4.2 Sample Configurations
4.2.1 The Access Gateway and Identity Server in the DMZ
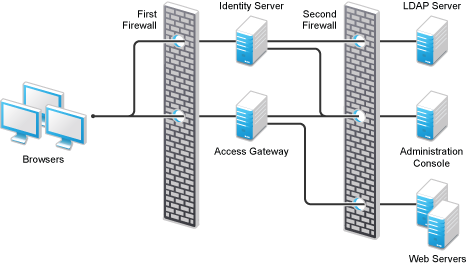
Figure 4-2 The Identity Server and the Access Gateway in the DMZ
First Firewall
If you place a firewall between the browsers and the Access Gateway and Identity Server, you need to open ports so that the browsers can communicate with the Access Gateway and the Identity Server and the Identity Server can communicate with other Identity Providers.
Table 4-8 Ports to Open in the First Firewall
|
Port |
Purpose |
|---|---|
|
TCP 80 |
For HTTP communication. |
|
TCP 443 |
For HTTPS communication. |
|
Any TCP port assigned to a reverse proxy or tunnel. |
|
|
TCP 8080 |
For HTTP communication with the Identity Server. For information about redirecting the Identity Server to use port 80, see |
|
TCP 8443 |
For HTTPS communication with the Identity Server. For information about redirecting the Identity Server to use port 443, see |
|
TCP 8445 |
For HTTP Identity Provider introductions. If you do not enable Identity Provider introductions, you do not need to open this port. For more information about this option, see the option in |
|
TCP 8446 |
For HTTPS Identity Provider introductions. If you do not enable Identity Provider introductions, you do not need to open this port. For more information about this option, see the option in |
Second Firewall
The second firewall separates the Web servers, LDAP servers, and the Administration Console from the Identity Server and the Access Gateway. You need the following ports opened in the second firewall:
Table 4-9 Ports to Open in the Second Firewall
|
Port |
Purpose |
|---|---|
|
TCP 80 |
For HTTP communication with Web servers. |
|
TCP 443 |
For HTTPS communication with Web servers. |
|
Any TCP connect port assigned to a Web server or to a tunnel. |
|
|
TCP 1443 |
For communication from the Administration Console to the devices. |
|
TCP 8444 |
For communication from the devices to the Administration Console. |
|
TCP 289 |
For communication from the devices to the Novell Audit server installed on the Administration Console. If you do not enable auditing, you do not need to open this port. |
|
TCP 524 |
For NCP certificate management in NPKI. The port needs to be opened so that both the device and the Administration Console can use the port. |
|
TCP 636 |
For secure LDAP communication of configuration information. |
4.2.2 A Firewall Separating Access Manager Components from the LDAP Servers
You can configure your Access Manager components so that your Administration Console is on the same side of the firewall as your Access Manager components and have a firewall between them and the LDAP servers, as illustrated in Figure 4-3.
Figure 4-3 A Firewall Separating the Administration Console and the LDAP Server

In this configuration, you need to have the following ports opened in the second firewall for the Administration Console and the Identity Server.
Table 4-10 Ports to Open in the Second Firewall
|
Ports |
Purpose |
|---|---|
|
TCP 636 |
For secure LDAP communication. This is used by the Identity Server and the Administration Console. |
|
TCP 524 |
For configuring eDirectory as a new User Store. NCP is used to enable SecretStore by adding a SAML authentication method and storing a public key for the Administration Console. During day-to-day operations, this port is not used. If your LDAP server is Active Directory or Sun ONE, this port does not need to be opened. |
4.2.3 Configuring the Firewall for the SSL VPN Server
The SSL VPN server can be installed as a separate machine or as a component running on the Linux Access Gateway. Although it is configured to be a protected resource of the Access Gateway, it also allows direct communication with the client browsers.
Figure 4-4 SSL VPN Server and Firewalls

The SSL VPN server needs the following port opened on the first firewall if clients are accessing the SSL VPN server directly:
Table 4-11 Ports to Open in the First Firewall for SSL VPN
|
Port |
Purpose |
|---|---|
|
TCP 7777 |
For client communication. This is the default port, but it can be configured to use TCP 443. |
You need to open ports on the second firewall according to the offered services.
Table 4-12 Ports to Open in the Second Firewall for SSL VPN
|
Port |
Purpose |
|---|---|
|
TCP 22 |
For SSH. |
|
TCP 23 |
For Telnet. |
|
Ports specific to an application. |
|
4.2.4 Configuring the Firewall for the J2EE Agent
The J2EE Agent is installed on a J2EE server running JBoss, WebLogic, or WebSphere. You can configure it to be a protected resource of the Access Gateway or you can allow direct access. Figure 4-5 illustrates these configurations.
Figure 4-5 J2EE Agent and Firewalls

If the J2EE server is installed behind the first firewall and browsers are allowed direct access to it, the following ports need to be opened in the first firewall:
Table 4-13 Ports to Open in the First Firewall for the J2EE Agent
|
Port |
Purpose |
|---|---|
|
TCP 8080 |
For non-secure connections to a JBoss server. |
|
TCP 8443 |
For secure connections to a JBoss server. |
|
TCP 9080 |
For non-secure connections to a WebSphere server. |
|
TCP 9443 |
For secure connections to a WebSphere server. |
|
TCP 7001 |
For non-secure connections to a WebLogic server. |
|
TCP 7002 |
For secure connections to a WebLogic server. |
If the J2EE server is installed behind the second firewall, the following ports need to be opened in the second firewall:
Table 4-14 Ports to Open in the Second Firewall for the J2EE Agent
|
Port |
Purpose |
|---|---|
|
TCP 8080 |
For non-secure connections to a JBoss server. |
|
TCP 8443 |
For secure connections to a JBoss server. |
|
TCP 9080 |
For non-secure connections to a WebSphere server. |
|
TCP 9443 |
For secure connections to a WebSphere server. |
|
TCP 7001 |
For non-secure connections to a WebLogic server. |
|
TCP 7002 |
For secure connections to a WebLogic server. |
|
TCP 8080 or 8443 |
For authentication communication. The port of the Base URL of the Identity Server needs to be open. |