3.8 Specifying Configuration Information
When the server reboots, you are required to complete the following configuration information:
3.8.1 Specifying the Password for the System Administrator “root”
In the Password for the System Administrator root page:
-
Specify the password for the root administrator.
For security reasons, the root user’s password should be at least five characters long and should contain a mixture of both uppercase and lowercase letters and numbers. Passwords are case sensitive.
The default password length limit is 8 characters. The maximum possible length for passwords is 72 characters. If you have a password longer than eight characters, click Expert Options > Blowfish > OK.
-
Confirm the password.
-
Click Next.
3.8.2 Specifying the Hostname and Domain Name
On the Hostname and Domain Name page:
-
Specify the hostname associated with the IP address you have or will assign to the server.
-
Specify the domain name for the server.
-
Deselect Change Hostname via DHCP.
-
Click Next.
3.8.3 Specifying Network Configuration Settings
On the Network Configuration page, you can change the configuration for the following, most of which do not apply in an OES server installation scenario:
-
Network Mode
-
Firewall
-
IPv6
-
Network Interfaces
-
DSL Connections
-
ISDN Adapters
-
Modems
-
VNC Remote Administration
-
Proxy
In this section, we provide details only for the components that apply to OES servers.
Network Interface
Configuration success is directly tied to specific networking configuration requirements. Ensure that the settings covered in the steps that follow are configured exactly as specified.
Specify the setting for each network board on the server:
-
On the Network Configuration page, click Network Interfaces.
-
On the Network Card Configuration Overview page, select the network card you want to configure, then click Edit.
-
Select Static Address Setup, then specify the IP address and the subnet mask for the interface.
OES requires a static IP address.
-
In the Detailed Settings list, select Hostname and Name Server.
-
In the Name Servers and Domain Search List panel, specify from one to three DNS server IP addresses.
-
Click OK to return to the Detailed Settings list.
-
-
In the Detailed Settings list, select Routing.
-
Specify the IP address of the default gateway on the subnet where you are installing the OES server.
-
Click OK to return to the Detailed Settings list.
-
-
Click Next to return to the Network Card Configuration Overview page.
-
Complete Step 2 through Step 6 for each network board, then click Next to return to the main Network Configuration page.
Firewall
For security reasons, a firewall is started automatically on each configured interface. The configuration proposal for the firewall is updated automatically every time the configuration of the interfaces or services is modified.
Many of the OES services require an open port in the firewall. Table 3-2 shows the ports that are automatically opened when each listed OES service is configured.
Table 3-2 Open Enterprise Server Services and Ports
|
Service |
Default Ports |
|---|---|
|
Domain Services for Windows |
|
|
NetIQ eDirectory |
|
|
iManager |
|
|
iPrint |
|
|
Novell AFP |
|
|
Novell Archive and Version Services |
|
|
Novell CIFS |
|
|
Novell DHCP |
|
|
Novell DNS |
|
|
Novell FTP |
|
|
Novell Information Portal |
|
|
Novell NetWare Core Protocol (NCP) |
|
|
Novell Remote Manager |
|
|
SFCB |
|
|
QuickFinder |
|
|
Samba |
|
|
Secure Shell |
|
|
Storage Management Services (Backup) |
|
|
Time Synchronization |
|
To adapt the automatic settings to your own preferences:
-
Click Change > Firewall.
-
In the left panel, select the settings you want to change, then make the changes in the right panel.
-
When you are finished, click Accept.
For more information about the firewall, see “Configuring the Firewall with YaST” in the SUSE Linux Enterprise Server 11 Security Guide.
To disable the firewall:
-
On the Network Configuration page, under Firewall, click enabled on the Firewall is enabled status line.
When the firewall is disabled, the status for Firewall should read Firewall is disabled.
-
Verify that the settings on the Network Configuration page are set as desired, then click Next to save the configuration. Continue with Testing the Connection to the Internet.
3.8.4 Testing the Connection to the Internet
On the Test Internet Connection page:
-
Select Yes, Test Connection to the Internet, then click Next.
Obtaining the latest SUSE release notes might fail at this point. If it does, view the log to verify that the network configuration is correct, then click Next.
If the network configuration is not correct, click Back > Back and fix your network configuration. See Network Interface.
IMPORTANT:Do not skip this test. For a successful install, you must configure the Novell Customer Center and update SLES 11 SP4 from the patch repository before configuring OES services.
-
Continue with Specifying Novell Customer Center Configuration Settings.
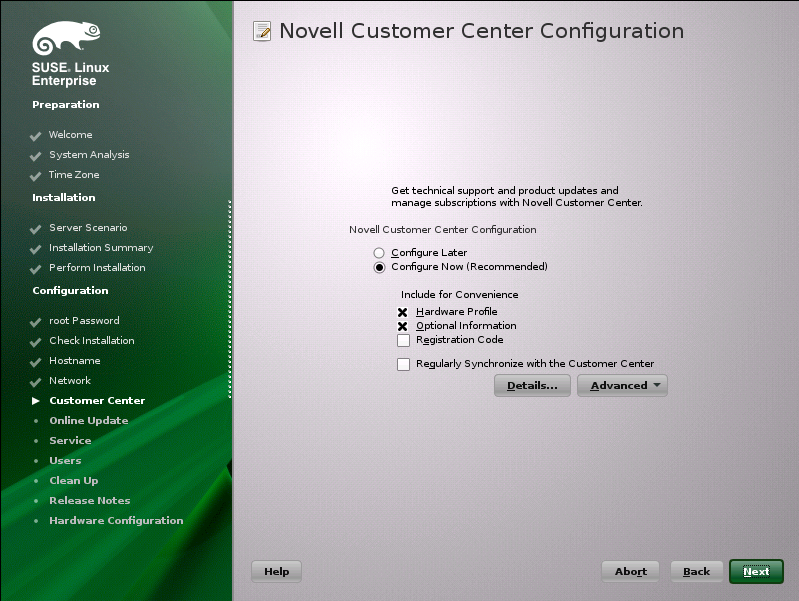
3.8.5 Specifying Novell Customer Center Configuration Settings
OES 11 SP3 requires that the SLES 11 SP4 base be updated prior to installing and configuring OES 11 SP3 services. If not, some OES services, such as Novell FTP, will not function properly after the installation and will need to be configured again after the SLES patches are applied.
Therefore, when you are entering the Novell Customer Center configuration information, it is critical that you enter either your purchased SLES 11 SP4 code or the 60-day evaluation code available with your SLES 11 SP4 download.
-
On the Novell Customer Center Configuration configuration page, select all of the following options, then click Next.
Option
What it Does
Configure Now
Proceeds with registering this server and the SLES 11 SP4 and OES 11 SP3 product in the Novell Customer center.
Hardware Profile
Sends the information to the Novell Customer Center about the hardware that you are installing SLES 11 SP4 and OES 11 SP3 on.
Optional Information
Sends optional information to the Novell Customer Center for your registration. For this release, this option doesn’t send any additional information.
Registration Code
Makes the registration with activation codes mandatory.
Regularly Synchronize with the Customer Center
Keeps the installation sources for this server valid. It does not remove any installation sources that were manually added.
-
After you click Next, the following message is displayed.
Wait until this message disappears and the Manual Interaction Required page displays.
-
On the Manual Interaction Required page, note the information that you will be required to specify, then click Continue.
-
On the Novell Customer Center Registration page, specify the required information in the following fields, then click Submit:
Field
Information to Specify
Email Address
The email address for your Novell Login account.
Confirm Email Address
The same email address for your Novell Login account
SUSE Linux Enterprise Server 11 SP4 (optional)
Specify your purchased or 60-day evaluation registration code for the SLES 11 SP4 product.
If you don’t specify a code, the server cannot receive any updates or patches.
