5.1 Using the Console Taskbar
The taskbar on the left provides access to the Management Console tasks. If the taskbar is not visible, click the button.
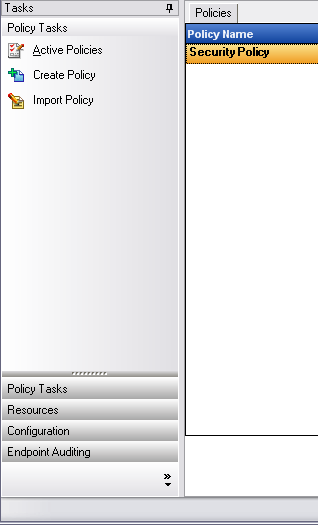
Figure 5-1 The Management Console
The functions available in the taskbar are described in the following sections:
5.1.1 Policy Tasks
The primary function of the Management Console is the creation and dissemination of security policies. The Policy Tasks guide the administrator through creating and editing security policies that are used by the Endpoint Security Client to apply centrally managed security to each endpoint.
The Policy Tasks include the following:
-
Active Policies: Displays a list of current policies, which can be reviewed and edited. Click the policy to open it.
-
Create Policy: Starts the policy creation process. For more information, see Section 6.0, Creating and Distributing Security Policies.
-
Import Policy: Imports policies created using other management services. For more information, see Section 6.4.1, Importing Policies.
Clicking any of the policy tasks minimizes the taskbar. Click the Tasks button left side of the Management Console to display it again.
5.1.2 Resources
The following resources are available to help you:
-
Contact Support: Launches a browser to display the Novell Contacts and Offices page.
-
Online Technical Help: Launches a browser to display the Novell Training and Support page.
-
Management Console Help: Launches Help.
5.1.3 Configuration
The Management Service Configuration tasks provide controls for both the ZENworks Endpoint Security Management server infrastructure and controls for monitoring additional enterprise directory services. See Section 5.3, Using the Configuration Window for details. This control is not available when running a "Stand-Alone" Management Console. See the ZENworks Endpoint Security Management Installation Guide for more information.
5.1.4 Endpoint Auditing
Endpoint Auditing gives you access to Endpoint Security Management Reporting and Alerting.
Alerts monitoring ensures that any attempts to compromise corporate security policies are reported in the Management Console. This allows the ZENworks Endpoint Security Management administrator to know of potential problems and take any appropriate remedial actions. The Alerts dashboard is completely configurable, granting total control over when and how frequently alerts are triggered. See Section 5.4, Using Alerts Monitoring for details.
Reporting is critical in assessing and implementing strong security policies. Reports can be accessed through the Management Console by clicking . The endpoint security information gathered and reported back is also completely configurable, and can be gathered by domain, group, or individual user. See Section 5.5, Using Reports for details.