7.4 Implementing Access Restrictions
After you access the Digital Airlines site as a public resource (see Section 7.3, Configuring Public Access to Digital Airlines), you can configure the site for authentication and authorization requirements. This section describes the following tasks:
7.4.1 Enabling an Authentication Procedure
After hiding the internal Web server behind the Access Gateway, you can add an authentication method to the Web site by using the following procedure:
-
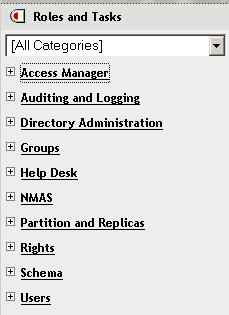
In the Administration Console, click > > .
-
Click > > > .
-
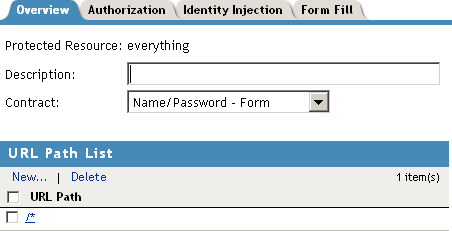
In the field, select .
IMPORTANT:Make sure to select the from the drop-down menu. does not work correctly if the base URL for the Identity Server is HTTP.
-
Click to return to the Protected Resources page.
-
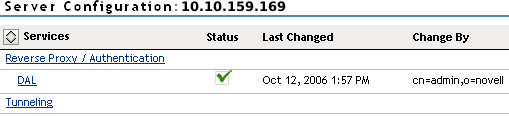
Click the link, then click > .
This pushes the new configuration to the server. When the configuration process is complete, the status returns to .
-
To test the results, open a browser and enter the URL of your Web site.
The Web site should now be protected and require you to log in by using a name and password. For this example, log in as the admin user of your Administration Console.

The Digital Airlines site appears.
-
Close all sessions of the browser.
The Digital Airlines page has a logout graphic, but it isn’t an action. The current session is active until you log out (which isn’t possible), until the session times out (the default value is 15 minutes), or you close all sessions of the browser.
-
Continue with Section 7.4.2, Configuring a Role-Based Policy.
7.4.2 Configuring a Role-Based Policy
Previously in the Digital Airlines example, you learned how to set up and configure Access Manager to protect a basic Web service. Access Manager also uses role-based access control (RBAC) to conveniently assign a user to a particular job function or set of permissions within an enterprise, in order to control access.
Access Manager enables you to assign roles to users, based on attributes of their identity, and then associate policies with the roles. In designing your own actual production environment, you need to decide which roles you need (such as, sales, administrative, and accounting). You create Role policies that assign the roles to your users, and then you create Authorization and Identity Injection policies that use the roles to control access.
This section explains how to set up an Identity Injection policy that customizes the main page of the Digital Airlines site. When the index.php page has access to the user’s name, the main page displays the name. If the user belongs to the sales_role role, the button is displayed on the page.
To configure an Identity Injection policy that uses a role, complete the following tasks:
Adding an LDAP Attribute to Your Configuration
The LDAP attribute that is added in this section is an LDAP attribute assigned to the User class in eDirectory. This attribute is used to assign users to the sales role.
-
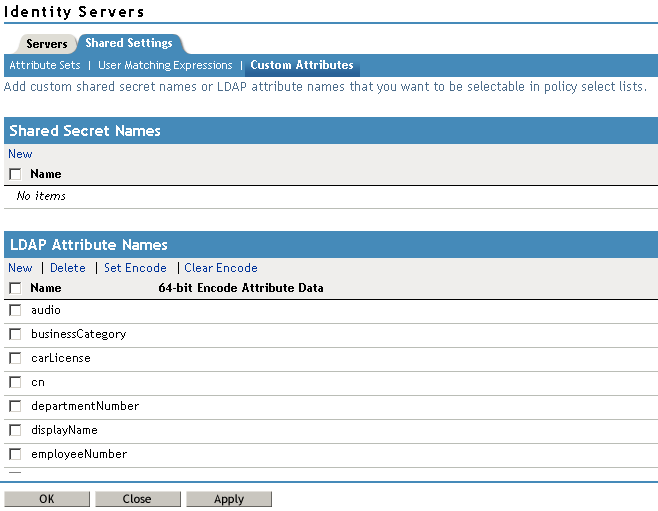
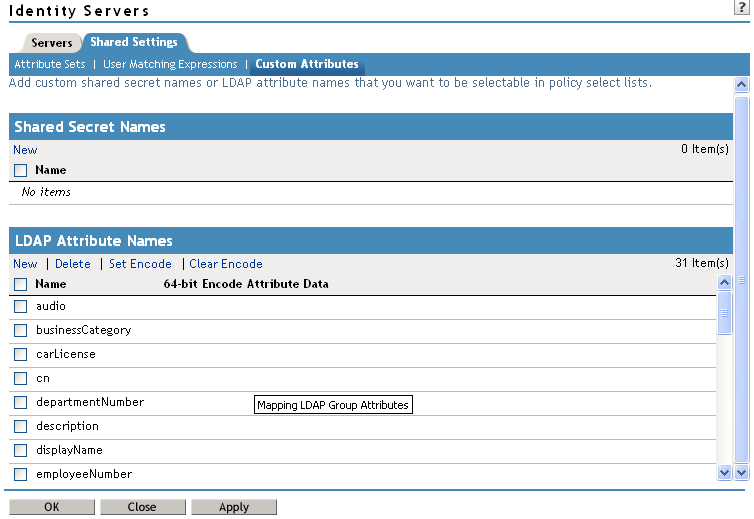
In the Administration Console, click > > > .