Open Enterprise Server 11 SP3 (optional)
Specify your purchased or 60-day evaluation registration code for the OES 11 SP3 product.
If you don’t specify a code, the server cannot receive any updates or patches.
System Name or Description (optional):
Specify a description to identify this server.
-
When the message to complete the registration displays, click Continue.
-
After you click Continue, the following message is displayed with the Manual Interaction Required screen.
Wait until this message disappears and the Novell Customer Center Configuration page displays.
-
Select Configure Now to download any updates that are available for the server, then click Next.
-
Continue with Updating the Server Software.
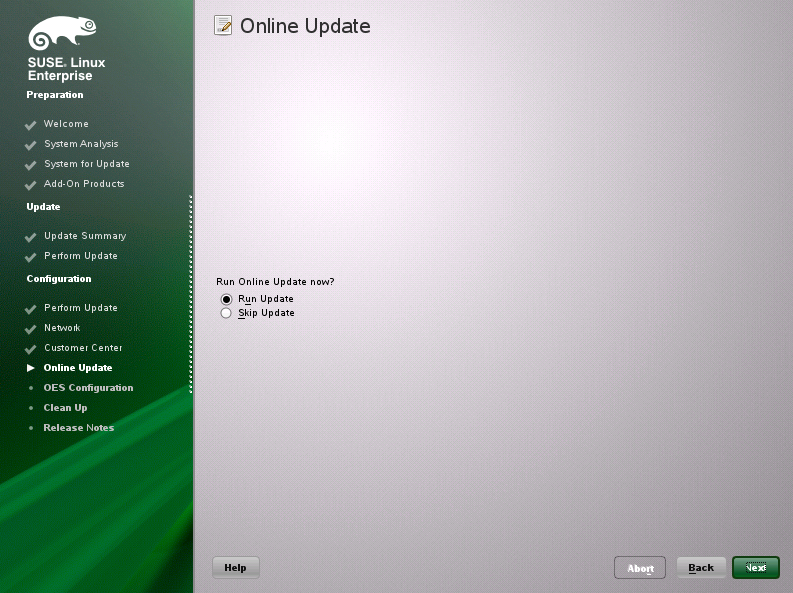
3.8.6 Updating the Server Software
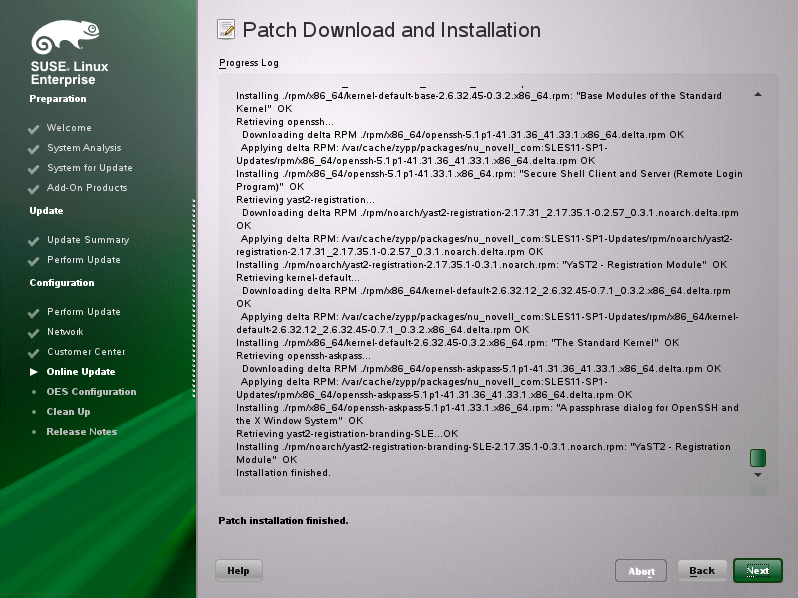
When you have a successful connection to the Internet and have registered the server in the Novell Customer Center, the server displays the Online Update page. You must run the online update now for a successful OES installation.
-
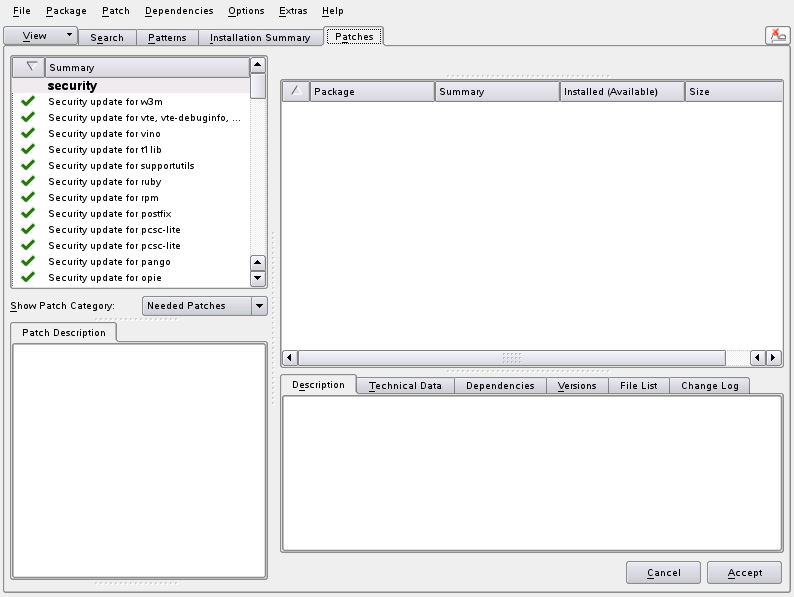
On the Online Updates page, click Run Update > Next.
-
On the page that shows that updates are available, click Accept.
The check marks that are shown on the summary portion of the page are the patches that will be installed on your system after clicking Accept.
-
When you see the following message, click Next.
-
In the pop-up that informs you about the kernel update, click OK.
The system reboots before continuing the installation.
-
Continue with Specifying Service Configuration Settings.
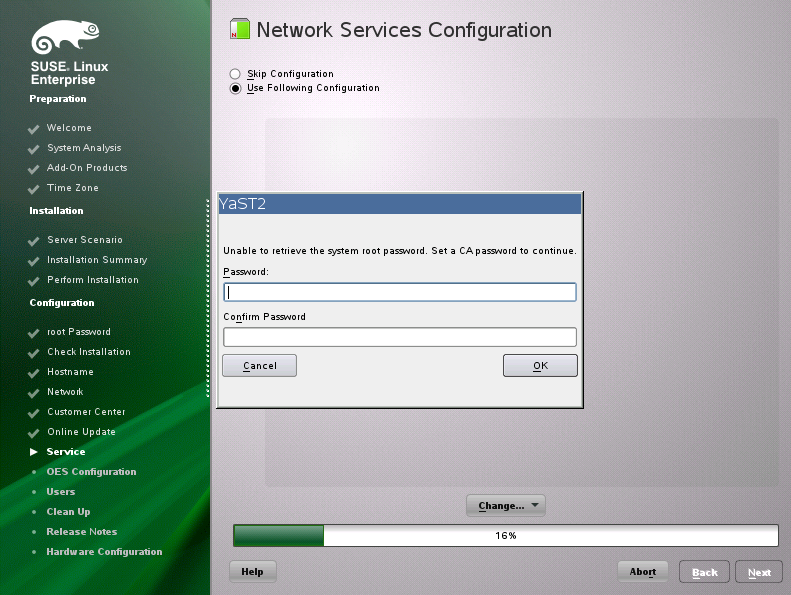
3.8.7 Specifying Service Configuration Settings
Because the server was rebooted during the installation, the default settings for CA management lost the root password as indicated by the red text under CA Management.
-
Reset the password for root.
-
Observe the settings on the Installation Settings page.
