83.2 Server Certificates and SSL Encryption
You should strengthen native GroupWise encryption with Secure Sockets Layer (SSL) communication between servers where GroupWise agents are installed. You can choose to purchase a server certificate from a commercial certificate authority (CA) or you can generate a self-signed certificate.
The advantage of using a self-signed certificate is that you can proceed to set up SSL immediately, without waiting to the certificate from a certificate authority. However, the first time the GroupWise client encounters the self-signed certificate, it prompts the user to accept the certificate. The advantage of a commercially generated certificate is that the GroupWise client accepts it automatically. You might choose to use a self-signed certificate initially, while you are waiting to obtain a commercially generated certificate.
If you have not already set up SSL on your system, complete the following tasks:
If you have already set up SSL on your system and are using it with other applications in addition to GroupWise, skip to Section 83.2.4, Configuring the Agents to Use SSL.
83.2.1 Purchasing a Commercially Generated Certificate
In order to purchase a commercially generated certificate, you must create a certificate signing request (CSR).
Generating a Certificate Signing Request
The certificate signing request (CSR) includes the hostname of the server where the agents run. Therefore, you must create a CSR for every server where you want the GroupWise agents to use SSL. However, all GroupWise agents running on the same server can all use the same certificate, so you do not need separate CSRs for different agents. The CSR also includes your choice of name and password for the private key file that must be used with each certificate. This information is needed when configuring the agents to use SSL.
Using the GroupWise Generate CSR Utility (GWCSRGEN)
One way to create a CSR is to use the GroupWise Generate CSR utility (GWCSRGEN). This utility takes the information you provide and creates a .csr file from which a public certificate file can be generated.
IMPORTANT:Starting in GroupWise 2012 SP1, GWCSRGEN is no longer a recommended method for creating CSRs. You can still use it for convenience, but for optimum security, use a standard CSR generation method native to your operating system.
-
Start the GroupWise Generate CSR utility.
Linux:
The utility (gwcsrgen) is installed to the /opt/novell/groupwise/agents/bin directory. You must be logged in as root to start the utility.
Windows:
The utility (gwcsrgen.exe) is located in the \admin\utility\gwcsrgen directory either in downloaded GroupWise 2012 software image or in the GroupWise software distribution directory.

-
Fill in the fields in the box. The private key information is used to create both the Private Key file and the certificate signing request file.
Key Filename: Specify a name for the Private Key file (for example, server1.key). If you do not want the file stored in the same directory as the GWCSRGEN utility, specify a full path with the file name (for example, c:\certs\server1.key or /opt/novell/groupwise/certs/server1.key). The directory where you want to create the .key file must already exist.
Linux:
Use only lowercase characters.
Windows:
No limitations
Key Length: The key length can be 1024, 2048, or 4096. The default is 1024.
Key Password: Specify the password for the private key. The password can be up to 256 characters (single-byte environments).
Verify Password: Specify the password again.
-
Fill in the fields in the box.
CSR Filename: Specify a name for the certificate signing request file (for example, server1.csr). If you don’t want the file created in the same directory as the GWCSRGEN utility, specify a full path with the file name (for example, c:\certs\server1.csr or /opt/novell/groupwise/certs/server1.csr). The directory where you want to create the .csr file must already exist.
Linux:
Use only lowercase characters.
Windows:
No limitations
-
Fill in the fields in the box. This information is used to create the certificate signing request file. You must fill in all fields to generate a valid CSR file.
Country: Specify the two-letter abbreviation for your country (for example, US).
State/Province: Specify the name of your state or province (for example, Utah). Use the full name. Do not abbreviate it.
City: Specify the name of your city (for example, Provo).
Organization: Specify the name of your organization (for example, Novell, Inc.).
Division: Specify your organization’s division that this certificate is being issued to (for example, Novell Product Development).
Hostname of Server: Specify the DNS hostname of the server where the server certificate will be used (for example, dev.provo.novell.com).
-
Click to generate the CSR file and Private Key file.
The CSR and Private Key files are created with the names and in the locations you specified in the and fields.
-
Skip to Submitting the Certificate Signing Request to a Certificate Authority.
For convenience, if you need to generate multiple certificates, you can record the information for the fields listed in Using the GroupWise Generate CSR Utility (GWCSRGEN) in a configuration file so that the information is automatically provided whenever you run the GroupWise Generate CSR utility. The configuration file must have the following format:
[Private Key] Location = Extension = key [CSR] Location = Extension = csr [Required Information] Country = State = City = Organization = Division = Hostname =
If you do not want to provide a default for a certain field, insert a comment character (#) at the beginning of that line. Name the file gwcsrgen.cnf. Save the file in the same directory where the utility is installed:
|
Linux: |
/opt/novell/groupwise/agents/bin |
|
Windows: |
\grpwise\software\admin\utility\gwcsrgen |
Linux: Using OpenSSL
For background information, see HOWTO Certificates.
-
Open a terminal window, become root, and change to a convenient directory where you want to create the CSR.