-
In the section, click , type description in the field, then click .
This adds the description attribute to the policy list of available LDAP attributes, and you can use this attribute to assign a role to your users.
-
Click .
-
Continue with Creating a Sales Role.
Creating a Sales Role
Use the following procedure to create a sales role for the Digital Airlines example. (For more information about Role policies, see Creating Role Policies
in the Novell Access Manager 3.0 SP4 Administration Guide.)
-
In the Administration Console, click > > > .

-
In the section, click
-
In the section, click then fill in the following fields:
Name: Specify .
Type: Select .
-
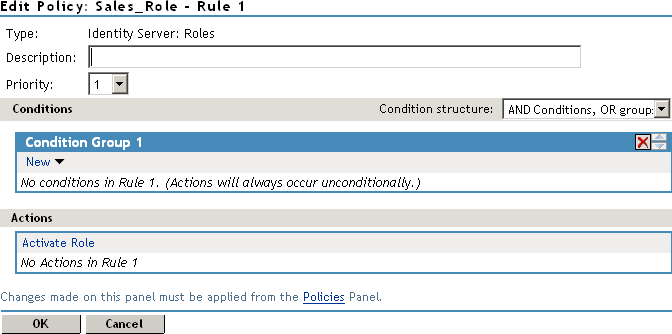
Click to open the policy editor.
-
In , click > , and assign the following values:
LDAP Attribute: Select (If is not included in the list, you can add it from this page. For instructions, see Step 5.a through Step 5.c.)
Comparison: Select .
Mode: Select .
Value: Select (from the drop-down box); specify Sales as the value.
Result on Condition Error: Select
If the attribute is not listed in the drop-down menu, create it by following this procedure:
-
In , click > , scroll to the bottom of the list, then click .
-
In the field, specify , then click .
-
In the field, select from the drop-down menu.
-
-
In the window, click , then specify sales_role in the field. Your rule should look similar to the following:
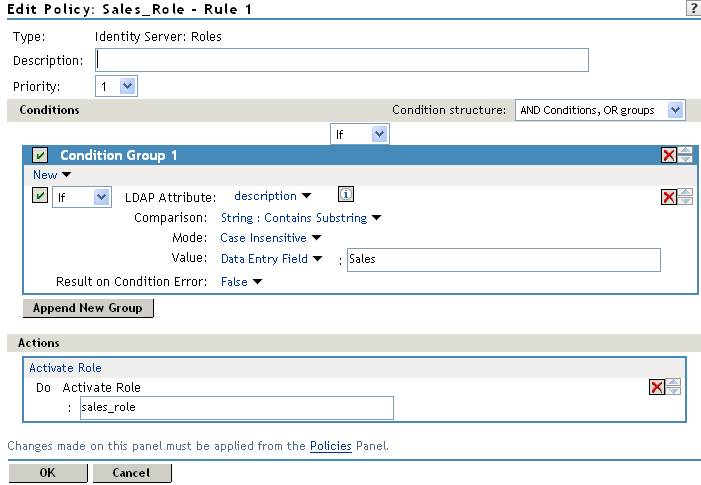
The value for might be case sensitive. If you are going to inject this role into a policy for a Web server, and the page on the Web server is configured so that it evaluates case, make sure the value entered here matches what is expected on the Web server. The button on the Digital Airlines site requires that this value be lowercase: sales_role.
-
Click to close the Rule editor, then click to close the .
-
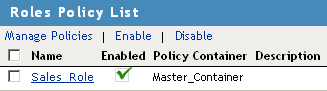
To save the Role policy, click , then click to return to the .
-
In the , select then click .
-
Click .
-
Click to update the Identity Server.
Wait for the to return to .
-
Continue with Creating a New User with a Sales Role.
Creating a New User with a Sales Role
After you have created a user policy, only users provisioned with that policy can access the protected Web resource. This section describes how to create a user that meets the conditions to be assigned the Sales role. These instructions assume that you are using the configuration store of the Administration Console as the LDAP user store. If you are using a different server than the LDAP user store, you need to modify these instructions:
-
In the Administration Console, click .
-
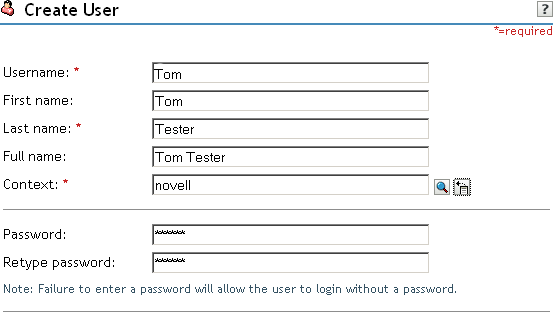
Click then fill in the following fields:
Username: Specify Tom.
