

  |
The Configure panel lets you set up client acceleration (forward and transparent proxy) and Web acceleration (reverse proxy) for HTTP and FTP requests. It also lets you configure authentication profiles and ACL rule access, fine-tune caching services, and specify how error pages are vended to browsers.
Path: Cache > Client Accelerator or Transparent Handling or Web Server Accelerator > Enable Authentication > Authentication Options
Figure 73
Add Authentication Profiles Dialog Box
The Add Authentication Profiles dialog box lets you select one authentication profile to authenticate the users of the proxy service from which you accessed this dialog box.
The Existing Profiles list shows all the authentication profiles you have created. See Authentication Dialog Box. The Service Profiles list contains the profile that is active for the proxy service from which you accessed the Add Authentication Profiles dialog box.
Maximum Idle Time Before Requiring a New Login: The period of browser inactivity allowed before the proxy server requests a new login.
Forward Authentication Information to Web Server: If this option is checked, the username and password are sent to the Web server.
Prompt for Username/Password over HTTP: If this option is checked, authentication will be done over unencrypted HTTP instead of HTTPS.
Cookie Domain: In Configure > Web Server > Modify > Authentication Options, there is a Cookie Domain field. Single authentication across two accelerators within the same iChain Proxy Server is not possible when the Cookie Domain is different on each accelerator. The Cookie Domain field can be used to allow single authentication across multiple acclerators where the cookie domain by default would be different for each accelerator. For example, if Accelerator One has a DNS name of www.support.novell.com and Accelerator Two has a DNS name of www.developernet.novell.com, the cookie domains would be support.novell.com for Accelerator One and developernet.support for Accelerator Two. The cookie domains are different for each accelerator, so users would be prompted for authentication when accessing Accelerator Two, even if they had already authenticated to Accelerator One. If the cookie domain is changed to novell.com on each accelerator, then users would not need to authenticate again when accessing Accelerator Two if they had already authenticated through Accelerator One. This would not be possible if one of the DNS names would have ended with acme.com and the other DNS name ended with novell.com. Both accelerators need to have a common subdomain for this to work.
Existing Profiles: A list of the authentication profiles you create in Cache > Authentication. For more information, see Authentication Tab.
Service Profiles: The authentication profile that is active for the proxy service from which you accessed the Add Authentication Profiles dialog box. List content depends on whether And Profiles or Or Profiles is selected. You add a profile to the list by clicking a profile in the Existing Profiles list, then clicking Add. You can remove the profile from this list using the Delete button.
AND Profiles: If this button is selected, the profiles in the Service profiles list are used in conjunction with each other to authenticate to users accessing the Web servers specified by this accelerator.
OR Profiles: If this button is selected, either one of the profiles in the Service profiles list are used to authenticate the users accessing the Web servers specified by this accelerator.
Path: Configure > Web Server Accelerator
Figure 74
Web Server Accelerator Tab
The Web Server Accelerator tab lets you add one or more Web server (reverse proxy) accelerators. The proxy server acts as the front end to Web servers on your Internet or intranet and off-loads frequent requests, thereby freeing up bandwidth. Using a Web server accelerator also increases security because the IP addresses of your Web servers are hidden from the Internet. For more information, see Overview of Web Server Acceleration.
Field names shown in the Web Server Accelerators list are explained in Web Server Accelerator Dialog Box.
Load Balance at Session Level Only: Checking this box causes the proxy server to use the same Web server for all fills during a session. This prevents eBusiness users from needing to log in multiple times. This setting affects all Web server accelerators configured on the proxy server.
Path: Configure > Web Server Accelerator > Insert
Figure 75
Web Server Accelerator Dialog Box
The Web Server Accelerator dialog box lets you create Web server accelerator services for handling requests to Web servers.
Enable This Accelerator: Specifies whether to enable the defined Web server accelerator after you have configured it. The default is Enabled.
Name: Each Web server accelerator service requires a name you create. For example, you can select a name that indicates which Web server is being serviced by the appliance, or alternately, a set of browsers configured to access the Web server accelerator as a proxy server. A valid name consists of a DOS-style, eight-character name with no special characters or spaces.
If logging is enabled, the appliance uses the Web server accelerator name as the directory name that the log files for the Web server accelerator are kept in.
DNS Name: The contents of this field depend on the type of accelerator you are using.
If you are accelerating multiple Web servers for multiple Web sites on the same IP address, you must create a Web server accelerator definition for each DNS name that is used in browser requests. This name must exactly match one of the names in the requests. If your infrastructure supports multi-homing, refer to Appliance Groups and Multi-homed Configurations, Standard Multi-homing for Multiple Web Sites, Multi-homing and Path-Based Support, and Path-Based Multi-homing Examples for further information.
If you are accelerating multiple Web servers for a single Web site and plan to use path-based multi-homing, you must use the same DNS name in every accelerator definition.
