UID, GID, and mode bits). This makes things simpler because Linux/POSIX-based users (Local, SSH, and Samba) do not have more rights than the same user would have if he were accessing files through NCP. This makes NSS easier to manage.