-
CA Management: This indicates the certificate that is used by the Apache web server if another certificate is not specified.
By default, OES creates and installs a replacement eDirectory certificate later in the installation process. We recommend that you accept the eDirectory certificate option because it is much more secure than the certificate that is proposed.
Alternatively, you can install a third-party certificate.
In all cases, do not disable the configuration at this point because the services that use Apache will not work if you do.
For more information about OES certificate management, see
Certificate Management
in the OES 11 SP3: Planning and Implementation Guide. -
OpenLDAP Server: Do not enable this option. On OES servers, NetIQ eDirectory LDAP server replaces the SLES 11 SP4 OpenLDAP server.
-
-
If you are not installing a third-party certificate, click Next.
or
If you are installing a third-party certificate, click CA Management and refer to the information about Certificate Authority Management on SLES. See in the “Managing X.509 Certification” in the SUSE LINUX Enterprise Server 11 Security Guide. Then return to these instructions to continue your OES installation.
-
If you did not select the NetIQ eDirectory pattern for this server, continue with Specifying LDAP Configuration Settings.
Otherwise, skip the next section and continue with Specifying eDirectory Configuration Settings.
3.8.8 Typical and Custom OES Configuration
Beginning with OES 11 SP3, you can configure OES in two methods: Typical Configuration and Custom Configuration. The Typical Configuration is also called as Express Install. It helps to install OES 11 SP3 with minimal user intervention and the Custom Configuration is the detailed usual method to configure OES.
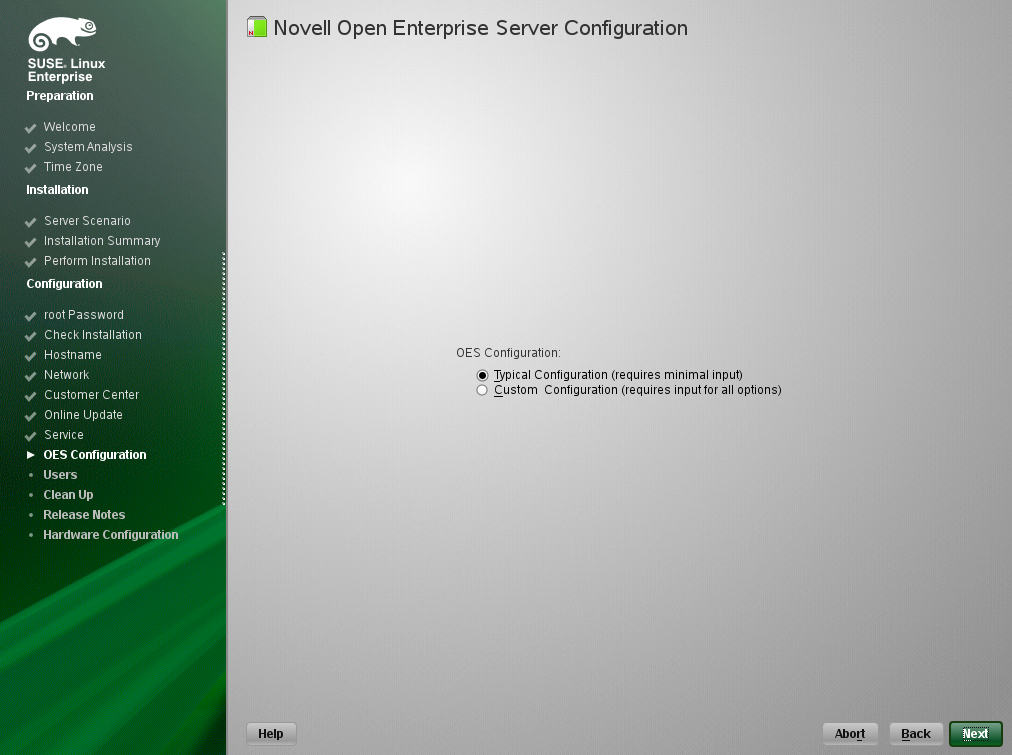
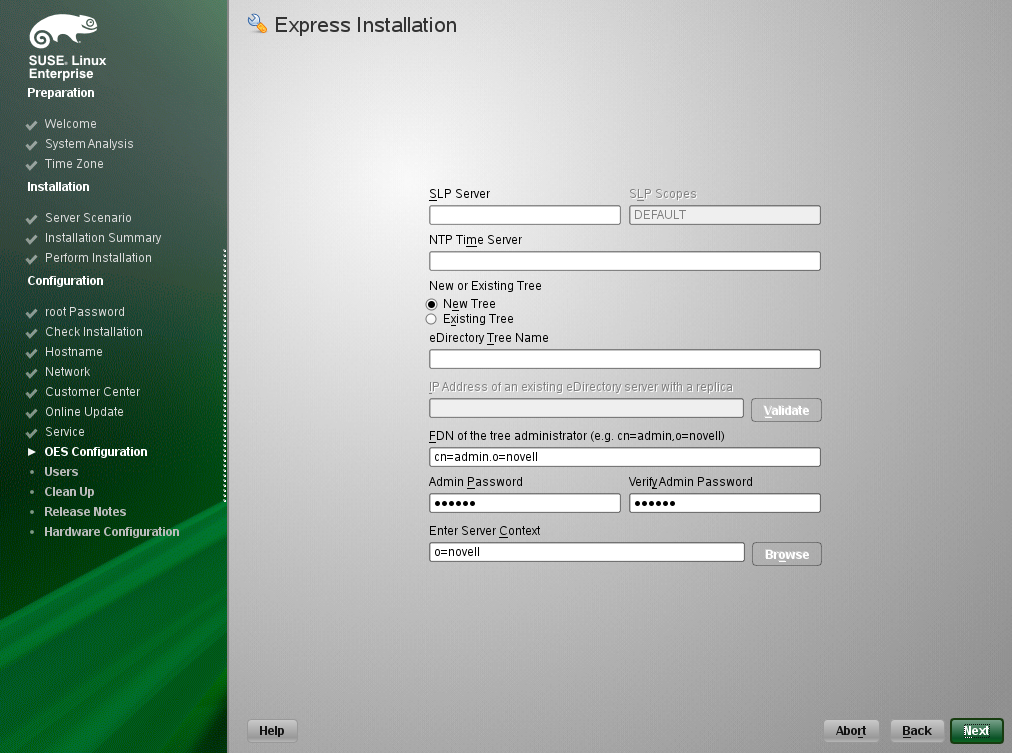
Typical Configuration
In the OES Configuration screen, if you have chosen to configure OES using Typical Configuration, you only need to provide the following minimum configuration details:
-
SLP Server and SLP Scopes: In these fields, specify the host name or the IP address of the server where the SLP agent is running and the SLP scopes. If you don't enter any SLP details, multicast SLP mode is chosen by default.
NOTE:If you would like to use the current server as the DA server, click Back and choose the custom configuration instead of typical configuration.
-
NTP Time Server: Specify the IP address or the host name of the Network Time Protocol (NTP) server.
-
New or Existing Tree: If you would like to configure OES using an existing eDirectory tree, choose Existing Tree else New Tree.
-
eDirectory Tree Name: Provide the eDirectory tree name.
-
IP Address of an existing eDirectory Server with a replica: If you have chosen to configure OES using an existing tree, this field is enabled to provide the IP address of an existing eDirectory serer.
IMPORTANT:Ensure that you verify the status of the eDirectory tree using the Validate button. If the validation is unsuccessful, do not proceed further with the OES configuration until the eDirectory server is up and running.
-
FDN of the tree administrator: Specify the fully distinguished name of the administrative user.
-
Admin Password and Verify the Admin Password: In these two fields, specify the eDirectory administrative passwords.
-
Enter Server Context: Specify the location of the server context in the eDirectory tree.
