3.1 Configuring Trusted Root Certificates
Configuration Level: Global
The list of trusted root containers is used for certificate validation. During certificate validation, the method builds the certificate chain. In order to be valid, the certificate chain must end with a trusted root certificate. Trusted root certificates are stored in trusted root containers in eDirectory.
The certificate validation process ensures that the login certificate has been issued by a trusted Certificate Authority (CA). This is accomplished by validating that the certificate chain contains only trusted root certificates.
-
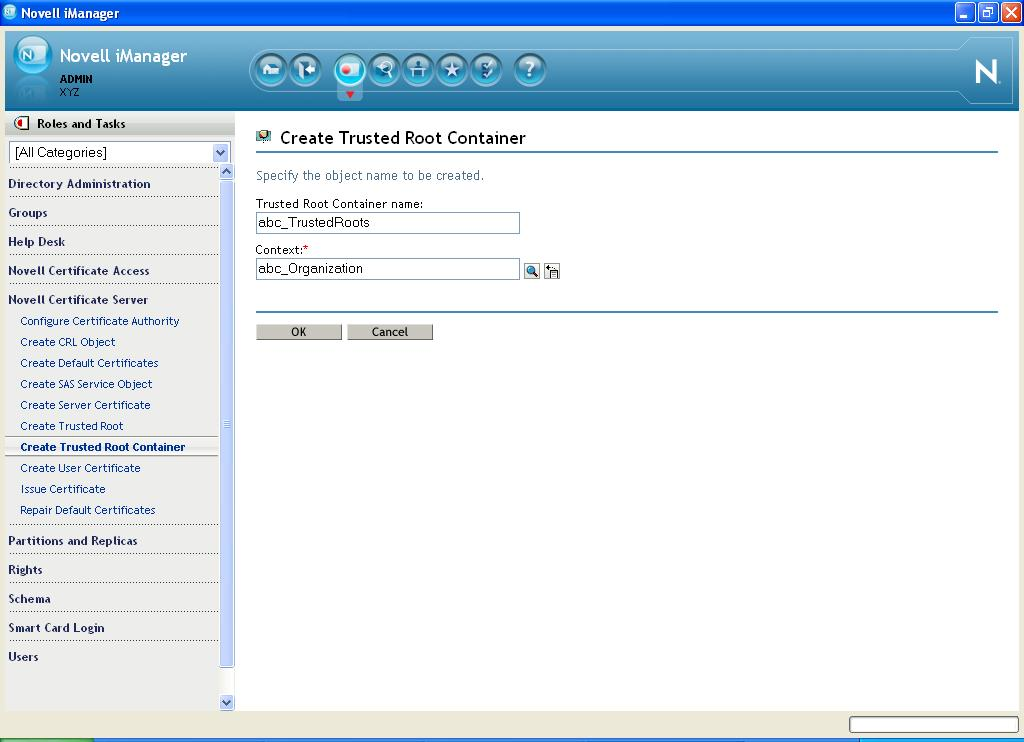
In iManager, create a trusted root container:
-
Select .
-
Specify the container name and location.
-
Click .
-
-
Import trusted root certificates:
-
Select .

-
Fill in the following fields:
-
Name: Specify a name. This name is the Trusted Root object that is created in the directory to hold the certificate material. Choose a name that allows you to recognize which CA this issuing certificate came from.
IMPORTANT:This name cannot contain any dot characters. If it does, you encounter an NDS-601 error.
-
Container: Browse to and select the trusted root container created in Step 1.
-
Certificate: Browse to and select a standard DER file (*.der or *.cer) or Base 64 encoded DER file (*.b64, *.pem, or *.cer). This file contains the material for the issuing certificate.
If you do not already have this file, consult your CA for information and instructions on how to obtain it.
-
-
Click .
-
-
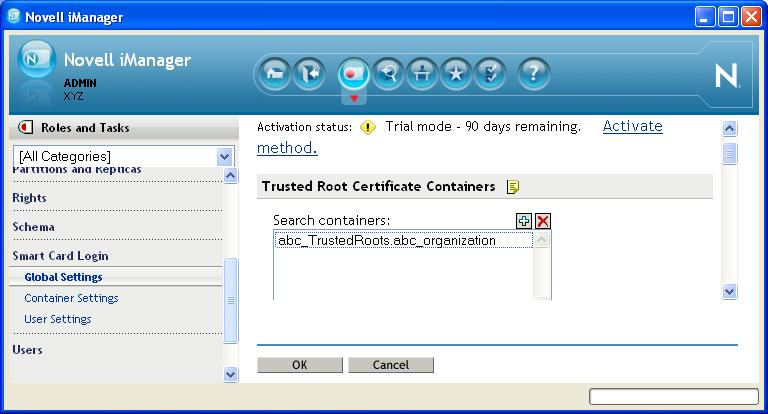
Add the trusted root container to the method's global settings:
-
Select .
-
Click the plus sign to add the trusted root container to the list.
-
Click .
-