First name: Specify Tom.
Last name: Specify Tester.
Context: Click the icon, then click . The user is automatically assigned the context of .
Password: Assign a password to the user.
Retype password: Retype the assigned password.
Your user entry should look similar to the following:
-
Scroll to the field, then click the icon.
-
In the text box, type Sales (initial uppercase), then click to return to the Create User page.
-
On the Create User page, click , then click to close the task.
Tom meets the requirements to be assigned the Sales role when he logs in.
-
Continue with Creating the Identity Injection Policy for a Custom Header.
Creating the Identity Injection Policy for a Custom Header
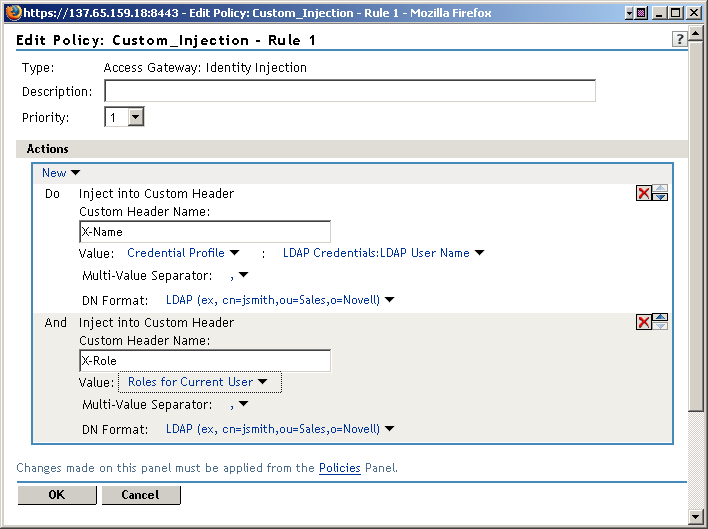
The following policy injects the user’s roles and DN into a custom header. The index.php page reads this information and uses it to display the user’s name. If the user is assigned the sales_role, the button is displayed on the main page.
-
In the Administration Console, click > > > > > > .
-
Click > .
-
In the section, click , then fill in the following:
Name: Specify .
Type: Select .
-
In the section, click > .
-
To inject the user’s name, fill in the following values:
Custom Header Name: Specify .
Value: Select . The is selected automatically for you.
-
To inject the user’s roles, click > , then fill in the following values for the second custom header:
Custom Header Name: Specify .
Value: Select .
Your policy should look similar to the following:
-
Click twice, then click .
-
Click .
-
In the section, select , then click.
-
Click .
-
Click the link, then click > .
-
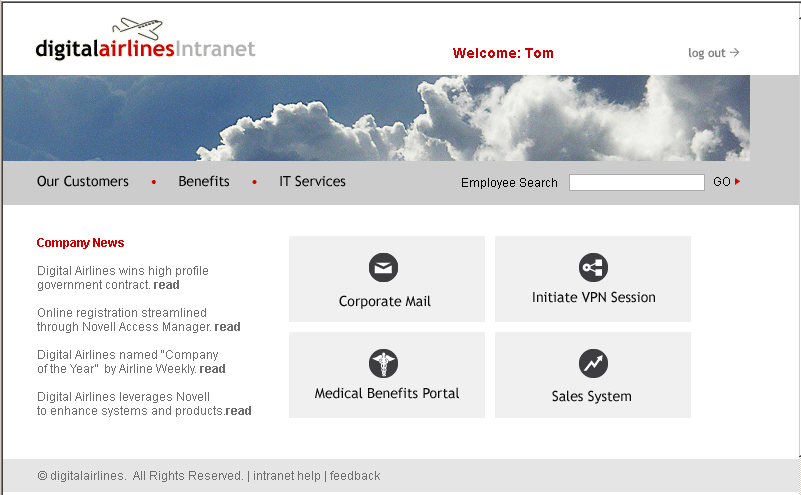
To test Tom’s access rights, complete the following steps:
-
Open a new browser, then enter the URL of the Digital Airlines Web site you’ve created.
In this example, it is am3bc.provo.novell.com.
-
When prompted for user ID and password from Access Manager, log in with Tom’s credentials.
