8.1 How SecureLogin Uses Smart Cards
This section provides information on the following:
8.1.1 Prerequisites
The use of smart cards with Novell SecureLogin is based on the enterprise or corporate preference to allow user to utilize a smart card to log in and store their single sign-on data, or to encrypt their directory data by using a Public Key Infrastructure (PKI) token.
To enable the smart card support for Novell SecureLogin, the option must be selected during the installation regardless of your intended preferences for setting the security preference, .
IMPORTANT:Novell SecureLogin 6.1 SP1 only supports ActivClient*, Gemalto* (formerly Axalto), and AET SafeSign* smart card middleware.
8.1.2 Using Smart Card to Log In to Workstation
Novell SecureLogin allows a user to alternate their log in method by using both a smart card and their log in credentials.
However, a user can only log in by using both a smart card and password log in to access the SecureLogin credentials only if the option is selected during installation.
If the option is not selected during installation, a user attempting to access SecureLogin on the workstation is forced to log in with his or her username and network password.
Using Smart Card for an Initial Log In
When no smart card preferences are applied to the user, the is set to , and the user has not initially logged in by using his or her username and password, the following warning message is displayed.
Figure 8-1 Smart Card Warning
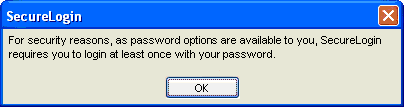
For security reasons, Novell SecureLogin requires a user to log in at least once by using the username and password before their smart card access is available.
When the preference is set to and the smart card preferences are applied to the user, then the user can initially log in by using either the smart card or the username and password. The security warning is not displayed.
8.1.3 Storing Single Sign-on Credentials
SecureLogin uses a store-and-forward approach to single sign-on credentials, and records user IDs and passwords in this store. It is likely that many, if not all, of an individual user's passwords will be stored in this credential store. Given this architecture, the security of SecureLogin credential store is extremely important.
When a smart card is used in conjunction with SecureLogin, a number of new features can be optionally implemented to increase security. Some of them are:
-
Using smart card to encrypt SecureLogin.
-
Storing single sign-on credentials such as application usernames and passwords on the smart card.
-
Typing single sign-on availability to the smart cards so only those who log in using a smart card are able to start and administer single sign-on.
SecureLogin uses a two-tier encryption process to secure users’ sensitive credentials and information. All user passwords are encrypted with the user key, and all user data, including password fields, are encrypted with the master key.
The result is a two-tier encryption process where password values are encrypted twice: once with the user key and once with the master key, while all other data is encrypted once with master key.
Using SecureLogin in conjunction with a smart card provides an additional level of security because the key used to decrypt data is stored on the smart card, and authentication is through two-factor authentication: smart card and PIN. If the you select the option option, users must insert a smart card and enter a PIN for SecureLogin to load.
8.1.4 Authentication Methods
The following sections explain the strong authentication methods used in Novell SecureLogin.
Advanced Authentication
New Functionality in the AAVerify Command
This release of Novell SecureLogin enhances the AAVerify command functionality.
A predefined AAVerify application definition command (script) used to reauthenticate a user already exists in the previous releases of Novell SecureLogin.
For details of the AAVerify application definition command, see the Novell SecureLogin 6.1 SP1 Application Definition Guide.
The existing version of the AAVerify command relies on either SecureLogin Advanced Authentication (SLAA) or Novell Modular Authentication Services (NMAS) being deployed on the server of the backend to process any reauthentication calls.
The new AAVerify command was developed specifically provide a secure method to reauthenticate a user successfully before populating the Novell SecureLogin credentials for designated sensitive applications. In an enterprise or corporate environment, a sensitive application is one where a Novell SecureLogin application definition is applied calling for reauthentication.
To process the reauthentication request, the new AAVerify command now takes into account the method by which users are currently logged in, as well as their directory connectivity status.
If users have logged in with a username and password, they are prompted to reauthenticate by using the password, regardless of whether they are offline or online.
If users have logged in with a smart card, they are prompted to reauthenticate by using the original smart card PIN, regardless of whether they are offline or online.
The new AAVerify command is independent of SLAA or NMAS and can be used to enforce strong user-friendly re-authentication by using a smart card and PIN or password without installing SLAA or NMAS.
The new AAVerify command caters to a mixed environment where either of the following conditions exist:
-
A user might log in to a number of workstations by using a combination of both smart card or password authentication
-
A scenario where several users might log in to one workstation by either smart card or password authentication.
The New ?IsPin Variable
?IsPin is a new Novell SecureLogin variable available in Microsoft Active Directory mode only.
The ?IsPin variable is automatically generated when a user logs in and stores, information based on whether the user has logged in to the workstation by using a smart card and PIN, or has logged in by using a password.
