6.2 NIT (Novell Identity Translator)
The Novell Identity Translator (NIT) is a new service introduced in OES 2015 as explained in the following sections:
6.2.1 A New NSS Authorization Model
Beginning with OES 2015, a new authorization model has been included for CIFS-user access to NSS volumes.
The new model requires that eDirectory and Active Directory (AD) users all have unique User IDs (UIDs).
6.2.2 Not All Users Have UIDs by Default
-
eDirectory: LUM-enabled eDirectory users have UIDs; non-LUM-enabled eDirectory users do not.
-
Active Directory: Generally speaking, AD users don’t have UIDs, but AD can be configured to assign the uidNumber attribute to users when required.
6.2.3 Ensuring that Your CIFS-NSS Users Have UIDs
The Novell Identity Translator (NIT) lets you ensure that all users requiring NSS authorization have the required UIDs.
-
eDirectory: When NIT is properly configured, all eDirectory users can access NSS using CIFS, as summarized in Table 6-1.
Table 6-1 NIT Guarantees UIDs for All eDirectory Users
User UID Status in eDirectory
What NIT Does
LUM-enabled user
Retrieves the UID from eDirectory
Non-LUM-enabled user
Generates a UID within the specified UID range
-
Active Directory: If needed, you can configure NIT to simply retrieve and pass along UIDs that are set in Active Directory by deselecting the Generate UIDs for AD Users option when you Configure the NSS AD Support service. However, you must then ensure that all AD users who need access to NSS through CIFS have the uidNumber attribute set on their AD account. The caveats associated with the Generate UIDs for AD Users option are summarized in Table 6-2.
Table 6-2 NIT Can Guarantee UIDs for Active Directory Users
UIDs in Active Directory
Generate UIDs for AD Users Option Status
What NIT Does
The uidNumber attribute is set for some or all AD users.
Those users have a UID number in Active Directory.
Enabled
Generates UIDs within the specified UID range for all AD users needing NSS access.
The uidNumber attribute in Active Directory is ignored.
Disabled
Retrieves the uidNUmber from Active Directory when available.
Users without a uidNumber cannot access NSS.
The uidNumber attribute is not set for any AD users.
No AD users have a UID number in Active Directory
Enabled
Generates UIDs within the specified UID range for all AD users needing NSS access.
Disabled
No users can access NSS because none of them has a UID.
6.2.4 Which OES Components Rely on NIT
NIT is used as an infrastructure component by various OES services, including CIFS, NSS, and SMS.
6.2.5 What NIT Does
NIT does the following:
-
Dynamically generates UIDs for non-LUM-enabled eDirectory users so that they can access NSS resources on Linux.
-
As specified in the nitd.conf file, either retrieves or dynamically generates UIDs for Active Directory users so that they can access NSS resources on Linux.
-
Provides user and group IDs and other details such as SID, samAccountName, GUID for AD identities and FQDN, GUID details for eDirectory identities to services like NSS, CIFS, and SMS.
-
Is backward-compatible and co-exists with Linux User Management (LUM).
-
Maintains all of the users information in an AD forest where the OES server’s computer object is located.
-
Ensures uniqueness of User IDs for all the users across eDirectory and Active Directory users and groups accessing an OES server.
NOTE:The UIDs distributed by NIT are server-specific. They are not stored in eDirectory or Active Directory, and they are not visible to Linux services.
6.2.6 Prerequisites
The following are required for NIT to service Active Directory users and groups:
DNS
-
Domain Controller and Global Catalog Server Discovery: DNS entries for all the Domain Controllers and Global Catalog Servers must exist in order for NIT to detect which of them are closest and then retrieve the required AD user information. Ensure to provide the complete DNS name of the OES CIFS server.
-
SRV Records: The DNS should contain the SRV entries for the Domain Controllers, Global Catalog servers and KDC servers in the OES joined forest and other trusted forests.
Kerberos
For external forest trusts, “Kerberos Forest Search Order (KFSO)” should be enabled for Windows clients to connect an OES CIFS server. For more information, see Configuring AD Server to Support Kerberos Authentication for External Forest Users Using CIFS Client in the OES 2018 SP2: OES CIFS for Linux Administration Guide.