NOTE: If you are changing the DNS name on an accelerator which has authentication enabled, the existing cookie domain may not be valid with the new DNS name if the DNS name is not a subdomain of the cookie domain (resulting in the browser displaying a 403 Forbidden Error message). You can check the cookie domain at Authentication Options > Cookie Domain.
Use Host Name Sent by Browser (Multi-homing Web Server): Checking this option preserves the host name in the HTTP header exactly as it came in the browser request.
Alternate Host Name: Checking this option causes the string specified to be substituted for the host name in the HTTP header before the request is forwarded to the Web server.
Return Error If Host Name Sent by Browser Does Not Match Accelerator DNS Host Name: Checking this option causes iChain Proxy Services to match the host name in the DNS header that came from the browser against the DNS name specified in this accelerator definition. If the names don't match, the request is not forwarded to the Web server. Instead, iChain Proxy Services returns an error to the requesting browser.
Act as a Tunnel: Normally an accelerator service processes HTTP requests in order to fill them. However, it is not unusual that some of the traffic coming through the appliance is not HTTP-based.
Web servers often handle SSL connections, and less frequently they might need to let Telnet, FTP, chat, or other kinds of traffic through without attempting to process it.
The Act as a Tunnel option lets you create one or more accelerator services for the specific purpose of tunneling non-HTTP traffic through the appliance to the origin Web server. When the option is checked, the accelerator sets up a tunnel for all incoming traffic. Since tunnels are already limited because they can only connect to the fill Web server on the specified fill port, they are much more secure than connections to forward or transparent services that use the CONNECT method. For more information on CONNECT security concerns, see Using HTTP CONNECT.
When you check the Act as a Tunnel option, you have the additional option of having the accelerator service tunnel only SSL traffic.
Tunnel Only SSL Traffic: If you decide to have the accelerator act as a tunnel, you can elect to have it tunnel only SSL traffic. The service will then verify that the address and port being accessed are actually an SSL Web site. If verification fails, the service will tear down the connection.
NOTE: The SSL port number for the SSL tunnel is specified via the Accelerator proxy port and not the SSL listening port.
Forward Browser IP Address in Request Header [Enable X-Forwarded-For]: X-Forwarded-For headers are used to pass browser ID information along with browser request packets. If the headers are included, Web servers can determine the origin of browser requests they receive. If the headers are not included, browser requests have anonymity.
Checking the X-Forwarded-For option causes the appliance to either add information to an existing X-Forwarded-For or Forwarded-For header, or to create a header if one doesn't already exist.
Leaving the option unchecked causes the appliance to remove X-Forwarded-For headers from any Web accelerator requests passing through the appliance.
Deciding whether to check the option requires that you weigh the desires of browser users to remain anonymous against the desires of Web server owners (e-commerce sites, for example) to collect data about who is accessing their site.
Enable Authentication: Checking this box causes the appliance to require authentication of users wanting to use its Web server accelerator services. Clicking Authentication Options displays the Add Authentication Profiles dialog box.
Enable Logging for This Accelerator: Causes log files to be kept for this Web server accelerator. Clicking Log Options displays the Log Options dialog box.
Enable Secure Exchange: Selecting this option allows SSL to be used for HTTP requests between the client and the iChain box, and optionally between the iChain box and Web servers. The default is Disabled. Clicking Secure Exchange Options displays the Secure Exchange Options dialog box.
SSL Listening Port: Specifies the port that will be used for Secure Exchange communication.
IMPORTANT: iChain Proxy Services requires that each service (including HTTPS) use a unique IP address and port combination. The default HTTPS port is 443. Attempts to enable HTTPS for more than one service on the same IP address and port will result in a TCP bind error.
Certificate: This drop-down list displays certificates you have stored on your appliance. System-generated certificates do not appear in the list.
Use this field after you have stored a certificate you created specifically for the Web server accelerator you are creating. This will prevent browsers from receiving certificate confirmation messages each time they access the appliance. For more information, see Managing Appliance Certificates.
Enable Path-Based Multi-homing: This option is enabled only when you have created another accelerator definition and have not created a standard multi-homing relationship between previously defined accelerators on the iChain Proxy Services appliance. In other words, you don't have multiple accelerators sharing the same accelerator IP address and port.
Path-based multi-homing lets you configure the system so that a multi-homing master accelerator fills general requests from a site's main Web server and routes specific requests to specialized child accelerators that fill from other specialized Web servers. This option lets you create child accelerators for path-based multi-homing configurations.
When you enable path-based multi-homing for the accelerator you are defining, you must also click the Path Rule Options button and specify a path rule that the multi-homing master can use to route traffic to the accelerator you are defining. For more information, see Path Rule Options Dialog Box.
You will also notice that if you have created multiple accelerators that can function as multi-homing masters, when you select a name in the Multi-homing Master drop-down list, the DNS Name, Accelerator Proxy Port, and Accelerator IP Addresses selections dynamically change to match the accelerator whose name you have selected. For more information regarding path-based multi-homing, see Multi-homing and Path-Based Support.