When the ?IsPin variable is called from an application definition, it indicates the following:
-
If the returned value is true, it means that the user has logged in by using a smart card, and only the PIN value is passed through to the Novell SecureLogin.
-
If the returned value is false, it means that the user has logged with a password.
NOTE:The ?IsPin variable is updated only at a login and is not updated at a screen unlock.
Supported Operating System Environment
The new AAVerify command functionality has been completely tested in the following systems:
-
Microsoft Windows XP SP2
-
Microsoft Windows 2000 SP4
-
Microsoft Windows Vista (32-bit)
Supported Directory Environments
The Novell SecureLogin AAVerify command functionality is not currently supported in either LDAP or stand-alone mode.
Recommended Configuration
The option is normally based on your preference to have the Novell SecureLogin users utilize a smart card to store the single sign-on data or to encrypt their user’s directory data by using a Public Key Infrastructure (PKI).
If you decide to allow users to log in to their workstations by using a smart card and reauthenticate against their smart card, then the option must be selected during the installation regardless of the option set for .
NOTE:We recommend that you use a smart card configuration policy to lock the screen on card removal to ensure that the smart card belongs to the currently logged-in user.
Example Application Definition
The following application definition shows how to call the AAVerify command based on the login method. It uses the Notepad application. After the Notepad application is started, the AAVerify command is invoked to prompt the user to reauthenticate, using the login method for the workstation.
Dialog Class Notepad EndDialog OnException AAVerifyFailed Call AAVerifyFailed OnException AAVerifyCancelled Call AAVerifyCancelled If ?isPin Eq “true” AAVerify -method "smartcard" ?result Else AAVerify -method "password" ?result EndIf ClearException AAVerifyFailed ClearException AAVerifyCancelled Type $username Type \n Type $password Type \n Sub AAVerifyFailed MessageBox "Reauthentication failed." EndScript EndSub Sub AAVerifyCancelled MessageBox "Reauthentication cancelled." EndScript EndSub ## EndSection: "Login Window"
Reauthenticating a Predefined Web Application
If the new AAVerify command is used to reauthenticate a Web browser-based application or if the option is enabled for Web applications, then the predefined application definition for the Web browser must be applied for that particular user to avoid confusion when prompting for reauthentication.
One Time Password
The use of multiple passwords places high maintenance overheads on large enterprises. Users are frequently required to use and manage multiple passwords.
A one time password reduces the cost, particularly with regard to calls to the help desk to reset a forgotten password, or to ensure that all passwords are provisioned when a new user starts, or deleted when existing user leaves the organization.
SecureLogin integrates with ActivCard* one time password authentication functionality and provides you access to the GenerateOTP application definition command, which can be used to generate synchronous authentication and asynchronous authentication soft token support for smart card user authentication. For more information on one-time password see, Section 8.1.7, One-Time Password.
8.1.5 Network Authentication
Network authentication is the verification of a user's login credentials before granting access to a network or operating system. Users typically authenticate to a network using one of the following methods:
-
Password
-
Biometric device (fingerprint or iris scan)
-
Smart card and PIN
-
Token
When a user authenticates successfully and the operating system loads, SecureLogin starts and manages the login credentials to the user's single sign-on-enabled applications.
If you want to enforce biometric, smart card, or token authentication at the application (or transaction) level, SLAA or NMAS can be integrated with SecureLogin to prompt the user to re-authenticate before SecureLogin retrieves their credentials and logs in to single sign-on enabled applications.
Network authentication methods can also be integrated with SecureLogin to manage a user's Windows log in credentials. The authentication methods retrieves a user’s Windows username and password from the smart card and automatically enters this into the Windows Graphical Identification and Authorization (GINA) interface when the users enters a PIN.
8.1.6 Smart Card Application Re-Authentication
Stronger application re-authentication methods such as Secure Login Advanced Authentication and NMAS can also be integrated with SecureLogin to provide additional smart card and PIN re-authentication to single sign-on-enabled applications.
To do this, enable the option and configure the re-authentication method.
For information about configuring SecureLogin to re-authenticate an application, see Section 10.0, Reauthenticating Applications.
8.1.7 One-Time Password
A one-time password is an authentication method specifically designed to avoid the security exposures inherited with traditional fixed and static password usage.
One-time passwords rely upon a predefined relationship between the user and an authenticating server. The encryption key is shared between the user's token generator (which can be a token or one-time password-enabled smart card) and the server, with each performing the pseudo-random code calculation at user login. If the codes match, the user is authenticated.
The main benefit of one-time password systems is that it is impossible for a password to be captured on the wire and replayed to the server. This is particularly important if a system does not encrypt the password when it is sent to the server, as is the case with many legacy mainframe systems.
SecureLogin uses an application definition (script) command to provide access to the GenerateOTP command, which can be used to generate synchronous and asynchronous authentication soft token support for smart card user authentication as well as hard token support for the Vasco* Digipass* token generator.