-
After providing all these details, click Next. OES will be installed and configured without any user intervention.
Custom Configuration
This is the normal method of installing and configuring OES by providing every configuration detail that OES requires instead of using the default configuration details. Custom configuration is explained in detailed in Section 3.8.9, Specifying LDAP Configuration Settings, Section 3.8.10, Specifying eDirectory Configuration Settings, Section 3.8.11, Configuring OES Services, and Section 3.8.12, Configuration Guidelines for OES Services.
3.8.9 Specifying LDAP Configuration Settings
Many of the OES services require eDirectory. If eDirectory was not selected as a product to install on this server but other OES services that do require LDAP services were installed, the LDAP Configuration service displays, so that you can complete the required information.
To specify the required information on the Configured LDAP Server page:
-
In the eDirectory Tree Name field, specify the name for the existing eDirectory tree that you are installing this server into.
-
In the Admin Name and Context field, specify the name and context for user Admin in the existing tree.
-
In the Admin Password Name field, specify a password for the Admin user in the existing tree.
-
Add the LDAP servers that you want the services on this server to use. The servers that you add should hold the master or a read/write replica of eDirectory. Do the following for each server you want to add:
-
Click Add.
-
On the next page, specify the following information for the server to add, then click Add.
-
IP address
-
LDAP port and secure LDAP port
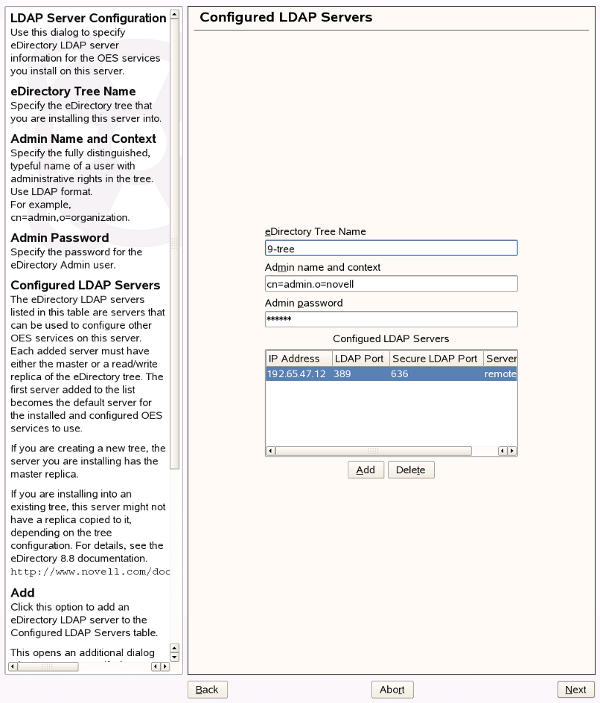
-
-
-
When all of the LDAP servers that you want to specify are listed, click Next.
-
Verify that the Novell Open Enterprise Server Configuration page displays the settings that you expected, then click Next.
-
Continue with Configuring OES Services.
3.8.10 Specifying eDirectory Configuration Settings
When you specify the eDirectory configuration settings, you can specify information to create a new tree and install the server in that new tree, or you can install the server into an existing tree by specifying the information for it. Use the following instructions as applicable:
Specifying SLP Configuration Options
-
On the eDirectory Configuration - SLP page, specify the SLP options as desired.
You have the following options for configuring SLP:
-
Use Multicast to Access SLP: This option allows the server to request SLP information by using multicast packets. Use this in environments that have not established SLP DAs (Directory Agents).
IMPORTANT:If you select this option, you must disable the firewall for SLP to work correctly. Multicast creates a significant amount of network traffic and can reduce network throughput.
-
Configure SLP to use an existing Directory Agent: This option configures SLP to use an existing Directory Agent (DA) in your network. Use this in environments that have established SLP DAs. When you select this option, you configure the servers to use by adding or removing them from the SLP Directory Agent list.
-
Configure as Directory Agent: This option configures this server as a Directory Agent (DA). This is useful if you plan to have more than three servers in the tree and want to set up SLP during the installation.
-
DASyncReg: This option causes SLP, when it starts, to query the Directory Agents listed under Configured SLP Directory Agents for their current lists of registered services. It also causes the DA to share service registrations that it receives with the other DAs in the SLP Directory Agent list.
-
Backup SLP Registrations: This option causes SLP to back up the list of services that are registered with this Directory Agent on the local disk.
-
Backup Interval in Seconds: This specifies how often the list of registered services is backed up.
-
-
Service Location Protocols and Scope: This option configures the scopes that a user agent (UA) or service agent (SA) is allowed when making requests or when registering services, or specifies the scopes a directory agent (DA) must support. The default value is DEFAULT. Use commas to separate each scope. For example, net.slp.useScopes = myScope1,myScope2,myScope3.
-
Configured SLP Directory Agents: This option lets you manage the list of hostname or IP addresses of one or more external servers on which an SLP Directory Agent is running.
-
-
Click Next and confirm your selection if necessary, then continue with Selecting the NetIQ Modular Authentication Services (NMAS) Login Method.
Specifying Synchronizing Server Time Options
eDirectory requires that all OES servers are time-synchronized.
-
On the eDirectory Configuration - NTP page, click Add.
-
In the Time Server text box, specify the IP address or DNS hostname of an NTP server, then click Add.
For the first server in a tree, we recommend specifying a reliable external time source.
When you install multiple servers into the same eDirectory tree, ensure that all servers point to the same time source and not to the server holding the master replica.
For servers joining a tree, specify the same external NTP time source that the tree is using, or specify the IP address of a configured time source in the tree. A time source in the tree should be running time services for 15 minutes or more before connecting to it; otherwise, the time synchronization request for the installation fails.
-
If you want to use the server’s hardware clock, select Use Local Clock.
For servers joining a tree, the installation does not let you proceed if you select this option. You must specify the same external NTP time source that the tree is using, or specify the IP address of a configured time source in the tree that has been running time services for 15 minutes or more.
-
Continue with Specifying SLP Configuration Options.
For more information on time synchronization, see Implementing Time Synchronization
in the OES 11 SP3: Planning and Implementation Guide.
Creating a New eDirectory Tree and Installing the Server in It
-
On the eDirectory Configuration - New or Existing Tree page, select New Tree.
-
In the eDirectory Tree Name field, specify a name for the eDirectory tree that you want to create.
On OES servers, services that provide HTTPS connectivity are configured to use one of the following certificates:
-
An eDirectory certificate issued by the Novell International Cryptographic Infrastructure (NICI)
-
A third-party server certificate
-
The YaST self-signed common server certificate created in Step 2
Self-signed certificates provide minimal security and limited trust. Unless you have invested in a third-party certificate, we recommend that you use the eDirectory certificates instead.
By default, the Use eDirectory Certificates for HTTPS Services check box is selected. This means that the existing server certificate and key files (YaST or third-party) will be replaced with eDirectory server certificate and key files.
The default YaST server certificate and key files are:
-
Key file: /etc/ssl/servercerts/serverkey.pem
-
Certificate file: /etc/ssl/servercerts/servercert.pem
The eDirectory server certificate and key files are:
-
Key file: /etc/ssl/servercerts/eDirkey.pem
-
Certificate file: /etc/ssl/servercerts/eDircert.pem
For more information, see
Certificate Management
in the OES 11 SP3: Planning and Implementation Guide. -
-
On the eDirectory Configuration - New Tree Information page, specify the required information:
-
The fully distinguished name and context for the user Admin on the existing server
-
The password for user Admin on the existing server
-
-
Click Next.
-
On the eDirectory Configuration - Local Server Configuration page, specify the following information:
-
The context for the server object in the eDirectory tree
-
A location for the eDirectory database
The default path is /var/opt/novell/eDirectory/data/dib, but you can use this option to change the location if you expect to have a large number of objects in your tree and if the current file system does not have sufficient space.