Multi-home Master: This drop-down list contains the names of accelerators you have defined that can function as multi-homing masters, meaning they are not configured as child accelerators to other multihoming masters.
Custom Login Page Location (blank to disable):The field on the Web Server Accelerator dialog for the custom login page is populated with the directory from SYS:ETC\PROXY\DATA, where the login pages can be found. If a user enters NIKE in this field, the user is specifying thta the custom login/logout pages will be found in SYS:ETC\PROXY\DATA\NIKE.
Web Server Port: The port number that the origin Web server is listening on for incoming connections. The default for HTTP is 80 (1 - 65535).
Web Server Addresses: The IP address or local DNS name of each Web server from which the appliance fills the cache for this Web server accelerator. The appliance must be able to fill all requests through any of these names or addresses unless path-based multi-homing is being used.
Accelerator Proxy Port: The port number that the proxy server is listening on for incoming connections. The default for HTTP is 80 (1 - 65535).
Accelerator IP Addresses: For normal accelerator situations, non-path-based multi-homing configurations, and accelerators configured as multi-homing masters, this is the appliance's IP addresses to which DNS resolves the Web server's (or Web site's) DNS name and on which the Web server accelerator listens for incoming connections from the Internet.
For child accelerators in path-based multi-homing configurations, this is the IP address or addresses to which the multi-homing master forwards browser requests that match the specified path rule.
Path: Configure > Web Server Accelerator > Insert (Modify) > Log Options
Figure 76
Log Options Dialog Box
This dialog contains numerous settings for logging the operations and errors of the iChain Proxy Server.
Common: If this option is checked, only three parameters (Date, Time, and Client IP) will be enabled. No others wil be selectable.
Extended: If this option is checked, all of the Extended log fields will be enabled. The Date, Time, and Client IP options are checked by default and may not be unchecked.
Rollover When File Size Reaches (in MB): If this option is selected, the log file will roll over (empty and start writing from the beginning) after the file reaches the size specified in the edit field.
Rollover Every: If this option is selected, the log file will roll over automatically over a specified time interval or starting at a certain day.
Limit Number of Files to: If this option is selected, the number of old log files kept on the server will be limited to the number entered in the edit field.
Delete Files Older Than: If this option is selected, old log files will be deleted on the time interval specified.
Do Not Delete: If this option is selected, none of the log files will be deleted.
FTP Log Push Button: Launches the FTP Log Push Configuration dialog box.
Path: Configure > Web Server Accelerator > Insert (Modify) > Log Options > FTP Log Push
Figure 77
Log Push Configuration Dialog Box
This dialog box enables you to set FTP log push options.
FTP Log Push Enable: If this option is checked, FTP log push is enabled.
Host Server: The name of the host server where the logs will be pushed.
Login Name: The user name on the host server to log in as. This user must have appropriate rights to be able to push logs to the server.
Password: The password for the user on the host server.
Default Directory: The directory on the host server where the logs will be pushed.
IP Address: The IP address of the host server.
Delete Log Files from ICS Server after Push: If this option is checked, the logs will be deleted from the iChain Proxy Server after they have been pushed to the specified host server.
Log Push Result: This field displays the result of the log push.
Push Logs When the Logs Rollover: If this option is checked, the logs will automatically be pushed to the host server when they roll over.
Days to Push the Logs: The Logs will be pushed to the host server every day that has been checked.
Time to Push the Logs: The logs will be pushed to the host server starting at the time specified by these two fields.
Log Types: Check each type of log that will be pushed to the host server.
Path: Configure > Web Server Accelerator > Insert (Modify) > Secure Exchange Options
Figure 78
Secure Exchange Options Dialog Box
This dialog box provides additional Secure Exchange options.
NOTE: When Secure Exchange is enabled, the Web server port must be configured under Secure Exchange Options.
Port (Client to Proxy): This field specified which port will be used for communication between the client (browser) and the proxy server. The default is port 443.
Port (Proxy to Web Server): This field specifies which port will be used for communication between the proxy server and the origin Web server. The default is port 80. When Secure Exchange is enabled, this port must be configured here and not at the Web Server Accelerator dialog box.
Mark Pages Non-Cacheable on the Browser: If this option is checked, all pages will be marked as non-cacheable on the browser.
Enable Secure Access Between Secure Exchange and Web Server: If this option is checked, the connection between the proxy server and the origin Web server will be secured.
List of Trusted Roots: This list displays the current list of trusted roots in use by the proxy server.
Import Trusted Root: When you click Insert, the Import Trusted Root button is enabled. If you click this button, it will launch the Import Trusted Root dialog box.
Path: Configure > Web Server Accelerator > Insert (Modify) > Secure Exchange Options > Import Trusted Root
Figure 79
Import Trusted Root Dialog Box
This dialog box allows the user to import trusted roots into the system for use during Secure Exchange.