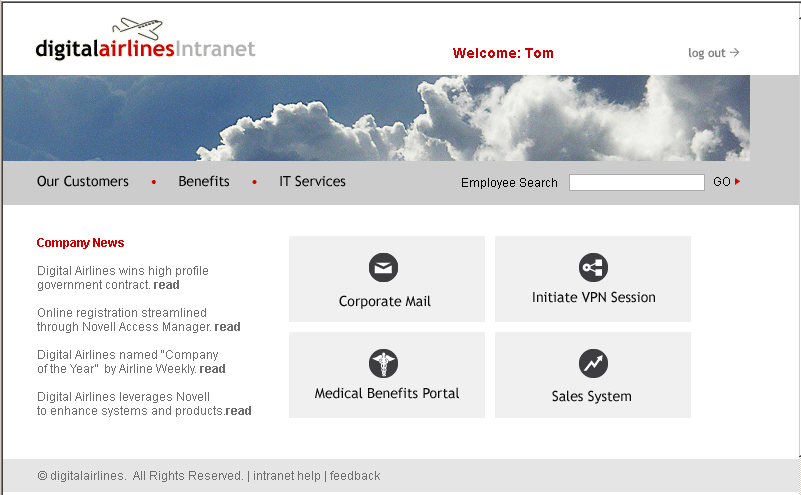
The page appears with a message at the top and the button appears in the lower right-hand corner of the page.
-
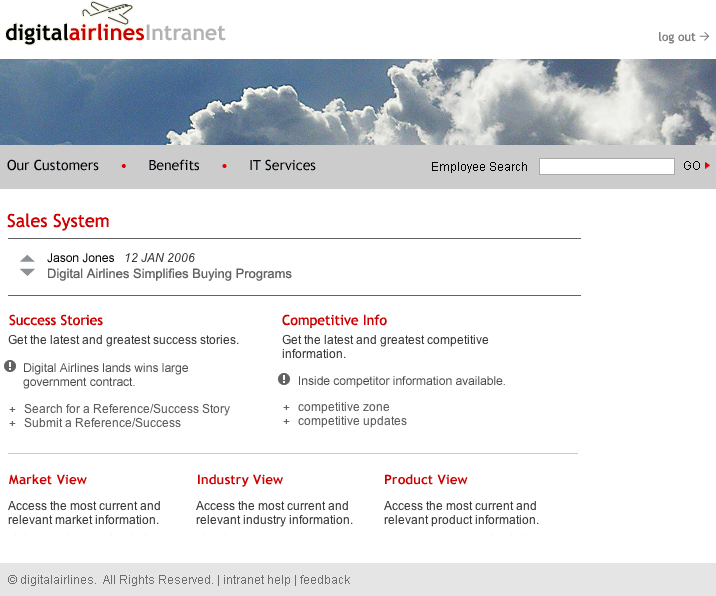
Click the button, and the Sales page appears.
-
Close all sessions of the browser.
-
-
To test that the sales_role is required for the button to appear, complete the following steps:
-
Open a new browser, then enter the URL of the Digital Airlines Web site you’ve created.
In this example, it is am3bc.provo.novell.com.
-
Log in as the admin user. The page should have a at the top of the page, but the button should not appear.
-
To the URL, add /sales, and the Sales page appears.
This illustrates that although the link is hidden, the Sales page is not protected.
-
Close all sessions of the browser.
-
-
Continue with Section 7.4.3, Assigning an Authorization Policy to Protect a Resource.
7.4.3 Assigning an Authorization Policy to Protect a Resource
Use the following procedure to limit access to the Sales page based on the Sales role:
-
In the Administration Console, click > > > > > .
-
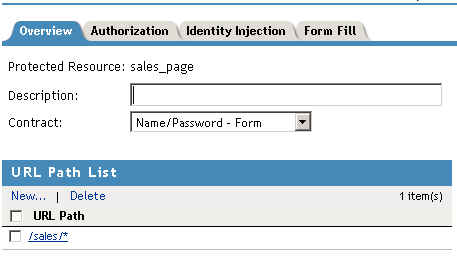
In the , click New, specify sales_page for the name, then click OK.
-
For the , select .
-
In the , click /*, modify it to specify /sales/*, then click .
Your protected resource should look similar to the following:
-
Click > .
-
Click then fill in the following fields:
Name: Specify
Type: Select .
-
Click .
The Edit Policy page appears.
-
In , click > , then specify the following values:
Comparison: Select .
Mode: Select .
Value: Select
Return on Condition Error: Select
-
In the section, ensure that is selected.
Your rule should look similar to the following:
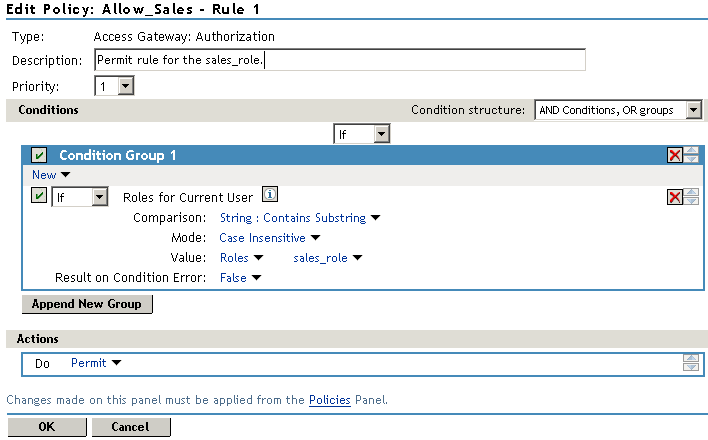
This rule allows everyone assigned to the sales_role to have access.