-
Enter the following command to create a private key file:
openssl genrsa -out -key key_file_name.key 2048Replace key_file_name.key with a convenient name for the private key file, such as gw.key.
-
Create the CSR:
-
Enter the following command:
openssl req -new -key key_file_name.key -out csr_file_name.csr
Replace key_file_name.key with the key file that you created in Step 2.
-
Enter the two-letter code for your country, such as US for the United States, DE for Germany, and so on.
-
Enter your state or province.
-
Enter your city.
-
Enter the name of your company or organization.
-
Enter your department or other organizational unit.
-
Enter the fully qualified domain name of the server for which you are obtaining a certificate, such as gw3.novell.com.
-
Enter the email address of a contact person for that server.
-
(Optional) Enter a password for the CSR.
-
(Optional) Enter a secondary name for your company or organization.
-
-
Skip to Submitting the Certificate Signing Request to a Certificate Authority.
Windows Server 2008: Using IIS Manager
-
Open IIS Manager.
-
In the pane, click the server to display the server Home view.
-
In the , double-click .
-
In the pane, click .
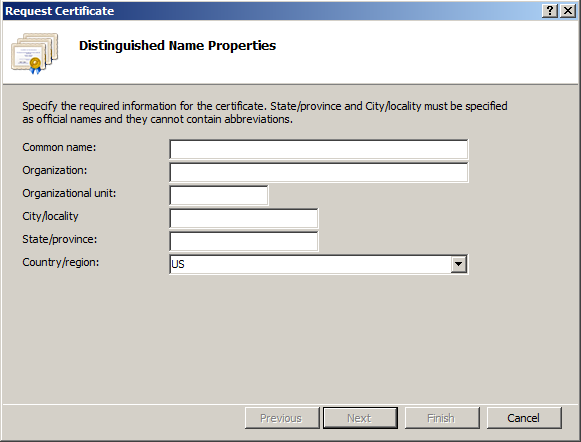
-
In the field, specify the fully qualified domain name of the server for which you are obtaining a certificate, such as gw3.novell.com.
-
Fill in the rest of the fields with the requested information, then click .
-
The default cryptographic service provider and bit length are acceptable, so click .
-
Specify a name for the CSR file, such as gw.csr, then click .
If you do not specify a full path name, the CSR file is created in the c:\Windows\System32 directory.
-
Skip to Submitting the Certificate Signing Request to a Certificate Authority.
Windows Server 2003: Using Internet Information Services
-
In the Control Panel, click .
-
Right-click a Web site, then click .
-
On the tab, click , then click .
-
Select , then click .
-
Select , then click .
-
Specify an identifying name for the certificate, then click .
-
Specify your company name and department name, then click .
-
Specify the fully qualified domain name of the server for which you are obtaining a certificate, such as gw3.novell.com, then click .
-
Specify the location of your company, then click .
-
Specify a name for the CSR file, such as gw.csr, then click .
If you do not specify a full path name, the CSR file is created in the c:\Windows\System32 directory.
-
Review the information that you have provided, then click to create the CSR file.
-
Continue with Submitting the Certificate Signing Request to a Certificate Authority.
Submitting the Certificate Signing Request to a Certificate Authority
To obtain a server certificate, you can submit the certificate signing request (server_name.csr file) to a certificate authority. If you have not previously used a certificate authority, you can use the keywords “certificate authority” to search the Web for certificate authority companies.
The process of submitting the CSR varies from company to company. Most provide online submission of the request. Follow their instructions for submitting the request. The certificate authority must be able to provide the certificate in Base64/PEM or PFX format.
83.2.2 Generating a Self-Signed Certificate
There are several ways to generate a self-signed certificate:
Using ConsoleOne on Windows or Linux
The NetIQ Certificate Server, which runs on a Linux server with NetIQ eDirectory, enables you to establish your own certificate authority and issue server certificates for yourself. For complete information, see the NetIQ Certificate Server Web site.
To quickly create your own public certificate in ConsoleOne:
-
Click to see if the Certificate Server snap-in to ConsoleOne is installed.
If you need to install the snap-in on Linux, it is available in the version of ConsoleOne provided in the consoleone subdirectory in the downloaded GroupWise 2012 software image. It is called the PKI Snapin.
If you need to install the snap-in on Windows, you can download the snap-ins for Windows ConsoleOne from the Novell Downloads site.
NOTE:You can create a server certificate in Novell iManager, as well as in ConsoleOne, using steps similar to those provided below.
-
Browse to and select the container where your Server object is located.
-
Click , then in the field, browse to and select the CSR file created by GroupWise Generate CSR utility (GWCSRGEN) in Generating a Certificate Signing Request.
