3.5 Generating Certificates
Micro Focus Kanaka for Mac 3.0.1 requires you to provide an x.509 certificate signed by a well-known certificate authority or another certificate authority that enables you export its trusted root certificate and deploy it to your Macs. The certificate must be in Privacy Enhanced Mail (PEM) format and must be installed in the appropriate secured location where the Kanaka Engine is running.
3.5.1 Certificate Types
There are two ways of obtaining a trusted certificate. Each method has its pros and cons.
-
Create a certificate signing request, and have your internal eDirectory certificate authority (CA) sign the certificate. This is referred to as an internal CA.
-
Create a certificate signing request, and have a trusted third-party certificate authority (CA) sign the certificate. This is referred to as an external CA.
Table 3-1 Internal and External Certificate Authority Considerations
|
Certificate Authority |
Pros |
Cons |
|---|---|---|
|
Internal |
|
|
|
External |
|
|
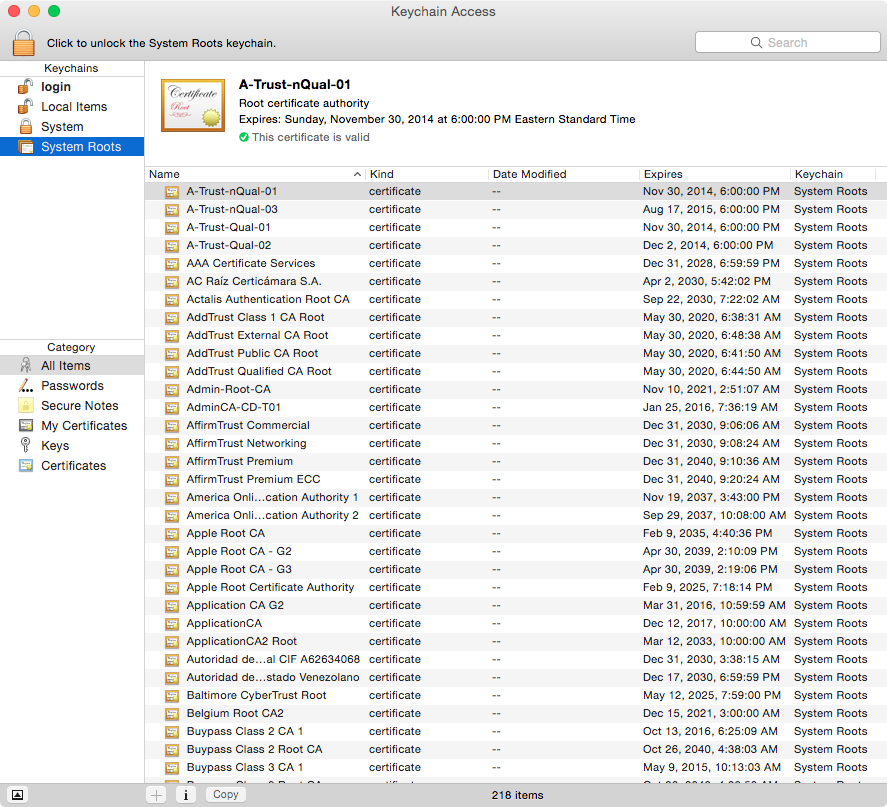
If you decide to use an external CA, you can obtain a list of CAs that are already trusted by opening the Keychain Access app and viewing the System Roots.
Figure 3-1 List of Trusted Certificate Authorities
3.5.2 Exporting an eDirectory Server Certificate
Depending on usage, choose to export the DNS or IP certificate for the Open Enterprise Server that hosts the Kanaka Engine. If Kanaka clients are configured with the DNS hostname of the OES server, you should export the DNS AG <server DNS hostname> certificate. If Kanaka clients are configured with the IP address of the OES server, you should export the IP AG <server IP address> certificate.
-
Log in to iManager.
-
From Roles and Tasks, click NetIQ Certificate Access.
-
Click Server Certificates.
-
Select the certificate for the OES server hosting the Kanaka Engine.
-
Click Export.
-
From the Certificates drop-down menu, select the certificate that you checked in Step 4.
-
Leave Export private key selected.
-
Leave Include all certificates in the certification path if available selected.
-
Enter a password to protect the private key.
This is required when Export private key is selected.
-
Click Next.
-
Click Save the exported certificate.
The file is saved to your Downloads folder with the name cert.pfx.
3.5.3 Convert a PKCS#12 Certificate to a PEM Certificate
iManager exports server certificates in the PKCS#12 or PFX format. This format needs to be converted to PEM format for the Kanaka Engine. You can use one of the following two methods to do so:
microfocus-kanakaengine-convertcert
-
Copy the cert.pfx file to the OES server hosting the Kanaka Engine.
-
In a terminal session on the OES server hosting the Kanaka Engine type:
microfocus-kanakaengine-convertcert
-
When prompted, enter the name of the certificate cert.pfx.