Imported Filename: The name of the trusted root file.
Inserted Trusted Root Contents: The contents of the trusted root file.
Path: Configure > Web Server Accelerator > Insert > Enable Path-Based Multi-homing > Path Rule Options
Figure 80
Path Rule Options Dialog Box
This dialog box lets you specify a string that, if present in the browser request, will cause the multi-homing master accelerator to route the request to the child accelerator being defined.
The string match can occur immediately following the DNS name (the Starts With option) or at the end of the URL (the Ends With option).
Sub-Path Match String: This is the string the multi-homing master will compare against the browser request. If the string is not found, the multi-homing master accelerator attempts to fill the request through the Web server addresses in its accelerator definition. If the string is found, the multihoming master accelerator routes the request to the accelerator with the matching string.
Starts With: Checking this option indicates to the multi-homing master that the Sub-Path Match String field contains a path that might immediately follow the DNS name in the browser request. If the string matches the path in the request, the multi-homing master forwards the request to the child accelerator being defined. The initial forward slash (/) is required in the string to directly access the child page. If you don't include the initial forward slash, it will only find your child page (for example, http://www.icweb.com/yahoo) after you visit the main/master (http://www.icweb.com) page. Only when you have the intial forward slash can you access your child page directly. If you try to access the child page without the forward slash, you will get a Page Not Found error.
Remove Sub-Path from URL: You should check this option if the path string doesn't actually appear at the root of the Web server. If this option is checked, the string is stripped from the request before the request is sent to the Web server. This probably indicates that the object is at the root of the Web server. If this option is not checked, the matched string is retained in the request sent to the Web server.
Ends With: Checking this option indicates to the multi-homing master accelerator that the Sub-Path Match String field contains a file extension, such as gif, jpg, mpg, cgi, and so on. If a match is found at the end of the browser request, the multi-homing master will route the request to the child accelerator being defined.
Path: Configure > FTP
Figure 81
FTP Tab
The FTP tab lets you configure the appliance to provide an FTP listening address (Mini FTP Server) for appliance management, FTP forward proxy (client acceleration), and FTP reverse proxy (Web server acceleration) services.
IMPORTANT: All appliance FTP services listen on port 21. Therefore, each IP address on the appliance can be configured for only one FTP service (Mini FTP, Forward Proxy, or FTP Accelerator).
Mini FTP Server: Check an address in the Server IP Addresses list to enable it for FTP listening. If an address is not checked, you cannot upload or download files using FTP.
FTP Client Accelerator: Check an address in the Proxy IP Addresses list to enable FTP forward proxy services on that address.
syntax: ftp appliance_proxy_address
username: anonymous$ftp_host
password:
ftp://anonymous$ftp_host@appliance_proxy_address
ftp://anonymous@ftp_host
IMPORTANT: The default separator is the dollar sign ($), and this character should be used whenever possible. The pound sign (#) and the at sign (@) are also known to work as separators.
Although the browser-based tool will let you specify other characters such as the comma (,), the percent sign (%), and the colon (:), these characters will not work as FTP separators, and they will not appear in command line interface queries.
If you are using an FTP client, you might need to configure the client to recognize the dollar sign ($).
FTP Web Server Accelerator: This list displays a summary of the FTP accelerators created in the FTP Accelerator dialog box. You can only enable or disable the service represented by an item in the list. To modify a list item, click the item > click Modify.
Path: Configure > FTP > Insert under FTP Accelerator list
Figure 82
FTP Accelerator Dialog Box
The FTP Accelerator dialog box lets you define an FTP accelerator service on the appliance.
Enable This Accelerator: Checking this option activates the defined FTP accelerator service.
FTP Server Name: Either the IP address or DNS name of the FTP server being accelerated.
Accelerator IP Addresses: All appliance IP addresses are listed. Checking the box to the left of an address enables FTP acceleration through the address for the server listed in the FTP Server Name field.
Path: Configure > Authentication
Figure 83
Authentication Tab
The Authentication tab lets you enable the appliance to authenticate users to an LDAP or RADIUS authentication source.
Authentication Profiles List: This lists the authentication profiles you have configured on the appliance using the Authentication dialog box.
Path: Configure > Authentication > Insert under the Authentication Profiles list
Figure 84
Authentication Dialog Box
The Authentication dialog box lets you assign an authentication profile name and specify either LDAP or RADIUS as the authentication source.
IMPORTANT: iChain Proxy Services doesn't recognize case differences in profile names. MyProfile and myprofile are, effectively, the same profile name.
Also, iChain Proxy Services partially overwrites and concatenates previously created profiles without warning if a duplicate name is used. Therefore, if you create a profile named MyProfile and later create another profile named myprofile, iChain Proxy Services will remove the first name, concatenate parts the first profile with the second, and use the second name.
To avoid these problems, ensure that each profile has a unique name.
After selecting the authentication source, you must configure the source by clicking its respective Options button.
Path: Configure > Authentication > Insert > LDAP Authentication > LDAP Options
Figure 85
LDAP Options Dialog Box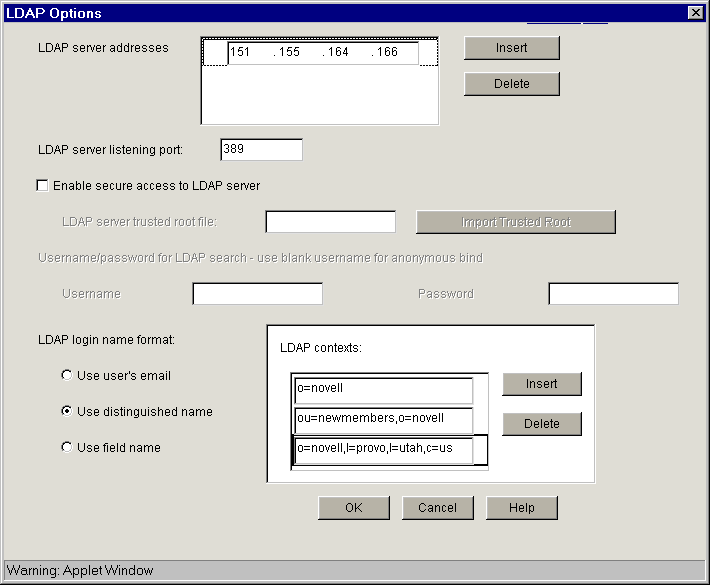
Use the LDAP Options dialog box to configure the appliance so users can authenticate through an LDAP database.
LDAP Server Addresses: The IP addresses of the LDAP servers. Specifying multiple LDAP servers allows for failover LDAP servers. If the first LDAP server cannot be accessed, the next LDAP server on the list will be tried, an so-on down the line in the order specified.
LDAP Server Listening Port: The port number the LDAP server is listening on for requests from LDAP clients. The default is 389 for normal access. Use 636 for secure access.
Enable Secure Access to LDAP Server: Checking this box causes the data sent between the LDAP client and the LDAP server to be sent using SSL.
LDAP Server Trusted Root File: The path on the appliance to a trusted root file that contains the Certificate Authority (CA) used by the LDAP server in the profile you are creating.
iChain's proxy server fills this field with information for the trusted root file you create using the Import Trusted Root button. See the instructions found in Import Trusted Root Dialog Box.
If the LDAP server uses a CA for which you have previously created a trusted root file, you can manually type the path and filename in this field. For example, you might be using the same LDAP server for multiple authentication profiles.
Import Trusted Root: Clicking this button opens the Import Trusted Root dialog box (see Import Trusted Root Dialog Box).
Username: Enter the username to use for accessing the LDAP server.
Password: Enter the password to use for accessing the LDAP server.
The contents of this box change depending on the option selected.
Select this option to have users log in using their e-mail name field in the LDAP database. You must provide one or more contexts in which the LDAP server will search for the e-mail name.
This option is somewhat redundant with Use Field Name because the e-mail name is simply an LDAP field name. E-mail is offered separately because it is used so often.
LDAP Search Base: Click Insert to enter the context of one or more LDAP containers from which the search for the e-mail name should begin.
Select this option to allow users to authenticate using their LDAP usernames. Users can use either their fully distinguished (full LDAP contexts) LDAP usernames, or you can provide a list of LDAP contexts so users only need to type their usernames.
IMPORTANT: Using this option with Netscape's LDAP server requires a special setup procedure.
LDAP Contexts: This list contains specific contexts in which the LDAP server will look for usernames. This provides a shortcut to authentication of users by allowing them to type only their LDAP usernames.
The appliance searches each context until it either locates the name or exhausts the search. If duplicate names exist in different contexts, the appliance searches until the correct name/password match is found.
Select this option to require that users enter a specific LDAP field name.
Field Name: The LDAP field name (such as User ID) through which users can authenticate.
LDAP Search Base: Click Insert to enter the context of one or more LDAP containers. The appliance will perform a subtree search in all containers in the list and in their subcontainers.
Path: Configure > Authentication > Insert > LDAP Authentication > LDAP Options > Import Trusted Root
Figure 86
Import Trusted Root Dialog Box
The Import Trusted Root dialog box lets you create a trusted root file with a .DER extension that contains information identifying the Certificate Authority used by the LDAP server for the profile you are creating.
To create a trusted root file:
In the Imported Filename field, type a path and filename for the trusted root file.
The filename can contain up to eight alphanumeric characters. The appliance automatically appends the .DER extension if you don't include it.
IMPORTANT: Be sure you use a unique filename for each .DER file. The appliance overwrites files without warning if you use duplicate filenames.
Remember that iChain Proxy Services is not case-sensitive, so MyCert.DER and mycert.der are, effectively, the same filename.
