1.4 Configuring the Access Gateway
The basic Access Gateway configuration procedures have been divided into the following tasks:
1.4.1 Configuring a Reverse Proxy
You protect your Web services by creating a reverse proxy. A reverse proxy acts as the front end to your Web servers in your DMZ or on your intranet, and off-loads frequent requests, thereby freeing up bandwidth and Web server connections. It also increases security because the IP addresses and DNS names of your Web servers are hidden from the Internet. A reverse proxy can be configured to protect one or more proxy services.
To create a reverse proxy, you must create at least one proxy service with a protected resource. You must supply a name for each of these components. Reverse proxy names and proxy service names must be unique to the Access Gateway because they are configured for global services such as IP addresses and TCP ports. For example, if you have a reverse proxy named products and another reverse proxy named library, only one of these reverse proxies can have a proxy service named corporate.
Protected resource names need to be unique to the proxy service, but they don’t need to be unique to the Access Gateway because they are always accessed through their proxy service. For example, if you have a proxy service named account and a proxy service named sales, they both can have a protected resource named public.
This first reverse proxy is used for authentication. You need to configure the proxy service to use the DNS name of the Access Gateway as its , and the Web server and the resource on that Web server need to point to the page you want displayed to the users when they first access your Web site. You can use Access Gateway configuration options to allow this first page to be a public site with no authentication required until the users access the links on the page, or you can require authentication on this first page. The following configuration steps have you first configure the protected resource as a public resource, then you modify the configuration to require authentication.
-
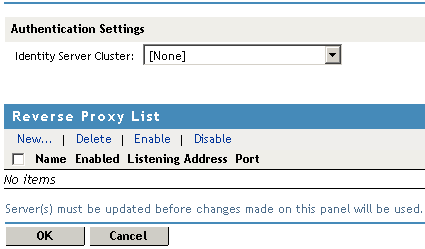
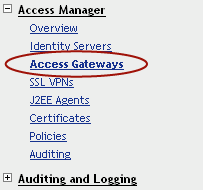
In the Administration Console, click > > > .
-
In the option, select the configuration you have assigned to the Identity Server.
This sets up the trust relationship between the Access Gateway and the Identity Server that is used for authentication.
-
In the , click , specify a display name for the reverse proxy, then click .
-
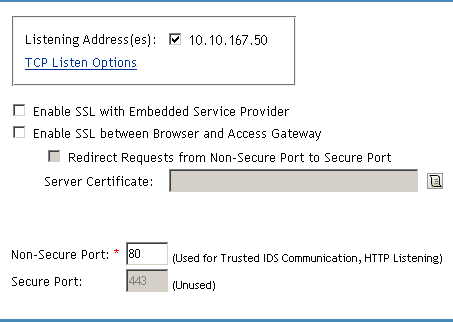
Enable a listening address.
Listening Address(es): A list of available IP addresses. If the server has only one IP address, only one is displayed and it is automatically selected. If the server has multiple addresses, you can select one or more IP addresses to enable. You must enable at least one address by selecting its check box.
TCP Listen Options: Options for configuring how requests are handled. You cannot set up the listening options until you create a proxy service.
-
Ignore the SSL configuration options.
This basic configuration does not set up SSL. For SSL information, see Section 3.0, Enabling SSL Communication.
-
Configure a listening port.
Non-Secure Port: Select 80, which is the default port for HTTP.
Secure Port: This is the HTTPS listening port. This port is unused and cannot be configured until you enable SSL.
-
In the , click .
-
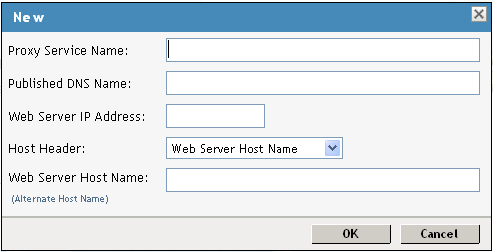
Fill in the fields.
Proxy Service Name: A display name for the proxy service.
Published DNS Name: The DNS name you want the public to use to access your site. This DNS name must resolve to the IP address you set up as the listening address. For the example in Figure 1-2, this name would be www.mytest.com.
Web Server IP Address: The IP address of your Web server. This is usually a Web server with content that you want to share with authorized users and protect from all others. In Figure 1-2, this is Server 4, whose IP address is 10.15.70.21.
Host Header: The name you want sent in the HTTP header to the Web server. This can be either the Published DNS Name (the option) or the DNS name of the Web Server (the option).
Web Server Host Name: The DNS name that the Access Gateway should forward to the Web server. This option is not available if you selected for the option. The name you use depends upon how you have set up the Web server. If your Web server has been configured to verify that the host name in the header matches its name, you need to specify that name here. In Figure 1-2 the Web Server Host Name is mywebserver.com.
-
Click .
-
Continue with Section 1.4.2, Configuring a Public Protected Resource.
1.4.2 Configuring a Public Protected Resource
The first protected resource in this configuration tutorial is configured to be a public resource. For information on how to set up authentication for a protected resource, see Section 1.5, Configuring the Access Gateway for Authentication.
-
In the , click > .
-
In the , click .
-
Specify a display name for the protected resource, then click .

-
(Optional) Specify a description for the protected resource.
-
In the field, select .
The field must be set to . This is what makes this resource a public resource.
-
Configure the .
The default path is /*, which allows access to everything on the Web server. Modify this if you need to restrict access to a specific directory on your Web server.
-
To delete the default path, select the check box by the path, then click .
-
To edit a path in the list, click the path, modify it, then click .
-
To add a path, click , specify the path, then click . For example, to allow access to the pages in the public directory on the Web server, specify the following path:
/public/*
-
-
Click .
-
In the , verify that the protected resource you created is enabled, then click OK.
-
Click the link.
-
To apply the changes, click > .
Until this step, nothing has been permanently saved or applied. The status pushes the configuration to the server and writes the configuration to the configuration data store. When the update has completed successfully, the server returns the status of .
To save the changes to the configuration store without applying them, do not click . Instead, click . If you have pending configuration settings, the button is active, and the configuration page indicates which services will be updated. Click to write these changes to the configuration store. The changes are not applied until you click on the Access Gateways page.
-
To update the Identity Server to establish the trust relationship with the Access Gateway, click > , then click .
Wait until the status is and the status is green.
-
Click .
-
(Optional). To test this configuration from a client browser, enter the published DNS name as the URL in the browser. For the example illustrated in Figure 1-2, you would enter the following URL:
http://www.mytest.com
This should resolve to the published DNS name you specified in Step 8, and the user should be connected to the Web server through the Access Gateway.
-
Continue with Section 1.5, Configuring the Access Gateway for Authentication.