OES communicates with Active Directory Domain Controllers over 389 port and Global Catalog servers over 3268 port by using Kerberos. So, 389 and 636 ports should be opened for Kerberos communication.
6.2.7 NIT Components
NIT contains the following components:
-
nit daemon: Serves requests from CIFS, NSS, SMS, and other OES services to map and resolve eDirectory and Active Directory user identities as applicable.
-
nitconfig utility: Lets administrators configure NIT in a terminal prompt by adding and modifying configuration parameters. The nitconfig utility changes the /etc/opt/novell/nit/nitd.conf file based on the parameters entered.
-
NIT configuration file: /etc/opt/novell/nit/nitd.conf.
Each entry occupies a single line in the file. Lines that are blank, or that start with a pound sign (#), are ignored.
IMPORTANT:If you change the NIT UID range, either manually or using the nitconfig utility, you must restart the server.
6.2.8 NIT Log Files
NIT actions are logged in the following locations:
-
NIT log: /var/opt/novell/logs/nit/nit.log
-
nitconfig log file: /var/opt/novell/log/nit/nitconfig.log
6.2.9 Interactions With eDirectory and Active Directory
NIT interacts with LUM, NCP, the AD Global Catalog Server, and Domain Controllers to retrieve and map user information.
6.2.10 How NIT Works
Figure 6-1 NIT - overview
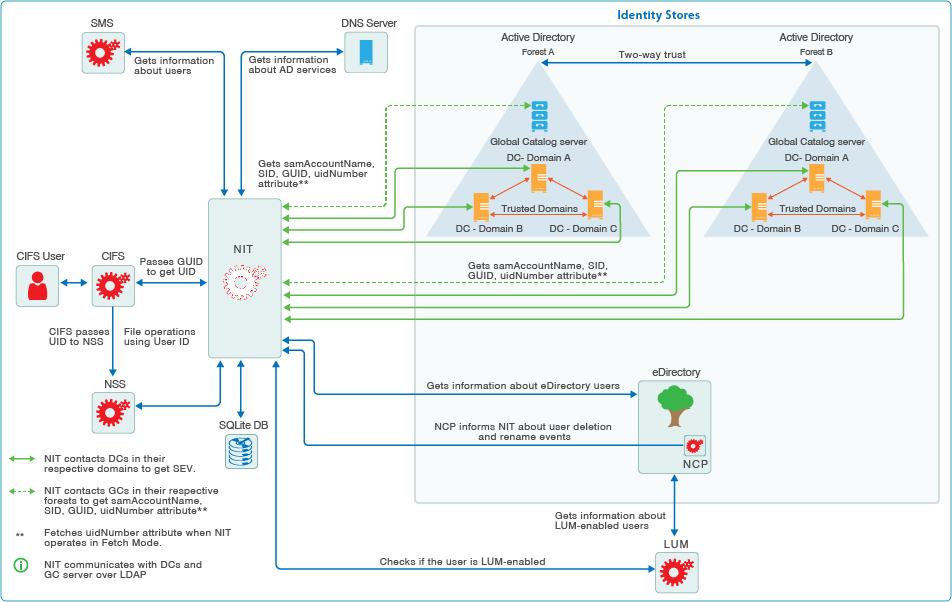
NIT supports two identity stores:
-
Active Directory
and
-
eDirectory
NIT can run in two modes:
-
Support only eDirectory
-
Support eDirectory and Active Directory
You can configure this through nitconfig by changing the value of ad-mode parameter. If you set the value to yes, then NIT supports eDirectory and Active Directory. If you set it to no, then NIT supports only eDirectory.
6.2.11 Active Directory users:
For Active Directory users, NIT can be configured to run in one of two modes:
-
Generate Mode: NIT generates and uses its own UID numbers. Even if the Active Directory users have the UID numbers populated, those are not used by NIT.
or
-
Fetch Mode: NIT only retrieves UID numbers that are available in Active Directory. If a UID is not set for a particular user, that user cannot access NSS resources.
If you are configuring NIT in fetch mode for Active Directory users, ensure that the Active Directory users who require access to NSS file systems have UID numbers set in Active Directory.