The path must be a directory path that already exists. You cannot create directories on the appliance.
If you want to list your trusted root files later, use an FTP-accessible directory, such as SYS:\ETC\PROXY\DATA, as the path. Otherwise, you won't be able to list the files. For a list of FTP-accessible directories, see Limitations of the Appliance's Mini FTP Server.
If you don't include a path with the filename, the proxy server creates the file at the root of the SYS: volume. You cannot see the root of the SYS: volume using FTP.
Using a text editor on your configuration workstation, open the .DER file for the Certificate Authority > select the file contents > paste the contents to the clipboard.
To obtain .DER files, contact a Certificate Authority vendor.
Return to the Import Trusted Root dialog box > paste the clipboard contents into the text box above the OK and Cancel buttons.
Click OK.
Path: Configure > Authentication > Insert > RADIUS Authentication > RADIUS Options
Figure 87
RADIUS Options Dialog Box
Use this dialog box to specify a RADIUS server the appliance can use for authentication.
NOTE: Port 1812 is the default RADIUS server port, however, the Novell RADIUS server defaults to port 1645. It is possible for a different default port to be specified when the Novell RADIUS server is loaded.
RADIUS Server Address: The IP address of the RADIUS server.
RADIUS Server Listening Port: The port number on which the RADIUS server listens for incoming authentication requests.
RADIUS Shared Secret: The string the RADIUS server uses to verify that the appliance can request authentication of users.
RADIUS Server Reply Time in Seconds: The total time the appliance will wait for a response from the RADIUS server before authentication fails. The default is 7 seconds.
RADIUS Resend Time in Seconds: The interval in seconds between appliance requests to the RADIUS server. The default is two seconds. This means that the appliance could send three requests before the 7-second default limit expires and the authentication request fails.
iChain 2.0 supports RADIUS authentication via the RADIUS server supplied by Novell or a RADIUS server supplied by third-party vendors. The Novell RADIUS server uses NDS® eDirectoryTM 8.5 as the underlying database for storing user objects.
If the Novell RADIUS server is running on the iChain authorization server, it has the ability to indicate the fully distinguished name of the user object that was authenticated via RADIUS. iChain must use the fully distinguished name of the user in order to perform ACL rights checking when accessing a protected resource. A RADIUS server provided by a vendor other than Novell will store user objects in their own database.
iChain must be able to map this third-party name to a user object stored in NDS eDirectory 8.5 on the authorization server in order to determine if the user has rights to the protected resource he or she is attempting to access. This is done by performing an LDAP subtree search on the authorization server for the user name entered on the iChain login dialog. In order to perform this search, two fields must be changed on the ACLCheck authentication profile.
A search base must be specified that identifies an NDS container that defines where in the tree to begin the search and the anonymous bind feature must be set to No. This is done by entering the following commands on the iChain Proxy Services console screen:
add authentication aclcheck ldap searchbase = container name set authentication aclcheck ldap bindanonymous = no apply
If there is already a value specified for the searchbase, the set command must be used instead of the add command, as shown below:
set authentication aclcheck ldap searchbase = container name
The container name may specify an NDS organization or an organizational unit that appears on the authorization server. For example:
add authentication aclcheck ldap searchbase = o=novell
The implication here is that an eDirectory user object must be created on the authorization server whose CN is the same as the RADIUS user name and it must appear hierarchically in the tree somewhere below the container specified by the searchbase.
Also verify that iChain has defined an LDAP server, user, and password. This is needed to perform the searchbase lookup.
For example:
>get authentication aclcheck ldap
authentication aclcheck ldap address = 10.252.3.5
authentication aclcheck ldap bindusername = cn=admin;o=novell
authentication aclcheck ldap bindpassword = password
If the above values are empty, they can be input at the iChain browser GUI > Configure > ACL tab.
Path: Configure > Management
Figure 88
Management Tab
The Management tab lets you identify objects that will be either pinned (explicitly downloaded and retained in cache as long as possible) or bypassed (explicitly not cached when requested by users). It also lets you specify how pinned objects are stored on the appliance (pin type).
Enable Pin List: Check this box to activate pinning on the appliance. For information regarding what pin lists are and how they function, see The Pin List and Pin List Examples.
NOTE: Checking this option affects only the pinning of objects on the appliance. It has no effect on whether objects are cached unless the pin type is set to Bypass.
Default Refresh Frequency: Lets you specify when the appliance checks to see if items should be added to or removed from the list of objects being pinned. At refresh time the appliance re-evaluates the objects in cache for the URL list and downloads those objects that have changed. For absolute URLs, objects in links are also evaluated down to the link level specified. Choices range from one time only to any arbitrary time interval.
Default Refresh Time: Lets you specify the time of day or the time interval when pinned objects will be refreshed. To specify an interval, you must first select Timed Interval from the Default Refresh Frequency drop-down list.