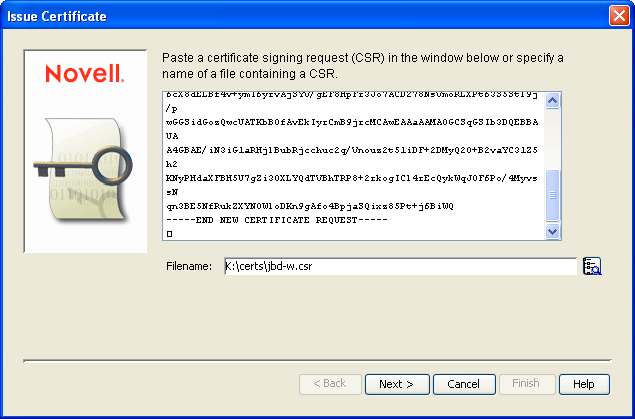
-
Click .
By default, your own organizational certificate authority signs the request.
-
Click .
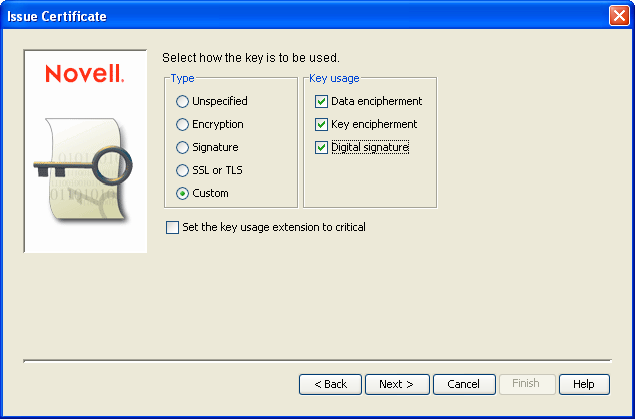
-
In the box, select .
-
In the box, select all three usage options.
-
Click .
-
In the field, select the length of time you want the certificate to be valid.
You might want to change the setting to a longer period of time to best meet the needs of your organization.
-
Click , view the summary information, then click .
-
Select .
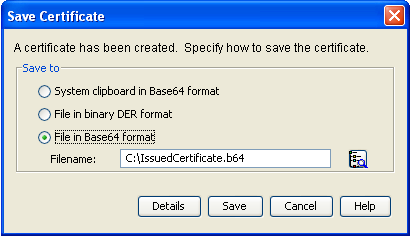
-
Specify the path and file name for the certificate.
Linux:
Use only lowercase characters.
Windows:
No limitations
You can retain the .b64 extension or use the more general .crt extension.
-
Click .
Using YaST on Linux
-
On the Linux server desktop, click , then enter the root password.
-
Click .
-
If you did not create the YaST_Default_CA during the installation of Linux on the server:
-
Click , specify the name and location of an existing CA, click , then skip to Step 4.
or
Click , then continue with Step 3.b.
-
Fill in the following fields:
CA Name: Specify the name of the CA certificate.
Common Name: Specify the name of the certificate authority.
Organization: Specify the name of your organization (for example, Novell, Inc.).
Organizational Unit: Specify your organization’s division that this certificate is being issued to (for example, Novell Product Development).
Locality: Specify the name of your city or other regional division (for example, Provo).
State: Specify the name of your state (for example, Utah). Use the full name. Do not abbreviate it.
Country: Select the name of your country (for example, USA).
-
Click .
-
Specify and verify the certificate password, then click .
-
Click to create the root certificate authority on the server.
-
-
After you have a certificate authority on the Linux server:
-
Select or the CA you just created, click , specify the CA password, then click .
-
On the tab, .
-
Select .
-
Specify the certificate password and, if desired, specify and verify a new password for the new certificate file.
-
Browse to and select the directory where you want to create the certificate file, then specify the file name for the certificate, adding a .pem extension.
-
Click to create the certificate file, then click again to confirm.
-
Exit from YaST.
-
-
In a terminal window, log in as root, then separate the .pem file created by YaST into a .crt file and a .key file, as required by GroupWise:
-
Use a text editor such as gedit to open the .pem file.
-
Select and copy the BEGIN CERTIFICATE line through the END CERTIFICATE line into a new file, name it the same as the server name, and add a .crt extension to the file name when you save it.
-
Select and copy the BEGIN RSA PRIVATE KEY line through the END RSA PRIVATE KEY line into a new file, name it the same as the server name, and add a .key extension to the file name when you save it.
-
Exit the text editor.
-
Using the openssl Command on Linux
A convenient way to create a certificate from the Linux command line is to use the openssl command, as described in HOWTO Keys.
83.2.3 Installing the Certificate on the Server
After processing your CSRs, the certificate authority sends you a public certificate (server_name.b64) file for each CSR. You might need to extract the private key from the public certificate. The private key file might have an extension such as .pem or .pfx. The extension is unimportant as long as the file format is correct.
If you used the Issue Certificate feature in ConsoleOne, as described in Section 83.2.2, Generating a Self-Signed Certificate, it generated the public certificate file (server_name.b64) and private key file (server_name.key).
Copy the files to any convenient location on each server. The location must be accessible to the GroupWise agents that run on the server.
83.2.4 Configuring the Agents to Use SSL
To configure the agents to use SSL you must first enable them for SSL and then provide certificate and key file information. For detailed instructions, see the following sections: