6.2 Setting Up an LDAP Server
You must configure one or more LDAP servers, in addition to an LDAP directory, when one or both of the following situations exist:
-
You want to configure a pool of LDAP servers to provide redundancy for LDAP authentication.
-
You want to provide GroupWise users in a remote location with a local LDAP server and directory replica to facilitate prompt LDAP authentication.
Add one of more LDAP servers to your GroupWise system, and then configure a pool of LDAP servers for each post office.
6.2.1 Adding an LDAP Server
Ensure that you know the required information for the LDAP server that you want to set up for use with your LDAP directory.
To add an LDAP server to make your LDAP directory more accessible:
-
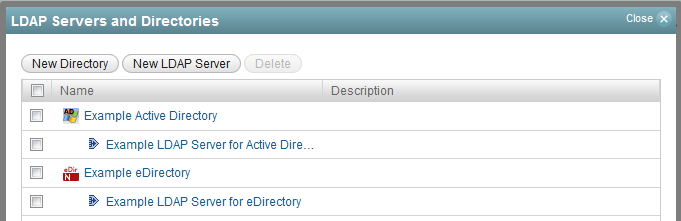
In the GroupWise Administration Console, click System > LDAP Servers, and then click New LDAP Server.
-
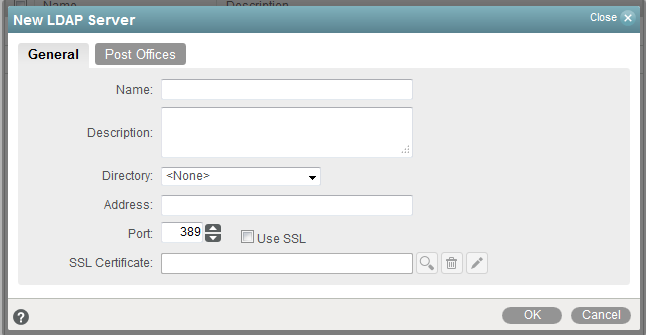
Fill in the fields on the General tab, and then click the Post Offices tab.
-
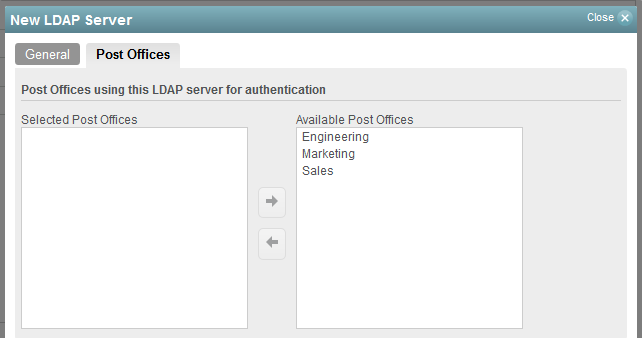
Select one or more post offices in the Available Post Offices list, and then click the arrow button to move them into the Selected Post Offices list.
-
Click OK to add the new LDAP server to your GroupWise system.
-
Click Close to return to the main Administration Console window.
-
Continue with Configuring a Pool of LDAP Servers.
6.2.2 Configuring a Pool of LDAP Servers
When you configure multiple LDAP servers, all configured LDAP servers make up the initial LDAP server pool. By default, the POA can contact any server in the pool when authenticating a GroupWise user that belongs to a post office. This provides load balancing and fault tolerance because each LDAP server in the pool is contacted equally often by the POA. You might prefer that the POA for a post office first contact specific LDAP servers, contacting other servers in the pool only if none of the preferred LDAP servers are available.
-
In the GroupWise Administration Console, ensure that you have more than one LDAP server set up for use with GroupWise.
-
Browse to and click the name of a post office, and then click the Security tab.
-
Select LDAP Authentication to activate the pool settings.
-
(Optional) Adjust the pool settings as needed for your network environment.
-
Select one or more LDAP servers in the Available LDAP Servers list, and then click the arrow button to move them into the Selected LDAP Servers list.
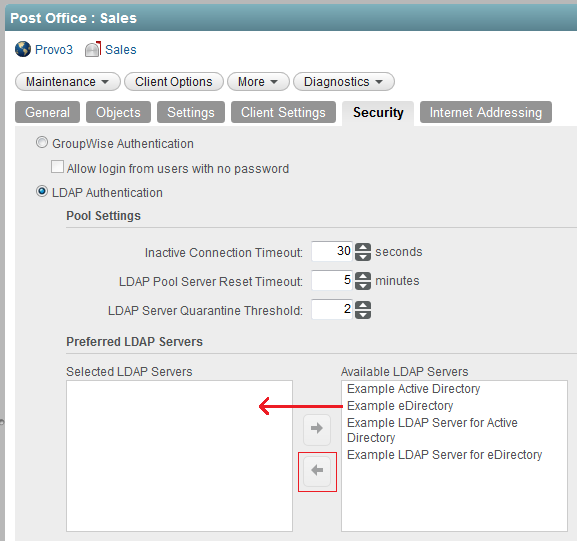
NOTE:The “pooling” function is not automatic with multiple available LDAP servers in your GroupWise system. Load balancing and fault tolerance across LDAP servers will only occur in post offices for those servers added to the Selected LDAP Servers list shown in the image above.
-
Click OK to save the security settings for the post office.
Corresponding Startup Switches: You can also use the ‑‑ldappoolresettime startup switch in the POA startup file to configure the timeout interval.
6.2.3 Specifying Failover LDAP Servers
In order to set up the failover process, you first have to set up the LDAP server pool so that those servers are part of the failover. See Configuring a Pool of LDAP Servers.
Once you have an LDAP server pool, you can use the --ldapServerFailoverList switch. Then, if the primary LDAP server fails to respond, the POA tries the next LDAP server in the list, and so on, until it is able to access the LDAP directory. This provides failover LDAP servers for the primary LDAP server but does not provide load balancing, because the primary LDAP server is always contacted first.
-
In the GroupWise Administration Console, ensure you have provided the basic LDAP information on the Post Office object Security tab.
For background information, see Providing LDAP Authentication for GroupWise Users.
-
Edit the POA startup file (post_office.poa) with an ASCII text editor.
For more information about the POA startup file, see Using POA Startup Switches.
-
Use the --ldapServerFailoverList startup switch to list addresses for multiple LDAP servers. Use a space between each host name or IP address.
Syntax:
Windows: /ldapServerFailoverList-"hostName1 hostName2 hostName3"
Linux: --ldapserverFailoverList "hostName1 hostName2 hostName3"
For example:
Windows: /ldapServerFailoverList-"Srvr01.mydomain.com Srvr02.mydomain.com Srvr03.mydomain.com"
Linux: --ldapServerFailoverList "Srvr01.mydomain.com Srvr02.mydomain.com Srvr03.mydomain.com"
-
Save the POA startup file, and then exit the text editor.
-
Stop the POA, and then start the POA so that it reads the updated startup file.