The pin list lets you specify URL patterns for identifying objects on the Web. You configure each URL pattern in the list with specific handling instructions as explained below.
URL Mask: This can contain complete or partial URL patterns. A single URL mask might apply to a large set of URLs, or it might be so specific that only a single file on the Web matches it. For more information, see Pin List Examples.
Pin Type: This specifies whether and how the appliance will cache objects that match the URL mask.
Pin Links: This specifies how many link levels iChain Proxy Services will follow the pin type rule you've established.
Pin Images: This option is used to pin image files that reside on a different host than the page requested.
Refresh Frequency/Time: This lets you specify a refresh frequency and time for the URL that is different from the default values shown above the pin list. After inserting the URL, click Modify to see the dialog box that lets you change these fields. Functionality is the same as described for the default refresh frequency fields.
The Dynamic Bypass feature lets you configure the appliance so that specific errors from Web sites are explicitly not cached and subsequent requests to the Web sites are simply passed through for a specific time period. For more information, see Dynamic Bypass.
Enable Dynamic Bypass (Requires Router To Be Enabled): Checking this option enables the Dynamic Bypass feature.
Dynamic Bypass Duration: The period of time in hours and minutes that the URL remains in the Dynamic Bypass list, causing the appliance to transparently pass matching requests through to the origin Web server.
Dynamic Bypass Error Codes to Enable: This section lists all valid HTTP 1.1 errors. You can check and uncheck all the errors using the All and None buttons, or you can check only the errors you want enabled for dynamic bypass.
Enable Dynamic Bypass Logging: Checking this option enables logging of all dynamic bypass transactions. Log entries include the time of the log entry, the word Bypassed, and the URL added to the Dynamic Bypass list.Click Log Options to set log file rollover options and specify the handling of the oldest log files. For help with setting these options, see Log Rollover Options. The information most relevant to the dynamic bypass feature is contained in Configuration Step 3: Specifying Rollover Options, and Configuration Step 4: Specifying Handling of Older Files.
The two drop-down lists below the pin list let you specify object caching based on the following:
The Cache option lets you specify whether cachable objects that meet the criteria are always cached.
The Cache option is sometimes misinterpreted to imply that objects meeting the criteria are always cached. That is not the case. The proxy server appliance will not cache objects that Web server administrators have marked non-cachable.
By the same token, the Do Not Cache option is sometimes misinterpreted to imply that objects meeting the criteria are never cached. That is also not the case. Objects containing question marks and /cgi in the path might meet other criteria that cause them to be cached. This option only causes the proxy server to ignore question marks and /cgi in determining whether to cache objects.
Clicking the Reset button resets the two drop-down lists back to their default (do not cache) settings.
Path: Configure > Tuning
Figure 89
Tuning Tab
The Tuning tab lets you restrict and enable functionality that affects all appliance operations. The implications for each option are explained below.
Ignore Refresh Requests from Browser: When a user clicks Refresh or Reload in the browser, the default system action is to send a new request to the Web server. Checking this option causes refresh or reload requests to be filled from the cache until cache freshness parameters are met. See Cache Freshness Dialog Box.
Filter Cookies: If enabled, iChain Proxy Services removes all cookie HTTP request headers from requests forwarded to Web servers. It also removes all set-cookie HTTP reply headers from replies coming from Web servers.
Enable Persistent Connections to Browsers: If enabled, all connections from browsers to the appliance remain open. This makes the response time between the appliance and browsers faster.
Enable Persistent Connections to Origin Servers: If enabled, all connections from browsers to Web servers (through the appliance) remain open. This can cause some Web servers and their networks to crash, depending on the number of simultaneous connections they support.
Enable Initial Splash Screen: If enabled, browsers receive first-time and periodic notification that their requests are being processed by the appliance. The splash screen is customizable so that ISPs, for example, can advertise the fact that they are providing accelerated Web service. For information on customizing the splash screen, see Using FTP to Customize the Appliance Splash Screen. The splash screen is disabled (turned off) by default.
Act as a Single User (Private) Cache: If enabled, iChain Proxy Services caches objects that have been flagged for private caches only.
Enable Read-Ahead Images Embedded in the Page: If checked, iChain Proxy Services will retrieve and cache objects that have been flagged Read-Ahead. You specify the maximum number of Read-Ahead objects the proxy server will retrieve in the Maximum Number of Concurrent Read-Ahead Requests field.
Path: Configure > Tuning > Cache Freshness
Figure 90
Cache Freshness Dialog Box
The Cache Freshness dialog box lets you set time values governing when iChain Proxy Services revalidates requested cached objects against those on their respective origin Web servers. If requested objects have changed, iChain Proxy Services re-caches them. Default field values are shown in Figure 90.
iChain Proxy Services does not automatically recache objects when they expire. Expired objects are revalidated (and recached if they have changed) only when requested by browsers and in accordance with the time values set in the Cache Freshness dialog box. For more information on the appliance's cache-freshness features, see Cache Freshness and Managing Cache Freshness.