You must add the uidNumber attribute explicitly to the Global Catalog server because it is not part of the default attributes.
For more information about replicating UID numbers to the Global Catalog server, refer to the Microsoft Support website.
By default, NIT runs in generate mode where UID numbers are dynamically generated for Active Directory users within the range that you specify in the NIT configuration.
6.2.12 eDirectory users:
For eDirectory LUM-enabled users, NIT obtains the UID number that is already available in eDirectory. NIT automatically creates UIDs for non-LUM-enabled users from the UID range that you specify either directly in nitd.conf or through the nitconfig utility.
6.2.13 Task FAQ
How do I set UID ranges?
You can set the UID ranges through YaST as part of the OES installation.
You can also set and manage UID ranges using the nitconfig utility after the NIT service is configured as part of OES installation.
How do I estimate UID ranges?
Estimate the number of users who might access the server, and then set a UID range that is double that number. Ensure that these ranges do not overlap with the LUM ranges and Linux UID ranges, if present.
How long are UIDs valid?
The UIDs are valid until the OES system is rebooted. However, the UIDs are retained when the NIT service restarts.
Are the UIDs unique?
UIDs generated are unique within each server’s environment, including the Identity stores (eDirectory and Active Directory) and the local file systems (both Linux and POSIX).
What happens if a cluster resource is moved?
When a cluster resource is mounted on a different cluster node, UIDs are automatically generated for new user connections on the new node. UID management and generation is specific to each cluster node (OES 2018 server). There is no NIT configuration or activity at the cluster level.
How do I manage NIT?
To start, stop, and restart the NIT service, use these command options:
rcnovell-nit status | stop | start | restart
To configure and change NIT settings, use the nitconfig utility.
IMPORTANT:If you change the NIT UID range, you must restart the server.
What is cache and SQLite DB?
NIT stores eDirectory and Active Directory user information, GUID to UID mapping information and SID to GUID mapping information in non-persistent in-memory cache.
NIT stores GUID to UID (UIDs generated by NIT for non LUM-enabled eDirectory and Active Directory users) mapping information in /var/opt/novell/nit/db/.g_i_info SQLite DB file, and SID to GUID mapping information in /var/opt/novell/nit/db/.s_g_info SQLite DB file. The information stored in SQLite DB files are persistent across NIT restarts.
On a server reboot, the in-memory cache information is cleared and the .g_i_info SQLite DB file is deleted.
When the NIT daemon is restarted, the in-memory cache is cleared and NIT rebuilds GUID to UID mapping information and SID to GUID mapping information into cache by reading from the SQLite DB files.
In addition, only the user information in the in-memory cache is cleared once in 8 hours and the GUID to UID and SID to GUID mapping information remain unaltered.
6.2.14 Administrative Access Restrictions
When an OES server is joined to an Active Directory domain, by default, members of the Domain Admins group will have Supervisor rights over all the volumes that are enabled with Active Directory identities flag.
You can override this default functionality by configuring a group of your choice. Because the group has full control over the Active Directory enabled volumes, add users with caution.
If NIT could not identify the configured group from Active Directory, it falls back to the default behavior.
Whenever you change the Active Directory supervisor group, do the following:
-
Restart the NIT daemon by running the rcnovell-nit restart command at the terminal console.
-
Restart the CIFS service by running the rcnovell-cifs restart command at the terminal console.
-
Force the SEV update to occur immediately for all users in the NSS file system by running the nss /ForceSecurityEquivalenceUpdate command at the nsscon prompt.
6.2.15 Performance and Tuning
-
ad-gc-handles: NIT interacts with the Global Catalog servers to fetch Active Directory user and group information. By default, NIT establishes 10 connections with the GC server. Based on the number of users, increase this number to improve the file access response time.
-
hash-size: NIT caches eDirectory and Active Directory user information in hash tables. By default, the size is configured to 211. This can be increased to a maximum of 1:10. For example, for 20,000 users the hash size will be a prime number close to 2048.
NIT stores the user cache information in the following SQLite DB files: /var/opt/novell/nit/db/.g_i_info and /var/opt/novell/nit/db/.s_g_info.
-
UID Start and End Range: Changing the UID start and end ranges requires a system reboot.