-
Click .
-
In the , select .
This second rule is a general deny rule for everyone who has not been assigned the sales_role.
-
Make sure the field is set to 10 and that the has no conditions.
-
In the section, click , select , then select .
-
In the text box, type the deny message: Sorry, you must work in sales today. Your rule should look similar to the following.
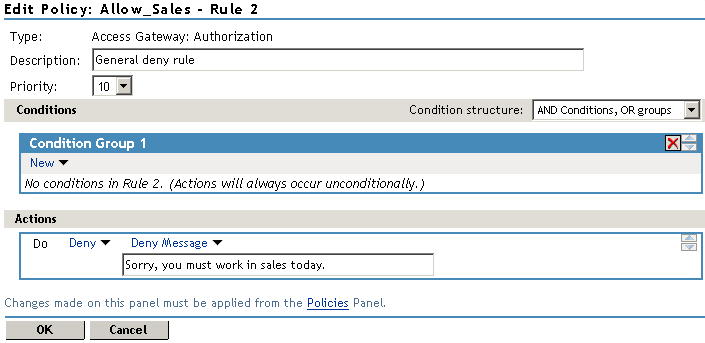
With no conditions in the condition group, this creates a general deny rule that matches everyone. The users who have been assigned the sales role match the first rule that is processed. Everyone else matches this general deny rule.
-
Click to close the rule editor, then click to close the .
-
In the Policy List window, click , then click .
-
In the , select the policy, then click .
-
Click .
-
Click the link, then click > .
-
Test the results using the following procedure:
-
Open a new browser, then enter the URL of the Digital Airlines Web site you’ve created.
In this example, it is am3bc.provo.novell.com.
-
Log in as the admin user.
-
Add /sales to the URL.
You should receive the following response window with the message derived from the Access Gateway you just configured:

Now, only users with an assigned Sales role can access the Sales page.
-
-
Test the results with a user who has the Sales role.
-
Open a new browser, then enter the URL of the Digital Airlines Web site you’ve created.
In this example, it is am3bc.provo.novell.com.
-
Log in as Tom.
-
Click the button or add /sales to the URL.
The Sales page is displayed.
-
Close all sessions of the browser.
-
-
Continue with Section 7.4.4, Configuring an Identity Injection Policy for Basic Authentication.
7.4.4 Configuring an Identity Injection Policy for Basic Authentication
A common way to protect Web resources is to configure the Web server to require basic authentication for accessing a resource. The Web is configured to check for the user’s name and password in the HTTP authentication header. If you have Web resources with this type of configuration, you can enable single sign-on to these resources by creating a policy that injects the username and password into the HTTP authentication header.
This section explains how to set up the /sales directory to require basic authentication, and then how to create the Identity Injection policy.
Configuring the Web Server for Basic Authentication
It is difficult to create a configuration on the Apache Web server that provides consistent results by using LDAP SSL for basic authentication. Because this is a tutorial and is expected to be implemented in a testing environment, the following steps explain how to configure Apache to allow for a clear text password over LDAP and how to configure basic authentication in this environment. The purpose behind this section is not to explain how to configure Apache, but to explain how you can enable single sign-on for Web resources that require basic authentication.
Enabling LDAP Clear Text Passwords
To turn off the SSL requirement on the internal LDAP user store:
-
Log in to the Administration Console.
-
Click the icon
 in the top menu bar.
in the top menu bar.
-
Expand the novell container.
-
Browse to the LDAP Group - <your server name> object, click the link, then select .
-
Select the attribute, then click .
-
Select the check box, then click .
-
Click or at the bottom of the page.
If you do not click one of these buttons, your modifications are not saved.
-
To return the Administration Console machine to its default view, click the icon in the top menu bar.
-
From a terminal window on the Administration Console machine, log in as root.
-
Restart eDirectory with the following command:
/etc/init.d/ndsd restart
Enabling Basic Authentication
You need to enable the Apache server to require basic authentication for the /sales directory. The procedure depends upon whether your Web server is installed on SLES 9.x or SLEX 10.x:
Configuring the Apache Server on SLES 10.x for Basic Authentication
On SLES 10.x, you need to enable two authentication modules and modify an Apache configuration file.
-
At the Apache server machine, log in to YaST.
-
Click > > .
-
Scroll down, then enable the and modules.
-
Click .
-
In a text editor, open the /etc/apache2/httpd.conf file.
-
Add the following section to the end of the file:
<Directory "/srv/www/htdocs/sales"> Options Indexes FollowSymLinks AllowOverride None order allow,deny allow from all AuthType Basic AuthName Internal AuthBasicAuthoritative off AuthBasicProvider ldap AuthzLDAPAuthoritative off AuthLDAPURL ldap://127.0.0.1/o=novell?uid??(objectclass=*) require valid-user AuthLDAPBindDN cn=admin,o=novell AuthLDAPBindPassword novell </Directory>
Replace the information in the AuthLDAPURL line with the information the IP address of your LDAP user store. Modify the query string to match your user store. This sample line assumes that the Web server and your LDAP user store are installed on the Administration Console, and 127.0.0.1 is its internal address.