-
The ports to use for servicing LDAP requests
The default ports are 389 (non-secure) and 636 (secure).
IMPORTANT:The scripts that manage the common proxy user introduced in OES 11 SP3 require port 636 for secure LDAP communications.
-
The ports to use for providing access to the iMonitor application
The default ports are 8028 (non-secure) and 8030 (secure).
-
-
Click Next. Then continue with Specifying Synchronizing Server Time Options.
Installing the Server into an Existing eDirectory Tree
-
On the eDirectory Configuration - New or Existing Tree page, select Existing Tree.
-
In the eDirectory Tree Name field, specify a name for the eDirectory tree you want to join.
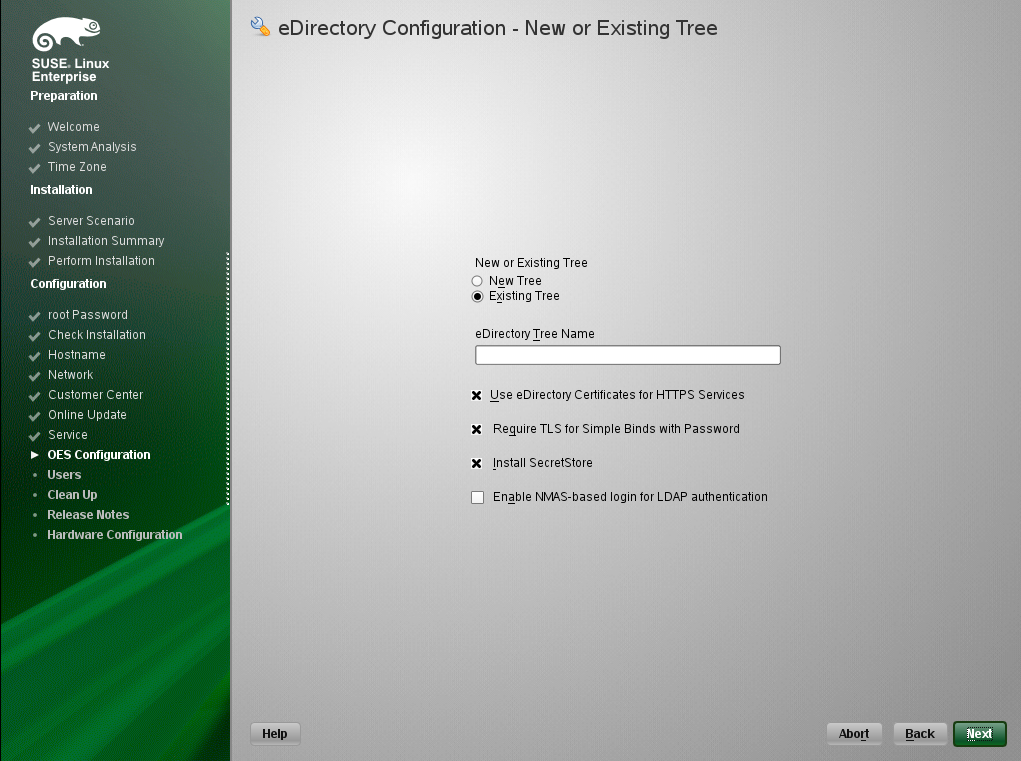
On OES servers, services that provide HTTPS connectivity are configured to use either of the following:
-
An eDirectory certificate issued by the Novell International Cryptographic Infrastructure (NICI)
-
The YaST self-signed common server certificate created in Step 2
Self-signed certificates provide minimal security and limited trust. We recommend that you use the eDirectory certificates instead.
By default, the Use eDirectory Certificates for HTTPS Services check box is selected. This means that the existing YaST server certificate and key files will be replaced with eDirectory server certificate and key files.
The default YaST server certificate and key files are:
-
Key file: /etc/ssl/servercerts/serverkey.pem
-
Certificate file: /etc/ssl/servercerts/servercert.pem
The eDirectory server certificate and key files are:
-
Key file: /etc/ssl/servercerts/eDirkey.pem
-
Certificate file: /etc/ssl/servercerts/eDircert.pem
For more information on certificate management, see
Certificate Management
in the OES 11 SP3: Planning and Implementation Guide.-
Select Enable NMAS-based login for LDAP authentication to enforce the use of a single-secure password for all Novell and partner products. The Secure Password Manager of the NMAS module manages this universal password implementation.
-
-
On the eDirectory Configuration - Existing Tree Information page, specify the required information:
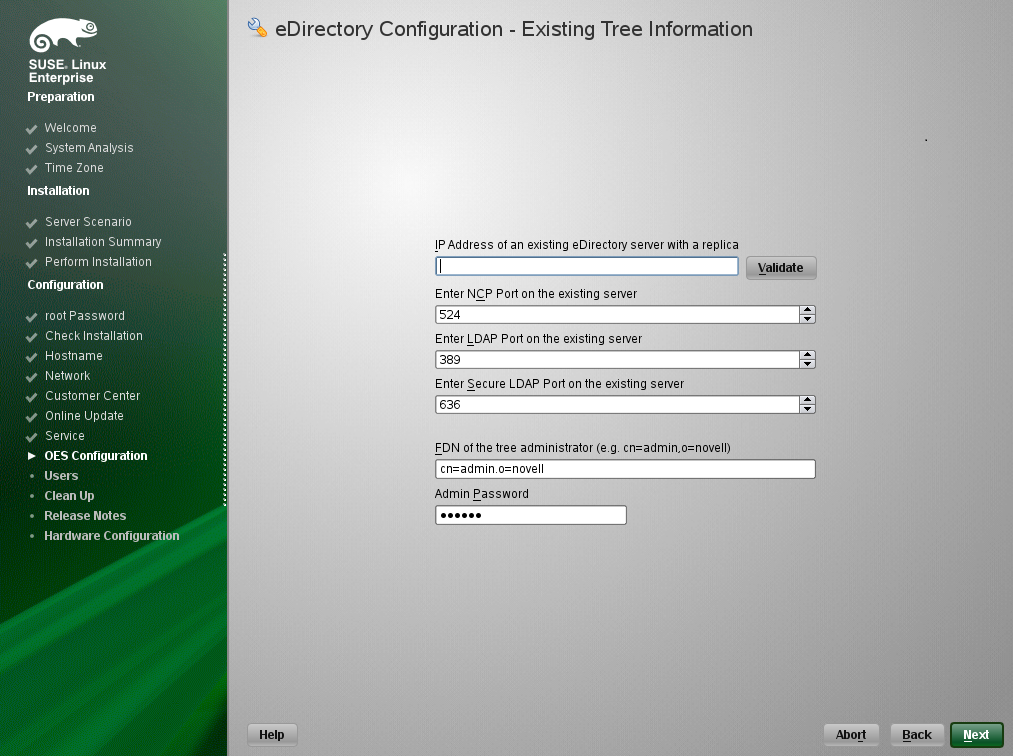
-
The IP address of an existing eDirectory server with a replica.
IMPORTANT:Ensure that you verify the status of the eDirectory tree using the Validate button. If the validation is unsuccessful, do not proceed further with the OES configuration until the eDirectory server is up and running.
-
The NCP port on the existing server
-
The LDAP and secure LDAP port on the existing server
-
The fully distinguished name and context for the user Admin on the existing server
-
The password for user Admin on the existing server
-
-
Click Next.
-
On the eDirectory Configuration - Local Server Configuration page, specify the following information:
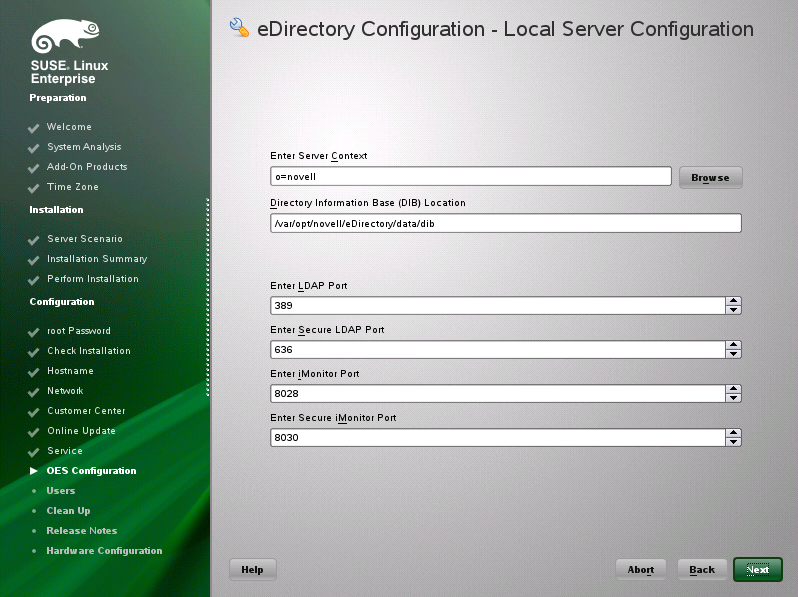
-
The context for the server object in the eDirectory tree
-
A location for the eDirectory database
The default path is /var/opt/novell/eDirectory/data/dib, but you can use this option to change the location if you expect to have a large number of objects in your tree and if the current file system does not have sufficient space.
-
The ports to use for servicing LDAP requests
The default ports are 389 (non-secure) and 636 (secure).
IMPORTANT:The scripts that manage the common proxy user introduced in OES 11 SP3 require port 636 for secure LDAP communications.
-
The ports to use for providing access to the iMonitor application
The default ports are 8028 (non-secure) and 8030 (secure).
-
-
Click Next. Then continue with Specifying Synchronizing Server Time Options.
Selecting the NetIQ Modular Authentication Services (NMAS) Login Method
-
On the NetIQ Modular Authentication Services page, select all of the login methods you want to install.
IMPORTANT:The NMAS client software must be installed on each client workstation where you want to use the NMAS login methods. The NMAS client software is included with the Novell Client software.
The following methods are available:
-
CertMutual: The Certificate Mutual login method implements the Simple Authentication and Security Layer (SASL) EXTERNAL mechanism, which uses SSL certificates to provide client authentication to eDirectory through LDAP.
-
Challenge Response: The Challenge Response login method works with the Identity Manager password self-service process. This method allows either an administrator or a user to define a password challenge question and a response, which are saved in the password policy. Then, when users forget their passwords, they can reset their own passwords by providing the correct response to the challenge question.
-
DIGEST-MD5: The Digest-MD5 login method implements the Simple Authentication and Security Layer (SASL) DIGEST-MD5 mechanism as a means of authenticating the user to eDirectory through LDAP.
-
NDS: The NDS login method provides secure password challenge-response user authentication to eDirectory. This method is installed by default and supports the traditional NDS password when the NMAS client is in use. Reinstallation is necessary only if the NDS login method object has been removed from the directory.
-
Simple Password: The Simple Password NMAS login method provides password authentication to eDirectory. The Simple Password is a more flexible but less secure alternative to the NDS password. Simple Passwords are stored in a secret store on the user object.
-
SASL GSSAPI: The SASL GSSAPI login method implements the Generic Security Services Application Program Interface (GSSAPI) authentication. It uses the Simple Authentication and Security Layer (SASL), which enables users to authenticate to eDirectory through LDAP by using a Kerberos ticket.
For more information about installing and configuring eDirectory, see “Installing or Upgrading NetIQ eDirectory on Linux in the NetIQ eDirectory 8.8 SP8 Installation Guide.
For more information on these login methods, see the online help and
Managing Login and Post-Login Methods and Sequences
in the Novell Modular Authentication Services 3.3.4 Administration Guide. -
-
Click Next. Then continue with Specifying OES Common Proxy User Information.
Specifying OES Common Proxy User Information
For an OES service to run successfully, you need to use a separate proxy account to configure and manage each service. However, using multiple proxy user accounts means more overhead for the administrator. To avoid this overhead, the common proxy user has been introduced. Each node in a tree can have a common proxy user for all of its services. This enables administrators to configure and manage multiple services with just one proxy user.
NOTE:Two nodes in a tree cannot have the same common proxy user.
For information about this option, see Common Proxy User
in the OES 11 SP3: Planning and Implementation Guide.
-
On the OES Common Proxy User Information page, specify the configuration settings for this user, then click Next.
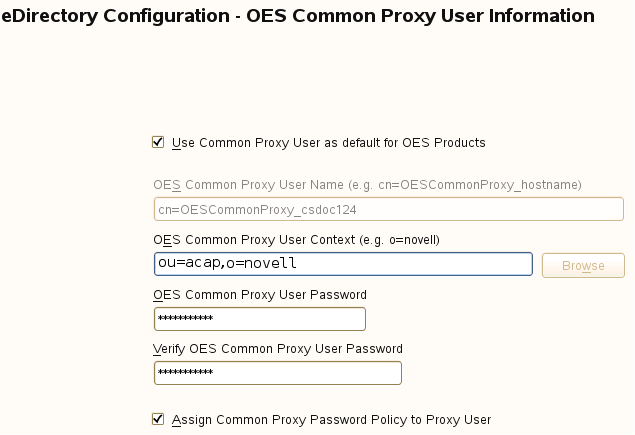
-
Use Common Proxy User as Default for OES Products: Selecting this option configures the common proxy user for the following services: CIFS, DNS, DHCP, iFolder, NetStorage, and NCS. Optionally, you can specify that LUM uses it.
-
OES Common Proxy User Name: For a host, the common proxy user's name is OESCommonProxy_hostname. You cannot specify any other name than what is given by the system. This restriction prevents possible use of the same common proxy user name across two or more nodes in a tree. For more information, see
Can I Change the Common Proxy User Name and Context?
in the OES 11 SP3: Planning and Implementation Guide. -
OES Common Proxy User Context: Provide the FDN name of the container where the common proxy needs to be created. By default, this field is populated with the NCP server context. For example, ou=acap,o=novell. Where ou is the organization unit, acap is the organization unit name, o is the organization, and novell is the new organization name. For an existing tree, click Browse and select the container where the Common Proxy User must be created.
-
OES Common Proxy User Password: You can accept the default system-generated password or specify a new password for the common proxy user.
NOTE:If you choose to provide your own password, it should conform to the policy that is in effect for the common proxy user. If the password contains single (') or double (") quotes, OES Configuration will fail. These characters have to be escaped by prefixing \. For example, to add a single quote, escape it as nove\'ll. The system-generated password will always be in conformance with the policy rules.
-
Verify OES Common Proxy User Password: If you specified a different password, type the same password in this field. Otherwise, the system-generated password is automatically included.
-
Assign Common Proxy Password Policy to Proxy User: The initial common proxy password policy is a simple password policy created with default rules. If desired, you can modify this policy after the installation to enforce stricter rules regarding password length, characters supported, expiration intervals, and so forth.
IMPORTANT:We recommended against deselecting the Assign Common Proxy Password Policy to Proxy User option. If deselected, the common proxy user inherits the password policies of the container, which could lead to service failures.
-
-
Continue with Configuring OES Services.