-
When prompted, enter the pass phrase that was used when the certificate was exported.
In this case, the pass phrase from Step 9 from Section 3.5.2, Exporting an eDirectory Server Certificate.
You are then prompted twice to enter a new pass phrase for the temporary key.
-
When prompted, re-enter the pass phrase you used for the temporary key in Step 4.
-
Stop the Kanaka Engine:
rcmicrofocus-kanakaengined stop
-
Copy the server.pem file:
cp server.pem /etc/opt/microfocus/kanaka/engine/config
-
Start the Kanaka Engine:
rcmicrofocus-kanakaengined start
Manual
-
Copy the cert.pfx file to the OES server hosting the Kanaka Engine.
-
In a terminal session on the OES server hosting the Kanaka Engine, enter the following commands and respond according to their responses:
openssl pkcs12 -clcerts -nokeys -in cert.pfx -out out.crt
-
When prompted, enter the password that you provided when you exported the certificate in Step 9 of Section 3.5.2, Exporting an eDirectory Server Certificate.
openssl pkcs12 -nocerts -in cert.pfx -out private.key
-
When prompted, enter the password that you provided when you exported the certificate in Step 9 of Section 3.5.2, Exporting an eDirectory Server Certificate.
openssl rsa -in private.key -out newkey.key
-
When prompted, enter the pass phrase that you provided when you exported the certificate in Step 9 of Section 3.5.2, Exporting an eDirectory Server Certificate.
cat newkey.key > server.pem
cat out.crt >> server.pem
The server.pem file can now be copied for use by the Kanaka Engine.
-
-
Stop the Kanaka Engine:
rcmicrofocus-kanakaengined stop
-
Copy the server.pem file:
cp server.pem /etc/opt/microfocus/kanaka/engine/config
-
Start the Kanaka Engine:
rcmicrofocus-kanakaengined start
3.5.4 Export an eDirectory CA Trusted Root
-
Log in to iManager.
-
From Roles and Tasks, click NetIQ Certificate Access.
-
Click Server Certificates.
-
Select the certificate for the OES server hosting the Kanaka Engine.
-
Click Export.
-
From the Certificates drop-down menu, select the organizational CA certificate (e.g. OU=Organizational CA.O=EINDOAK).
-
Leave the export format as DER.
-
Click Next.
-
Click Save the exported certificate.
The file is saved to your Downloads folder with the name cert.der.
The certificate is now ready to be deployed to macOS.
3.5.5 Adding a Trusted Root Certificate to macOS
-
Copy the cert.der file you created in Step 9 of Section 3.5.2, Exporting an eDirectory Server Certificate to macOS.
-
On macOS, open the Keychain Access.app.
-
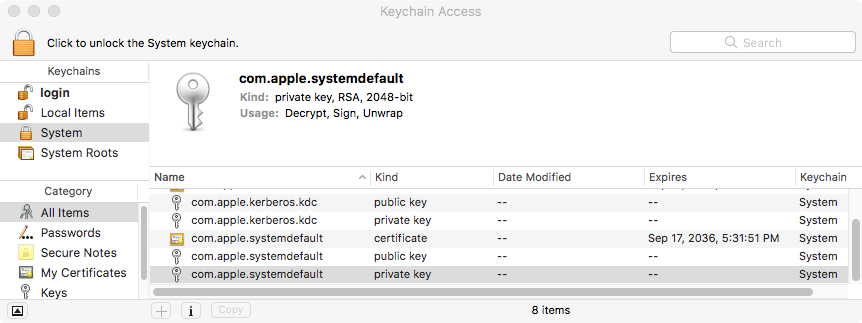
From the list of Keychains, select System.
-
Drag and drop cert.der to the System keychains.
-
When prompted, enter the necessary local administrator credentials.
The certificate is added to the System Keychain, but it must still needs to be trusted.
If you select the certificate Organizational CA, note that the text indicates that the root certificate is not trusted.
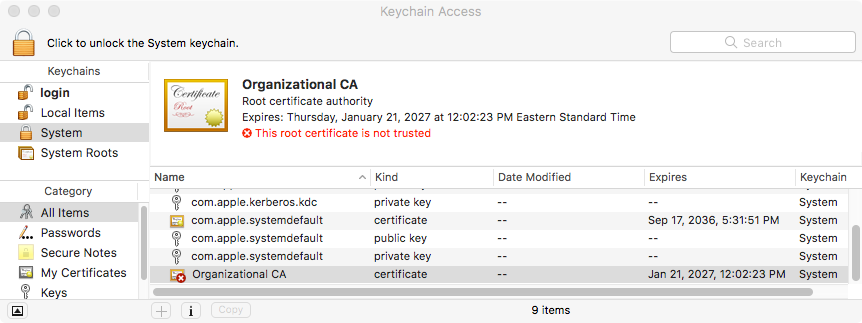
-
Double-click Organizational CA.
-
Expand Trust.
-
For When using this certificate, select Always Trust.
Note that the trusted status has not changed yet.
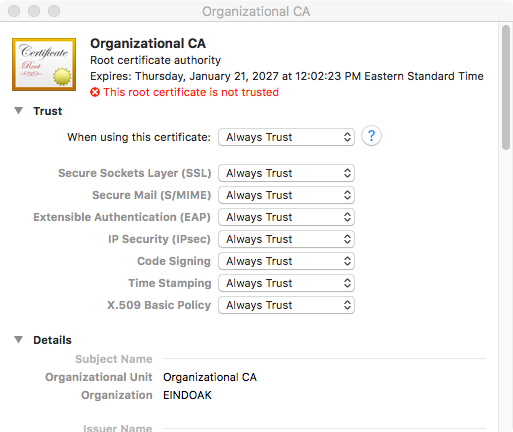
-
When prompted, enter the necessary local administrator credentials.
The status of Organizational CA should change to trusted.
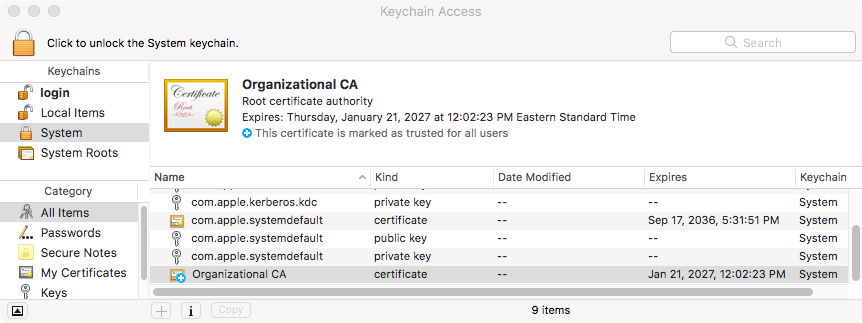
Kanaka clients can now successfully connect to the Kanaka Engine.
3.5.6 Creating Your Own Certificate
IMPORTANT:Be sure to store all your certificates in a secure location.
-
At the server that will host the Kanaka Engine, launch a terminal session.
-
Create a private key and certificate signing request via OpenSSL.
The following command uses OpenSSL to create your private key and certificate signing request (CSR) with a single command.
openssl req –newkey rsa:2048 –keyout private.key –out server.csr
-
When prompted, answer each of the questions pertaining to the certificate.
Question
Explanation
Country Name (two-letter code)
The ISO 3166 two-letter country code pertaining to the country where Kanaka Engine is located.
State or Province (full name)
The complete name of your state or province.
Locality Name (such as the city)
The complete name of your city.
Organization Name
The name of your company or organization.
Organizational Unit
The name of your department (optional).
Common Name
The name of your server.
Email Address
The email address of the certificate administrator.
Challenge Password
Generally optional, but required by some third-party certificate providers.
-
Submit the server.csr contents to the certificate authority of your choosing.
The certificate authority creates a certificate based the contents of the CSR file you created in Step 2. The certificate authority creates the certificate in one of many formats, such as DER, CER, CRT, or PEM. You can use any of these formats to produce the final PEM format that Micro Focus Kanaka for Mac will use.
-
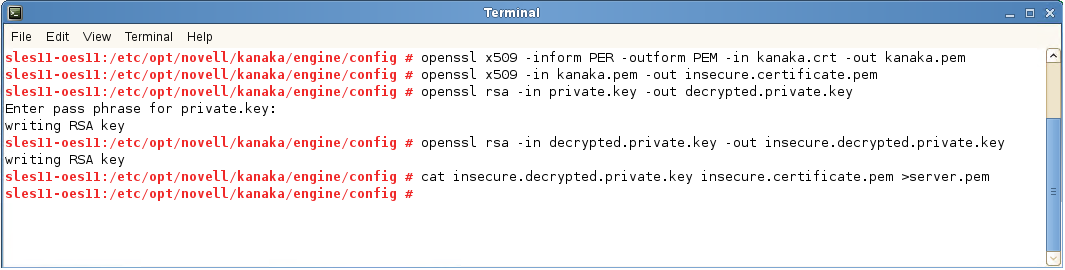
Convert the certificate to PEM format:
openssl x509 –inform DER –outform PEM –in certificate.crt -out certificate.pem
-
Remove the passphrase or password from the certificate:
openssl x509 –in certificate.pem -out insecure.certificate.pem
-
Decrypt the private key:
openssl rsa –in private.key -out decrypted.private.key
The private key is encrypted by default and needs to be decrypted for the Kanaka Engine to use.
-
Remove the passphrase or password from the certificate:
openssl rsa –in decrypted.private.key -out insecure.decrypted.private.key
-
Create the server.pem file with both the private key and certificate files:
cat insecure.decrypted.private.key insecure.certificate.pem > server.pem
The output file must be named server.pem.
For example:
-
Proceed with Section 5.0, Installing and Configuring the Engine.