The AuthLDAPBindDN and AuthLDAPBindPassword contain the distinguished name of a user and that user’s password. This user needs sufficient rights to log in to the LDAP user store and to search for the users in the tree.
-
Restart the Apache server with the following command:
/etc/init.d/apache2 restart
-
To test that the /sales directory now requires basic authentication:
-
Open a new browser, then enter the URL of the Digital Airlines Web site you’ve created.
In this example, it is am3bc.provo.novell.com.
-
Log in using the credentials for Tom.
Even though Tom has logged in and been assigned the correct role, he is prompted to log in again to access the /sales directory. To enable single-sign on, you must create an Identity Injection policy that injects Tom’s credentials into the authentication header.
-
-
Continue with Creating an Identity Injection Policy for Basic Authentication.
Configuring the Apache Server on SLES 9.x for Basic Authentication
On SLES 9.x, you need to modify an Apache configuration file.
-
At the Apache server machine, add the following section to the end of the /etc/apache2/httpd.conf file:
LoadModule ldap_module /usr/lib/apache2/mod_ldap.so LoadModule auth_ldap_module /usr/lib/apache2/mod_auth_ldap.so <Directory "/srv/www/htdocs/sales/"> AuthType Basic AuthName "Sales" AuthLDAPURL ldap://127.0.0.1/o=novell?uid?sub AuthLDAPBindDN "cn=admin,o=novell" AuthLDAPBindPassword "novell" require valid-user </Directory>
The AuthLDAPURL line is configured for the internal IP address of the Administration Console. If you have installed your Web server on a different machine, replace the 127.0.0.1 address with the IP address of your LDAP user store. In this configuration, this is the IP address of the Administration Console because we are using the internal configuration store as the LDAP user store.
The AuthLDAPBindDN and AuthLDAPBindPassword lines need to contain the DN and password of the administrator for the Administration Console. If you are using a different LDAP user store, make sure the search context (o=novell), the DN of the admin user, and the password are correct for your LDAP user store.
-
Restart the Apache server with the following command:
/etc/init.d/apache2 restart
-
To test that the /sales directory now requires basic authentication:
-
Open a new browser, then enter the URL of the Digital Airlines Web site you’ve created.
In this example, it is am3bc.provo.novell.com.
-
Log in using the credentials for Tom.
Even though Tom has logged in and been assigned the correct role, he is prompted to log in again to access the /sales directory. To enable single-sign on, you must create an Identity Injection policy that injects Tom’s credentials into the authentication header.
-
-
Continue with Creating an Identity Injection Policy for Basic Authentication.
Creating an Identity Injection Policy for Basic Authentication
This section explains how to enable single-sign by creating an Identity Injection policy that injects the user’s authentication credentials into a header. The Web server uses the credentials in the authentication header to satisfy its login requirements.
-
In the Administration Console, click > > > > > .
-
In the , click .
-
Click > > .
-
For the new policy, fill in the following fields:
Name: Specify II_of_Credentials for the name.
Type: Select for the type.
-
Click .
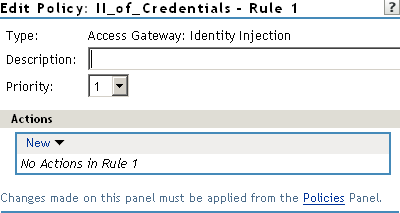
The Edit Policy page opens so you can create a rule for the policy.
-
Click , select , then select the following values:
User Name: Select . The value is automatically selected for you. This credential is the cn attribute of the user.
Password: Select . Click , then select .
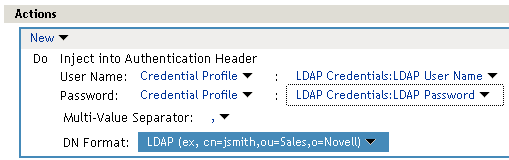
Your policy should look similar to the following:
-
Click to close the policy editing page, then click to close the Rule List page.
-
In the Policy List page, click , then click .
-
Select the check box, click , then click .
-
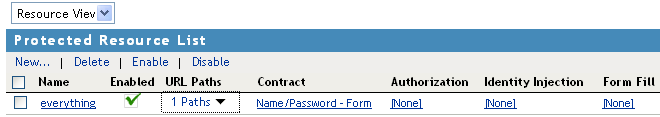
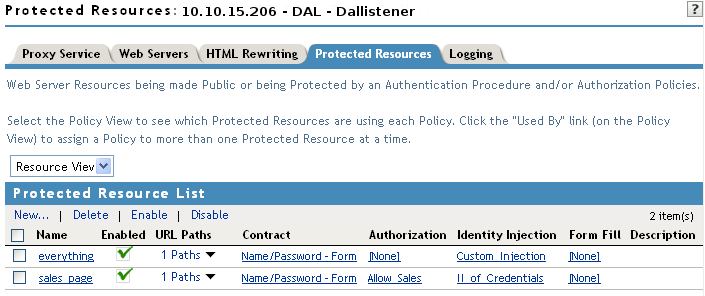
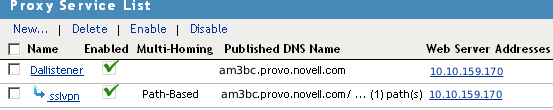
Click to return to the . Your list should look similar to the following:
-
To save your configuration changes, click the link, then click > .