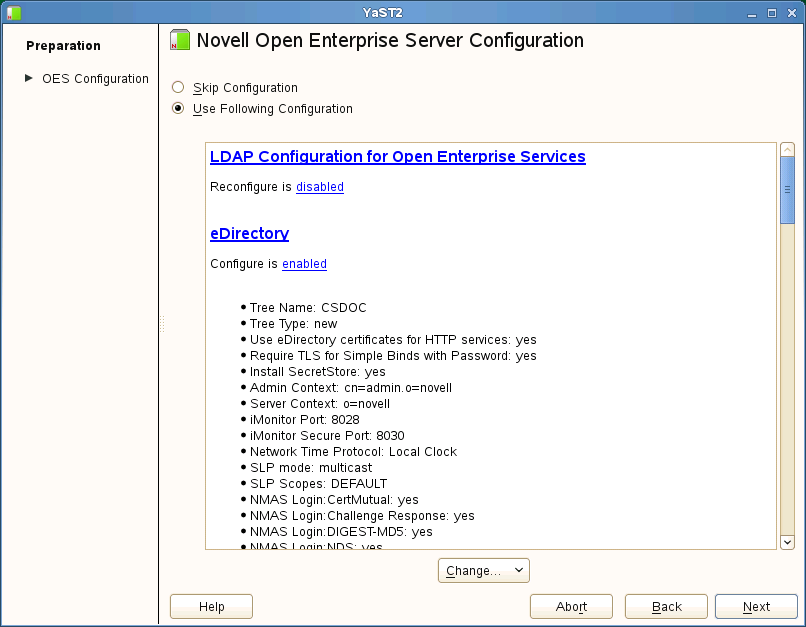
3.8.11 Configuring OES Services
After you complete the LDAP configuration or the eDirectory configuration, the Novell Open Enterprise Server Configuration summary page is displayed, showing all of the OES components that you installed and their configuration settings.
-
Review the setting for each component. Click the component heading to change any settings.
For help with specifying the configuration information for OES services, see the information in Configuration Guidelines for OES Services.
-
When you are finished reviewing the settings for each component, click Next.
-
When you confirm the OES component configurations, you might receive the following error:
The proposal contains an error that must be resolved before continuing.
If this error is displayed, check the summary list of configured products for any messages immediately below each product heading. These messages indicate products or services that need to be configured. If you are running the YaST graphical interface, the messages are red text. If you are using the YaST text-based interface, they are not red.
For example, if you selected Linux User Management in connection with other OES products or services, you might see a message similar to the following:
Linux User Management needs to be configured before you can continue or disable the configuration.
If you see a message like this, do the following:
-
On the summary page, click the heading for the component.
-
Supply the missing information in each configuration page.
When you specify the configuration information for OES services, see the information in Configuration Guidelines for OES Services, or if you are reading online, click a link below:
When you have finished the configuration of a component, you are returned to the Novell Open Enterprise Server Configuration summary page.
-
If you want to skip the configuration of a specific component and configure it later, click Enabled in the Configure is enabled status to change the status to Reconfigure is disabled.
If you change the status to Reconfigure is disabled, you need to configure the OES components after the installation is complete. See Installing or Configuring OES 11 SP3 on an Existing Server.
-
-
After resolving all product configuration issues, click Next to proceed with the configuration of all components.
-
When the configuration is complete, continue with Section 3.9, Finishing the Installation.
3.8.12 Configuration Guidelines for OES Services
Service Configuration Caveats
Keep the following items in mind as you configure the OES 11 SP3:
Table 3-3 Caveats for Configuring OES Services
|
Issue |
Guideline |
|---|---|
|
Software Selections When Using Text-Based YaST |
Some older machines, such as a Dell 1300, use the text mode install by default when the video card does not meet SLES 11 SP4 specifications. When you go to the Software Selection, and then to the details of the OES software selections, YaST doesn’t bring up the OES selections like it does when you use the graphical YaST (YaST2). To view the Software Selection and System Task screen, select Filter > Pattern (or press Alt+F > Alt+I). |
|
Specifying a State identifier for a Locality Class object |
If you to specify a state identifier, such as California, Utah, or Karnataka, as a Locality Class object in your eDirectory tree hierarchy, ensure to use the correct abbreviation in your LDAP (comma-delimited) or NDAP (period-delimited) syntax. When using LDAP syntax, use ou=example_organization,o=example_company,st=utah,c=us When using NDAP syntax, use ou=example_organization.o=example_company.s=utah.c=us |
|
Specifying Typeful Admin Names |
When you install OES, you must specify a fully distinguished admin name by using the typeful, LDAP syntax that includes object type abbreviations (cn=, ou=, o=, etc.). For example, you might specify the following: cn=admin,ou=example_organization,o=example_company |
|
Using Dot-Delimited or Comma-Delimited Input for All Products |
For all parameters requiring full contexts, you can separate the names by using comma-delimited syntax. Ensure that you are consistent in your usage within the field. The OES installation routine displays all input in the comma-delimited (LDAP) format. However, it converts the name separators to dots when this is required by individual product components. IMPORTANT:After the OES components are installed, be sure to follow the conventions specified in the documentation for each product. Some contexts must be specified using periods (.) and others using commas (,). However, eDirectory supports names like cn=juan\.garcia.ou=users.o=novell. The period (.) inside a name component must be escaped. When using NDAP format (dot), you must escape all embedded dots. For example: cn=admin.o=novell\.provo When using LDAP format (commas), you must escape all embedded commas. For example: cn=admin,o=novell\,provo The installation disallows a backslash and period (\.) in the CN portion of the admin name. For example, these names are supported: cn=admin.o=novell cn=admin.o=novell\.provo cn=admin.ou=deployment\.linux.o=novell\.provo These names are not supported: cn=admin\.first.o=novell cn=admin\.root.o=novell Before LUM-enabling users whose cn contains a period (.), you must remove the backslash (\) from the unique_id field of the User object container. For example, cn=juan.garcia has a unique_id attribute = juan\.garcia. Before such a user can be LUM-enabled, the backslash (\) must be removed from the unique_id attribute. |
LDAP Configuration for Open Enterprise Services
Table 3-4 LDAP Configuration for Open Enterprise Services Values
|
Page and Parameters |
|
|---|---|
|
Configured LDAP Servers |
|
|
|
|
|
|
|
|
|
Novell AFP Services
Table 3-5 Novell Apple Filing Protocol Parameters and Values
|
Page and Parameters |
|
|---|---|
|
AFP Configuration - Mac Client Access to NSS Volumes |
|
|
|
For additional configuration instructions, see Installing and Setting Up AFP
in the OES 11 SP3: Novell AFP for Linux Administration Guide.
Novell Archive and Version Services
Table 3-6 Novell Archive and Version Services Parameters and Values
|
Page and Parameters |
|
|---|---|
|
Archive and Version Services Configuration |
|
|
|
|
|
|
|
For additional configuration instructions, see Setting Up Archive and Version Services
in the OES 11 SP3: Novell Archive and Version Services Administration Guide.
Novell Backup/Storage Management Services (SMS)
Table 3-7 Novell Backup/Storage Management Services Parameters and Values
|
Page and Parameters |
|
|---|---|
|
SMS Configuration |
|
|
|
For additional configuration instructions, see Installing and Configuring SMS
in the Installing and Configuring SMS guide.
Novell CIFS for Linux
Table 3-8 Novell CIFS Parameters and Values
|
Page and Parameters |
|
|---|---|
|
Novell CIFS Service Configuration |
|
|
|
|
|
|
|
|
|
|
|
|
Novell CIFS Service Configuration (2) |
|
|
|
For additional configuration instructions, see Installing and Setting Up CIFS
in the OES 11 SP3: Novell CIFS for Linux Administration Guide and the OES 11 SP3: Novell AFP for Linux Administration Guide
Novell Cluster Services
Table 3-9 Novell Cluster Services Parameters and Values
|
Page and Parameters Before you configure a node for a Novell Cluster Services cluster, ensure that you have satisfied the prerequisites and have the necessary Administration rights described in |
|
|---|---|
|
Novell Cluster Services (NCS) Configuration |
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
Novell Cluster Services (NCS) Proxy User Configuration (2) |
|
|
Specify one of the following users as the NCS Proxy user.
|
|
Novell Cluster Services (NCS) Configuration (3) |
|
|
|
|
|
|
|
For additional instructions, see the OES 11 SP3: Novell Cluster Services for Linux Administration Guide.