HTTP Maximum: The maximum number of hours or days iChain Proxy Services will serve HTTP data from cache before revalidating it against content on the origin Web server. No object is served from cache after this value expires without being revalidated.
This overrides a freshness or Time to Expire header value specified by the Webmaster if he or she specified a longer time.
You use this value to reduce the maximum time iChain Proxy Services waits before checking whether requested objects need to be refreshed.
HTTP Default: The value iChain Proxy Services uses to determine when to revalidate requested objects for which Webmasters have not specified a freshness or Time to Expire header value.
HTTP Minimum: The minimum number of hours or minutes iChain Proxy Services will serve HTTP data from cache before revalidating it against content on the origin Web server. No requested object will be revalidated sooner than specified by this value.
This overrides the freshness or Time to Expire header value specified by the Webmaster if he or she specified a shorter time.
You can use this value to increase the minimum time iChain Proxy Services waits before checking whether requested objects need to be refreshed. This parameter does not override No Cache or Must Revalidate directives from the origin Web server.
FTP Default: The number of hours or days FTP data remains in cache before it expires. iChain Proxy Services does not revalidate expired FTP objects. It simply recaches them when they are requested.
Gopher Default: The number of hours or days Gopher data remains in cache before it expires. iChain Proxy Services does not revalidate expired Gopher objects. It simply recaches them when they are requested.
Continue Accelerator Fill Time: The number of minutes or hours that the appliance's Web acceleration services ignore browser request cancellations and continue downloading objects from the target Web server until the download is complete.
Continue Forward Fill Time: The number of minutes or hours that the appliance's HTTP forward and transparent proxy services ignore browser request cancellations and continue downloading objects until the download is complete.
HTTP Retries: The number of retry requests that will be issued.
Path: Configure > Mini Web (to see this tab, click the upper-right corner of the Tuning tab.)
Figure 91
Mini Web Tab
The Mini Web tab lets you configure how appliance-generated error pages are vended to browsers.
HTTP Web Server Error Vending Port: The port the browser will use when requesting objects that are part of the error pages. Changing this value does not affect the port for appliance administration, which is fixed at 1959.
HTTP Web Server Error Page Language: From the drop-down list, you can select a language for appliance-generated error messages to browsers.
Path: Configure > Access Control
The Access Control tab lets you define the parameters necessary to set up access control. This tab includes the following fields:
ISO Object LDAP Name: Specifies the name of the iChain Service Object (ISO) containing parameter settings defining your iChain domain or infrastructure.
Password Management Servlet URL: Defines the URL of the password management servlet on the iChain Proxy Server. This servlet enables users within your iChain infrastructure to change their passwords. The password management servlet is installed at /ichain/PasswordExpired.html on the proxy server. The URL for this servlet should be defined as http://x.x.x.x/ichain/PasswordExpired.html where x.x.x.x is the IP address of the iChain Proxy Server.
LDAP Server Addresses: Specifies the IP addresses of the iChain LDAP access control servers. Specifying multiple LDAP servers allows for load-balancing of the LDAP servers. Requests to the LDAP servers for access control are done in a round-robin fashion.
Enable Secure Access to LDAP Server: Checking this box causes the data sent between the LDAP client and the LDAP server to be sent using SSL.
LDAP Server Trusted Root File: The path on the appliance to a trusted root file that contains the Certificate Authority (CA) used by the LDAP server in the profile you are creating. The system fills this field with information for the trusted root file you create using the Import Trusted Root button. If the LDAP server uses a CA for which you have previously created a trusted root file, you can manually type the path and filename in this field. For example, you might be using the same LDAP server for multiple authentication profiles.
Import Trusted Root: Clicking this button opens the Import Trusted Root dialog box.
LDAP Port: Specifies the port on which the LDAP server will listen for access control requests. The default is 389 for normal access. Uses 636 for secure access.
LDAP Proxy User: Specifies the LDAP username for the iChain Proxy Server to use when making requests for access control information from the iChain LDAP access control server.
Password: Specifies the LDAP password for the iChain Proxy Server to use when making requests for access control information from the iChain LDAP access control server.
Enable Unauthorized Access Rule Hit Logging: Specifies whether to enable logging for unauthorized access rule hits. The default is Disabled.
Enable Object Level Access Control: Specifies whether to enable object level access control.
IMPORTANT: When the access control profile is first generated, object level access control must be disabled. Apply the ACL profile, then mark Enable, then click Apply.
Enable Form Fill Authentication: Specifies whether to enable Single Sign-on with login HTML forms from origin servers.
Refresh ACLCheck: Refreshes the ACLCheck parameter settings.
Refresh OLAC: If OLAC has been enabled, use Refresh to force an immediate reread of OLAC parameters.
Refresh Form Fill: Refreshes the connection to LDAP servers and Form Fill policy rules.
  |