-
To test the configuration:
-
Open a new browser, then enter the URL of the Digital Airlines Web site you’ve created.
In this example, it is am3bc.provo.novell.com.
-
Log in as Tom.
The Digital Airlines site should appear with the button.
-
Click the button. You should have access to the Sales System site, as shown below:
For more information about Identity Injection policies, see
Creating Identity Injection Policies
in the Novell Access Manager 3.0 SP4 Administration Guide. -
Close all sessions of the browser.
-
-
Continue with Section 7.4.5, Initiating an SSL VPN Session.
7.4.5 Initiating an SSL VPN Session
This section explains how to initiate an SSL Virtual Private Network (VPN) connection in the Digital Airlines example. The SSL VPN agent provides secure access to non-HTTP applications.
Figure 7-4 GUI Button to Initiate an SSL VPN Session

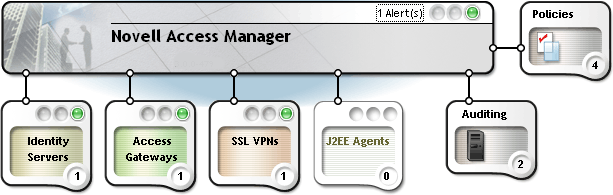
Before performing this task, you must have the SSL VPN agent installed on either your Identity Server or on your Linux Access Gateway. Your Access Manager console should appear similar to the green state shown in Figure 7-5:
Figure 7-5 Access Console Indicating the Status of Access Manager Components
For more information about installing the SSL VPN server, see Installing SSL VPN
in the Novell Access Manager 3.0 SP4 Installation Guide.
For the Digital Airlines example, you will perform the following tasks:
Configuring the SSL VPN as a Protected Resource
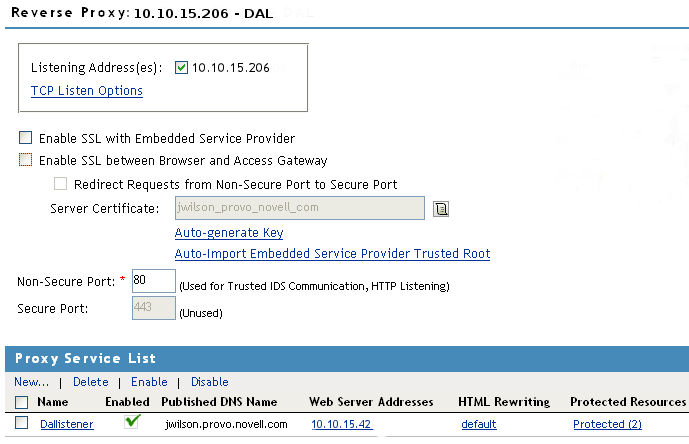
To configure the SSL VPN as protected resource, you must first create a reverse proxy for it.
-
In the Administration Console, click > > > .
-
In the , click , then provide the following values:
Proxy Service Name: Specify .
Multi-Homing Type: Select . (For more information about accessing multiple resources, see
Using Multi-Homing to Access Multiple Resources
in the Novell Access Manager 3.0 SP4 Administration Guide.)Path: Specify /sslvpn.
Web Server IP Address: Specify the IP address of SSL VPN server.
Host Header: If your SSL VPN server has a DNS name, select . Otherwise, select .
Web Server Host Name: Specify the DNS name of the SSL VPN server if you selected for the option.
-
Click .
The Reverse Proxy window is displayed.
-
In the , click > .
-
Change the from 80 to 8080, then click .
-
Continue with Creating an SSL VPN Protected Resource and Identity Injection Policy.
Creating an SSL VPN Protected Resource and Identity Injection Policy
-
In the , select the .
-
In the , select the check box, then click .
-
Fill in the following fields:
Policy Container: Select Master_Container.
Policy: Select . In the Policy List window, click , then click .
Name: Select .
Your configuration should look like the following:
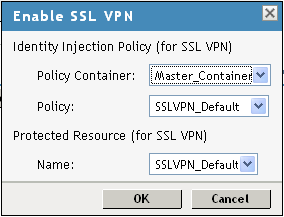
-
Click .
The option creates a protected resource, creates a default SSL VPN identity injection policy, then assigns it to the protected resource. When it completes, the / Path should now indicate as the Protected Resource.
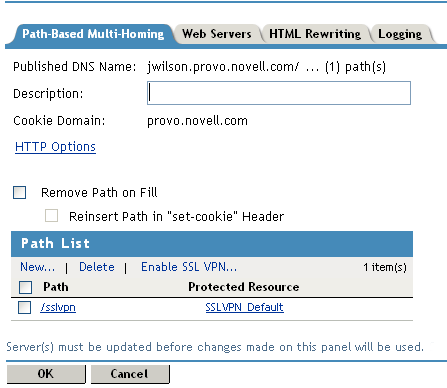
-
Click .