Novell DHCP Services
Table 3-10 Novell DHCP Services Parameters and Values
|
Page and Parameters |
|
|---|---|
|
Novell DHCP Services Configuration |
|
|
|
|
|
|
|
|
|
|
|
|
|
|
Novell DHCP LDAP and Secure Channel Configuration |
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
Novell DHCP Services Interface Selection |
|
|
|
For additional configuration instructions, see Installing and Configuring DHCP
in the OES 11 SP3: Novell DNS/DHCP Services for Linux Administration Guide.
Novell DNS Services
Table 3-11 Novell DNS Services Parameters and Values
|
Page and Parameters |
|
|---|---|
|
Novell DNS Configuration |
|
|
|
|
|
|
|
For additional configuration instructions, see Installing and Configuring DNS
in the OES 11 SP3: Novell DNS/DHCP Services for Linux Administration Guide.
Novell Domain Services for Windows
There are multiple configuration scenarios, depending on your deployment. For information, see Installing Domain Services for Windows
in the OES 11 SP3: Domain Services for Windows Administration Guide.
NetIQ eDirectory Services
IMPORTANT:You specified the eDirectory configuration for this server in either Specifying LDAP Configuration Settings or Specifying eDirectory Configuration Settings, and the settings you specified were extended to your OES service configurations by the OES install.
If you change the eDirectory configuration at this point in the install, your modifications might or might not extend to the other OES services. For example, if you change the server context from o=example to ou=servers.o=example, the other service configurations might or might not reflect the change.
Be sure to carefully check all of the service configuration summaries on the Novell Open Enterprise Server Configuration summary screen. If any of the services don’t show the eDirectory change you made, click the service link and modify the configuration manually. Otherwise, your installation will fail.
Table 3-12 NetIQ eDirectory Parameters and Values
|
Page and Parameters |
|
|---|---|
|
eDirectory Configuration - New or Existing Tree |
|
|
|
|
|
|
eDirectory Configuration - New/Existing Tree Information |
|
|
|
|
|
|
|
|
|
|
|
|
|
|
eDirectory Configuration - Local Server Configuration |
|
|
|
|
|
|
|
|
|
|
|
|
|
|
eDirectory Configuration - NTP and SLP |
|
|
|
|
|
|
|
|
|
|
NetIQ Modular Authentication Services |
|
|
IMPORTANT:NMAS client software (included with Novell Client software) must be installed on each client workstation where you want to use the NMAS login methods.
If you want to install all of the login methods into eDirectory, click Select All. If you want to clear all selections, click Deselect All. For more information on these login methods, see Defaults: Challenge Response and NDS |
|
OES Common Proxy User Information |
|
|
|
For additional configuration instructions, see Installing or Upgrading NetIQ eDirectory on Linux
in the NetIQ eDirectory 8.8 SP8 Installation Guide.
Novell FTP Services
No additional configuration is required.
Novell iFolder
When you configure iFolder as part of the OES install and configuration, you can specify only an EXT3 or ReiserFS volume location for the System Store Path, which is where you store iFolder data for all your users. You cannot create NSS volumes during the system install.
If you want to use an NSS volume to store iFolder data, you must reconfigure iFolder after the initial OES installation. To reconfigure, use Novell iManager to create an NSS volume, then go to YaST > Open Enterprise Server > Install and Configure Open Enterprise Services and select iFolder 3.9 to enter new information. All previous configuration information is removed and replaced.
Table 3-13 Novell iFolder 3.9 Parameters and Values
|
Page and Parameters |
|
|---|---|
|
Novell iFolder System Configuration Options |
|
|
|
|
Novell iFolder System Configuration |
|
|
|
|
|
|
|
|
|
|
Novell iFolder System Configuration (2) |
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
Novell iFolder LDAP Configuration |
|
|
|
|
|
|
Novell iFolder System Configuration |
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
Novell iFolder Web Access Configuration |
|
|
|
|
|
|
|
|
|
|
|
|
|
|
Novell iFolder Web Admin Configuration |
|
|
|
|
|
|
|
|
|
|
|
|
|
For additional configuration instructions, see Installing and Configuring iFolder Services
in the Novell iFolder 3.9.2 Administration Guide.
Novell iManager
Table 3-14 Novell iManager Parameters and Values
|
Page and Parameters |
|
|---|---|
|
iManager Configuration |
|
|
|
|
|
For additional configuration instructions, see Installing iManager
in the NetIQ iManager Installation Guide.
Novell iPrint
Table 3-15 Novell iPrint Parameters and Values
|
Page and Parameters |
|
|---|---|
|
iPrint Configuration |
|
|
|
|
|
For additional configuration instructions, see Installing and Setting Up iPrint on Your Server
in the OES 11 SP3: iPrint Linux Administration Guide.
Novell Linux User Management
Table 3-16 Novell Linux User Management Parameters and Values
|
Page and Parameters |
|
|---|---|
|
Linux User Management Configuration |
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
Linux User Management Configuration (2) |
|
|
IMPORTANT:Before you change the PAM-enabled service settings, ensure that you understand the security implications explained in
|
For additional configuration instructions, see Setting Up Linux User Management
in the OES 11 SP3: Novell Linux User Management Administration Guide.
Novell NCP Server / Dynamic Storage Technology
Table 3-17 Novell NCP Server Parameters and Values
|
Page and Parameters |
|
|---|---|
|
NCP Server Configuration |
|
|
|
For additional configuration instructions, see Installing and Configuring NCP Server for Linux
in the OES 11 SP3: NCP Server for Linux Administration Guide.
Novell NetStorage
Table 3-18 Novell NetStorage Parameters and Values
|
Page and Parameters |
|
|---|---|
|
NetStorage Configuration |
|
|
|
|
|
|
|
|
|
For additional configuration instructions, see Installing NetStorage
in the OES 11 SP3: NetStorage Administration Guide for Linux.
Novell Pre-Migration Server
No additional configuration is required. For information, see Preparing the Source Server for Migration
the OES 11 SP3: Migration Tool Administration Guide.
Novell QuickFinder
Table 3-19 Novell QuickFinder Parameters and Values
|
Page and Parameters |
|
|---|---|
|
Novell QuickFinder Admin User |
|
|
|
|
|
|
|
|
Novell QuickFinder Admin Password |
|
|
|
|
|
For additional configuration instructions, see Installing QuickFinder Server
in the OES 11 SP3: Novell QuickFinder Server 5.0 Administration Guide.
Novell Remote Manager
No additional configuration for the installation is required. To change the configuration after the installation, see Changing the HTTPSTKD Configuration
in the OES 11 SP3: Novell Remote Manager Administration Guide.
Novell Samba
Table 3-20 Novell Samba Parameters and Values
|
Page and Parameters |
|
|---|---|
|
Novell Samba Configuration |
|
|
|
|
|
|
|
|
|
For additional configuration instructions, see Installing the Novell Samba Components
in the OES 11 SP3: Novell Samba Administration Guide.
Novell Storage Services (NSS)
Table 3-21 Novell Storage Services Parameters and Values
|
Page and Parameters |
|
|---|---|
|
NSS Unique Admin Object |
|
|
|
|
|
For additional configuration instructions, see Installing and Configuring Novell Storage Services
in the OES 11 SP3: NSS File System Administration Guide for Linux.