-
Click the link, then click > .
Testing the SSL VPN Basic Configuration
Basic configuration of the SSL VPN is complete after it is protected behind your gateway and you have built your necessary identity injection policies. Test your basic configuration with the following procedure:
-
To access the SSL VPN servlet, open a new browser and enter
-
Log in with any authorized username and password that is registered within your corporate domain, including the user you created in Creating a New User with a Sales Role.
-
Click the link.
-
If requested, click to accept the certificate for the SSL VPN client.
-
Verify that the SSL VPN client downloads, installs, and runs:
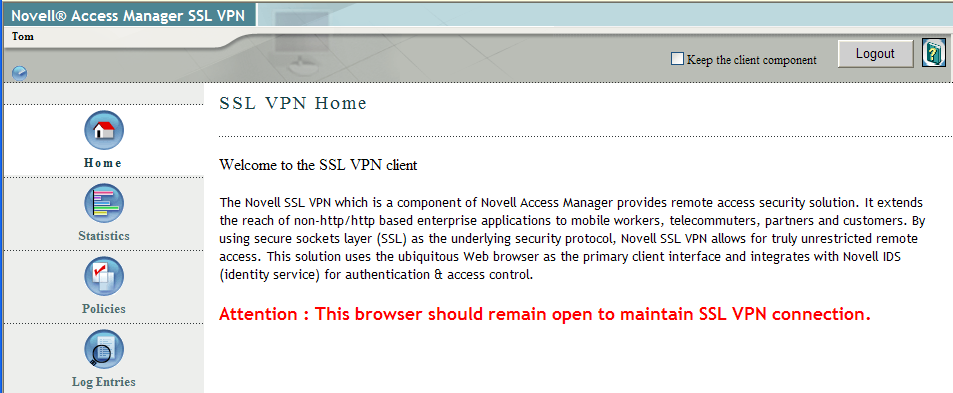
Notice that the user’s first name (“Tom”) is injected into the header of the SSL VPN browser.
-
Click , then close the browser.
Configuring a Traffic Policy
Traffic policies allow you to control access to different networks and applications protected behind the SSL VPN. Simulate this by creating a rule that allows access to your network:
-
In the Administration Console, click > > > .

-
Click , type , then click .
-
In the Traffic Policies list, select the check box, then click .
-
Click the new, enabled sales policy, then provide the following values:
Role: . Specify this value in the field after clicking the icon.
Destination Network: 10.0.0.0. This field is usually prepopulated, or you can specify the IP address of the SSL network.
Network Mask: 255.0.0.0. This field is usually prepopulated, or you can specify the value for your destination network.
Predefined Application: You can also select from drop-down list to specify your network application.
Name: Protected Network. You can also provide any descriptive name for the SSL network.
Protocol: Any. Specifies whether the protocol is, , , or .
Port: Port. Specifies the port number on which the service you select listens. The value of 0 allows all ports.
Action: . Specifies whether the service can be encrypted or denied.

-
Click to save the configuration and return to the List of Traffic Policies page.
-
Click twice, then on the SSL VPNs page, click .
-
Test the traffic rule:
-
Open a new browser session and enter http://am3bc.provo.novell.com/sslvpn/login.
-
Log in as admin user of the Administration Console.
-
In the left navigation window, click .
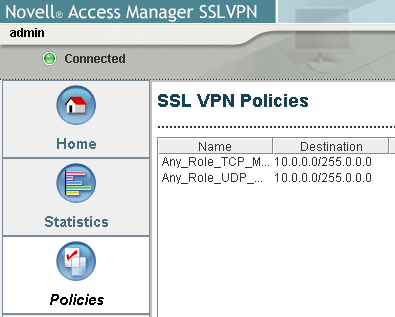
Notice that without a sales role, the admin user has no access to the Digital Airlines network. Access is granted only when you log in with your sales credentials created in Creating a New User with a Sales Role.
-
Log out of the SSL VPN session.
-
Open a new SSL VPN browser session and enter http://am3bc.provo.novell.com/sslvpn/login.
-
Log in as Tom. (See Creating a New User with a Sales Role.)
-
In the left navigation window, click .
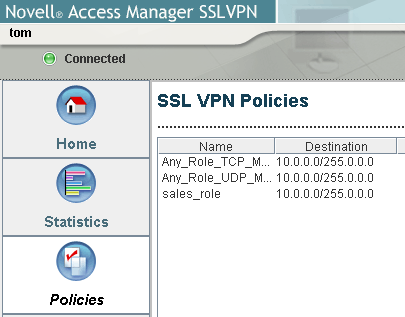
Notice that the user “” is now assigned a on the SSL VPN server.
-
For more information about Traffic Policies, see Configuring Traffic Policies
in the Novell Access Manager 3.0 SP4 Administration Guide.